I was recently talking to a large Enterprise customer and they pointed out how complex their network had become over the last few years. They requested that before they hear about Cisco’s routing and switching product portfolio, a discussion on running the network operations and automation would be valuable. This is not surprising as, today, I find most organizations, service provider and enterprise alike, are looking at techniques to deploy in an automatic way network services and infrastructure as a primary requirement.
This customer is not alone, networks are growing rapidly and technologies like IOT, Micro-services, containerized and virtualizated environments will cause the size and complexity of modern networks to increase exponentially.
What’s driving the enterprise customers to automation?
As the customer networks have increasingly become complex, the need to manage the network changes and flexibility to create new services quickly is the key to running these networks.
Key reasons for the customers asking for automation include:
- Need for faster and more scalable network and service deployments
- Need to manage multi-vendor networks
- Increased complexity of managing physical and virtual networks
- High cost of network operations
Beyond keeping a handle on transport and connectivity, related concerns like security and network policy compliance are proving to be very demanding for network operators.
Successful automaton initiatives are structured as a series of smaller steps that build upon each other. This is where Cisco Network Services Orchestrator (NSO) comes in. NSO delivers automation and orchestration at the network layer and also at the network services tier.
Cisco Network Services Orchestrator (NSO) is an industry-leading software for automating services across traditional and virtualized networks. One of the things it is designed to do is manage the network device layer (a router, switch or an application) and at the service layer (eg managed VPN, managed Security service) being able to add, change, and delete service instance without disrupting overall service in an automated way. This improves efficiency in network operations (thus reducing opex) while also improving speed of service delivery and customer experience (thus driving revenue growth).
Cisco NSO Architecture
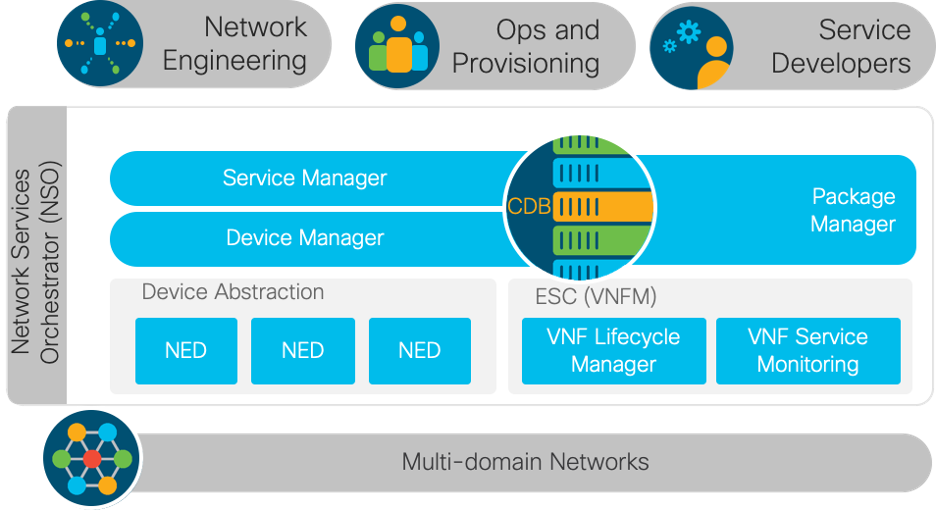
With Cisco NSO, you can automate the deployment of a more powerful and efficient network. NSO is architected in an easy to understand modular approach. Networks engineers can use NSO’s model driven programmatic interface that allows for control of network elements from device turn-up and configuration to more sophisticated service lifecycle management. The diagram below elaborates on the NSO architecture and how it helps customers overcome some of the challenges described above.
How does NSO automate multi-vendor network deployments?
Device Manager layer
Customers often relate to us the difficulties they face managing a multi-vendor network, with many operating systems and device versions running. NSO supports the process of validating, implementing and abstracting your network config and network operations, providing support for the end to end operation. NSO makes device configuration commands available over a network wide, Command Line Interface (CLI), APIs, web and user interfaces.
Support for multi-vendor networks is achieved through a rich variety of Network Element Drivers (NEDs). The multi-vendor device manager layer uses the network element drivers (NEDs) to mediate access to both Cisco and more than 100 other-party physical and virtual devices.
For more on NEDs and supported NEDs, refer to this link:
https://www.cisco.com/c/en/us/products/collateral/cloud-systems-management/network-services-orchestrator/datasheet-c78-734669.html
NSO provides a centralized configuration database
The Configuration Database (CDB) contains the current synchronized configurations for all devices and services in the network domain. NSO keeps the CDB in sync with the real network device configurations to ensure configuration consistency.
The NSO configuration database and transaction engine is at the heart of the product and helps provides access to devices configurations and historical changes made to the configuration.
NSO can synchronize configuration from the devices for audits and compliance checks. This means that the database will always represent the true state of the network. The database can be imported, exported and queried using XML, XPath, and the CLI and Web interfaces. Programmatic interfaces to the database are also provided.
NSO function packages contain models and code for a specific function. It could be a NED for a specific device, a service model like MPLS VPN, a application Web UI package etc. Function packages can be added, removed and upgrade in run-time.
Service manager layer
The need for more agile service deployment and the ability to flow manage the service layer is achieved with this layer. For NSO to deploy services across network devices, service models are needed. These service models are managed by the Service manager layer. A service model in is defined in the configuration language YANG: the service model defines the black-box view of a service; the input parameters are required when activating the service. This YANG model also interfaces towards all NSO northbound entities,
NSO increases the TTM and lowers cost of service delivery
NSO is responsible for mapping the service model and the parameters into what is the resulting device configuration. NSO features to ensure shorter time-to-market and lower cost of ownership than any other service activation tools on the market. NSO can also perform service audits to detect if any device configuration has changed with respect to the desired service configuration. The diff can be displayed and analyzed, and the service can be re-deployed if needed.
NSO is typically used for provisioning network services like VPNs, ACLs, BGP Peers, etc. NSO can provision services and device configurations as one atomic transaction. NSO also supports service updates and NSO automatically cleans up the network when services are deleted.
Cisco NSO provides a single pane of glass view for the full network infrastructure. Below is an example of the network wide CLI view and a UI based view provided by NSO.
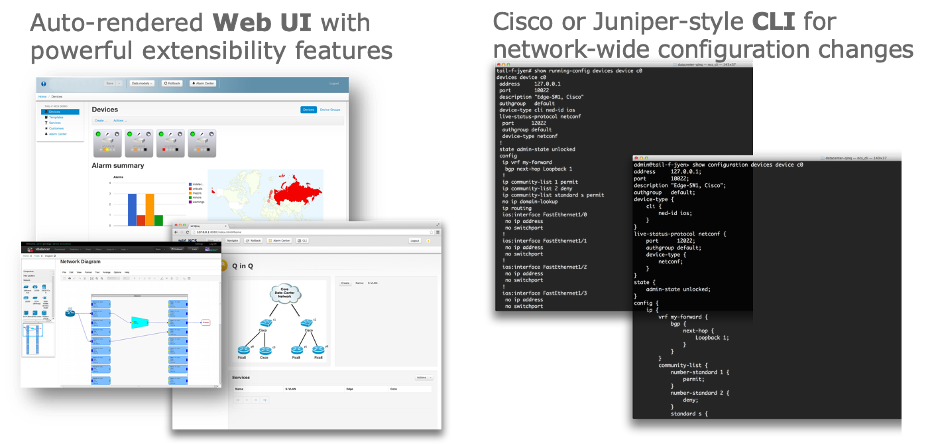
The example in the screen shot above shows how NSO can be used to provision bulk Network Changes – for example pushing a specific ACL on all network elements belonging to a group. This can be achieved by using a UI based interface or using the NSO CLI interface which provides options for both Cisco and Juniper style CLI.
Gains customers are realizing with Cisco NSO
Customers are seeing phenomenal gains with NSO driven full automation. NSO is robust and proven in SP, Enterprise deployments with Industry’s broadest multivendor support. Below are some efficiency numbers driven by NSO deployment with a tier 1 operator. The efficiency gains realized had the aspects of new device onboarding and configuration management improvements. There are noticeable improvements in network service activation and change times. Below are the improvements seen by a tier 1 customer for service onboarding efficiency:
Device on boarding efficiency improvements: ~70%
Improvements in configuration change request times: ~75%
Improvements in Method of Procedure(MOP): ~79%
We are seeing an exponential adoption of Cisco NSO among our Enterprise, Service Provider and Public Sector customer base. The momentum for Cisco Network Services Orchestrator (NSO) continues to grow.
NSO 5.0 has been out in the market and customers are providing positive reviews on its functionality. To download your free copy of NSO 5.X with trial NEDs for non-production use, head over to developer.cisco.com/nso
Finally, NSO has an active community of developers and users on DevNet. You can review sample deployment examples and get any questions answered on the NSO community page.
