Hello Everyone,
I hope you are all doing well, despite whats going on with the pandemic.
Anyways, I was trying to improve the Host Profile quality exploring several alternatives. Nmap, API, etc.
At this time I focused on nmimport.pl and was able to achieve the basics; addition, removal, OS, protocols, Third-Party Product Maps, etc.
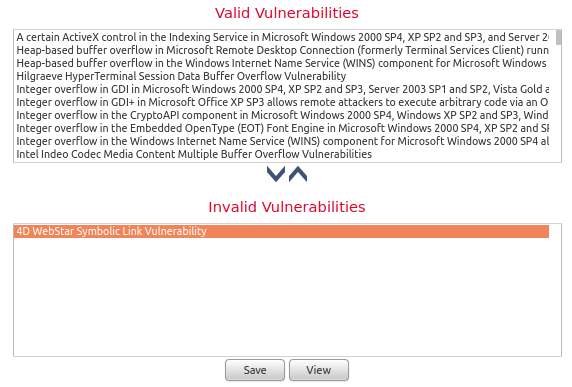
What I was trying next is Vulnerabilities. To set which ones are Valid and Invalid.
So far I was playing with "SetValidVuln" y "SetInvalidVuln" but neither had any effect that I could see.
My hope was being able to move vulnerabilities from Valid to Invalid as we do manually.
Very briefly, according to the documentation, one of the parameters for either command is "vuln_id". And "vuln_id" can be a "Valid Cisco vulnerability IDs", or "mapped third-party vulnerability IDs".
I was kind of able to create a mapping, but I'm more interested in finding the Cisco vulnerability IDs to natively and directly validate/invalidate vulnerabilities. Mapping is fine for small jobs.
Neither SVID, nor CVE ID worked as written in FMC.
Nmap doesn't work for me all that consistently. Sometimes it takes too long, other times the collection is poor, and, most shockingly, brief-but-notable traffic interruption took place while running.
API, I'm no expert so would rather have that as a last resort.
Lastly, is there a tool to parse and format CSV files to make them suitable for the nmimport.pl?
If anyone has a better approach, and care to share some details, I'd appreciate it.
Thank you!
Regards
Peter