- Cisco Community
- Technology and Support
- Networking
- Routing
- Re: PBR Not working in cisco nexus C9372TX -Core switch
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-29-2020 11:15 PM - edited 11-30-2020 07:49 AM
PBR Not working in cisco nexus C9372TX -Core switch
I have an issue with PBR in my core switch.
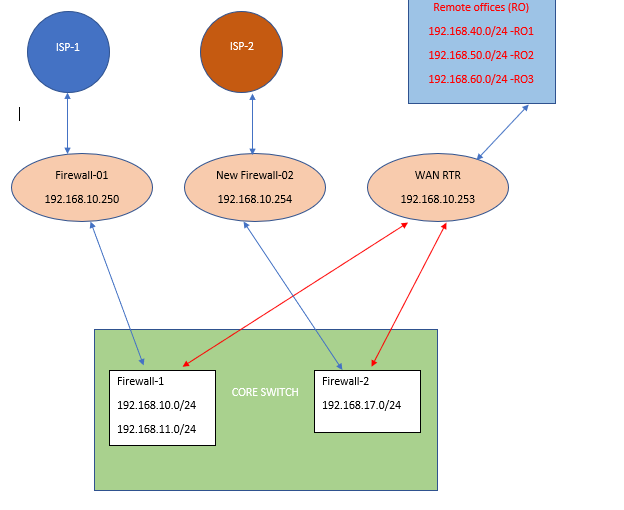
Network diagram is given below.
========================LAN Traffic to firewall-1 Working without any issue =========================
Below listed networks internet traffic is going to firewall-1
and remote offices network going to WAN-RTR (192.168.10.253) without PBR and using default route and static route.
192.168.10.0/24
192.168.11.0/24
ip route 0.0.0.0/0 192.168.10.250 name LAN-to-Firewall-01
ip route 192.168.0.0/16 192.168.10.253 name LAN-WAN-RTR-for------INTRANET
=========================LAN Traffic to firewall-2 using PBR not working ========================
Below listed networks internet traffic has goes to firewall-2 (192.168.10.254)
and remote offices can able to access via WAN-RTR (192.168.10.253)
192.168.17.0/24
Currently two default routes are running in core switch for firewall 1&2
ip route 0.0.0.0/0 192.168.10.250 name LAN-to-Firewall-01
ip route 0.0.0.0/0 192.168.10.254 10 LAN-to-Firewall-02
For 192.168.17.0/24 network internet traffic i have configured a PBR in core switch and routed to firewall-2
and 192.168.17.0/24 network can able to reach internet in icmp only. url;s not working because internal dns not resolving in the applied
PBR in interface vlan10.
traceroute from testing pc vlan10 network 192,168.17.0/24
C:\Users\TEMP>tracert 8.8.8.8
Tracing route to 8.8.8.8 over a maximum of 30 hops
1 <1 ms <1 ms <1 ms 192.168.17.251
2 <1 ms <1 ms <1 ms 192.168.10.254-----traffic hitting to firewall and exiting from wan port
3 1 ms 1 ms 1 ms 115.254.37.118
4 19 ms 19 ms 19 ms 74.125.51.2
5 19 ms 19 ms 19 ms 74.125.242.145
6 20 ms 20 ms 19 ms 216.239.42.215
7 20 ms 19 ms 19 ms 8.8.8.8---- traffic reaches to destination public ip
same time internet ( browsing not working due to some internal dns i think so pbr is blocking the dns resolving dns ip is 192.168.10.136 )not getting in testing pc vlan10
And 192.168.17.0/24 network cant able to reach remote office network also.
Can someone help me to resolve the PBR issue.
=======configurations ======
interface Vlan10
ip address 192.168.17.251/24
ip policy route-map PBR_IT_Internet_17_NW
hsrp version 2
hsrp 10
preempt
priority 150 forwarding-threshold lower 80 upper 90
ip 192.168.17.252
ip dhcp relay address 192.168.10.235
no shutdown
=================
SBSTJ_CORE-SW1# show route-map PBR_IT_Internet_17_NW
route-map PBR_IT_Internet_17_NW, permit, sequence 10
Match clauses:
ip address (access-lists): IT_Internet_17_NW
Set clauses:
ip next-hop 192.168.10.254
SBSTJ_CORE-SW1#
SBSTJ_CORE-SW1#
SBSTJ_CORE-SW1#
SBSTJ_CORE-SW1# show acc
access-lists accounting
SBSTJ_CORE-SW1# show access-lists IT_Internet_17_NW
IP access list IT_Internet_17_NW
10 permit ip 192.168.17.0/24 any
SBSTJ_CORE-SW1#
====================
Solved! Go to Solution.
- Labels:
-
Other Community Feedback
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-01-2020 05:38 AM
Hello
Okay lets try it another way-
no ip access-list extended nopbr
ip access-list extended nopbr
pemit ip any <vlan x>
permit ip any <vlan y>
route-map PBR_IT_Internet_17_NW deny 20
match ip address nopbr
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-01-2020 03:32 PM
Hello
Glad to hear it - that’s what these forums are for!
Thanks for the feedback much appreciated.
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-02-2020 12:29 AM
Hello
Yes you can but obviously you’ll need to tweak the extended nopbr access-list for each SVI you apply it to
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 01:34 AM
Hello
@sangeethsan wrote:
For 192.168.17.0/24 network internet traffic i have configured a PBR in core switch and routed to firewall-2
and 192.168.17.0/24 network can able to reach internet in icmp only. url;s not working because internal dns not resolving in the applied
PBR in interface vlan10.And 192.168.17.0/24 network cant able to reach remote office network also.
The reason for this is you have stated a catch all policy-based routing that as such all traffic for vlan 10 is being PBR'd via Fw2.
You’ll probably need to tweak the pbr access-list to accommodate a more deterministic routing path for vlan 10 users
try and test the following:
IP access list extended IT_Internet_17_NW
no 10
permit tcp any any eq 80
permit tcp anyany eq 443
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 02:02 AM
ACL in PBR updated and not working.
Now 192.168.17.0 traffic is not hitting to firewall-02.
SBSTJ_CORE-SW1# show route-map PBR_IT_Internet_17_NW
route-map PBR_IT_Internet_17_NW, permit, sequence 10
Match clauses:
ip address (access-lists): IT_Internet_17_NW
Set clauses:
ip next-hop 192.168.10.254
SBSTJ_CORE-SW1#
SBSTJ_CORE-SW1#
SBSTJ_CORE-SW1# sh acc
access-lists accounting
SBSTJ_CORE-SW1# sh access-lists IT_Internet_17_NW
IP access list IT_Internet_17_NW
10 permit tcp any any eq www
20 permit tcp any any eq 443
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 06:16 AM - edited 11-30-2020 06:18 AM
Hello
Okay lets step back a little, What excatly interms of traffic do you want to policy route from vlan 10?
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 07:28 AM
for vlan 10 internet traffic has go to firewall-02 (192.168.10.254)
and vlan 10 remote office traffic has go to WAN-RTR (192.168.10.253)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 08:07 AM
Hello,
I think you have to policy route the traffic to the remote network, and use the default route for all the other traffic. The entire config should look like below (I changed the names of the access list and the route map):
ip access-list IT_REMOTE_17_NW 10
permit ip 192.168.17.0/24 192.168.0.0/16
!
route-map PBR_IT_REMOTE_17_NW
match ip address IT_REMOTE_17_NW
set ip next-hop 192.168.10.253
!
interface Vlan10
ip address 192.168.17.251/24
ip policy route-map PBR_IT_REMOTE_17_NW
!
ip route 0.0.0.0/0 192.168.10.254 10 LAN-to-Firewall-02
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 08:42 AM
Hi George,
Not only remote office traffic ,internet traffic also i need to routed to 192.168.10.254
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 09:27 AM
Hello,
this contradicts what you said earlier:
--> for vlan 10 internet traffic has go to firewall-02 (192.168.10.254)
--> and vlan 10 remote office traffic has go to WAN-RTR (192.168.10.253)
Write it out like this:
Source (x.x.x.x/y) --> needs to go to x.x.x.x/y
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 08:33 AM
Hello
@sangeethsan wrote:
for vlan 10 internet traffic has go to firewall-02 (192.168.10.254)
and vlan 10 remote office traffic has go to WAN-RTR (192.168.10.253)
So all vlan 10 (internet .office) traffic to go via just these two nex-hops correct and whatbout failover?
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 08:40 AM - edited 11-30-2020 08:46 AM
Hi Paul ,
Yes absolutely. The second firewall we have deployed newly. so my concern in to route the internet traffic of vlan 10 to firewall 2 and remote office traffic should go to 192.168.10.253.
How I can achieve this ? using PBR or any other terminology we can apply ??
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 08:56 AM
Hello
OKay would you try this and let me know how you get on,
no route-map PBR_IT_Internet_17_NW
ip access extended IT_Internet_17_NW
permit ip any 192.168.40.0 0.0.0.255
permit ip any 192.168.50.0 0.0.0.255
permit ip any 192.168.60.0 0.0.0.255
route-map PBR_IT_Internet_17_NW permit 10
match ip address IT_Internet_17_NW
set ip next hop 192.168.10.253
route-map PBR_IT_Internet_17_NW permit 99
set ip next hop 192.168.10.254
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 09:26 AM - edited 11-30-2020 09:49 AM
Hi Paul,
Please look into the results .Hopefully 80% working some fine tunes required.
C:\Users\TEMP>ipconfig
Windows IP Configuration
Ethernet adapter Ethernet:
Connection-specific DNS Suffix . : suntecsbs.com
Link-local IPv6 Address . . . . . : fe80::550b:7217:ba25:e39c%14
IPv4 Address. . . . . . . . . . . : 192.168.17.29
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . : 192.168.17.252
C:\Users\TEMP>
C:\Users\TEMP>
C:\Users\TEMP>ping 8.8.8.8
Pinging 8.8.8.8 with 32 bytes of data:
Reply from 8.8.8.8: bytes=32 time=20ms TTL=118
Reply from 8.8.8.8: bytes=32 time=20ms TTL=118
Reply from 8.8.8.8: bytes=32 time=20ms TTL=118
Reply from 8.8.8.8: bytes=32 time=20ms TTL=118
Ping statistics for 8.8.8.8:
Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),
Approximate round trip times in milli-seconds:
Minimum = 20ms, Maximum = 20ms, Average = 20ms
Trace complete.
==============================Internet traffic hiting to 192.168.10.254 but browser not working due dns=========================================
C:\Users\TEMP>
C:\Users\TEMP>
C:\Users\TEMP>tracert 8.8.8.8
Tracing route to 8.8.8.8 over a maximum of 30 hops
1 <1 ms <1 ms <1 ms 192.168.17.251
2 <1 ms <1 ms <1 ms 192.168.10.254 ==>>>>>>>>>>>>>>>>>>>>>>>>>>>>
3 1 ms 3 ms 1 ms 115.254.37.118
4 19 ms 19 ms 19 ms 74.125.51.2
5 39 ms 19 ms 19 ms 74.125.242.145
6 20 ms 20 ms 20 ms 216.239.42.215
7 20 ms 20 ms 20 ms 8.8.8.8
Trace complete.
=============== local DNS not resolving from vlan 10============
C:\Users\TEMP>nslookup
DNS request timed out.
timeout was 2 seconds.
Default Server: UnKnown
Address: 192.168.10.236
C:\Users\TEMP>
C:\Users\TEMP>nslookup
DNS request timed out.
timeout was 2 seconds.
Default Server: UnKnown
Address: 192.168.10.236
>
> youtube.com
Server: UnKnown
Address: 192.168.10.236
DNS request timed out.
timeout was 2 seconds.
DNS request timed out.
timeout was 2 seconds.
^C
C:\Users\TEMP>
=========local DNS from other network ========================
C:\Users\sangeethms>nslookup
Default Server: sbssvad10.suntecsbs.com
Address: 192.168.10.136
================local networks not reaching, so there is a chanace of DNS issue due to local network reachability===================
C:\Users\TEMP>ping 192.168.10.136
Pinging 192.168.10.136 with 32 bytes of data:
Request timed out.
Request timed out.
Request timed out.
Request timed out.
Ping statistics for 192.168.10.136:
Packets: Sent = 4, Received = 0, Lost = 4 (100% loss),
C:\Users\TEMP>ping 192.168.10.236
Pinging 192.168.10.236 with 32 bytes of data:
Request timed out.
Request timed out.
Ping statistics for 192.168.10.236:
Packets: Sent = 2, Received = 0, Lost = 2 (100% loss),
Control-C
^C
C:\Users\TEMP>ping 192.168.10.153
Pinging 192.168.10.153 with 32 bytes of data:
Request timed out.
R
==========================Remote office traffic going from vlan10 _working =====================================
C:\Users\TEMP>ping 192.168.40.252
Pinging 192.168.40.252 with 32 bytes of data:
Reply from 192.168.40.252: bytes=32 time=8ms TTL=250
Reply from 192.168.40.252: bytes=32 time=8ms TTL=250
Ping statistics for 192.168.40.252:
Packets: Sent = 2, Received = 2, Lost = 0 (0% loss),
Approximate round trip times in milli-seconds:
Minimum = 8ms, Maximum = 8ms, Average = 8ms
Control-C
^C
C:\Users\TEMP>tracert 192.168.40.252
Tracing route to 192.168.40.252 over a maximum of 30 hops
1 <1 ms <1 ms <1 ms 192.168.17.251
2 <1 ms <1 ms <1 ms 192.168.10.253==>>>>>>>>>>>>>>>>>>>>>>>>>>>>>working
3 7 ms 7 ms 7 ms 10.1.40.253
4 9 ms 9 ms 10 ms 192.168.40.252
C:\Users\TEMP>ping 192.168.40.251
Pinging 192.168.40.251 with 32 bytes of data:
Reply from 192.168.40.251: bytes=32 time=8ms TTL=58
Reply from 192.168.40.251: bytes=32 time=7ms TTL=58
Reply from 192.168.40.251: bytes=32 time=7ms TTL=58
Reply from 192.168.40.251: bytes=32 time=8ms TTL=58
Ping statistics for 192.168.40.251:
Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),
Approximate round trip times in milli-seconds:
Minimum = 7ms, Maximum = 8ms, Average = 7ms
C:\Users\TEMP>ping 192.168.40.248
Pinging 192.168.40.248 with 32 bytes of data:
Request timed out.
Reply from 192.168.40.248: bytes=32 time=18ms TTL=58
Reply from 192.168.40.248: bytes=32 time=8ms TTL=58
Reply from 192.168.40.248: bytes=32 time=8ms TTL=58
Ping statistics for 192.168.40.248:
Packets: Sent = 4, Received = 3, Lost = 1 (25% loss),
Approximate round trip times in milli-seconds:
Minimum = 8ms, Maximum = 18ms, Average = 11ms
C:\Users\TEMP>ping 192.168.40.245
Pinging 192.168.40.245 with 32 bytes of data:
Request timed out.
Request timed out.
Reply from 192.168.40.245: bytes=32 time=7ms TTL=249
Reply from 192.168.40.245: bytes=32 time=7ms TTL=249
Ping statistics for 192.168.40.245:
Packets: Sent = 4, Received = 2, Lost = 2 (50% loss),
Approximate round trip times in milli-seconds:
Minimum = 7ms, Maximum = 7ms, Average = 7ms
C:\Users\TEMP>ping 192.168.40.246
Pinging 192.168.40.246 with 32 bytes of data:
Request timed out.
Reply from 192.168.40.246: bytes=32 time=15ms TTL=58
Reply from 192.168.40.246: bytes=32 time=8ms TTL=58
Reply from 192.168.40.246: bytes=32 time=8ms TTL=58
Ping statistics for 192.168.40.246:
Packets: Sent = 4, Received = 3, Lost = 1 (25% loss),
Approximate round trip times in milli-seconds:
Minimum = 8ms, Maximum = 15ms, Average = 10ms
================================================================================
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 10:13 AM
Hi Paul,
If a PBR applied in ip local policy will help to resolve the local DNS ??
Now only existing issue is internet not getting due to local DNS resolution.
ICMP packets are hitting firewall-2 and going to public.
Pinging 8.8.8.8 with 32 bytes of data:
Reply from 8.8.8.8: bytes=32 time=20ms TTL=118
Reply from 8.8.8.8: bytes=32 time=20ms TTL=118
Reply from 8.8.8.8: bytes=32 time=20ms TTL=118
Reply from 8.8.8.8: bytes=32 time=20ms TTL=118
1 <1 ms <1 ms <1 ms 192.168.17.251
2 <1 ms <1 ms <1 ms 192.168.10.254 ==>>>>>>>>>>>>>>>>>>>>>>>>>>>>
3 1 ms 3 ms 1 ms 115.254.37.118
4 19 ms 19 ms 19 ms 74.125.51.2
5 39 ms 19 ms 19 ms 74.125.242.145
6 20 ms 20 ms 20 ms 216.239.42.215
7 20 ms 20 ms 20 ms 8.8.8.8
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 11:14 AM
Hello
@sangeethsan wrote:
Hi Paul,
If a PBR applied in ip local policy will help to resolve the local DNS ??
Now only existing issue is internet not getting due to local DNS resolution.
Local PBR realtes to traffic generated "locally" from the rtr itself, if this is what you mean?
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2020 08:49 PM - edited 11-30-2020 09:51 PM
Hi Paul,
Local PBR will help or not ? I am just asking to you.
Now i have analyzed the traffic of vlan10 to firewall-2 is passing without DNS resolving.
I have found inter vlan communication is not working now . All interface vlans are running in nexus 9000.
These vlans are not accessible from vlan10 and dns ( 192.168.10.136)is located inside vlan1 ( All infra servers are located in vlan1)
Once inter vlan communication issue we can resolve the DNS resolution will resolve automatically
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide