- Cisco Community
- Technology and Support
- Networking
- Routing
- VPN NAT IOS 8.3
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
VPN NAT IOS 8.3
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2010 03:00 AM - edited 03-04-2019 10:12 AM
We have successfully created various Site to Site VPN tunnels across our Cisco ASA 5520 infrastructure using the normal method off Internal LAN 10.137.230.x > No NAT > VPN Tunnel.
This has been done on your Firewall model which is shown below
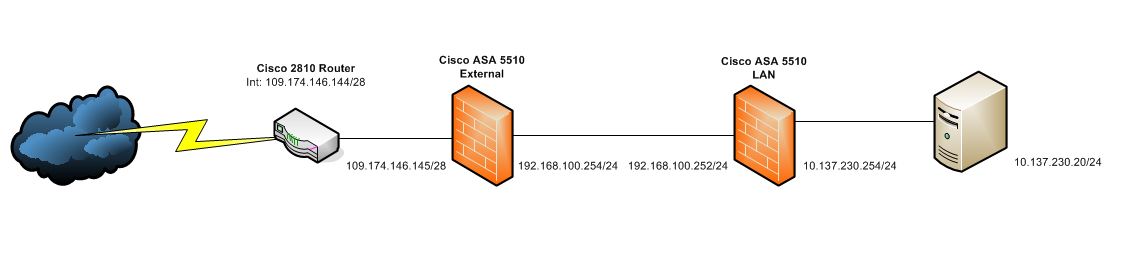
However, we now have to create a VPN tunnel to a third party where they want to do the following:
Internal LAN 10.137.230.x > NAT 109.174.146.130 > VPN Tunnel
Would anyone be able to help with this, it would be really appreciated.
- Labels:
-
Other Routing
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2010 03:09 AM
Assuming that traffic will always be initiated from the ASA site, you can configure NAT on the ASA, and crypto ACL will be sourcing from the NATed address (109.174.146.130) towards the remote end.
Let's make example that remote LAN is 192.168.1.0/24
object network vpn-10.137.230.0
subnet 10.137.230.0 255.255.255.0
object network obj-109.174.146.130
host 109.174.146.130
object network vpn-192.168.1.0
subnet 192.168.1.0 255.255.255.0
nat (inside,outside) source dynamic vpn-10.137.230.0 obj-109.174.146.130 destination static vpn-192.168.1.0 vpn-192.168.1.0
Crypto ACL will be as follows:
access-list cryptoACL permit ip host 109.174.146.130 192.168.1.0 255.255.255.0
Hope that helps.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2010 02:08 PM
Thank you for your help, I have applied the config, changing our external IP to a specific one for this VPN tunnel.
Will let you know what happens on Monday.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide


