- Cisco Community
- Technology and Support
- Security
- Network Security
- Re: Cannot access ASA5510 for first time config ASDM or PING
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Cannot access ASA5510 for first time config ASDM or PING
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-31-2013 10:38 AM - edited 03-11-2019 06:51 PM
Hi
I have a fresh out the box asa5510 with 8.4 on it.
I have built these before but for some reason cannot get this one to work. I am consoled on, have applied the following config but can still not ping to or from, can not asdm, cannot http/s. Arp table shows device it tries to ping, but device trying to pping it has incomplete arp entry.
I am really stumped, does anyone have any idea?
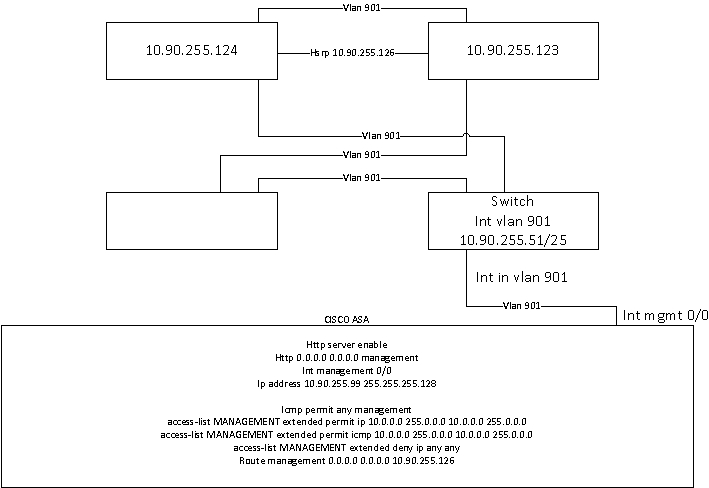
Please also see attached diagram for topology.
Thanks in advance
ciscoasa(config)# show run
: Saved
:
ASA Version 8.4(4)1
!
hostname ciscoasa
enable password 8Ry2YjIyt7RRXU24 encrypted
passwd 2KFQnbNIdI.2KYOU encrypted
names
!
interface Ethernet0/0
shutdown
no nameif
no security-level
no ip address
!
interface Ethernet0/1
shutdown
no nameif
no security-level
no ip address
!
interface Ethernet0/2
shutdown
no nameif
no security-level
no ip address
!
interface Ethernet0/3
shutdown
no nameif
no security-level
no ip address
!
interface Management0/0
nameif management
security-level 0
ip address 10.90.255.99 255.255.255.128
!
ftp mode passive
access-list MANAGEMENT extended permit ip 10.0.0.0 255.0.0.0 10.0.0.0 255.0.0.0
access-list MANAGEMENT extended permit icmp 10.0.0.0 255.0.0.0 10.0.0.0 255.0.0.0
access-list MANAGEMENT extended deny ip any any
pager lines 24
logging enable
logging console debugging
logging buffered warnings
mtu management 1500
no failover
icmp unreachable rate-limit 1 burst-size 1
icmp permit any management
no asdm history enable
arp timeout 14400
route management 0.0.0.0 0.0.0.0 10.90.255.126 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-record DfltAccessPolicy
user-identity default-domain LOCAL
http server enable
http 0.0.0.0 0.0.0.0 management
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart
telnet timeout 5
ssh timeout 5
ssh key-exchange group dh-group1-sha1
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
webvpn
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect ip-options
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect xdmcp
!
service-policy global_policy global
prompt hostname context
no call-home reporting anonymous
call-home
profile CiscoTAC-1
no active
destination address http
https://tools.cisco.com/its/service/oddce/services/DDCEService
destination address email
destination transport-method http
subscribe-to-alert-group diagnostic
subscribe-to-alert-group environment
subscribe-to-alert-group inventory periodic monthly
subscribe-to-alert-group configuration periodic monthly
subscribe-to-alert-group telemetry periodic daily
Cryptochecksum:79dc4cfc6161dcbd01a016ad9a2a2ca5
: end
%ASA-7-111009: User 'enable_15' executed cmd: show running-config
ciscoasa(config)#
- Labels:
-
NGFW Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-31-2013 10:46 AM
Hi,
I can't see any command that defines the ASDM image used on the ASA Flash memory
I mean this command
asdm image flash:/asdm-xxx.bin
This is atleast one reason the ASDM wont work. Though it would seem there is some other problem if you cant see ARP on the other end. I am not sure about the ICMP.
By default the interfaces should allow ICMP if there are no "icmp" configurations configured on the ASA.
- Jouni
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-31-2013 10:48 AM
I think that will be set when i get to http and download the image then connect first time. Thing is, I cannot connect at all.... not even for the first browse to the page http://10.90.255.99/admin
You will see I have openned up access, the pc I am trying to reach it from reaches the defult gateway and the default gateway and the management machine can both ping the switch that it is attached to and has an ip in the same vlan.
And thank you very much for taking the time to read and respond
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-31-2013 11:05 AM
Hi,
Actually didnt know that the ASA would still allow ASDM access without configuring that. Though I dont personally use ASDM other than for monitoring and some changes to VPN settings.
It seems strange to me that the there is an incomplete ARP table entry. To my understanding this was on the management host but the ASA had an ARP table entry for the host?
Have any of the previously used ASAs used the same software level as this one? Could there be some bug? Could you for example try booting it up with 8.4(5)?
I guess you could also try configuring a capture for ARP
capture ARP-CAP ethernet-type arp interface management
Then use
show capture ARP-CAP
While testing traffic
- Jouni
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-31-2013 11:27 AM
Very strange. I have nothing in the capture if I ping from the attached switch (Nexus 2k attached to Nexus 5K) which has a vlan interface in the same vlan and subnet, but if i ping from the firewall to the switch ip address, i just have whohas entries.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-31-2013 11:54 AM
Hi,
So no ARP request is even getting through to the ASA management interface but the ASA is still be to ARP for the destination IP address of the ICMP and receive the reply for that ARP?
Have you tried to attach a PC directly to the management port and seeing if it makes any difference to the problem with the ARP?
- Jouni
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-01-2013 03:51 PM
Hi,
In this configuration:
interface Management0/0
nameif management
security-level 0
ip address 10.90.255.99 255.255.255.128
!
!
access-list MANAGEMENT extended permit ip 10.0.0.0 255.0.0.0 10.0.0.0 255.0.0.0 // ACE1
access-list MANAGEMENT extended permit icmp 10.0.0.0 255.0.0.0 10.0.0.0 255.0.0.0 // ACE2
access-list MANAGEMENT extended deny ip any any // ACE3
In ACE1 the network 10.0.0.0/8 in the destination is not in the same network with 10.90.255.0/25 (MGMT interface)
Can you try these ACEs:
access-list MANAGEMENT extended permit ip 10.0.0.0 255.0.0.0 10.90.255.0 255.255.255.128
access-list MANAGEMENT extended permit icmp 10.0.0.0 255.0.0.0 10.90.255.0 255.255.255.128
access-list MANAGEMENT extended deny ip any any
I agree with Jouni, in first time use a PC directly to the MGMT interface.
and use the clear arp command to clear the ARP cache
Best regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-02-2013 12:31 AM
Hello B. Belhad,
Just to add.
The ACL is okay as it's matching and permiting the entire 10.0.0/8 space which covers the Customer's managment interface.
Sorry if I miss this but what happens if you ping from the SVI interface on the switch?
Do you see any packet reaching the ASA (Even ARP queries )?
Do you see anything?
Let me know,
Regards,
Senior Network Security and Core Specialist
CCIE #42930, 2xCCNP, JNCIP-SEC
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide





