- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Hi - old post, but would like
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
WLC + ISE Web Authentification
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-17-2016 04:55 AM - edited 03-11-2019 12:00 AM
I have configured the Web Authentification on the ISE which connects to the WLC.
My intention is it to create a Guest Portal which requires a username and a password on a web login page. I have managed to get all this working.
When a new client connects to the guest SSID which I have created, the user "must" enter username and password which was created by the sponsor.
The Problem: Once I have used a client, went through all the stages (web auth, username password, successfully connected to the internet)...The web login page never returns for the same client. The WLC registers the clients (Samsung Tablet) stores the information.
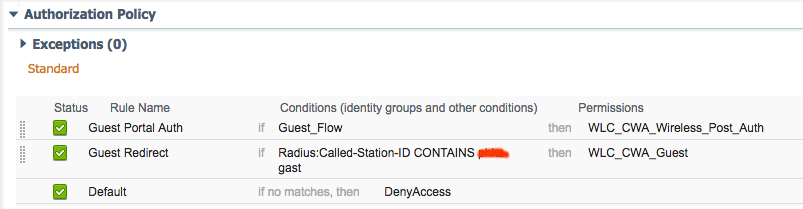
First time using the SSID:

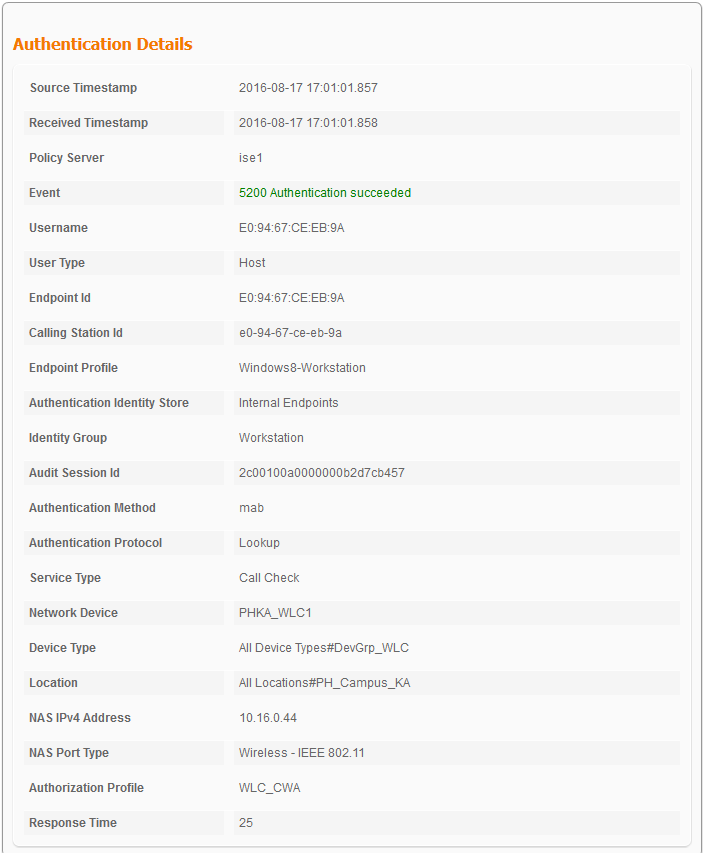
Second time using same SSID:

What I need is for the Centralized Web Authentication to always ask for the username and password after disconnecting from the network, whether its a returning client or a new client.
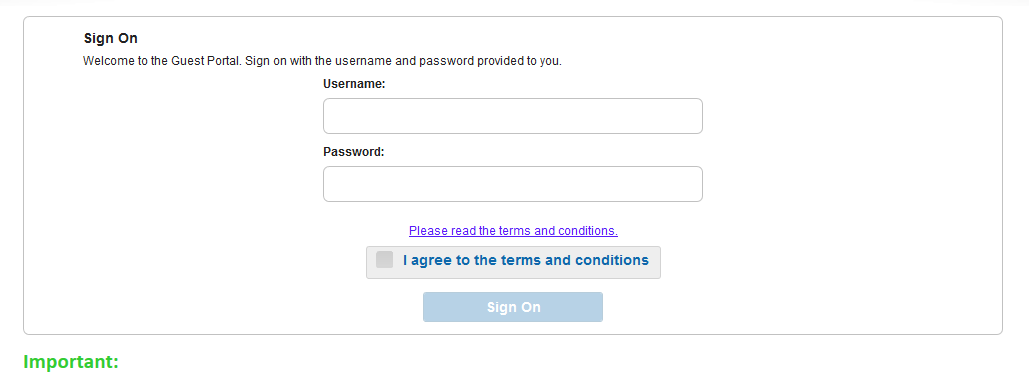
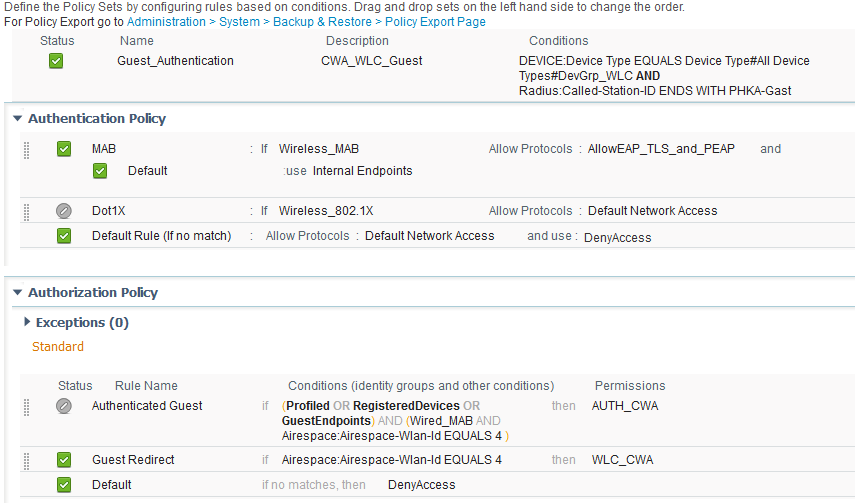
My Policy set:
Thanks
- Labels:
-
AAA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-17-2016 06:45 AM
There is no way to cache guest credentials with ISE because all of the guest logins are session based (based on the specific Radius session on the WLC or Switch). The only real way to get around guests having to enter their credentials on each new session is via device registration & it seems you're configured for THAT too.
Using device registration you can require the guests to log in the first time, their device will be registered (to GuestEndpoints for example), and then your post-CWA rule can be based on membership in GuestEndpoints.
This is now completely up to, how purge rule is configured to clear out that registered endpoints. (minimum of 1 day in ISE.) Once the purge happens, the client would be required to log in again. You need to check how this setting is configured on your ISE.
Rgds,
Jatin
~ Do rate helpful posts.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-17-2016 08:46 AM
I slightly understand where you coming from...purge rule = 1 day ...
Device registration = enable
Yet it doesn't quite solve my problem...
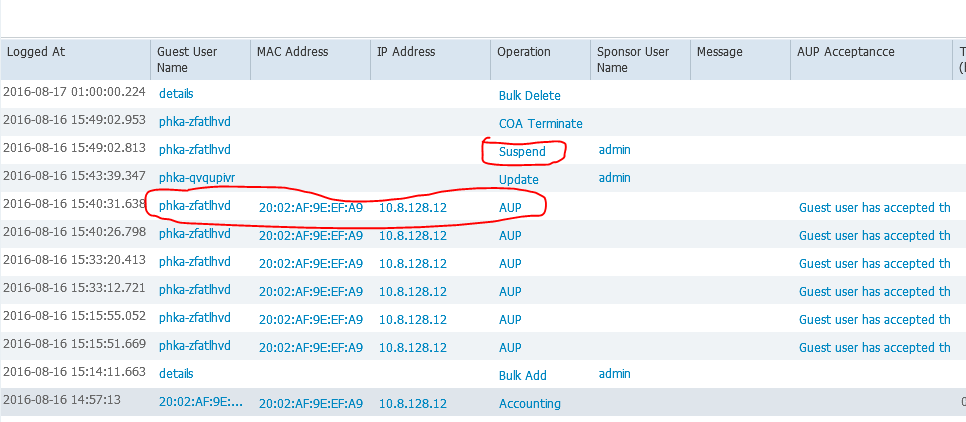
Major Issue: What is causing my clients (which I can see under Identities -> EndPoints) to be able to connect to the WLAN SSID Guests even though I have suspended all the guest accounts on my sponsor portal?
Is it the Policy? Is it the ACL? Is it the guest type settings?

Also when a client who was before connected to the Guest SSID, Username is no longer known because the web_authentication doesn't appear so the client just connects and can start surfing...which is not how I imagine a guest access...

As soon as a client (iPhone, Samsung Tablet, Windows Laptop etc.) gets assigned to a Identity Group in ISE (Workstation, Profiled, GuestEndPoints) the Web Authentication gets ignored???
When I look at the Authentication report details (Username is shown as the Mac Address instead of the generated Guest Username...?) | guest username: phka-xxxx |
Is the Autorisation part getting ignored now that the clients became part of Identity groups?
I cannot figure out where the problem actually lies because (must be something on the ISE cuz the WLC settings seem fine according to the cisco Documentations)
Hope you can help further...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-26-2016 03:05 AM
Managed to solve my Problem! If anybody has a similar issue feel free to ask...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-15-2017 03:26 AM
Hi - old post, but would like to know how you solved this issue?
Having same challenge. Suspend user account, guest device is registered, and device auth rule still authorizes device.
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-21-2017 11:32 PM
Hi Thomas,
Once the guest is authenticated, the ISE will go through a second authorization.
In this second authorization, we need to return a profile so the guest is permitted access to the network. I used usecase: "Guestflow" to easily match the second authorization.
Here is my Authorization Policy (which has been working ever since)
PS: Please give Feedback if this was helpful.
Regards
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide