- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- Digital Optical Monitoring - DOM
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
10-20-2011 09:56 PM - edited 08-23-2017 11:38 PM
Introduction
This document provide information about DOM (Digiatal Optical monitoring)
Information
Digital Optical Monitoring or DOM is an industry wide standard, intended to define a digital interface to access real-time operating parameters such as:
Optical Tx power
Optcal Rx power
Laser bias current
Temparature
Transceiver supply voltage
Which means, we are now by using DOM capable of performing transceiver monitoring and troubleshooting operations.
DOM Support on Cisco Transeivers
Not all transceivers support DOM, a list of capable transceivers is available at:
How to use DOM
Following command can be used to turn on/off DOM for all transceivers type in the system
Router(config)#transceiver type all
Router(config-xcvr-type)#monitoring
Router(config-xcvr-type)#end
Once enabled, DOM can be accessed via CLI using "show interface transceiver command"
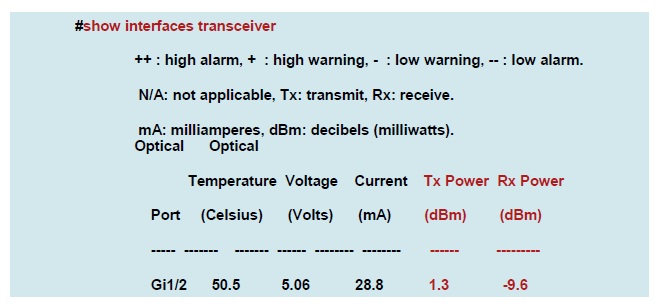
Off all the five values two mostly used and rellevant values are TX and RX power, temperature is also used sometimes. The operating range of these three values is unique across all modules and is available in the data sheet.
There is an extension available for this command, which is also very helpful and is used to check threshold values of the above paramaeters like temperature , Tx, Rx. The command is , show interface gig x/y transceiver detail
sh int gi 1/3 transceiver detail
Transceiver monitoring is disabled for all interfaces.
ITU Channel not available (Wavelength not available),
Transceiver is externally calibrated.
mA: milliamperes, dBm: decibels (milliwatts), NA or N/A: not applicable.
++ : high alarm, + : high warning, - : low warning, -- : low alarm.
A2D readouts (if they differ), are reported in parentheses.
The threshold values are calibrated.
High Alarm High Warn Low Warn Low Alarm
Temperature Threshold Threshold Threshold Threshold
Port (Celsius) (Celsius) (Celsius) (Celsius) (Celsius)
------- ------------------ ---------- --------- --------- ---------
Gi1/3 34.2 110.0 93.0 -30.0 -40.0
High Alarm High Warn Low Warn Low Alarm
Voltage Threshold Threshold Threshold Threshold
Port (Volts) (Volts) (Volts) (Volts) (Volts)
------- --------------- ---------- --------- --------- ---------
Gi1/3 3.31 3.90 3.70 2.90 2.70
High Alarm High Warn Low Warn Low Alarm
Current Threshold Threshold Threshold Threshold
Port (milliamperes) (mA) (mA) (mA) (mA)
------- ----------------- ---------- --------- --------- ---------
Gi1/3 0.1 -- 80.0 70.0 4.0 2.0
Optical High Alarm High Warn Low Warn Low Alarm
Transmit Power Threshold Threshold Threshold Threshold
Port (dBm) (dBm) (dBm) (dBm) (dBm)
------- ----------------- ---------- --------- --------- ---------
Gi1/3 -27.7 -- 0.9 -1.0 -11.5 -13.5
Optical High Alarm High Warn Low Warn Low Alarm
Receive Power Threshold Threshold Threshold Threshold
Port (dBm) (dBm) (dBm) (dBm) (dBm)
------- ----------------- ---------- --------- --------- ---------
Gi1/3 -7.2 0.7 -1.0 -20.0 -24.0
Related Information
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
v good explanation. but are these commands same across all platform/ios release?
like 7600/6500/iosxr/nexus ?
Router(config)#transceiver type all
Router(config-xcvr-type)#monitoring
Router(config-xcvr-type)#end
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks for these information, helped me alot trough understanding and configuring my DOM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
the following command DOES not exist of 38xx or 3750 or 3560 devices
transceiver type all
what product support this command?
show int transceiver
seems to only work on 3750/3650
but not on 38xx routers
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thank you for the information. Great tip!
I can confirm these commands are working on 6880 devices.
Thanks again!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
I can confirm that these commands work in the CGR2010.
Very useful to track fiber status.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
We just installed some 4431's with DOM supported SFP's. Do the 4431's support DOM and how do I turn it on. I have tried the above commands and it does not work. Any ideas. I did find some documentation that shows DOM is supported but it looks like it might just be in the NIM's and not for the onboard SFP ports.
Thanks
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
The command to show the Optical Rx and Tx levels is:
show interface <int id> transceiver detail
it works on WS 3560 Switch but not on 4560 switch.
The command transceiver type all does not work on 4560 either, despite being shown in the manual.
Regards
John
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
show interrface e1/3 transceiver
This command works on NX-OS too. Tested on N5k/N7k
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Jose Colon II
On the 4451X I was able to use the following command:
show hw-module subslot 0/0 transceiver 1 status
The Transceiver in slot 0 subslot 0 port 1 is enabled.
Module temperature = +22.878 C
Transceiver Tx supply voltage = 3346.3 mVolts
Transceiver Tx bias current = 13488 uAmps
Transceiver Tx power = -7.2 dBm
Transceiver Rx optical power = -7.8 dBm
Regards,
Lena
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi,
Thanks for the above information.
And can you please suggest any workaround for those optical devices that do not support DOM.
I'm interested in obtaining only the Tx power and Rx power.
Regards
Joy
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi!
Does the command "transceiver type all | monitoring" affect traffic on production system if I want to enable DOM on the switch?
Regards,
Anton
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community:


