- Cisco Community
- Technology and Support
- Security
- Network Security
- Re: Inter-VLAN routing on an ASA 5505 (9.1)
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Inter-VLAN routing on an ASA 5505 (9.1)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2014 10:12 PM - edited 03-11-2019 08:44 PM
Hi,
I am trying to setup inter-VLAN routing on an ASA 5505 so that my Server VLAN can talk to my Data VLAN. Both VLANs/subnets will need to be able to reach the Internet (at least until I get VPNs working so that I can remote into my server VLAN, then I will close off Internet connectivity to the servers). Currently I have dynamic NAT setup from my data VLAN and Internet is coming through just fine.
Servers will be on VLAN 3 (subnet 10.0.1.0/24), and Data will be VLAN 11 (10.10.11.0/24). I would like the default gateway to be set as 10.0.1.2 for the Server VLAN since that is how it is statically configured on each of my servers.
What do I need to do to get my VLANs talking internally? Is it a matter of simply configuring SVI's for each VLAN, and then setting each SVI as the default gateway for that VLAN/subnet, or is it more involved than that?
I have experience configuring inter-VLAN routing on 3560 (switches), but am new to the ASA platform, so any help with this would be greatly appreciated.
Thanks!
Austin
- Labels:
-
NGFW Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2014 11:33 PM
Hi,
I imagine there are some additional switches involved in the network in addition to the ASA or is the ASA the only device in your network (in addition to the hosts/servers)?
If your only have ASA5505 then it would naturally act as the gateway for the networks and the Vlan IDs would only have local significance.
If you have a switch network behind your ASA5505 and the ASA5505 is licensed with Security Plus license then you would be able to configure a Trunk between the ASA and the switches if needed and use the Vlan ID of the ASA interfaces in the rest of the networks. Naturally again the gateway of the subnets should be on the ASA.
If you have devices on your network already configured for specific default gateway then naturally you can configure that IP address on the ASA Vlan interface.
To be honest there is not many things to do with the ASA to get traffic going between 2 networks
- Create interface Vlan
- Configure "nameif" to name the interface, configure "ip address" of the interface
- Attach the Vlan ID of the Vlan interface to the required physical ports as Access Mode ports or if your using Trunk then on the appropriate Trunk interfaces. The physical port commands pretty much follow the IOS format but configuration options are pretty limited
- Configure interface ACLs to allow and/or block the required traffic. Its best to use interface ACLs from the get go as relying on "security-level" value doesnt give that many options. (By default interfaces with higher "security-level" value can connect towards network behind any lower "security-level" interface)
- Configure DHCP Server on the ASA if required for the hosts. As with the switch port configurations the DHCP is somewhat limited (Max pool size 256, 1 pool per interface, etc)
- You WONT have to configure any NAT between the local interfaces
I guess those would be the main points.
If you have a configuration on the ASA already but its not working you can share that here if you want us to have a look at it.
Hope this helps
- Jouni
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-13-2014 10:50 AM
Jouni,
Thanks for the tips.
Unfortunately I do not have a switch to work with, just the ASA. I believe a real switch will be aquired in the future as the office grows, but right now it is an office of just a few users, and they use chintzy little netgear unmanaged 16-port switches to provide more ports to users.
The ASA has a Sec+ license, so there are no issues with the number of VLANs (we won't even come close to using all 20). The reason I want to implement VLANs is that I do not want all of the users on the Data VLAN to be able to access the servers, just the developers. I also don't want traffic from the regular users to be running in the same VLAN/subnet as the servers - there is no need for this, and to me it is a security hole to have uneccessary protocols running on the Server VLAN.
I also want to do VLANs because we will most likely be running VoIP in the near furute, and I am told that it is always best practice to run voice traffic separate from data traffic. Is this correct?
I will give your suggestions a try in several hours and let you know how it goes.
Thanks,
Austin
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-15-2014 07:12 AM
Update:
So yesterday I got a chance to work on this device a little more. Here are the configurations I made:
1. Created VLAN interfaces: VLAN 1 (MGMT), VLAN 3 (SERVERS), VLAN 11 (DATA)
2. Named VLAN ints (MGMT, SERVERS, DATA)
3. Defined security levels (MGMT, SERVERS, DATA = 100)
4. Assigned IP address to ea. VLAN int
5. Configured ports as access ports
6. Permitted same security traffic (same-security-traffic permit inter-interface)
7. Configured ACL to ping from the SERVERS VLAN to the MGMT VLAN
After making these configurations, I setup a single host on Eth1 (MGMT VLAN), and another host on Eth2 (SERVERS VLAN) to do a quick test . Unfortunately I couldn't get a successful ping to go through.
I setup an ACL (SERVERS-in) that should allow ICMP traffic inbound from 10.0.1.0/24 (SERVERS VLAN/subnet) to the MGMT VLAN/subnet (10.0.2.0/24). I also setup an ACL (MGMT-in) that should allow ICMP echo replies to the SERVERS VLAN/subnet. I'm not sure if I entered something incorrectly, but I cannot get pings to go through when pinging from my host in the SERVERS VLAN to my host in the MGMT VLAN. I am wondering if I have a misconfigured ACL, or if there's something else that I missed.
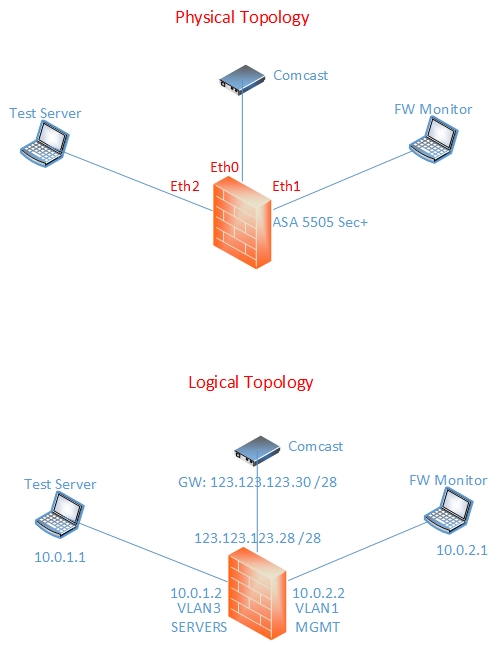
I have pasted my configs below as well as a diagram of my network. Any help would be greatly appreciated.
Thanks,
Austin
hostname cs-lans-fw
domain-name default.domain.invalid
enable password eDNDD7lBLzSPpYwe encrypted
names
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
switchport access vlan 3
!
interface Ethernet0/3
switchport access vlan 11
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
interface Vlan1
description management interface
nameif MGMT
security-level 100
ip address 10.0.2.2 255.255.255.0
!
interface Vlan2
description Outside interface
nameif outside
security-level 0
# Real IP replaced with fake IP
ip address 123.123.123.28 255.255.255.240
!
interface Vlan3
nameif SERVERS
security-level 100
ip address 10.0.1.2 255.255.255.0
!
interface Vlan11
nameif DATA
security-level 100
ip address 10.10.11.2 255.255.255.0
!
ftp mode passive
dns domain-lookup outside
dns server-group DefaultDNS
name-server 8.8.8.8
name-server 208.67.222.222
name-server 75.75.75.75
domain-name default.domain.invalid
same-security-traffic permit inter-interface
object network VNC
host 10.0.2.1
object service TCP_5900
service tcp source eq 5900
object network MGMT-subnet
subnet 10.0.2.0 255.255.255.0
object network SERVERS-subnet
subnet 10.0.1.0 255.255.255.0
object network DATA-subnet
subnet 10.10.11.0 255.255.255.0
object-group service Internet-udp udp
description Standard UDP Internet services
port-object eq domain
port-object eq ntp
object-group service Internet-tcp tcp
description Standard TCP Internet services
port-object eq www
port-object eq https
port-object eq domain
access-list SERVERS-in remark -=[Access lists to allow Internet TCP/UDP outgoing packets from SERVERS interface, and permit ICMP echo requests to MGMT]=-
access-list SERVERS-in extended permit udp 10.0.1.0 255.255.255.0 any object-group Internet-udp
access-list SERVERS-in extended permit tcp 10.0.1.0 255.255.255.0 any object-group Internet-tcp
access-list SERVERS-in extended permit icmp 10.0.1.0 255.255.255.0 10.0.2.0 255.255.255.0
access-list outside-in extended permit tcp any host 10.0.2.1 eq 5900
access-list DATA-in remark -=[Access lists to allow Internet TCP/UDP outgoing packets from DATA interface]=-
access-list DATA-in extended permit udp 10.10.11.0 255.255.255.0 any object-group Internet-udp
access-list DATA-in extended permit tcp 10.10.11.0 255.255.255.0 any object-group Internet-tcp
access-list MGMT-in remark -=[Access lists to allow Internet TCP/UDP outgoing packets from MGMT interface, and permit ICMP echo replies to SERVERS]=-
access-list MGMT-in extended permit udp 10.0.2.0 255.255.255.0 any object-group Internet-udp
access-list MGMT-in extended permit tcp 10.0.2.0 255.255.255.0 any object-group Internet-tcp
access-list MGMT-in extended permit icmp 10.0.2.0 255.255.255.0 10.0.1.0 255.255.255.0 echo-reply
access-list MGMT-in extended permit icmp 10.0.2.0 255.255.255.0 10.0.1.0 255.255.255.0
pager lines 24
logging asdm informational
mtu MGMT 1500
mtu outside 1500
mtu SERVERS 1500
mtu DATA 1500
no failover
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
nat (MGMT,outside) source static VNC interface service TCP_5900 TCP_5900
!
object network MGMT-subnet
nat (MGMT,outside) dynamic interface
object network SERVERS-subnet
nat (SERVERS,outside) dynamic interface
object network DATA-subnet
nat (DATA,outside) dynamic interface
access-group MGMT-in in interface MGMT
access-group outside-in in interface outside
access-group SERVERS-in in interface SERVERS
access-group DATA-in in interface DATA
route outside 0.0.0.0 0.0.0.0 173.167.15.30 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-record DfltAccessPolicy
user-identity default-domain LOCAL
aaa authentication http console LOCAL
aaa authentication ssh console LOCAL
http server enable
http 10.0.2.0 255.255.255.0 MGMT
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart
crypto ipsec security-association pmtu-aging infinite
crypto ca trustpool policy
telnet timeout 5
ssh 10.0.2.0 255.255.255.0 MGMT
ssh timeout 60
ssh key-exchange group dh-group1-sha1
console timeout 0
dhcpd address 10.10.11.10-10.10.11.25 DATA
dhcpd dns 8.8.8.8 interface DATA
!
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
webvpn
anyconnect-essentials
username user password wwmM/Ms2vq88kRD4 encrypted
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect rtsp
inspect esmtp
inspect sqlnet
inspect skinny
inspect sunrpc
inspect xdmcp
inspect sip
inspect netbios
inspect tftp
inspect ip-options
!
service-policy global_policy global
prompt hostname context
no call-home reporting anonymous
Cryptochecksum:6181739549f3cc2a9f58eafb69c03b30
: end
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-15-2014 07:37 AM
What license do you have installed on the ASA? As Jouni has mentioned you need to have a security plus license to get multiple internal VLANs to work on the 5505.
Did you check the logs to see if there were any drop entries?
Another thing you can try is to use the packet tracer to simulate a packet passing through the ASA.
packet-tracer input MGMT tcp 10.0.2.10 12345 10.0.1.10 80 detail
packet-tracer input SERVERS tcp 10.0.1.10 12345 10.0.2.10 80 detail
This should give you a good idea where the packet is being dropped.
If the packet is allowed through the ASA, I suggest checking to make sure that the antivirus/firewall installed on the server or PC is turned off and then test again.
--
Please remember to rate and select a correct answer
Please remember to select a correct answer and rate helpful posts
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-15-2014 08:21 AM
Marius,
This is a Sec+ (verified with the show version command).
Thanks for the PT suggestion. Was not aware of this tool. Will have to give it a try.
I know Jouni and the configuration guides say that there is no need to setup NAT, but should I give a static NAT a try to see if that does it? Do I need to setup additional routing rules? These are really the only two things I can think of that would cause this issue, unless my ACE's are incorrect, which I don't think they are.
Thanks,
Austin
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-15-2014 08:28 AM
Hi,
I would suggest adding ICMP Inspection on the ASA always so you only have to permit the initial Echo message and the ASA will handle the Echo reply with the Inspection
Add
policy-map global_policy
class inspection_default
inspect icmp
inspect icmp error
You wont need any NAT configurations between the local interfaces nor should you have them since it doesnt really add anything to setup.
The "packet-tracer" command would tell us if configurations have problems or if the problems are somewhere else perhaps.
- Jouni
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-15-2014 08:30 AM
to get your internal subnets to talk to eachother you do not need NAT configured. The only time you NEED to configure NAT/PAT is when you are connecting to the internet (or some other situations where you have overlapping subnets).
As long as all your networks are directly connected to the ASA, that is to say that the ASA has an interface in each network, then you do not need to configure routing between these subnets as the ASA already knows about them.
Please run the packet tracer and post back the results, we will have a better understanding of what is going on then.
--
Please remember to rate and select a correct answer
Please remember to select a correct answer and rate helpful posts
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-17-2014 09:27 PM
Okay, I finally got some pings to go through from the MGMT VLAN to the SERVERS VLAN. Here is what I did:
1) Removed the ICMP ACL's
2) Re-added the ICMP ACL's and added "echo" at the end of each "permit icmp" ACE
3) Copied the running-config to the startup-config and did a reload
I have pasted the config below.
One thing that I was doing wrong during my testing was that I was trying to ping the address assigned to each VLAN interface instead of pinging the hosts on each VLAN. I discovered that the hosts were reachable, but the VLAN interfaces were not. Why would this be? I assume it's some security feature.
Also, I am puzzled by the fact that I am able to ping the public IP address of my firewall. This shouldn't be possible since there are no ACL's allowing ICMP on the outside interface. Any thoughts on this?
Since I am able to ping between VLANs, I think it's safe to say that I have inter-VLAN routing working. Now I think it's a matter of getting ACL's setup to allow users on the DATA VLAN access to hosts on the SERVERS VLAN via specific port numbers.
Thanks again for all the help.
Austin
cs-lans-fw# show run
: Saved
:
ASA Version 9.1(2)
!
hostname cs-lans-fw
domain-name default.domain.invalid
enable password eDNDD7lBLzSPpYwe encrypted
names
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
switchport access vlan 3
!
interface Ethernet0/3
switchport access vlan 11
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
interface Vlan1
description management interface
nameif MGMT
security-level 100
ip address 10.0.2.2 255.255.255.0
!
interface Vlan2
description Outside interface
nameif outside
security-level 0
ip address 123.123.123.28 255.255.255.240
!
interface Vlan3
nameif SERVERS
security-level 100
ip address 10.0.1.2 255.255.255.0
!
interface Vlan11
nameif DATA
security-level 100
ip address 10.10.11.2 255.255.255.0
!
ftp mode passive
dns domain-lookup outside
dns server-group DefaultDNS
name-server 8.8.8.8
name-server 208.67.222.222
name-server 75.75.75.75
domain-name default.domain.invalid
same-security-traffic permit inter-interface
object network VNC
host 10.0.2.1
object service TCP_5900
service tcp source eq 5900
object network MGMT-subnet
subnet 10.0.2.0 255.255.255.0
object network SERVERS-subnet
subnet 10.0.1.0 255.255.255.0
object network DATA-subnet
subnet 10.10.11.0 255.255.255.0
object-group service Internet-udp udp
description Standard UDP Internet services
port-object eq domain
port-object eq ntp
object-group service Internet-tcp tcp
description Standard TCP Internet services
port-object eq www
port-object eq https
port-object eq domain
access-list SERVERS-in remark -=[Access lists to allow Internet TCP/UDP outgoing packets from SERVERS interface]=-
access-list SERVERS-in extended permit udp 10.0.1.0 255.255.255.0 any object-group Internet-udp
access-list SERVERS-in extended permit tcp 10.0.1.0 255.255.255.0 any object-group Internet-tcp
access-list SERVERS-in extended permit icmp 10.0.1.0 255.255.255.0 10.0.2.0 255.255.255.0 echo-reply
access-list SERVERS-in extended permit icmp 10.0.1.0 255.255.255.0 10.0.2.0 255.255.255.0 echo
access-list outside-in extended permit tcp any host 10.0.2.1 eq 5900
access-list DATA-in remark -=[Access lists to allow Internet TCP/UDP outgoing packets from DATA interface]=-
access-list DATA-in extended permit udp 10.10.11.0 255.255.255.0 any object-group Internet-udp
access-list DATA-in extended permit tcp 10.10.11.0 255.255.255.0 any object-group Internet-tcp
access-list MGMT-in remark -=[Access lists to allow Internet TCP/UDP outgoing packets from MGMT interface]=-
access-list MGMT-in extended permit udp 10.0.2.0 255.255.255.0 any object-group Internet-udp
access-list MGMT-in extended permit tcp 10.0.2.0 255.255.255.0 any object-group Internet-tcp
access-list MGMT-in extended permit icmp 10.0.2.0 255.255.255.0 10.0.1.0 255.255.255.0 echo-reply
access-list MGMT-in extended permit icmp 10.0.2.0 255.255.255.0 10.0.1.0 255.255.255.0 echo
pager lines 24
logging asdm informational
mtu MGMT 1500
mtu outside 1500
mtu SERVERS 1500
mtu DATA 1500
no failover
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
nat (MGMT,outside) source static VNC interface service TCP_5900 TCP_5900
!
object network MGMT-subnet
nat (MGMT,outside) dynamic interface
object network SERVERS-subnet
nat (SERVERS,outside) dynamic interface
object network DATA-subnet
nat (DATA,outside) dynamic interface
access-group MGMT-in in interface MGMT
access-group outside-in in interface outside
access-group SERVERS-in in interface SERVERS
access-group DATA-in in interface DATA
route outside 0.0.0.0 0.0.0.0 173.167.15.30 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-record DfltAccessPolicy
user-identity default-domain LOCAL
aaa authentication http console LOCAL
aaa authentication ssh console LOCAL
http server enable
http 10.0.2.0 255.255.255.0 MGMT
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart
crypto ipsec security-association pmtu-aging infinite
crypto ca trustpool policy
telnet timeout 5
ssh 10.0.2.0 255.255.255.0 MGMT
ssh timeout 60
ssh key-exchange group dh-group1-sha1
console timeout 0
dhcpd address 10.10.11.10-10.10.11.25 DATA
dhcpd dns 8.8.8.8 interface DATA
!
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
webvpn
anyconnect-essentials
username user password wwmM/Ms2vq88kRD4 encrypted
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect rtsp
inspect esmtp
inspect sqlnet
inspect skinny
inspect sunrpc
inspect xdmcp
inspect sip
inspect netbios
inspect tftp
inspect ip-options
!
service-policy global_policy global
prompt hostname context
no call-home reporting anonymous
Cryptochecksum:8c170cbd3656a7d9cf0b104332cf162b
: end
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2014 12:48 AM
I discovered that the hosts were reachable, but the VLAN interfaces were not. Why would this be? I assume it's some security feature.
By default the ASA permits ping to the interface that traffic ingresses on. So if you are pinging from a host on the inside interface you will be able to ping the inside interface IP but will not be able to ping the DMZ interface. This is unless you have configured icmp permit
Also, I am puzzled by the fact that I am able to ping the public IP address of my firewall. This shouldn't be possible since there are no ACL's allowing ICMP on the outside interface. Any thoughts on this?
Are you pinging the public IP from a host on the inside network or are you pinging from a host on the internet?
--
Please remember to rate and select a correct answer
Please remember to select a correct answer and rate helpful posts
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2014 06:07 AM
Marius Gunnerud wrote:
...you will be able to ping the inside interface IP but will not be able to ping the DMZ interface. This is unless you have configured icmp permitDMZ where DMZ is the interface name, and IP address is the IP you are pinging from.
Marius, this makes sense. Thanks.
Are you pinging the public IP from a host on the inside network or are you pinging from a host on the internet?
I am pinging from a host on a completely remote network ("the internet").
This morning I discovered that I can ping from my host in the SERVERS VLAN to my host in the MGMT VLAN, but I cannot ping from my host in the MGMT VLAN to my host in the SERVERS VLAN. I checked my ACL's and they appear to be correct. I also disabled anti-virus/firewall on the hosts to make sure that wasn't blocking the pings, but I'm still having the issue. What would cause this?
As requested previously, here is the output of the packet tracer commands. I'm no expert in interpretting these things, but as far as I can tell there are no red flags in the output.
cs-lans-fw# packet-tracer input SERVERS tcp 10.0.1.10 12345 10.0.2.10 80 detail
Phase: 1
Type: ROUTE-LOOKUP
Subtype: input
Result: ALLOW
Config:
Additional Information:
in 10.0.2.0 255.255.255.0 MGMT
Phase: 2
Type: ACCESS-LIST
Subtype: log
Result: ALLOW
Config:
access-group SERVERS-in in interface SERVERS
access-list SERVERS-in extended permit tcp 10.0.1.0 255.255.255.0 any object-group Internet-tcp
object-group service Internet-tcp tcp
description: Standard TCP Internet services
port-object eq www
port-object eq https
port-object eq domain
Additional Information:
Forward Flow based lookup yields rule:
in id=0xcb1f4ae8, priority=13, domain=permit, deny=false
hits=11, user_data=0xc9179e20, cs_id=0x0, use_real_addr, flags=0x0, protocol=6
src ip/id=10.0.1.0, mask=255.255.255.0, port=0, tag=0
dst ip/id=0.0.0.0, mask=0.0.0.0, port=80, tag=0, dscp=0x0
input_ifc=SERVERS, output_ifc=any
Phase: 3
Type: NAT
Subtype: per-session
Result: ALLOW
Config:
Additional Information:
Forward Flow based lookup yields rule:
in id=0xcaa8c3d0, priority=0, domain=nat-per-session, deny=false
hits=52, user_data=0x0, cs_id=0x0, reverse, use_real_addr, flags=0x0, protocol=6
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0, dscp=0x0
input_ifc=any, output_ifc=any
Phase: 4
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Forward Flow based lookup yields rule:
in id=0xcb199c68, priority=0, domain=inspect-ip-options, deny=true
hits=75, user_data=0x0, cs_id=0x0, reverse, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0, dscp=0x0
input_ifc=SERVERS, output_ifc=any
Phase: 5
Type: NAT
Subtype: per-session
Result: ALLOW
Config:
Additional Information:
Reverse Flow based lookup yields rule:
in id=0xcaa8c3d0, priority=0, domain=nat-per-session, deny=false
hits=54, user_data=0x0, cs_id=0x0, reverse, use_real_addr, flags=0x0, protocol=6
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0, dscp=0x0
input_ifc=any, output_ifc=any
Phase: 6
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Reverse Flow based lookup yields rule:
in id=0xcb144fc0, priority=0, domain=inspect-ip-options, deny=true
hits=12, user_data=0x0, cs_id=0x0, reverse, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0, dscp=0x0
input_ifc=MGMT, output_ifc=any
Phase: 7
Type: FLOW-CREATION
Subtype:
Result: ALLOW
Config:
Additional Information:
New flow created with id 84, packet dispatched to next module
Module information for forward flow ...
snp_fp_tracer_drop
snp_fp_inspect_ip_options
snp_fp_tcp_normalizer
snp_fp_translate
snp_fp_adjacency
snp_fp_fragment
snp_ifc_stat
Module information for reverse flow ...
snp_fp_tracer_drop
snp_fp_inspect_ip_options
snp_fp_translate
snp_fp_tcp_normalizer
snp_fp_adjacency
snp_fp_fragment
snp_ifc_stat
Result:
input-interface: SERVERS
input-status: up
input-line-status: up
output-interface: MGMT
output-status: up
output-line-status: up
Action: allow
cs-lans-fw# packet-tracer input MGMT tcp 10.0.2.10 12345 10.0.1.10 80 detail
Phase: 1
Type: ROUTE-LOOKUP
Subtype: input
Result: ALLOW
Config:
Additional Information:
in 10.0.1.0 255.255.255.0 SERVERS
Phase: 2
Type: ACCESS-LIST
Subtype: log
Result: ALLOW
Config:
access-group MGMT-in in interface MGMT
access-list MGMT-in extended permit tcp 10.0.2.0 255.255.255.0 any object-group Internet-tcp
object-group service Internet-tcp tcp
description: Standard TCP Internet services
port-object eq www
port-object eq https
port-object eq domain
Additional Information:
Forward Flow based lookup yields rule:
in id=0xcb1d43a0, priority=13, domain=permit, deny=false
hits=3, user_data=0xc917a280, cs_id=0x0, use_real_addr, flags=0x0, protocol=6
src ip/id=10.0.2.0, mask=255.255.255.0, port=0, tag=0
dst ip/id=0.0.0.0, mask=0.0.0.0, port=80, tag=0, dscp=0x0
input_ifc=MGMT, output_ifc=any
Phase: 3
Type: NAT
Subtype: per-session
Result: ALLOW
Config:
Additional Information:
Forward Flow based lookup yields rule:
in id=0xcaa8c3d0, priority=0, domain=nat-per-session, deny=false
hits=48, user_data=0x0, cs_id=0x0, reverse, use_real_addr, flags=0x0, protocol=6
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0, dscp=0x0
input_ifc=any, output_ifc=any
Phase: 4
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Forward Flow based lookup yields rule:
in id=0xcb144fc0, priority=0, domain=inspect-ip-options, deny=true
hits=8, user_data=0x0, cs_id=0x0, reverse, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0, dscp=0x0
input_ifc=MGMT, output_ifc=any
Phase: 5
Type: NAT
Subtype: per-session
Result: ALLOW
Config:
Additional Information:
Reverse Flow based lookup yields rule:
in id=0xcaa8c3d0, priority=0, domain=nat-per-session, deny=false
hits=50, user_data=0x0, cs_id=0x0, reverse, use_real_addr, flags=0x0, protocol=6
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0, dscp=0x0
input_ifc=any, output_ifc=any
Phase: 6
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Reverse Flow based lookup yields rule:
in id=0xcb199c68, priority=0, domain=inspect-ip-options, deny=true
hits=75, user_data=0x0, cs_id=0x0, reverse, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=0, dscp=0x0
input_ifc=SERVERS, output_ifc=any
Phase: 7
Type: FLOW-CREATION
Subtype:
Result: ALLOW
Config:
Additional Information:
New flow created with id 81, packet dispatched to next module
Module information for forward flow ...
snp_fp_tracer_drop
snp_fp_inspect_ip_options
snp_fp_tcp_normalizer
snp_fp_translate
snp_fp_adjacency
snp_fp_fragment
snp_ifc_stat
Module information for reverse flow ...
snp_fp_tracer_drop
snp_fp_inspect_ip_options
snp_fp_translate
snp_fp_tcp_normalizer
snp_fp_adjacency
snp_fp_fragment
snp_ifc_stat
Result:
input-interface: MGMT
input-status: up
input-line-status: up
output-interface: SERVERS
output-status: up
output-line-status: up
Action: allow
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2014 11:05 AM
As the packet tracer shows the packet is permitted through the ASA in both direction. So regardless of which side initiates traffic, the packet should pass through. It is quite strange that you can ping from SERVER to MGMT but not the other way around. Have you made any more changes recently? If so could you post an updated runing config output please?
--
Please remember to rate and select a correct answer
Please remember to select a correct answer and rate helpful posts
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2014 09:16 PM
Marius,
No I have not made any changes to the config. I'm at a loss here. The only thing I can think of that is wrong at this point is that there is something wrong with the host on the MGMT VLAN.
I am also still wondering why the firewall is responding to external ("from the Internet") pings. This shouldn't be the case since the only traffic permitted on the outside interface is a specific port to a specific host.
Seems like there are some strange things happening here.
I'm having another sysadmin take a look at this thing to see if he can get things sorted out.
Thanks for all of the help. I will post back once we figure out what's happening.
Austin
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-19-2014 01:11 AM
I suggest rebooting the ASA. and then test again. There seems to be reminents of past config present even though they do not show up in the configuration. You should not be able to ping the outside interface. And as per packet tracer traffic should be allowed across the ASA. Perhaps there is an issue with the MGMT host in this case but as for pinging the outside interface, that is just outright strange.
Schedule a maintenance window, save your configuration and then reboot the ASA.
--
Please remember to rate and select a correct answer
Please remember to select a correct answer and rate helpful posts
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-23-2014 02:16 PM
Marius,
I did a reboot, but that didn't solve the issue. I enabled logging later on and noticed that I was getting a "failed to locate egress interface" message when pinging from the DATA VLAN to the SERVERS VLAN. What does that even mean?
I didn't have anymore time to mess with this configuration, so I went ahead and restored the device to factory defaults, and I just kept one VLAN for the inside and one VLAN for the outside. Now I'm trying to setup a remote access IPSEC VPN, and I'm having issues pinging hosts on the inside of the firewall... I'm starting to wonder if I have a bad piece of equipment.
Thanks for your efforts!
Austin
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide




