- Cisco Community
- Technology and Support
- Security
- Network Security
- NAT Order Issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
NAT Order Issue
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-05-2012 07:58 PM - edited 03-11-2019 04:50 PM
Hi There
I am working on a task of redirecting any uncatched http traffic to Symantec public transparent proxy through Cisco ASA.
For the definition of uncatched http traffic, we have inbound squid servers for deploying IE proxy pac and redirect the http traffic to Symantec public transpraent proxy, however we can't deploy IE proxy pac to mobile device and non-support web browers.
Since we have some application using IE proxy setting for direct http communication with external domains, the current symantec policy addes those domains in the exception list so that they are not redirect to Symantec public transparent proxy server.
For the platform - Cisco ASA 5510 ASA 8.4(4)1
For the solution, I have the following two nat rules
(Order #1) For the networks (for example 10.3.142.0/24) with those applications which don't need to redirect to Symantec public transparent proxy
nat (inside,outside) 1 source static 10.3.142.0 Symantec_Translated_Source destination static Symantec_Catch_All_Initial_Destination Symantec_Catch_All_Initial_Destination service Symantec_Catch_All_Initial_Http Symantec_Catch_All_Initial_Http unidirectional
(Order #2) For the whole network (for example 10.0.0.0/8) to external on http
nat (inside,outside) 2 source static 10.0.0.0 Symantec_Translated_Source destination static Symantec_Catch_All_Initial_Destination Symantec_Catch_All_Translated_Destination service Symantec_Catch_All_Initial_Http Symantec_Catch_All_Translated_3128 unidirectional
From my understanding, the twice nat rule in section 1 is applied on a first match basis, in the order they appear in the configuration.
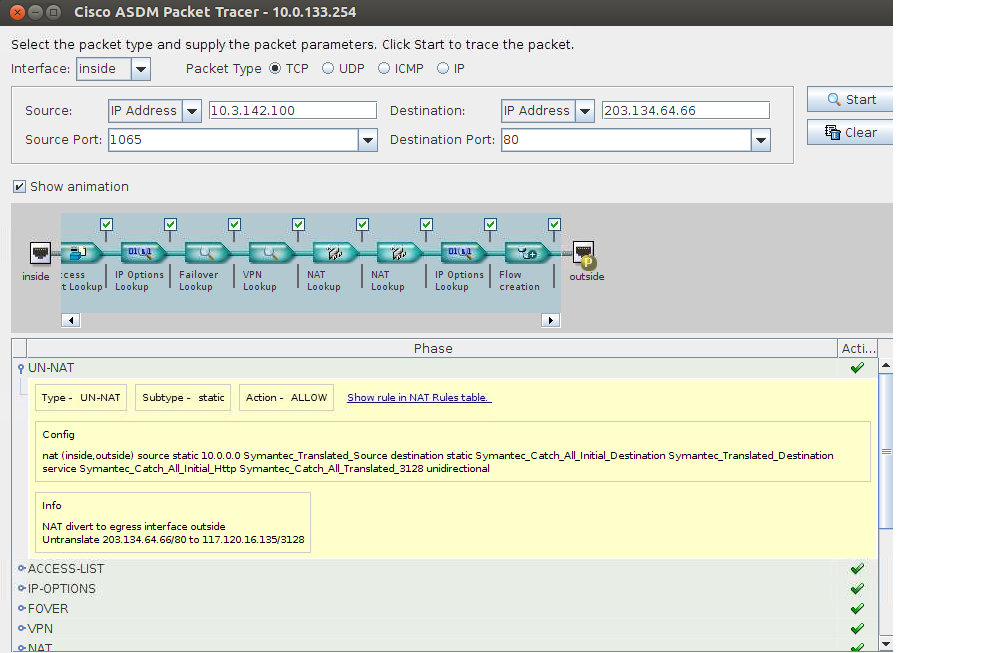
From the packet tracert result, the #2 rule is always kicked in the un-nat section and the following nat rule and I am not sure the reason. I though that NAT rule 1 shall be in first per my design purpose.
Any suggestion if there are any issues with this solution or are there any alternative solutions?
Thanks
Qing Yu
- Labels:
-
NGFW Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-05-2012 11:37 PM
Hello Quing,
Do use different object networks for each nat ( at least in this 2)
check bug CSCtq47028 witch I think is the one you are hitting
I am confident this is the problem
Remember to rate all the helpful post Quing, as we are here to help for free
Julio
Senior Network Security and Core Specialist
CCIE #42930, 2xCCNP, JNCIP-SEC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-06-2012 07:41 PM
HI Julio
Thanks very much for your prompt response.
I have updated rule#1 with different definition for network object and service object, reloaded the device, however rule#2 UN-nat still kicked in first.
Any suggestion?
Qing Yu
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-06-2012 09:13 PM
Hello Quin,
Can you post the entire configuration...
and also the complete packet tracer output from the CLI, you can change the outside IP addresses for security purposes
Regards
Rate all the answers, that is as important as a thanks for us
Julio
Senior Network Security and Core Specialist
CCIE #42930, 2xCCNP, JNCIP-SEC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2012 03:46 PM
Hi, I work with Qing and we are still having some trouble with the NAT rules.
I have pasted a cut-down version of the ASA's configuration and changed the public addresses. As you can see, we have a NAT rule that forwards all HTTP traffic from the 10.3.142.0 subnet to a Symantec cloud based proxy.
This NAT rule works great for our regular internet traffic but there are a few websites that we need to bypass the symantec proxy when accessing. I have tried creating another NAT rule for traffic destined to those websites when i test this, the traffic is always hitting the Symantec NAT. Any ideas?
Cheers
hostname ASA5510
!
interface Ethernet0/0
description inside network
nameif inside
security-level 100
ip address 10.0.133.254 255.255.255.0 standby 10.0.133.220
!
interface Ethernet0/1
description outside network
nameif outside
security-level 0
ip address 199.1.1.1 255.255.255.240
!
object network Symantec_Catch_Http_Translated_Source
host 199.1.1.4
description Symantec_Catch_Http_Translated_Source
object network obj_any
subnet 0.0.0.0 0.0.0.0
object network Symantec_Catch_All_Initial_Destination
subnet 0.0.0.0 0.0.0.0
description Symantec_Catch_All_Initial_Destination
object network Symantec_Translated_Destination
host 117.x.x.x
description Symantec_Translated_Destination
object service Symantec_Catch_All_Initial_Http
service tcp source range 1025 65535 destination eq www
description Symantec_Catch_All_Initial_Http
object service Symantec_Catch_All_Translated_3128
service tcp source range 1025 65535 destination eq 3128
description Symantec_Catch_All_Translated_3128
object network Symantec_Translated_Source
host 199.1.1.3
description Symantec_Translated_Source
object service http_test
service tcp source range 1025 65535 destination eq www
object-group network 10.3.142.0
description Internal network
network-object 10.3.142.0 255.255.255.0
nat (inside,outside) source static 10.3.142.0 Symantec_Translated_Source destination static Symantec_Catch_All_Initial_Destination Symantec_Translated_Destination service Symantec_Catch_All_Initial_Http Symantec_Catch_All_Translated_3128 unidirectional
!
nat (inside,outside) dynamic interface
route outside 0.0.0.0 0.0.0.0 internode-gw 1
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2012 07:45 PM
Does anyone have suggestions for this?
Cheers
K
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2012 08:56 PM
Hello,
Where is the nat rule you created to bypass the symantec NAT setup?
Senior Network Security and Core Specialist
CCIE #42930, 2xCCNP, JNCIP-SEC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2012 09:39 PM
Hi Jcarvaja,
I have tried a few different NAT variations with no success. I have pasted below the intial NAT rule I tried
object network TEST_SITE
host 203.x.x.x
!
object network Symantec_bypass
host 199.1.1.8
!
nat (inside,outside) source dynamic 10.3.142.0 Symantec_bypass destination static TEST_SITE TEST_SITE
After applying this NAT rule, the traffic sourced from 10.3.142.0 destined to the website 203.x.x.x still hits the rule below
nat (inside,outside) source static 10.3.142.0 Symantec_Translated_Source destination static Symantec_Catch_All_Initial_Destination Symantec_Translated_Destination service Symantec_Catch_All_Initial_Http Symantec_Catch_All_Translated_3128 unidirectional
!
Thanks,
Kris
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2012 09:50 PM
Hello,
I need the show run nat output.
Regards
Senior Network Security and Core Specialist
CCIE #42930, 2xCCNP, JNCIP-SEC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-01-2012 11:29 PM
Hi Jcarvaja,
I have setup a test ASA and having the same issues. Below is the full configuration. I have also included the outputs of running a packet tracer simulation to ip 8.8.8.8 on port 80 and to 203.2.2.1 on port 80.
As you can see, both of these from both of these simulation we hit the NAT rule that forwards everything to the symantec.cloud proxy. That is ok for the 8.8.8.8 IP but when we connect to the 203.2.2.1 80 we don't want this traffic to go via the symantec proxy.
ASA Version 8.4(4)1
!
hostname ciscoasa
enable password 56vvIVQPPoRkhbfy encrypted
passwd 2KFQnbNIdI.2KYOU encrypted
names
!
interface GigabitEthernet0/0
description inside network
nameif inside
security-level 100
ip address 10.0.133.254 255.255.255.0 standby 10.0.133.220
!
interface GigabitEthernet0/1
description outside network
nameif outside
security-level 0
ip address 199.1.1.1 255.255.255.240
!
interface GigabitEthernet0/2
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/3
shutdown
no nameif
no security-level
no ip address
!
interface Management0/0
shutdown
no nameif
no security-level
no ip address
management-only
!
ftp mode passive
object network Symantec_Catch_Http_Translated_Source
host 199.1.1.4
description Symantec_Catch_Http_Translated_Source
object network obj_any
subnet 0.0.0.0 0.0.0.0
object network Symantec_Catch_All_Initial_Destination
subnet 0.0.0.0 0.0.0.0
description Symantec_Catch_All_Initial_Destination
object network Symantec_Translated_Destination
host 117.1.1.3
description Symantec_Translated_Destination
object service Symantec_Catch_All_Initial_Http
service tcp source range 1025 65535 destination eq www
description Symantec_Catch_All_Initial_Http
object service Symantec_Catch_All_Translated_3128
service tcp source range 1025 65535 destination eq 3128
description Symantec_Catch_All_Translated_3128
object network Symantec_Translated_Source
host 199.1.1.3
description Symantec_Translated_Source
object service http_test
service tcp source range 1025 65535 destination eq www
object network TEST_SITE
host 203.2.2.1
object network Symantec_bypass
host 199.1.1.8
object-group network 10.3.142.0
description Internal network
network-object 10.3.142.0 255.255.255.0
pager lines 24
mtu inside 1500
mtu outside 1500
no failover
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
nat (inside,outside) source static 10.3.142.0 Symantec_Translated_Source destination static Symantec_Catch_All_Initial_Destination Symantec_Translated_Destination service Symantec_Catch_All_Initial_Http Symantec_Catch_All_Translated_3128 unidirectional
nat (inside,outside) source dynamic 10.3.142.0 Symantec_bypass destination static TEST_SITE TEST_SITE
!
object network obj_any
nat (inside,outside) dynamic interface
route outside 0.0.0.0 0.0.0.0 199.1.1.2 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-record DfltAccessPolicy
user-identity default-domain LOCAL
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart
telnet timeout 5
ssh timeout 5
ssh key-exchange group dh-group1-sha1
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect rtsp
inspect esmtp
inspect sqlnet
inspect skinny
inspect sunrpc
inspect xdmcp
inspect sip
inspect netbios
inspect tftp
inspect ip-options
!
service-policy global_policy global
prompt hostname context
Cryptochecksum:6e8921b79d18af46fc8fc5b661b13d1f
: end
ciscoasa(config)# packet-tracer input inside tcp 10.3.142.2 1025 8.8.8.8 80 de$
Phase: 1
Type: UN-NAT
Subtype: static
Result: ALLOW
Config:
nat (inside,outside) source static 10.3.142.0 Symantec_Translated_Source destination static Symantec_Catch_All_Initial_Destination Symantec_Translated_Destination service Symantec_Catch_All_Initial_Http Symantec_Catch_All_Translated_3128 unidirectional
Additional Information:
NAT divert to egress interface outside
Untranslate 8.8.8.8/80 to 117.1.1.3/3128
Phase: 2
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Forward Flow based lookup yields rule:
in id=0x73b9f6a0, priority=0, domain=inspect-ip-options, deny=true
hits=4, user_data=0x0, cs_id=0x0, reverse, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, dscp=0x0
input_ifc=inside, output_ifc=any
Phase: 3
Type: NAT
Subtype:
Result: ALLOW
Config:
nat (inside,outside) source static 10.3.142.0 Symantec_Translated_Source destination static Symantec_Catch_All_Initial_Destination Symantec_Translated_Destination service Symantec_Catch_All_Initial_Http Symantec_Catch_All_Translated_3128 unidirectional
Additional Information:
Static translate 10.3.142.2/1025 to 199.1.1.3/1025
Forward Flow based lookup yields rule:
in id=0x77c7c4e0, priority=6, domain=nat, deny=false
hits=4, user_data=0x73c8df98, cs_id=0x0, use_real_addr, flags=0x0, protocol=6
src ip/id=10.3.142.0, mask=255.255.255.0, port=0
dst ip/id=117.1.1.3, mask=255.255.255.255, port=3128,
sport range<0> : 1025-65535 dscp=0x0
input_ifc=inside, output_ifc=outside
Phase: 4
Type: NAT
Subtype: rpf-check
Result: ALLOW
Config:
nat (inside,outside) source static 10.3.142.0 Symantec_Translated_Source destination static Symantec_Catch_All_Initial_Destination Symantec_Translated_Destination service Symantec_Catch_All_Initial_Http Symantec_Catch_All_Translated_3128 unidirectional
Additional Information:
Forward Flow based lookup yields rule:
out id=0x77c7c710, priority=6, domain=nat-reverse, deny=false
hits=4, user_data=0x73c8e040, cs_id=0x0, use_real_addr, flags=0x0, protocol=6
src ip/id=10.3.142.0, mask=255.255.255.0, port=0
dst ip/id=117.1.1.3, mask=255.255.255.255, port=3128,
dport range<0> : 1025-65535 dscp=0x0
input_ifc=inside, output_ifc=outside
Phase: 5
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Reverse Flow based lookup yields rule:
in id=0x74698548, priority=0, domain=inspect-ip-options, deny=true
hits=5, user_data=0x0, cs_id=0x0, reverse, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, dscp=0x0
input_ifc=outside, output_ifc=any
Phase: 6
Type: FLOW-CREATION
Subtype:
Result: ALLOW
Config:
Additional Information:
New flow created with id 9, packet dispatched to next module
Module information for forward flow ...
snp_fp_tracer_drop
snp_fp_inspect_ip_options
snp_fp_tcp_normalizer
snp_fp_translate
snp_fp_adjacency
snp_fp_fragment
snp_ifc_stat
Module information for reverse flow ...
snp_fp_tracer_drop
snp_fp_inspect_ip_options
snp_fp_translate
snp_fp_tcp_normalizer
snp_fp_adjacency
snp_fp_fragment
snp_ifc_stat
Result:
input-interface: inside
input-status: up
input-line-status: up
output-interface: outside
output-status: up
output-line-status: up
Action: allow
ciscoasa(config)# packet-tracer input inside tcp 10.3.142.2 1025 203.2.2.1 80
Phase: 1
Type: UN-NAT
Subtype: static
Result: ALLOW
Config:
nat (inside,outside) source static 10.3.142.0 Symantec_Translated_Source destination static Symantec_Catch_All_Initial_Destination Symantec_Translated_Destination service Symantec_Catch_All_Initial_Http Symantec_Catch_All_Translated_3128 unidirectional
Additional Information:
NAT divert to egress interface outside
Untranslate 203.2.2.1/80 to 117.1.1.3/3128
Phase: 2
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Phase: 3
Type: NAT
Subtype:
Result: ALLOW
Config:
nat (inside,outside) source static 10.3.142.0 Symantec_Translated_Source destination static Symantec_Catch_All_Initial_Destination Symantec_Translated_Destination service Symantec_Catch_All_Initial_Http Symantec_Catch_All_Translated_3128 unidirectional
Additional Information:
Static translate 10.3.142.2/1025 to 199.1.1.3/1025
Phase: 4
Type: NAT
Subtype: rpf-check
Result: ALLOW
Config:
nat (inside,outside) source static 10.3.142.0 Symantec_Translated_Source destination static Symantec_Catch_All_Initial_Destination Symantec_Translated_Destination service Symantec_Catch_All_Initial_Http Symantec_Catch_All_Translated_3128 unidirectional
Additional Information:
Phase: 5
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Phase: 6
Type: FLOW-CREATION
Subtype:
Result: ALLOW
Config:
Additional Information:
New flow created with id 10, packet dispatched to next module
Result:
input-interface: inside
input-status: up
input-line-status: up
output-interface: outside
output-status: up
output-line-status: up
Action: allow
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-18-2012 06:51 PM
bump..Anyone have any ideas with this one?
Cheers
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide
