- Cisco Community
- Technology and Support
- Security
- Network Security
- Re: ASA NAT Configuration
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2021 08:28 AM - edited 04-16-2021 08:30 AM
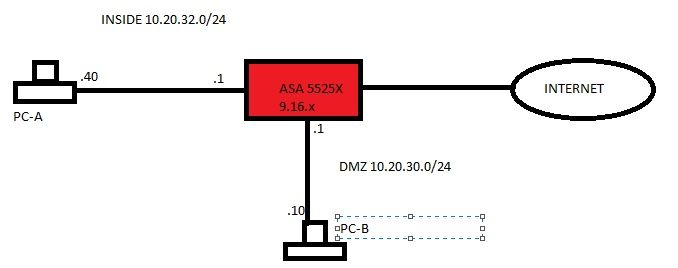
Hi all, I have an ASA 5525x with PC-A on the INSIDE network with IP address 10.20.32.40. PC-B is in DMZ with an IP address of 10.20.30.10. The security level for INSIDE is 100 and DMZ is 50. I have rules to allow PC-A to communicate with PC-B over TCP3389. I don't have any NAT configurations specified (at the moment) for translating packets from INSIDE to DMZ. When I run Wireshark capture on PC-B, I can see the IP address of PC-A communicating with it. My question, how is this possible when I don't have NAT configured between the two networks. My understanding of the way ASAs work, you must have NAT configured between two separate networks in order for the traffic to flow, for example from Inside to Outside.
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2021 08:36 AM
You don't need NAT, without a matching nat rule, traffic would be routed.
You'd normally need nat for outbound internet access, translating the private IP address to the public (routeable) IP address.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2021 08:34 AM
Ok so this is one of those where I had to put it on paper to understand it myself. I think I've figured this out (Duh!!). Packet comes into ASA, ASA performs a route lookup, and then forwards it out the DMZ interface. No NAT needed. NAT (dynamic PAT) is needed between inside and outside so the internal hosts can use the single IP address of the OUTSIDE interface!
Yeah!!!....its one of those days and I'm only on my second cup of coffee.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2021 08:36 AM
You don't need NAT, without a matching nat rule, traffic would be routed.
You'd normally need nat for outbound internet access, translating the private IP address to the public (routeable) IP address.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2021 08:46 AM
Thank you for confirming.
Cheers!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2021 08:48 AM
security level ( INSIDE 100 ) you should configure ACL rule and allow TCP
338 source PC B to destination PC A. NAT has nothing to do in this
scenario. the rules you have configure form INSIDE to DMZ are no longer
needed since ASA is stateful firewall and keep the connection table for all
traffic coming from Higher security level and allow the return traffic
then.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide