- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Who Me Too'd this topic
Who Me Too'd this topic
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-13-2019 11:48 PM
Hello,
I have set up Posture for AnyConnect VPN clients using ISE 2.4 and ASA ver 9.9.
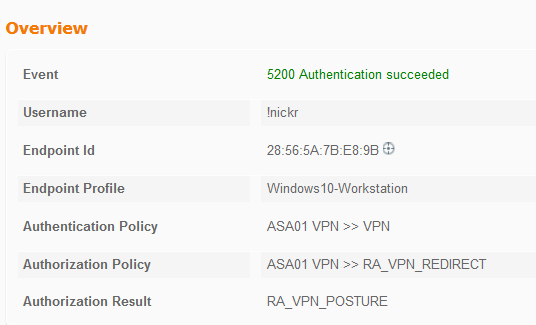
When starting up anyconnect the session connects to the ASA and hits an ISE policy that correctly redirects:
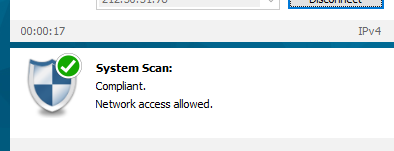
The AnyConnect client then runs a scan of the laptop to check for a simple file and this succeeds:
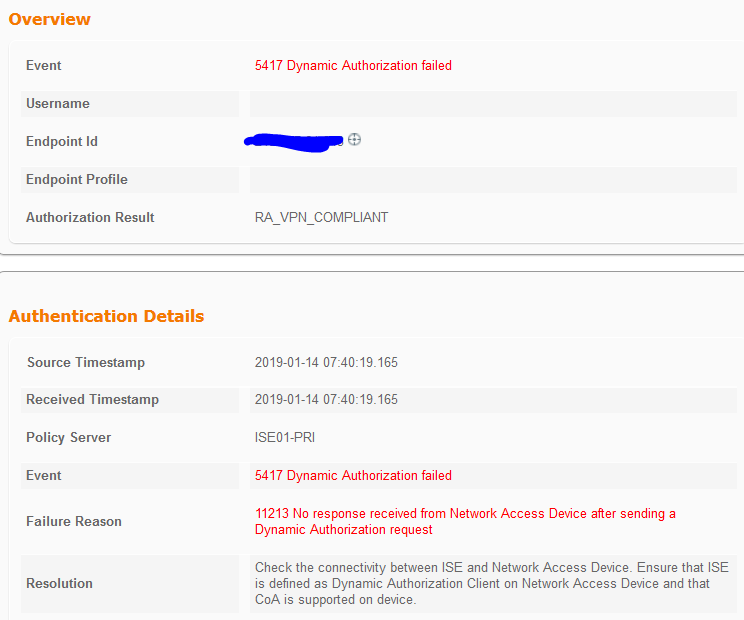
However, the CoA never happens and the logs on ISE show the below:
Below is a portion of the configuration on the ASA:
aaa-server ISE01 protocol radius
authorize-only
interim-accounting-update periodic 1
dynamic-authorization
aaa-server ISE01 (outside) host x.x.x.x
key *****
radius-common-pw *****
aaa-server TACACS-ISE protocol tacacs+
aaa-server TACACS-ISE (outside) host x.x.x.x
key *****
cts sxp enable
user-identity default-domain LOCAL
aaa authentication ssh console TACACS-ISE LOCAL
aaa authentication enable console TACACS-ISE LOCAL
aaa authentication http console ISE01 LOCAL
aaa accounting ssh console ISE01
aaa authentication login-history
webvpn
enable outside
anyconnect image disk0:/anyconnect-win-4.7.00136-webdeploy-k9.pkg 1
anyconnect image disk0:/anyconnect-win-4.5.02033-webdeploy-k9.pkg 2
anyconnect profiles AnyConnect-Profile disk0:/anyconnect-profile.xml
anyconnect enable
tunnel-group-list enable
cache
disable
error-recovery disable
group-policy DfltGrpPolicy attributes
vpn-tunnel-protocol ikev1 l2tp-ipsec ssl-clientless
group-policy ANYCONNECT.GP internal
group-policy ANYCONNECT.GP attributes
dns-server value x.x.x.x
vpn-tunnel-protocol ssl-client
split-tunnel-policy tunnelspecified
split-tunnel-network-list value SplitTunneling
webvpn
anyconnect profiles value AnyConnect-Profile type user
dynamic-access-policy-record DfltAccessPolicy
tunnel-group ANYCONNECT.VPN type remote-access
tunnel-group ANYCONNECT.VPN general-attributes
address-pool ANYCONNECT
authentication-server-group ISE01
accounting-server-group ISE01
default-group-policy ANYCONNECT.GP
tunnel-group ANYCONNECT.VPN webvpn-attributes
group-alias ANYCONNECT.VPN enable
tunnel-group x.x.x.x type ipsec-l2l
tunnel-group x.x.x.x ipsec-attributes
ikev1 pre-shared-key *****
ikev2 remote-authentication pre-shared-key *****
ikev2 local-authentication pre-shared-key *****------
When I initially connect my anycconnect to the firewall I see it getting an AV-Pair:
LAB-ASA01# debug radius dynamic-authorization
LAB-ASA01#
LAB-ASA01#
LAB-ASA01# Got AV-Pair with value profile-name=Windows10-Workstation
But nothing else after that.
Any help / ideas would be great.
Thanks
Nick
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)