- Cisco Community
- Technology and Support
- Networking
- Routing
- Non-ACI Spine Switch Cross Connect and ECMP
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Non-ACI Spine Switch Cross Connect and ECMP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-24-2018 10:25 AM
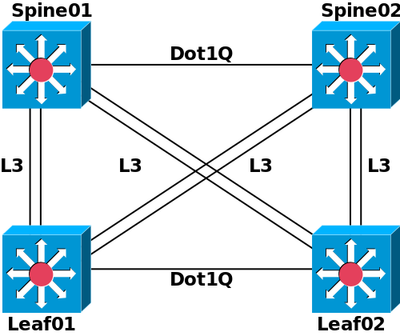
I have a pair of cisco nexus 9500 spine switches but not in ACI mode - just straight EIGRP L3 ECMP links to leaf switches. The spines are cross connected with a dot1Q trunk and so each sees the other as an EIGRP neighbor/peer over a common trunked vlan.
The leaf switches are also trunked east-west so we can do HSRP facing the end devices, so a dot1Q trunk makes sense there and the leaf switches are also using a common vlan to see each other as EIGRP neighbors/peers. Although above each leaf is show
So is the trunk and common vlans really needed for the spine switches, or is it a best practice of some kind, or is there any advantage to that ease-west peering for EIGRP?
- Labels:
-
Routing Protocols
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-30-2018 07:23 AM
Hi John,
In a standard leaf-spine architecture, the spines are pure L3 and there is no need to have any direct spine-to-spine connectivity. Obviously, in specific architectures there may be deviations that change this.
ECMP works across the available paths. In your case, assuming all links are equal, it will be two hops for any leaf to leaf traffic. Using a spine-to-spine link would mean three hops and the EIGRP computed metric should reject the path unless you have UCMP turned on with a relevant variance set.
Hope this helps
Dave
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide