- Cisco Community
- Technology and Support
- Networking
- SD-WAN and Cloud Networking
- Qs About Viptela Undelay and Overlay design?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Qs About Viptela Undelay and Overlay design?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-23-2021 11:14 PM
Hi All.
I'm currently reviewing SDWAN and I have question regarding how the technology works & design especially on Underlay and Overlay.
Questions:
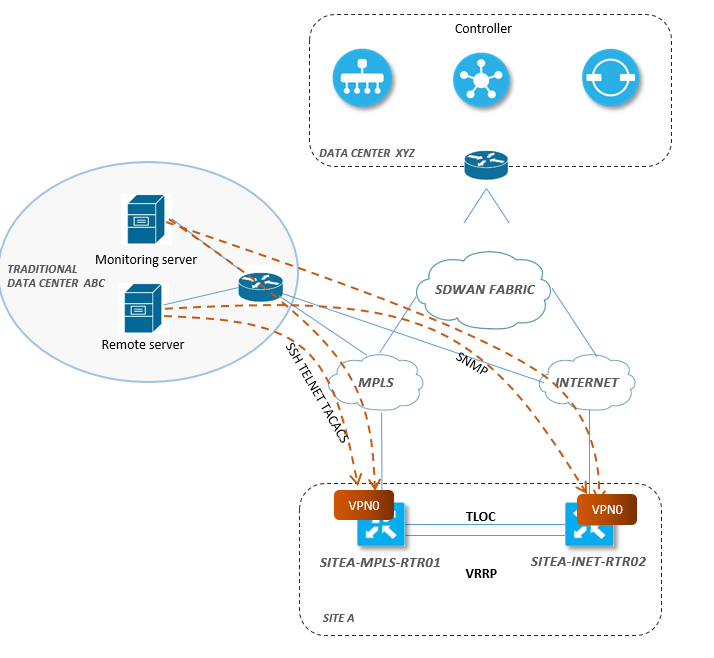
a. Let say we have a centralize monitoring server and remote server which is connected to MPLS (traditional way). Basically we just monitor the WAN IP and loopback mgmt IP of the WAN routers, Since from traditionally we just announce the mgmt to MPLS network or if internet router we build a secure connection to HUB or headend device or directly accessing the RTR using it WAN public IP. What approach should we do when migrating to SDWAN.
Does all remote connection and monitoring of vedge/controller should be on its VPN 512? Or this falls to VPN 0 Transport interface? What is your typical design/approach on this?
- Is it required to have a vEdge component on one of the Data center in where the vedge will participate or connect in SDWAN fabric? In below design, I will add a vedge on either DC ABC or at DC XYZ?
b. How interconnection/communication between the traditional remote site setup and sdwan site infra? Do we need to route the traffic from traditional remote site setup to DC to SDWAN fabric?
c. Common design in data center for underlay and overlay. Should we also do load balancing or we can also use a active/standby or per flow basis?
d. How default routing being implemented. If Multiple default route being use, does it means it being load balance? If Yes, How can we verify the actual exit interface of the traffic (ex. in traditional we have show ip cef) or we just based on flow output ?
e. If we need to forward Customer Internet traffic directly to internet of the site, We can achieve this by route leaking. but the question is that .. If we have multiple default route on transport vpn how can we ensure that all data traffic will be forwarded only to internet circuit not on MPLS do we have option to select a specific transport exit interface when using route leaking ?
I'm still reviewing the design guide and continuously reviewing the SDWAN. Just add this question maybe you can share the actual implementation on your end. Thanks
- Labels:
-
SD-WAN Architecture
-
SD-WAN vManage
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-24-2021 02:15 AM
Do all remote connection and monitoring of vedge/controller should be on its VPN 512? Or does this falls to the VPN 0 Transport interface? What is your typical design/approach on this?
Typically the remote branch routers will not have VPN 512 is used for the device management.
If the NMS systems are hosted in the ISP network then Syslog, SNMP, and Netflow (Cflowd) can be sourced from VPN0 and if the NMS system is hosted in customer DC then you can create a loopback IP address in service VPN and source from there.
How interconnection/communication between the traditional remote site setup and sdwan site infra? Do we need to route the traffic from the traditional remote site setup to DC to SDWAN fabric?
The most common approach is traffic between SD-WAN migrated site and Non-SD-WAN is done via DC.
However, you can explore the global route to the Service side route leaking feature if that fits your requirment.
Should we also do load balancing or we can also use a active/standby or per flow basis?
Bandwidth Augmentation by load balancing traffic across the available link key feature of Cisco SD-WAN and enable by default. But if your customer has a specific use case where they do not want certain applications not to be load balance then you can either make links active-standby or else you can data policy to traffic pinning.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-26-2021 12:40 AM
@mohspate , Thank you for your input and this is very informative. Now, it is time for me to apply this on my LAB.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide