- Cisco Community
- Technology and Support
- Networking
- Routing
- Re: Creating DMZ
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-05-2011 02:32 PM - edited 03-04-2019 01:50 PM
Hello Community,
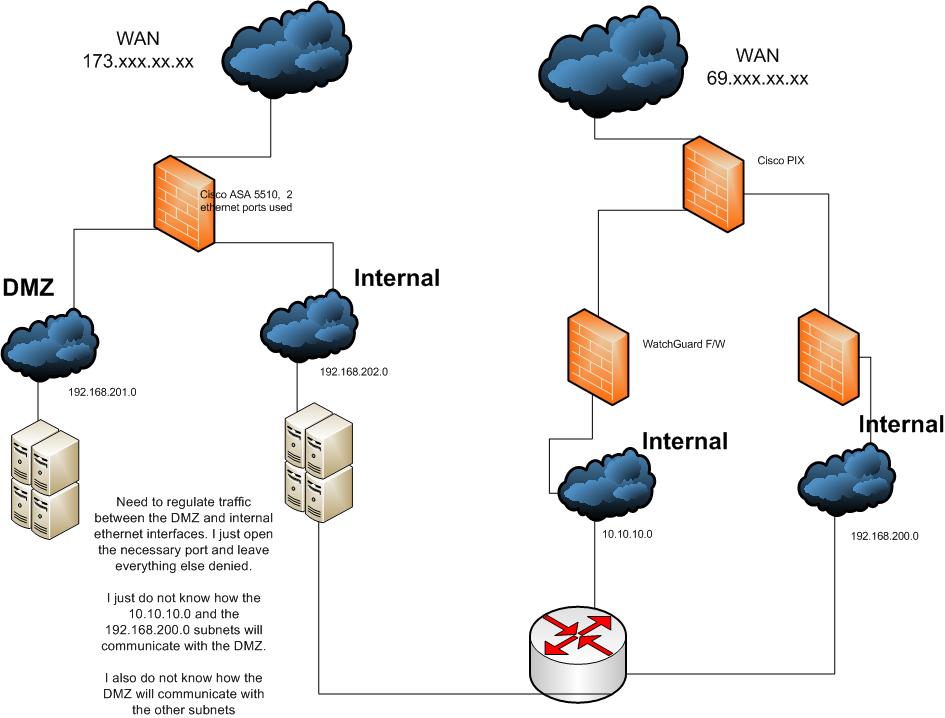
creating a DMZ on a ASA 5510 router within my environment of 3 internal subnets who have thier own firewall.
I have ethernet0/0 assigned a WAN address
I have ethernet0/1 assigned a subnet 192.168.201.0
I need to add ethernet0/2 a subnet 192.168.202.0
1. Ethernet0/1 will be the DMZ. which should not connect to my internal network.
2. Ethernet0/2 will be a new internal network and should be connected to my 3 other internal subnets via internal router.
3. I have to regulate traffic between ethernet0/1 and ethernet0/2, deny everything and open ports for needed communication between the two.
how will my other networks reach my DMZ and vise versa?
I have attched a screen shot of my network.
Solved! Go to Solution.
- Labels:
-
Other Routing
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-05-2011 02:42 PM
John
On your internal router you would have route for the DMZ ie.
ip route 192.168.201.0 255.255.255.0 192.168.202.x <-- where .x is the internal IP of the ASA firewall.
As for setting up access as far as NAT goes if you want the DMZ to be able to initiate connections to the inside and the inside to the DMZ for all 3 networks then on the ASA -
static (inside,dmz1) 192.168.201.0 192.168.201.0 netmask 255.255.255.0
static (inside,dmz1) 10.10.10.0 10.10.10.0 netmask 255.255.255.0
static (inside,dmz1) 192.168.200.0 192.168.200.0 netmask 255.255.255.0
note the above is per 8.3 NAT code. If your ASA is running 8.3 or greater the NAT will be different.
Edit - i forgot. On your ASA you will need to add routes for the 10.x.x.x and 192.168.200.x network ie.
route inside 10.10.10.0 255.255.255.0 192.168.201.x <-- where x is the IP assigned to the router interface on the 192.168.201.x network
route inside 192.168.200.0 255.255.255.0 192.168.201.x
Jon
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-05-2011 03:50 PM
Jon has given you pretty much the whole config . Ideally in the DMZ's(public) you dont't want the servers initiating connections to internal network. The connection's should be initiated from internal to the DMZ. This is for security pruposes.
There is a very good resource which pretty much every Architects/Designers use which is
www.cisco.com/go/cvd (This is an area where you find the Cisco recommended design guides for every scenario)
HTH.
Regards,
please rate if helpful
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-05-2011 02:42 PM
John
On your internal router you would have route for the DMZ ie.
ip route 192.168.201.0 255.255.255.0 192.168.202.x <-- where .x is the internal IP of the ASA firewall.
As for setting up access as far as NAT goes if you want the DMZ to be able to initiate connections to the inside and the inside to the DMZ for all 3 networks then on the ASA -
static (inside,dmz1) 192.168.201.0 192.168.201.0 netmask 255.255.255.0
static (inside,dmz1) 10.10.10.0 10.10.10.0 netmask 255.255.255.0
static (inside,dmz1) 192.168.200.0 192.168.200.0 netmask 255.255.255.0
note the above is per 8.3 NAT code. If your ASA is running 8.3 or greater the NAT will be different.
Edit - i forgot. On your ASA you will need to add routes for the 10.x.x.x and 192.168.200.x network ie.
route inside 10.10.10.0 255.255.255.0 192.168.201.x <-- where x is the IP assigned to the router interface on the 192.168.201.x network
route inside 192.168.200.0 255.255.255.0 192.168.201.x
Jon
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-05-2011 03:50 PM
Jon has given you pretty much the whole config . Ideally in the DMZ's(public) you dont't want the servers initiating connections to internal network. The connection's should be initiated from internal to the DMZ. This is for security pruposes.
There is a very good resource which pretty much every Architects/Designers use which is
www.cisco.com/go/cvd (This is an area where you find the Cisco recommended design guides for every scenario)
HTH.
Regards,
please rate if helpful
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide