- Cisco Community
- Technology and Support
- Networking
- Routing
- What’s New? IOS XE 17.9 Routing Release Update
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
What’s New? IOS XE 17.9 Routing Release Update
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-30-2022 01:05 PM - edited 08-30-2022 01:39 PM
Numerous enhancements to Cisco's routing portfolio were introduced with the release of IOS XE Cupertino 17.9 on August 30, 2022. Among the technologies updated in this release are security, virtual platforms, voice, quality of service, services, scale and performance, and a few minor updates to some of our Catalyst 8000 Edge platforms.
Now that we've established that, let's dive deeper into the specifics of each of these features.
Layer 2 Features
10GE MACSEC XPN Support on C8500L-8S4X
Currently, MACsec frames contain a 32-bit PN that is unique to each SAK. When the PN is depleted, a SAK rekey is performed to refresh the keys. The XPN feature in MKA/MACsec eliminates the common SAK rekeying issue that can occur in high-capacity links.
router(config)#mka policy xpn
router(config-mka-policy)#macsec-cipher-suite gcm-aes-xpn-128
router(config-mka-policy)#macsec-cipher-suite gcm-aes-xpn-256
router(config-mka-policy)#macsec disable-sci
router# show mka
router# show macsec
Today's Challenge
2^32 minimum-sized IEEE 802.3 frames can be sent in approximately 5 min at 10 Gb/s, which forces a SAK rekey. For higher capacity links, such as 40 Gb/s, PN will exhaust in a matter of seconds, bringing the overhead of frequent SAK rekeying to the control plane.
Enhancements Starting with 17.9
MKA/MACsec PI code already supports XPN; however, with 17.9, it is enabled on the PD side of the C8500L-8S4X.
Layer 3 Features
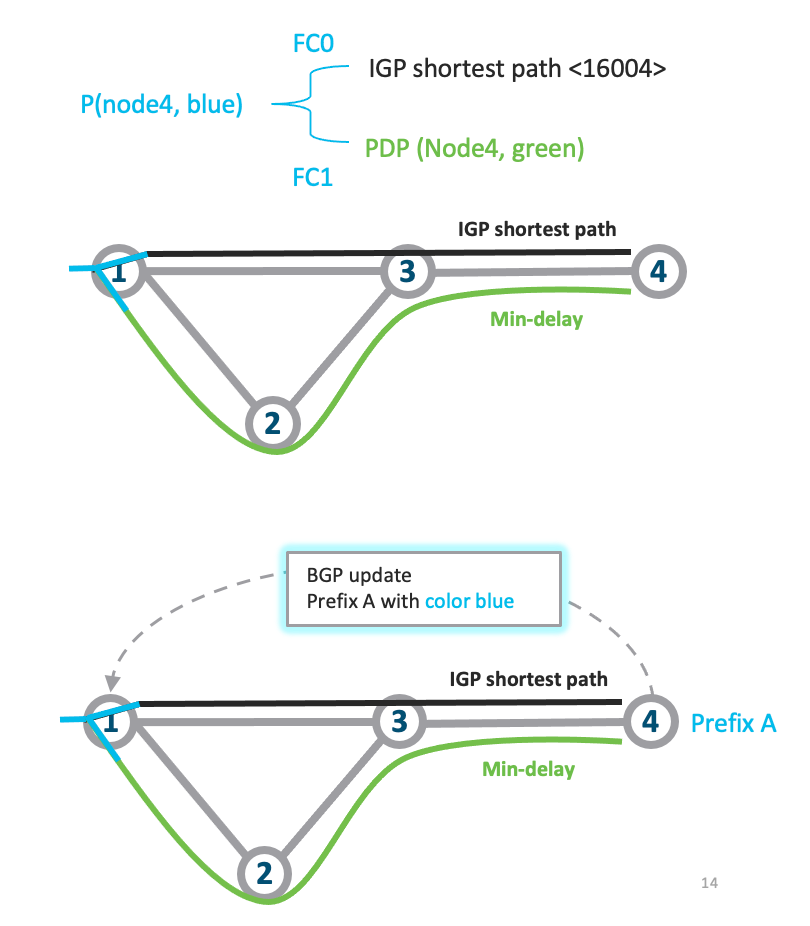
ODN - PFP with a RIB path
A PFP, like a PDP, is identified by <color, endpoint>. The configuration of a PFP distinguishes it from a PDP. PFP is configured with a per-flow forwarding class table of up to 8 entries instead of a dynamic/explicit path under path option. Each entry is identified by an FC and leads to a PDP or native RIB path. Each path option can have its own forwarding table and the same tie-breaking rule as in PDP is applied.
Color C is used to configure the PDP, which is then identified by PFP <C, PFP endpoint>. A default FC should be specified. If FC 0 is not explicitly configured, it becomes the default FC. Because of forwarding constraints, the default FC is not configurable and always uses FC 0 as the default.
Today's Challenge
The existing segment-routing traffic engineering policy, known as Per-Destination policy, directs all flows to the same destination on the same set of SID lists (PDP).
The Per-Flow policy (PFP) allows different flows, classified by forward class, that share the same destination to be directed to different SID lists.
Enhancements Starting with 17.9
The new feature will allow the configuration of a RIB Path on a Per-Flow-policy and be supported on the following platforms: RP2/ESP100, ASR1002-X, C8500, C8500L, C8300 and ISR4351.
ODN - PFP with a RIB path (was RIB Option) CLI Configuration
Configuration:
segment-routing traffic-eng
policy PERFLOW
color 10 end-point 1.1.1.1
binding-sid mpls 15001
candidate-path
preference 1
per-flow
forward-class 0 rib
forward-class 1 color 20
forward-class 2 color 30
Verification:
show ip route <>show segment-routing traffic-eng policy
IOS-XE Unicast to Multicast Service Reflection
The Cisco Multicast Service Reflection feature allows users to translate externally received multicast or unicast destination addresses to multicast or unicast addresses. The unicast to multicast service reflection feature allows users to convert unicast destination addresses to multicast addresses.
Today's Challenge
IOS-XE currently supports only IPv4 multicast to unicast and multicast to multicast translation/splitting. Multicast is typically not supported on WAN networks.
Enhancements Starting with 17.9
To bridge the feature gap between IOS and IOS-XE, IPv4 unicast to multicast translation/splitting will be supported in 17.9. This will be supported on the platforms ASR1K, ISR1K, ISR4K, and C8000.
Unicast-to-Multicast Service Reflection CLI Example Configuration and Explanation
interface Vif1
ip service reflect GigabitEthernet5 destination 66.0.0.7 to 239.3.3.0 mask-len 32 source 10.1.1.2
ip service reflect GigabitEthernet5 destination 66.1.1.0 to 239.2.2.0 mask-len 24 source 10.1.1.4
!
ip route 66.0.0.7 255.255.255.255 Vif1
ip route 66.1.1.0 255.255.255.0 Vif1
-
Source filter is GigabitEthernet5. Target traffic enters GigabitEthernet5. Null source filter means all interface traffic is target traffic.
-
'66.0.0.7' targets traffic with dst ip 66.0.0.7.
-
'239.3.3.0' is the translated multicast ip address.
-
Mask-len '32' means 66.0.0.7/32 traffic from 10.1.1.2 will be translated to 239.3.3.0/32. (after translation).
-
Mask-len '24' means 66.1.1.0/24 traffic from 10.1.1.4 will be translated to 239.3.3.0/24. (after translation). 66.1.1.222239.3.3.222
-
Static route is required to reach VIF1.
-
Static route prefix/mask must match SR destination/mask-len.
Unicast-to-Multicast Service Reflection CLI Verification
router# show ip mroute
(*, 239.0.0.0), 00:04:49/stopped, RP 192.168.0.254, flags: SJCF
Incoming interface: Null, RPF nbr 0.0.0.0
Outgoing interface list:
GigabitEthernet3, Forward/Sparse, 00:04:49/00:02:39, flags:
(10.1.1.2, 239.0.0.0), 00:00:05/00:02:54, flags: FT
Incoming interface: Vif1, RPF nbr 0.0.0.0
Outgoing interface list:
GigabitEthernet3, Forward/Sparse, 00:00:05/00:03:24, flags:
router# show platform hardware qfp active feature uni-sr
Vif1:
unicast service reflect info:
vif name: Vif1
vif if_handle: 2013
ingress name: Ethernet0
ingress if_handle: 10
replica count: 1 replica rule HW addr: 0x00000000e94e5c10
hash val: 5
prefix: 10.1.1.2/32
replica node info:
translated source: 10.1.1.2
translated destination: 239.3.3.0/32
replica rule HW addr: 0x00000000ead98880
match: octets 164427264 packets 1712784
router# show ip cef
10.1.1.2/32 attached Vif1
router# show ip mfib 239.3.3.0
(10.1.1.2,239.3.3.0) Flags: HW
SW Forwarding: 0/0/0/0, Other: 1/0/1
HW Forwarding: 1379885/2999/96/2249, Other: 0/0/0
Vif1 Flags: A NS
GigabitEthernet4 Flags: F NS
Pkts: 0/0/0 Rate: 0 pps
Support NAT Destination IP Logging in CGN Mode
Because Carrier Grade NAT (CGN) tracks only local address local port binds, destination IP and port are not logged when generating HSL records in CGN mode. In classic NAT mode, the destination IP and port are logged. When the destination IP and port must be present in log records, the general recommendation is to use classic NAT mode.
Today's Challenge
The customer, on the other hand, requires EIM (Endpoint Independent Mapping) and EIF (Endpoint Independent Filtering). Because EIF is not possible in classic NAT mode, the customer is unable to use it.
Enhancements Starting with 17.9
Only Autonomous mode is supported. This feature is supported by all platforms that support IOS XE NAT.
NAT Dest IP logging in CGN Mode Configuration and Verification
Device(config)# ip nat settings log-destination
Device(config)# end
Device#show run | include log
ip nat settings log-destination
ip nat log translations flow-export v9 udp ipv6-destination 2001::2 30000 source GigabitEthernet0/0/3
ip nat log translations flow-export v9 udp destination 172.27.61.85 20000
Some restrictions with this feature are;
- No Box-to-Box (B2B) HA for logging in 17.9
- No support for NAT64 CGN mode in 17.9
OGACL & ACL Scale Improvement
The Object Groups for ACLs feature allows you to group users, devices, or protocols and then apply those groups to access control lists (ACLs) to create access control policies for those groups. Recently, customers request that the scale number per ACL/OGACL be increased to a higher number.
Today's Challenge
The current Common Adaptive Classification Engine (CACE) has a limit of 64K entries. This means that in software TCAM, we can have a maximum of 64K ACE per ACL and a maximum of 64K networks in source/destination object groups per policy.
Enhancements Starting with 17.9
With the 17.9 release for the specified platforms, the scale is automatically increased.
OGACL & ACL Scale Improvement and Platforms Supported
NOTE: No CLI needed to increase the ACL scale.
AggGEC spread across multiple QFP 2.0 ASICs
An EtherChannel enables the combination of multiple physical Ethernet links into a single logical link. If a segment within an EtherChannel fails, traffic previously carried over the failed link switches to the EtherChannel's remaining segments.
Today's Challenge
All AggGEC QoS hierarchies were previously assigned to QFP0, limiting the aggregate throughput of all AggGECPort-channel interfaces to around 40 Gb/sec.
Enhancements Starting with 17.9
This feature adds CLI support for specifying Aggregate GEC QoS recycle core to be used for Aggregate GEC Port channel interface to the ESP100, ESP200, and ASR1002-HX platforms.
The aggregate throughput for the ESP100, ESP200, and ASR1002-HX platforms can be increased to approximately 80 Gb/sec by using multiple QFPs. However, due to inter-QFP bandwidth constraints, the ESP200 is limited to 80 Gb/sec.
platform qos port-channel-aggregate 12 2 (QFP number)
E911 PSAP and Selective router for C1100 Terminal Services Gateway
PSAP (Public Safety Answering Point) is a feature that allows you to connect to a serial port via telnet. It allows you to send the "H" character as a heartbeat to keep the session alive.
Selective Router – X25 serial port support, enables XOT support for X.25 to IP network translation.
Today's Challenge
When the ISR4000 platforms were introduced, this functionality was not included in IOS XE.
Enhancements Starting with 17.9
This feature adds ISR-G2 support for PSAP (Public Safety Answering Point) and selective router functionality. It will now be supported in tandem on the C1100 TSG.
Security Features
IPSec Dual Stack Feature for CISCO to 3rd party router
'Dual Stack' refers to the ability to carry both v4 and v6 traffic using a single SA over v4 underlay transport.
Today's Challenge
In its current implementation, IPsec makes a clear distinction between IPv4 and IPv6 policies. The native SVTI tunnel interface creates a single IPv4 proxy based on transport end points. It can only carry that type of traffic.
Enhancements Starting with 17.9
This feature is supported only on C8500, C8300, C8200, ASR1K, ISR4K and ISR1K platforms. Note: Dual Stack feature will be supported with IKEv2 only.
Sample IPSec Dual Stack Configuration
interface Tunnel1
ip address 100.100.100.1 255.255.255.0
tunnel source Ethernet0/0
tunnel mode ipsec <dual-overlay> <- Tunnel mode change to dual-overlay to support both v4 and v6
tunnel destination 1.1.1.2
tunnel protection ipsec profile ipsecprof
IPSec Dual Stack Verification “show” commands
Show crypto session [detail]
Show crypto ipsec saShow crypto map
Show crypto socket
Show crypto ikev2 session [detail]
Virtual Platform Features
C8000V: Mellanox CX5 100G NIC Support on KVM
Mellanox ConnectX-5 adapter cards allow data center administrators to benefit from improved server utilization as well as lower costs, power consumption, and cable complexity by allowing more virtual appliances, virtual machines (VMs), and tenants to coexist on the same hardware.
Today's Challenge
Increased throughput performance on the Catalyst 8000V has been requested by customers as well as stated as a competitive positioning statement.
Enhancements Starting with 17.9
C8KV now supports Mellanox CX-5 NICs drivers for SR-IOV / DPDK on generic RHEL KVM systems. This feature is dedicated to support CX5 VF only.
C8000V: Mellanox CX5 100G NIC Support on KVM CLI Verification
Router# sh platform software vnic-if database
vNIC Database
eth01_1636486309782733063
Device Name : Gi3
Driver Name : mlx5_core
MAC Address : 5254.0028.a404
PCI DBDF : IFDEV_SERVER_UIO
Management : no
Status : supported
Rec Status : added
Eth02_1636486314942226959
Device Name : G2
Driver Name : mlx5_core
MAC Address : 5254.006d.16b4
PCI DBDF : IFDEV_SERVER_UIO
Management : no
Status : supported
Rec Status : added
NOTE : “show platform software vnic interface-mapping” will indicate the new CX5 driver as mlx5_core will be a direct PCI address.
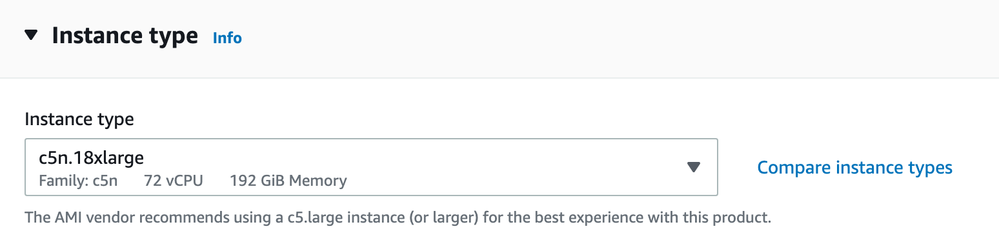
Catalyst 8000V Cloud Throughput Performance Enhancement (c5n.18xl)
Since the Catalyst 8000V's availability on cloud providers, customers have requested increased throughput performance.
Today's Challenge
Prior to 17.9, the number of cores the C8000V could use was limited by the currently supported AWS instance sizes, affecting maximum overall performance.
Enhancements Starting with 17.9
To improve throughput performance, this feature will support the AWS c5n.18xlarge instance size. Supporting this larger instance size in AWS will enable support for up to 16 vCPU, allowing for increased throughput.
There are no configuration commands for this feature, but we can check if the multi TXQs are being used with the following command:
Router# sh plat hard gfp act dat inf sw-nic
AWS IPSEC performance enhancement can be achieved through efficiently utilizing a higher count of PMD TXQs, which the c5n.18xl has:
Minor Feature Updates for 17.9.1
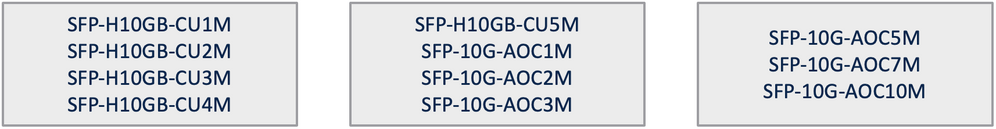
10G SFP support on C8300
Supported Platforms: C8300-2N2S-4T2X and C8300-1N1S-4T2X. New 10G SFP+ support on the C8300 product family on front panel ports where 10G SFP+ are available.
Disable USB port on C8500-12X & C8500-12X4QC
Adds support for being able to disable the front side USB port via CLI in autonomous and SDWAN mode on C8500-12X and C8500-12X4QC
Added CLI:
platform usb disable
Disable USB port on C8500L-8S4X
Adds support for being able to disable the front side USB port via CLI in autonomous and SDWAN mode on C8500L-8S4X
Added CLI:
platform usb disable
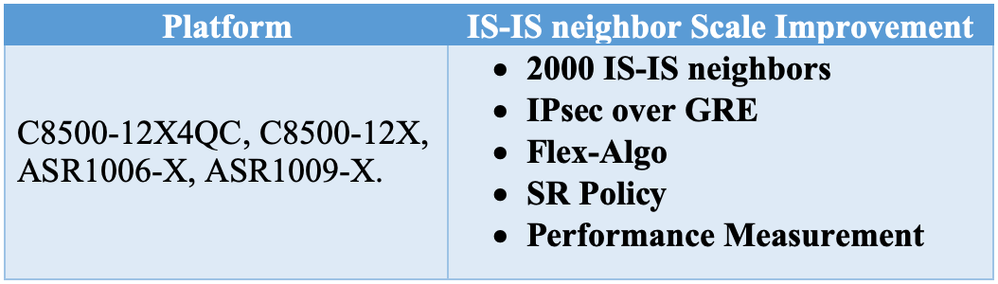
Scale Test Features for 17.9 Release
IS-IS neighbor scale improvement for SR-TE
In XE 17.9 we improve the scale to 2000 IS-IS neighbors for SR-TE deployment. The scale is applicable for following platforms and deployment:
NOTE : no CLI to increase the scale. The scale is increased automatically with 17.9 release for the specified platforms
- Labels:
-
Routing Protocols
-
WAN
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide