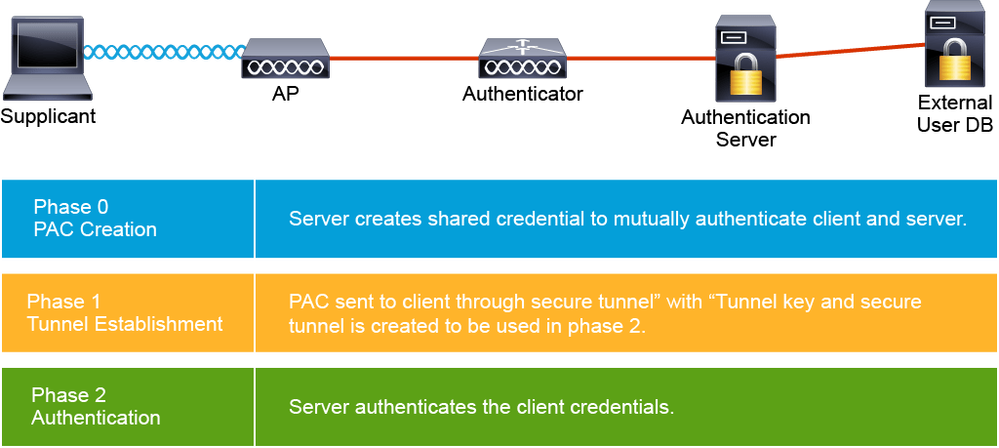
EAP-FAST has three phases:
Phase 0: A unique shared credential is generated by the server. It will be used by client and server to authenticate each other during phase 1. Credential is specific to a user ID and Server Authority ID (A-ID). The PAC needs to be installed on the client. It can be done manually or via a trusted connection where the client is authenticated using another method (for example, certificate-based [TLS] or password-based [MS-CHAP v2]).
Phase 1: The function of this phase is to establish a secure tunnel by using PAC credentials. The AAA server and the end user, or client, use PAC to authenticate each other and establish a secure tunnel. A process similar to TLS is used to verify the identity of the AAA server and to establish a secure tunnel between the client and AAA server. PAC replaces the digital certificate that is used in EAP-TLS and eliminates the need for a PKI to manage the certificates. A tunnel key will be established which will be used in phase 2 for confidentiality and integrity.
Phase 2: The RADIUS server authenticates the user credentials with another EAP, which is protected by the tunnel that is created in Phase 1. The common means of authentication are password and GTCs.