- Cisco Community
- Technology and Support
- Security
- Network Security
- NAT on multihoming edge ASA
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
NAT on multihoming edge ASA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-17-2011 12:16 AM - edited 03-11-2019 02:12 PM
hello
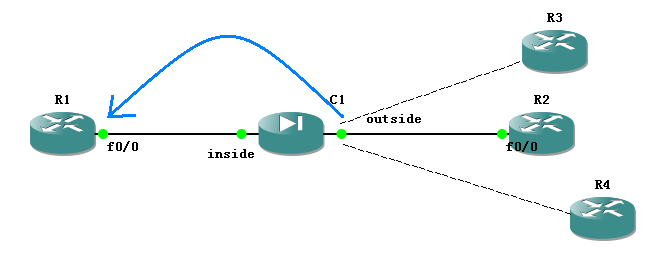
as following topology showing, we have multiple public addresses from different ISP. now we need map those public ( inside global ) addresses to single private ( inside local ) address, which assigned to a server, so that user from internet can reach this server.
the public address is 7.7.7.7, 8.8.8.8, 9.9.9.9.
the nat config is:
static (outside,inside) interface 20.0.0.200 netmask 255.255.255.255
after user ping those pubic addresses, the show nat outside displayed that the nat seems work well
ciscoasa(config)# sh nat outside
match ip outside host 20.0.0.200 inside any
static translation to 10.0.0.2
translate_hits = 20, untranslate_hits = 0
but ping still failed
p.s., i have configured icmp inspection and static route for traffic destined to those public addresses also added.
S 7.7.7.7 255.255.255.255 [1/0] via 10.0.0.100, inside
S 8.8.8.8 255.255.255.255 [1/0] via 10.0.0.100, inside
S 9.9.9.9 255.255.255.255 [1/0] via 10.0.0.100, inside
thanks for your reply!
- Labels:
-
NGFW Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-17-2011 01:18 AM
Hi,
If I understand it correctly, you have 3 ISP connections on the terminated on to the outside interface of the ASA (R2,R3,R4)???
You want to map the internal host 20.0.0.200 to three different public ip's ( 7.7.7.7, 8.8.8.8, 9.9.9.9)???
Well on the ASA you cannot do policy based routing and can only have one default route on the ASA, so this might be tough, moreover can you explain me, y do you have this nat:
static (outside,inside) interface 20.0.0.200 netmask 255.255.255.255
Please be aware that the return packets would always be directed towards the default gateway.
It would be helpful if you can provide your config from ASA.
Thanks,
Varun
Varun Rao
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-17-2011 02:24 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-31-2011 12:41 PM
Hi,
Your requirement is still confusing. You mention you want outside users to be able to access an inside server using 3 different IP addresses (7.7.7.7, 8.8.8.8 and 9.9.9.9).
If that's your requirement, on ASA 8.2 unfortunately that's not really possible though there is a way to "fool" the firewall to get it working:
http://www.cisco.com/en/US/products/ps6120/products_configuration_example09186a00807d2874.shtml
frankly, i have seen this to not work in quite a few occasions. Are you going to perform NAT on the ASA or on an inside router? If it's on the ASA, you do not need the following routes:
route inside 7.7.7.7 255.255.255.255 10.0.0.100 1
route inside 8.8.8.8 255.255.255.255 10.0.0.100 1
route inside 9.9.9.9 255.255.255.255 10.0.0.100 1
Regards,
Prapanch
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide
