- Cisco Community
- Technology and Support
- Security
- Network Security
- Re: Cisco FPR 1010 AnyConnect Can not Access Remote Internal LAN
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Cisco FPR 1010 AnyConnect Can not Access Remote Internal LAN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 06:22 AM - edited 02-21-2020 09:54 AM
Hello,
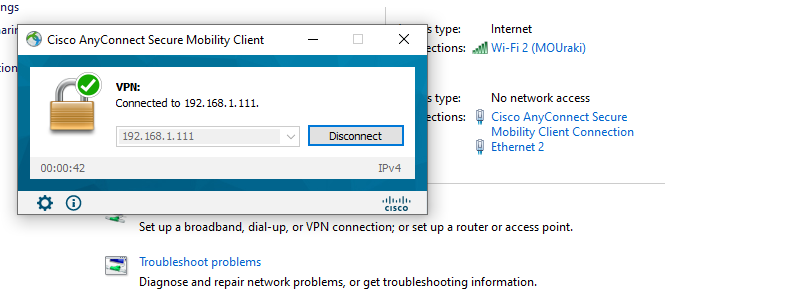
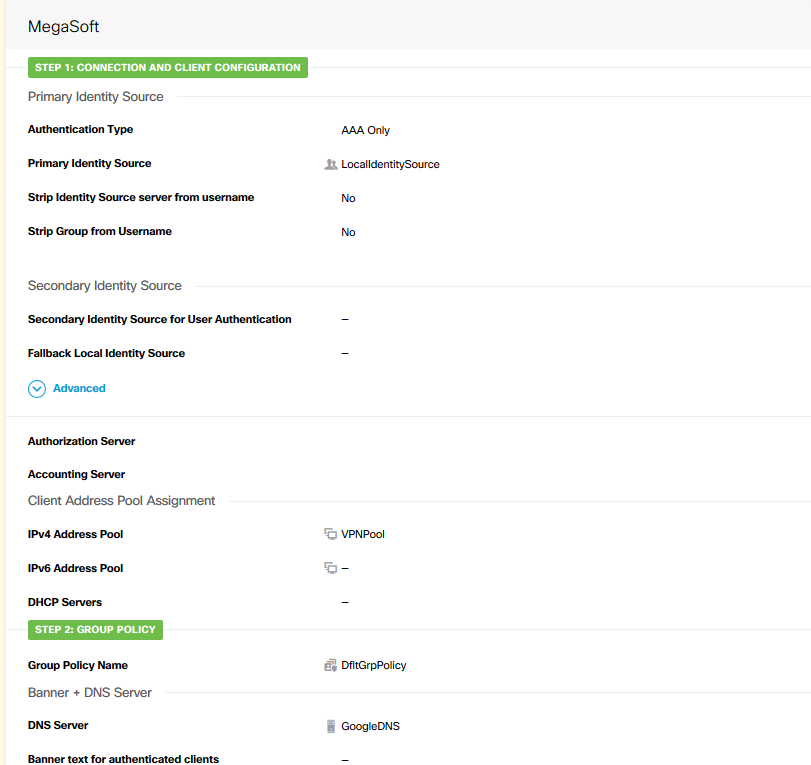
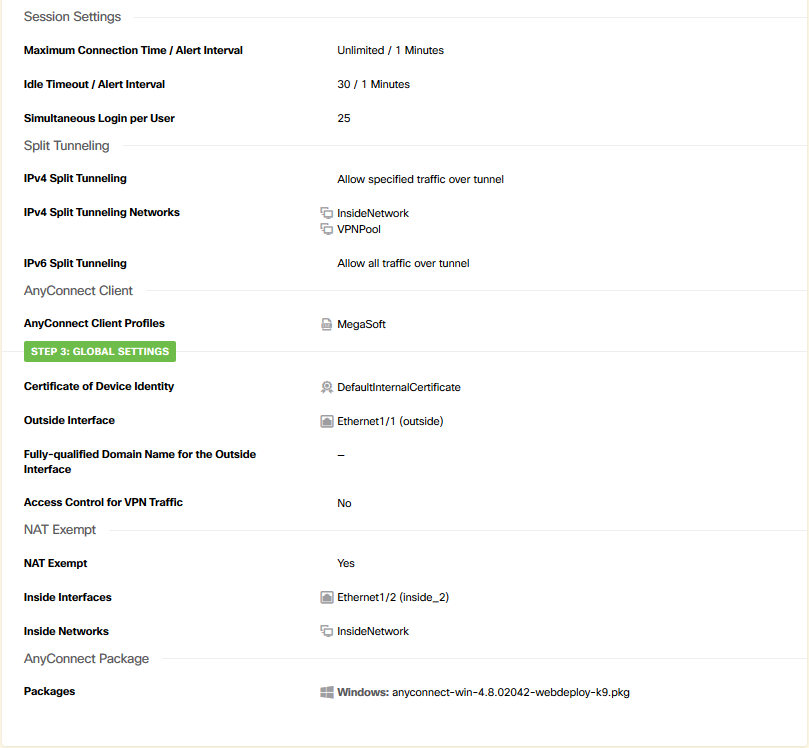
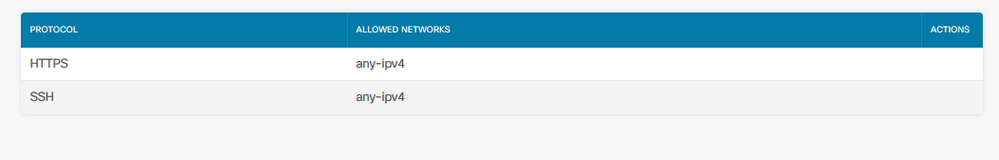
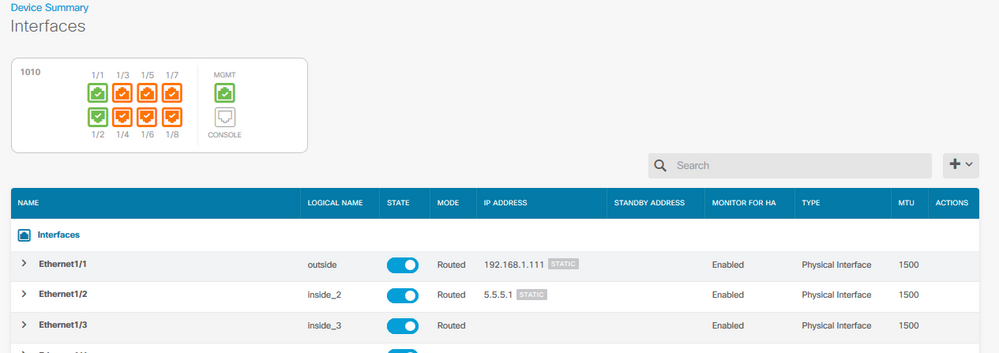
am using FBR 1010 to Configure AnyConnect Remote Access, on my test lap i used 192.168.1.0/24 as outside, and 5.5.5.0/24 as Inside, FW IP is 5.5.5.1 and outside VPN IP is 192.168.1.111
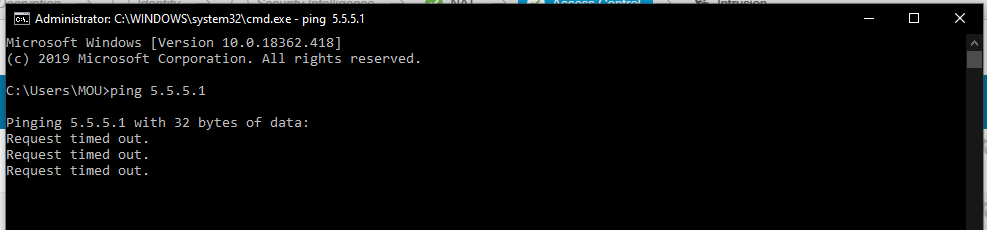
i connected VPN Client and i can access internet but i can not ping or https://5.5.5.1, any Help???
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 06:51 AM
That's not possible. When you connect to the FTD via Remote Access VPN your traffic enters the FTD from the outside interface, by design you cannot ping the FTD/ASA's far interface, in this instance the inside interface. You should test connectivity by pinging through the FTD to a device behind the firewall, not the firewall itself.
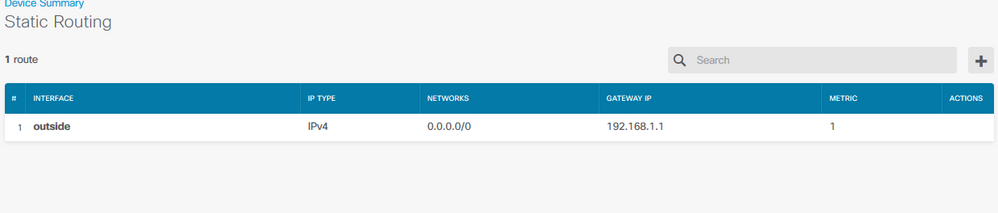
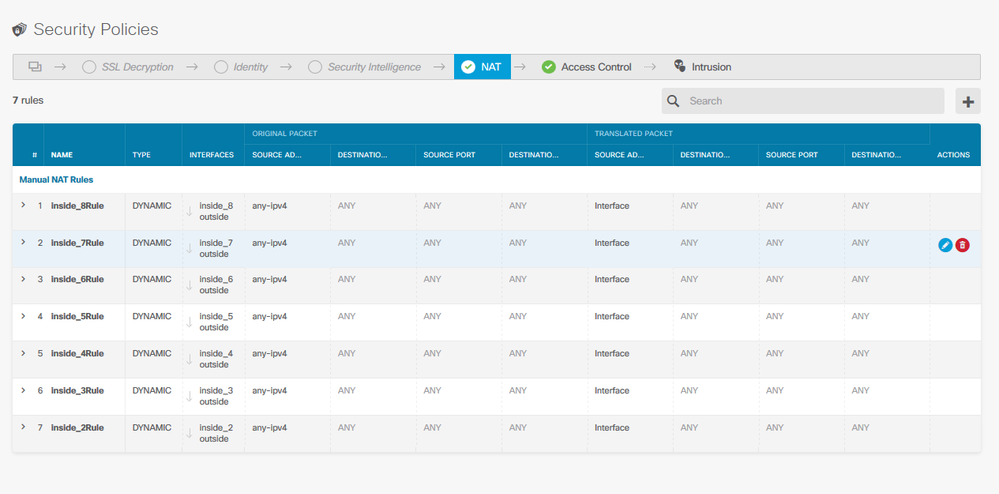
Aside from that it doesn't look like you have a NAT exemption rule defined. You need to define a NAT rule from that does not NAT traffic your inside network to your RAVPN IP Pool.
HTH
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 10:43 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 12:18 PM
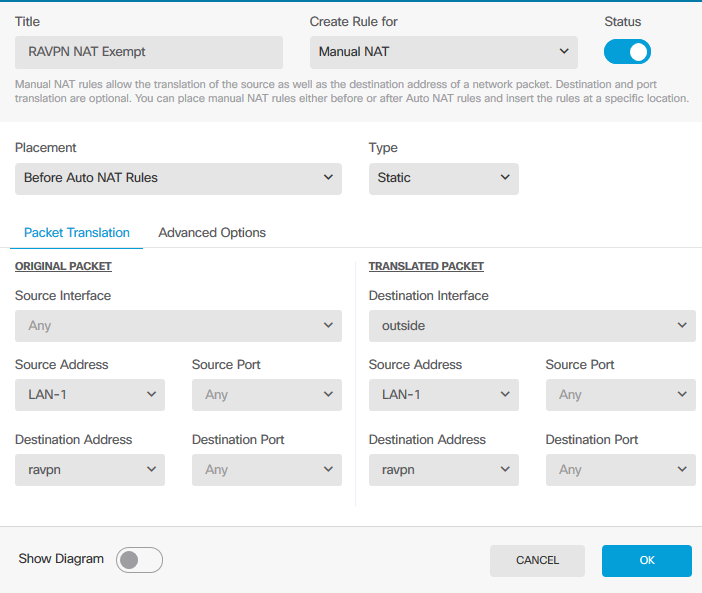
You rule should ressemble something like this:-
AND you need to ensure this NAT exemption rule is above your current rule #1, as at the moment your traffic from inside_2 will be natted on the outside interface.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 01:19 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 01:22 PM - edited 02-12-2020 01:26 PM
Provide the output of "show vpn-sessiondb detail anyconnect" and "show nat detail"
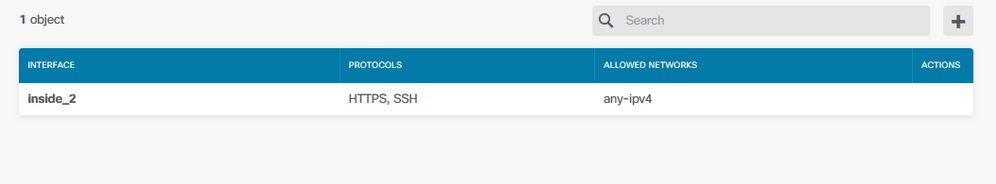
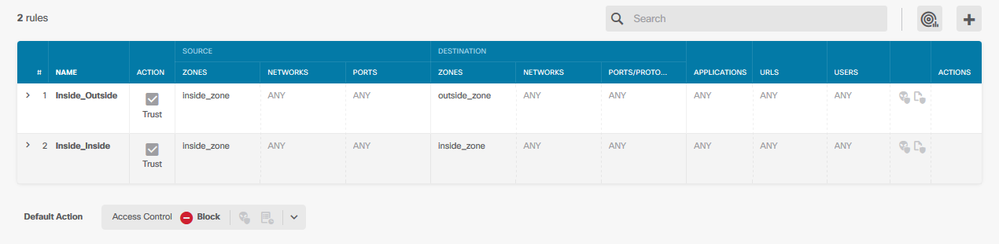
EDIT: You Firewall rule above doesn't permit trafic from outside to inside. All RAVPN traffic is sourced from outside, so you need to explictly permit traffic to inside.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 02:26 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 02:43 PM - edited 02-12-2020 02:47 PM
You needed to update your FIREWALL rule in the Access Control Policy, not the nat rule. The NAT rule you had previously would have sufficed, you need to change it back. When configured correctly the output of the NAT Exemption rule from the CLI would look like this:
"nat (inside_2,outside) source static InsideNetwork InsideNetwork destination static VPNPool VPNPool no-proxy-arp" - ensure it's the top nat rule.
InsideNetwork = inside_2 interface and VPNPool = outside interface, you need to ensure the nat rules are firewall rules reflect the correct source/destination interface.
Change your NAT rule back and amend the firewall rule, permitting traffic between the VPNPool and InsideNetwork and another permitting traffic from InsideNetwork to VPNPool.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-13-2020 12:11 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-13-2020 07:39 AM
Provide the output of "route print" from your the AnyConnect client computer, once connected to the VPN
Provide the output of "show nat detail" and "show vpn-sessiondb detail anyconnect" from the FTD
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 02:27 PM
> show nat detail
Manual NAT Policies (Section 1)
1 (outside) to (outside) source static VPNPool VPNPool destination static InsideNetwork InsideNetwork
translate_hits = 0, untranslate_hits = 0
Source - Origin: 10.10.10.0/24, Translated: 10.10.10.0/24
Destination - Origin: 5.5.5.0/24, Translated: 5.5.5.0/24
2 (outside) to (inside_2) source static VPNPool VPNPool destination static InsideNetwork InsideNetwork
translate_hits = 0, untranslate_hits = 0
Source - Origin: 10.10.10.0/24, Translated: 10.10.10.0/24
Destination - Origin: 5.5.5.0/24, Translated: 5.5.5.0/24
3 (inside_2) to (outside) source dynamic any-ipv4 interface
translate_hits = 186, untranslate_hits = 333
Source - Origin: 0.0.0.0/0, Translated: 192.168.3.111/24
Auto NAT Policies (Section 2)
1 (nlp_int_tap) to (inside_2) source static nlp_server_0_http_intf3 interface service tcp https https
translate_hits = 0, untranslate_hits = 102
Source - Origin: 169.254.1.3/32, Translated: 5.5.5.1/24
Service - Protocol: tcp Real: https Mapped: https
2 (nlp_int_tap) to (inside_2) source static nlp_server_0_ssh_intf3 interface service tcp ssh ssh
translate_hits = 0, untranslate_hits = 0
Source - Origin: 169.254.1.3/32, Translated: 5.5.5.1/24
Service - Protocol: tcp Real: ssh Mapped: ssh
3 (nlp_int_tap) to (diagnostic) source dynamic nlp_client_0_intf10 interface
translate_hits = 0, untranslate_hits = 0
Source - Origin: 169.254.1.3/32, Translated: 0.0.0.0/32
4 (nlp_int_tap) to (outside) source dynamic nlp_client_0_intf2 interface
translate_hits = 311, untranslate_hits = 101
Source - Origin: 169.254.1.3/32, Translated: 192.168.3.111/24
5 (nlp_int_tap) to (inside_2) source dynamic nlp_client_0_intf3 interface
translate_hits = 0, untranslate_hits = 0
Source - Origin: 169.254.1.3/32, Translated: 5.5.5.1/24
6 (nlp_int_tap) to (inside_3) source dynamic nlp_client_0_intf4 interface
translate_hits = 0, untranslate_hits = 0
Source - Origin: 169.254.1.3/32, Translated: 0.0.0.0/32
7 (nlp_int_tap) to (inside_4) source dynamic nlp_client_0_intf5 interface
translate_hits = 0, untranslate_hits = 0
Source - Origin: 169.254.1.3/32, Translated: 0.0.0.0/32
8 (nlp_int_tap) to (inside_5) source dynamic nlp_client_0_intf6 interface
translate_hits = 0, untranslate_hits = 0
Source - Origin: 169.254.1.3/32, Translated: 0.0.0.0/32
9 (nlp_int_tap) to (inside_6) source dynamic nlp_client_0_intf7 interface
translate_hits = 0, untranslate_hits = 0
Source - Origin: 169.254.1.3/32, Translated: 0.0.0.0/32
10 (nlp_int_tap) to (inside_7) source dynamic nlp_client_0_intf8 interface
translate_hits = 0, untranslate_hits = 0
Source - Origin: 169.254.1.3/32, Translated: 0.0.0.0/32
11 (nlp_int_tap) to (inside_8) source dynamic nlp_client_0_intf9 interface
translate_hits = 0, untranslate_hits = 0
Source - Origin: 169.254.1.3/32, Translated: 0.0.0.0/32
12 (nlp_int_tap) to (diagnostic) source dynamic nlp_client_0_ipv6_intf10 interface ipv6
translate_hits = 0, untranslate_hits = 0
Source - Origin: fd00:0:0:1::3/128, Translated:
13 (nlp_int_tap) to (outside) source dynamic nlp_client_0_ipv6_intf2 interface ipv6
translate_hits = 0, untranslate_hits = 0
Source - Origin: fd00:0:0:1::3/128, Translated:
14 (nlp_int_tap) to (inside_2) source dynamic nlp_client_0_ipv6_intf3 interface ipv6
translate_hits = 0, untranslate_hits = 0
Source - Origin: fd00:0:0:1::3/128, Translated:
15 (nlp_int_tap) to (inside_3) source dynamic nlp_client_0_ipv6_intf4 interface ipv6
translate_hits = 0, untranslate_hits = 0
Source - Origin: fd00:0:0:1::3/128, Translated:
16 (nlp_int_tap) to (inside_4) source dynamic nlp_client_0_ipv6_intf5 interface ipv6
translate_hits = 0, untranslate_hits = 0
Source - Origin: fd00:0:0:1::3/128, Translated:
17 (nlp_int_tap) to (inside_5) source dynamic nlp_client_0_ipv6_intf6 interface ipv6
translate_hits = 0, untranslate_hits = 0
Source - Origin: fd00:0:0:1::3/128, Translated:
18 (nlp_int_tap) to (inside_6) source dynamic nlp_client_0_ipv6_intf7 interface ipv6
translate_hits = 0, untranslate_hits = 0
Source - Origin: fd00:0:0:1::3/128, Translated:
19 (nlp_int_tap) to (inside_7) source dynamic nlp_client_0_ipv6_intf8 interface ipv6
translate_hits = 0, untranslate_hits = 0
Source - Origin: fd00:0:0:1::3/128, Translated:
20 (nlp_int_tap) to (inside_8) source dynamic nlp_client_0_ipv6_intf9 interface ipv6
translate_hits = 0, untranslate_hits = 0
Source - Origin: fd00:0:0:1::3/128, Translated:
Manual NAT Policies (Section 3)
1 (inside_2) to (outside) source dynamic InsideNetwork interface
translate_hits = 0, untranslate_hits = 0
Source - Origin: 5.5.5.0/24, Translated: 192.168.3.111/24
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 02:30 PM
> show vpn-sessiondb detail anyconnect
Session Type: AnyConnect Detailed
Username : user Index : 3
Assigned IP : 10.10.10.1 Public IP : 192.168.3.61
Protocol : AnyConnect-Parent SSL-Tunnel
License : AnyConnect Premium
Encryption : AnyConnect-Parent: (1)none SSL-Tunnel: (1)AES-GCM-256
Hashing : AnyConnect-Parent: (1)none SSL-Tunnel: (1)SHA384
Bytes Tx : 15942 Bytes Rx : 2893
Pkts Tx : 12 Pkts Rx : 34
Pkts Tx Drop : 0 Pkts Rx Drop : 0
Group Policy : DfltGrpPolicy Tunnel Group : MegaSoft
Login Time : 22:29:01 UTC Wed Feb 12 2020
Duration : 0h:00m:08s
Inactivity : 0h:00m:00s
VLAN Mapping : N/A VLAN : none
Audt Sess ID : c0a8036f000030005e447c2d
Security Grp : none Tunnel Zone : 0
AnyConnect-Parent Tunnels: 1
SSL-Tunnel Tunnels: 1
AnyConnect-Parent:
Tunnel ID : 3.1
Public IP : 192.168.3.61
Encryption : none Hashing : none
TCP Src Port : 50508 TCP Dst Port : 443
Auth Mode : userPassword
Idle Time Out: 30 Minutes Idle TO Left : 29 Minutes
Client OS : win
Client OS Ver: 10.0.18362
Client Type : AnyConnect
Client Ver : Cisco AnyConnect VPN Agent for Windows 4.8.02042
Bytes Tx : 7971 Bytes Rx : 0
Pkts Tx : 6 Pkts Rx : 0
Pkts Tx Drop : 0 Pkts Rx Drop : 0
SSL-Tunnel:
Tunnel ID : 3.2
Assigned IP : 10.10.10.1 Public IP : 192.168.3.61
Encryption : AES-GCM-256 Hashing : SHA384
Ciphersuite : ECDHE-RSA-AES256-GCM-SHA384
Encapsulation: TLSv1.2 TCP Src Port : 50514
TCP Dst Port : 443 Auth Mode : userPassword
Rekey Int (T): 240 Seconds Rekey Left(T): 237 Seconds
Idle Time Out: 30 Minutes Idle TO Left : 30 Minutes
Client OS : Windows
Client Type : SSL VPN Client
Client Ver : Cisco AnyConnect VPN Agent for Windows 4.8.02042
Bytes Tx : 7971 Bytes Rx : 2893
Pkts Tx : 6 Pkts Rx : 34
Pkts Tx Drop : 0 Pkts Rx Drop : 0
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide