- Cisco Community
- Technology and Support
- Security
- Network Security
- ASA 5510 communication between 2 same security interfaces.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
ASA 5510 communication between 2 same security interfaces.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-16-2014 09:39 AM - edited 03-11-2019 08:46 PM
Sorry to ask but I am in a time crunch and need to get this working today. I am trying to get the Inside interface to talk to the LegacyLAN interface. I could use the help thank you and sorry if this has been asked befor. Thank you for any help.
ASA Version 9.1(4)
!
hostname
domain-name
xlate per-session deny tcp any4 any4
xlate per-session deny tcp any4 any6
xlate per-session deny tcp any6 any4
xlate per-session deny tcp any6 any6
xlate per-session deny udp any4 any4 eq domain
xlate per-session deny udp any4 any6 eq domain
xlate per-session deny udp any6 any4 eq domain
xlate per-session deny udp any6 any6 eq domain
names
!
interface Ethernet0/0
description WAN
nameif Outside
security-level 0
ip address x.x.x.x 255.255.255.240
!
interface Ethernet0/1
description LAN
nameif Inside
security-level 100
ip address 10.132.3.1 255.255.255.0
!
interface Ethernet0/2
description DMZ
nameif DMZ
security-level 50
ip address 10.132.10.1 255.255.255.0
!
interface Ethernet0/3
description Guest Wireless
nameif GuestWireless
security-level 75
ip address 10.132.11.1 255.255.255.0
!
interface Management0/0
description LegacyLAN 192.168.119.X/24
nameif LegacyLAN
security-level 100
ip address 192.168.119.1 255.255.255.0
!
boot system disk0:/asa914-k8.bin
!
ftp mode passive
clock timezone CST -6
clock summer-time CDT recurring
dns domain-lookup Inside
dns domain-lookup LegacyLAN
dns server-group DefaultDNS
name-server 8.8.8.8
name-server 192.168.119.1
name-server 10.132.3.1
name-server 8.8.4.4
domain-name
!
same-security-traffic permit inter-interface
same-security-traffic permit intra-interface
!
object network Tunnel172.16.0.0
subnet 172.16.0.0 255.255.0.0
description Tunnel Network 172.16.X.X
object network Tunnel192.168.118.0
subnet 192.168.118.0 255.255.255.0
description Tunnel Network 192.168.152.X
object network Tunnel192.168.152.0
subnet 192.168.152.0 255.255.255.0
description Tunnel network 192.168.152.X
object network LegacyLAN
subnet 192.168.119.0 255.255.255.0
object-group network NETWORK_OBJ_10.132.10.0_24
description DMZ_Int
network-object 10.132.10.0 255.255.255.0
object-group network NETWORK_OBJ_10.132.11.0_24
description GuestWireless_Int
network-object 10.132.11.0 255.255.255.0
object-group network NETWORK_OBJ_10.132.3.0_24
description Inside_Int
network-object 10.132.3.0 255.255.255.0
object-group network DM_INLINE_NETWORK_1
network-object 10.132.3.0 255.255.255.0
network-object 192.168.119.0 255.255.255.0
object-group network Tunnel_Networks
description Tunnel Networks With Japan
network-object object Tunnel172.16.0.0
network-object object Tunnel192.168.118.0
network-object object Tunnel192.168.152.0
object-group network DM_INLINE_NETWORK_2
network-object 10.132.3.0 255.255.255.0
network-object 192.168.119.0 255.255.255.0
object-group network DM_INLINE_NETWORK_3
network-object 10.132.3.0 255.255.255.0
network-object 192.168.119.0 255.255.255.0
object-group network DM_INLINE_NETWORK_4
network-object 10.132.3.0 255.255.255.0
network-object 192.168.119.0 255.255.255.0
object-group network NETWORK_OBJ_192.168.119.0_24
description LegacyLAN_Int
network-object 192.168.119.0 255.255.255.0
access-list Outside_cryptomap extended permit ip object-group DM_INLINE_NETWORK_1 object-group Tunnel_Networks
access-list Outside_access_in extended permit ip object-group Tunnel_Networks object-group DM_INLINE_NETWORK_2
access-list LegacyLAN_access_in remark Implicit rule: Permit all traffic to less secure networks
access-list LegacyLAN_access_in extended permit ip any any
access-list LegacyLAN_access_in extended permit ip object-group Tunnel_Networks object-group DM_INLINE_NETWORK_4
access-list LegacyLAN_access_in extended permit ip 192.168.119.0 255.255.255.0 10.132.3.0 255.255.255.0
access-list Inside_access_in remark Implicit rule: Permit all traffic to less secure networks
access-list Inside_access_in extended permit ip any any
access-list Inside_access_in extended permit ip object-group Tunnel_Networks object-group DM_INLINE_NETWORK_3
access-list Inside_access_in extended permit ip 10.132.3.0 255.255.255.0 192.168.119.0 255.255.255.0
access-list NONAT extended permit ip 192.168.119.0 255.255.255.0 10.132.3.0 255.255.255.0
access-list NONAT extended permit ip 10.132.3.0 255.255.255.0 192.168.119.0 255.255.255.0
access-list LegacyLAN-network extended permit udp any any
access-list LegacyLAN-network extended permit ip any any
pager lines 24
mtu Outside 1500
mtu Inside 1500
mtu DMZ 1500
mtu GuestWireless 1500
mtu LegacyLAN 1500
no failover
icmp unreachable rate-limit 1 burst-size 1
icmp permit any Outside
icmp permit any Inside
icmp permit any DMZ
icmp permit any GuestWireless
asdm image disk0:/asdm-715-100.bin
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
nat (LegacyLAN,Outside) source static DM_INLINE_NETWORK_1 DM_INLINE_NETWORK_1 destination static Tunnel_Networks Tunnel_Networks no-proxy-arp route-lookup
!
object network LegacyLAN
nat (LegacyLAN,Outside) dynamic interface
!
nat (Inside,Outside) after-auto source dynamic any interface
nat (DMZ,Outside) after-auto source dynamic any interface
nat (GuestWireless,Outside) after-auto source dynamic any interface
access-group Outside_access_in in interface Outside
access-group Inside_access_in in interface Inside
access-group LegacyLAN-network in interface GuestWireless
access-group LegacyLAN_access_in in interface LegacyLAN
!
route Outside 0.0.0.0 0.0.0.0 201.144.158.97 1
!
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-record DfltAccessPolicy
!
management-access Inside
dhcp-client update dns server both
dhcpd dns 8.8.8.8 8.8.4.4
dhcpd update dns both override
!
dhcpd address 10.132.3.100-10.132.3.200 Inside
dhcpd dns 10.132.3.1 8.8.8.8 interface Inside
dhcpd update dns both override interface Inside
dhcpd enable Inside
!
dhcpd address 192.168.119.150-192.168.119.253 LegacyLAN
dhcpd dns 192.168.119.1 8.8.8.8 interface LegacyLAN
dhcpd update dns both override interface LegacyLAN
dhcpd enable LegacyLAN
!
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
ntp server 128.227.205.3 source Outside
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect ip-options
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect xdmcp
!
service-policy global_policy global
prompt hostname context
no call-home reporting anonymous
call-home
profile CiscoTAC-1
no active
destination address http https://tools.cisco.com/its/service/oddce/services/DDCEService
destination address email callhome@cisco.com
destination transport-method http
subscribe-to-alert-group diagnostic
subscribe-to-alert-group environment
subscribe-to-alert-group inventory periodic monthly
subscribe-to-alert-group configuration periodic monthly
subscribe-to-alert-group telemetry periodic daily
- Labels:
-
NGFW Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-16-2014 10:15 AM
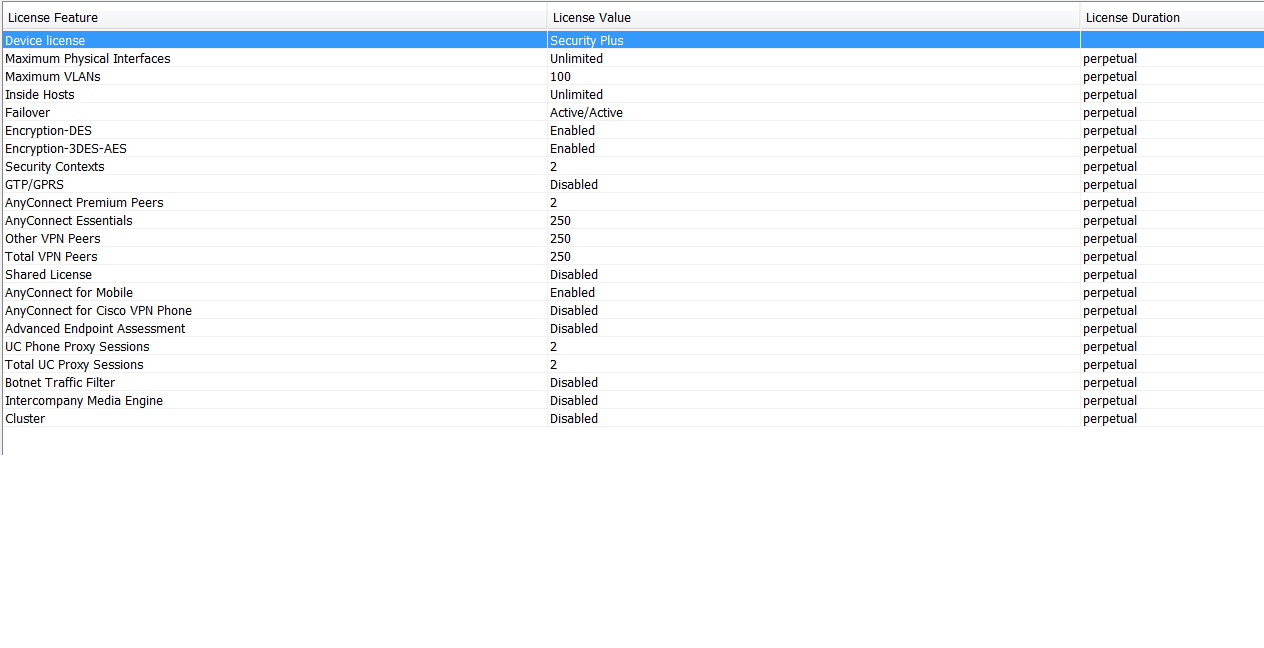
Do you have a security plus license activated? That's required on a 5510 to allow traffic through the box to the management interface as you are attempting with your configuration.
(Note that the newer X series do not allow this at all.)
Other than that it appears pretty good (your access-list entries "permit ip any any" make the following ACEs ineffective - I assume you have those in for troubleshooting).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-16-2014 10:27 AM
Sorry for the dumb question but how do I check?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-16-2014 10:32 AM
I think this is it?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-16-2014 11:19 AM
I changed the Intefaces as follows:
!
interface Ethernet0/3
description LegacyLAN 192.168.119.X/24
nameif LegacyLAN
security-level 100
ip address 192.168.119.1 255.255.255.0
no shut
!
interface Management0/0
description Guest Wireless
nameif GuestWireless
security-level 75
ip address 10.132.11.1 255.255.255.0
no shut
!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-16-2014 11:48 AM
Yes you are correct that you found a display that verifies that you do have the Security Plus license.
You tell us that you changed it around so that the Legacy LAN is no longer on the Management Interface. But you do not tell us if this change made any difference in the behavior. And I am not sure what the behavior is. Since you are asking I assume that the interfaces are not communicating. But can you give any specifics about what is going on that might help us understand the problem better? I started to ask if you see anything in the logs - but then I looked at your configuration and do not see that logging is enabled. Enabling logging might be helpful in finding the issue.
I will also offer a comment about your access lists, such as this one
access-list Inside_access_in remark Implicit rule: Permit all traffic to less secure networks
access-list Inside_access_in extended permit ip any any
access-list Inside_access_in extended permit ip object-group Tunnel_Networks object-group DM_INLINE_NETWORK_3
access-list Inside_access_in extended permit ip 10.132.3.0 255.255.255.0 192.168.119.0 255.255.255.0
If the access list starts off with a permit ip any any then all other lines are redundant and will have no effect since everything is already permitted.
HTH
Rick
[edit] I just noticed that Marvin has already commented on the access list permit any any issue. sorry for the duplication.
Rick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-16-2014 11:56 AM
Yes you are correct the I am unable to get trafic to pass between the 2 interfaces. I will enable loging. Both networks can get to the internet. Could you also give me a acccess list the will permit these network to get to the internet that is alitel more sucure. Thank you all for the continued help.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-16-2014 12:33 PM
It is interesting that both interfaces can get to the Internet but not to each other. When logging is enabled it may give us a better clue about what the problem is.
Part of the config suggests that there is (or will be) VPN configured. I do not see any VPN so far. Can you clarify this?
I suggest that we wait to discuss changes in access lists until we have resolved the problem that is preventing communication between these interfaces.
HTH
Rick
Rick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-16-2014 12:43 PM
You are correct there is a tunnel currently that functions, and we will be implemetnting client VPN also. Thank you for the help. I will post the logs shortly.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-16-2014 12:37 PM
Just use the packet tracer wizard from ASDM or the packet-tracer cli utility. It will tell you what would prevent a given flow. Use an address on the respective source and destination networks and something like tcp/80 to test.
Sent from Cisco Technical Support iPad App
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-16-2014 12:44 PM
Thank you I will try this also and post the results. Thank you for the help.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide


