- Cisco Community
- Technology and Support
- Security
- Network Security
- Re: Cisco ASA isolate inside clients
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-29-2020 06:46 AM
Hello Cisco community! 🙂
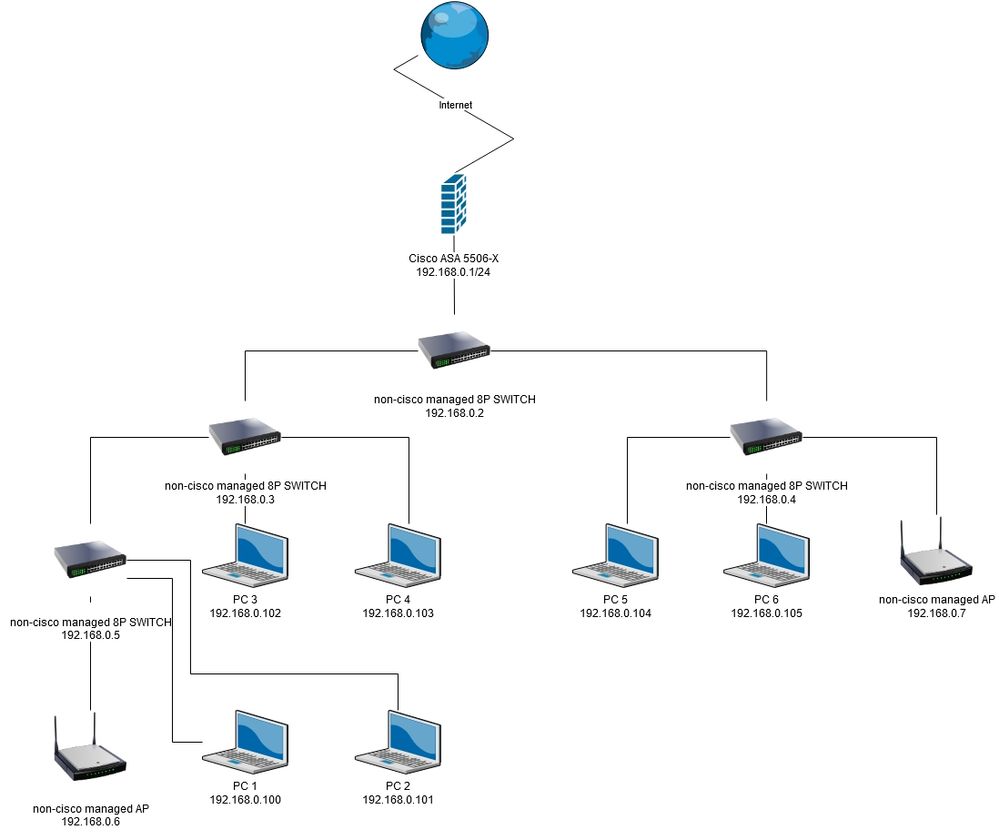
I'm facing problem which I can't solve for few days so maybe you guys can help. I have Cisco ASA 5506 with network structure like on attached diagram. I have one "inside" network 192.168.0.0/24. My goal is to isolate all internal clients (PC1,PC2,AP clients) that they couldn't "talk" to each other, but they can go to outside (internet). I don't want to create separate vlans on ASA for every client and aggregate it to selected switched ports (my switches has ability IEEE 802.1Q VLAN tagging), because I need all clients to be in one network for site-to-site connection with our business partner. I have tried to add ACL rules like this:
access-list INS extended deny ip any 192.168.0.0 255.255.255.0 access-list INS extended permit ip any any access-group INS in interface inside
but it doesn't change anything. I also checked logs to see internal traffic, but it looks like ASA didn't get this traffic.
Do you have any idea how should I achieve my goal?
Have a nice day!
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-29-2020 07:43 AM
If you have Cisco switch, you may use 'private vlan' to do what you want. Other brands switch may have the similar feature, you got to have a check.
Alternatively, you will need to deploy the host based firewall (e.g. windows firewall) to isolate the client within the same broadcast domain.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-29-2020 07:43 AM
If you have Cisco switch, you may use 'private vlan' to do what you want. Other brands switch may have the similar feature, you got to have a check.
Alternatively, you will need to deploy the host based firewall (e.g. windows firewall) to isolate the client within the same broadcast domain.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-01-2020 08:16 AM
Hi,
Thanks for your reply. 🙂
I wasn't sure if internal traffic goes through ASA firewall, so thanks for clarify.
I was thinking about host based firewalls, but in my case it is impossible to deploy, because in network sometimes are temporary PCs and I don't have physical access to them.
I'll try with private vlans. I'm not sure if my switches has this feature, so probably I'll change them.
Thanks again!
Have a nice day!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide