- Cisco Community
- Technology and Support
- Service Providers
- Service Providers Knowledge Base
- ASR9000 Understanding the BNG configuration (a walkthrough)
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 11-07-2011 01:58 PM
Introduction
In this document we're walking through a configuration setting up BNG for IPoE and PPPoE. The Setup for this configuration is similar to the setup you can see in the YouTube video for an ip sessions demo.
Problem Description
Detailed description of how to set up the configuration and the options establishing PPPoE and IPoE sessions. Understanding the anatomy of a control policy language.
Setup
Configuration and Explanations
hostname A9K-BNG
radius-server host 3.0.0.38 auth-port 1645 acct-port 1646
!Radius-server definition with ip address and UDP ports it is going to !use.
key 7 045802150C2E
!Secret key for the radius communication
timeout 1
!Maximum time waiting for response
retransmit 1
!Maximum number of times you retransmit the request, after waiting <timeout> time.
!COA server definition
aaa server radius dynamic-author
port 1700
!COA port is standard 1700
client 3.0.0.1 vrf default server-key 7 13061E010803
client 10.86.1.49 vrf default server-key 7 14141B180F0B
!The clients from which we are going to accept a COA Response.
!Attribute definitions that we can reference for the nas-port
!building.
!”MY_AUTH” will take the mac address, circuit ID and remoteIDand
!append them together separated by hash signs. If one of the fields is
!not available, an empty string will be provided for that portion.
!example 0000.1111.2222##remoteid or 0000.2222.1111#circ#remote
!
aaa attribute format MY_AUTH
mac-address plus circuit-id plus remote-id separator #
!
aaa attribute format NAS_PORT_FORMAT
circuit-id plus remote-id separator .
! Nas-port computation for PPPoE(32) and if not pppoe then follow the
! global (non typed) logic
aaa radius attribute nas-port format e SSAAPPPPQQQQQQQQQQVVVVVVVVVVUUUU type 32
aaa radius attribute nas-port format e SSAAPPPPQQQQQQQQQQVVVVVVVVVVUUUU
!Set up the XR nas-port-id (attr87) for sessions following the nas-
!port format instructions above.
aaa radius attribute nas-port-id format NAS_PORT_FORMAT
!Set up for AAA usage. Note that we don’t have “aaanew-model” in
!XR. Also “subscriber” is used for BNG. Method “PPP” is used for
!serial PPP.
aaa authorization subscriber default group radius
aaa authentication subscriber default group radius
!DHCP configuration
dhcp ipv4
!specify a profile name and define what method is used, relay, proxy
!or snooping.
profile AutoSelectGiaddr proxy
!Different classes may be defined. This is not necessarily the
!vendor class, but here we can check certain options in the discover
!to selectively set the helper address and giaddr. That last one
!will affect the pool we’re going to use on the dhcp server.
class HardPhone1
match option 60 hex 4861726450686F6E6531 mask 0
!the option 60 is vendor-class followed by a hex string. I chose it
!to match the “class” section from the line above, but that is not
!necessary. The mask defines which bytes are must match and don’t
!cares. Mask of 0 means full match.
helper-address vrf default 81.1.1.2 giaddr10.1.1.254
!
class HardPhone2
match option 60 hex 4861726450686F6E6532 mask 0
helper-address vrf default 81.1.1.2 giaddr172.28.15.254
!
relay information option
relay information policy replace
relay information option remote-id testme
relay information option allow-untrusted
! This configuration above defines the option 82 handling.
! Allow untrustedmeans that we accept dhcp discovers with a 0.0.0.0
! giaddr, which is normally the case when there is no relay between
! the client and the 9k.
Relay information Policy:
Case # | Received Packet Option-82 Suboptions | Configured Option-82 Suboptions | Forwarded Packet Option-82 Suboptions for Full-Option-82 keep | Forwarded Packet Option-82 Suboptions for Individual-Suboption keep | Forwarded Packet Option-82 Suboptions for replace | ||||||||||
1 | “rx-cid” | “rx-rid” | “in-rid” | vpn-id | “rx-cid” | “rx-rid” | “rx-cid” | “rx-rid” | vpn-id | “rx-cid” | “in-rid” | vpn-id | |||
2 | “rx-cid” | “in-rid” | vpn-id | “rx-cid” | “rx-cid” | “in-rid” | vpn-id | “rx-cid” | “in-rid” | vpn-id | |||||
3 | “in-rid” | vpn-id | “in-rid” | vpn-id | “in-rid” | vpn-id | “in-rid” | vpn-id | |||||||
! Define the interfaces and the attached profiles
interface Bundle-Ether100.2 proxy profile AutoSelectGiaddr
interface Bundle-Ether1001.2 proxy profile AutoSelectGiaddr
!
pppoe bba-group X
tag ppp-max-payload minimum 1200 maximum 2000
service selection disable
! PPPoE group definition. Currently there is limited service selection
!support (just matching on service name). The COS values for PPPoE
!control can be defined here and the processing/support for max-
!payload tag. In IOS you could configure the processing of vendor-tags
!and strip them selectively. In XR we always process the tags and we
!always strip them from a PADR
!IP address pool definition
pool vrf default ipv4 POOL
address-range 199.1.1.1 199.1.255.255
!
!The dynamic templates are like IOS virtual-templates. The base !configuration for each session is defined here. L3 features as well !as PPP specific parameters are defined here.
dynamic-template
type ppp TPL
ppp authentication chap
ppp ipcp dns 1.2.3.4 1.2.3.3
ppp ipcp peer-address pool POOL
ipv4 unnumbered Loopback1000
!
type ipsubscriberIPSUB
ipv4 unnumbered Loopback12
ipv4 access-group IPSUB_FAIL_ACL ingress
ipv4 access-group IPSUB_FAIL_ACL egress
!Few ACL definitions referenced in the radius profile, qos class-maps
!or in the dynamic template.
ipv4 access-list PERM_ALL
10 permit ipv4 any any
20 permit icmp any any
!
ipv4 access-list lab-video
20 permit udp any any eq 5544
30 permit udp host 49.1.1.2 any
!
ipv4 access-list IPSUB_FAIL_ACL
5 permit icmp any any
10 permit tcp any host 49.1.1.2 eqwww
15 permit tcp host 49.1.1.2 eqwww any
20 deny ipv4 any any
!QOS class-map used in COA parameterized QOS requests
!remember that with pQOS you can define the policy-map via RADIUS,
!however you need to define your class-maps locally in XR.
class-map match-any VIDEO
match access-group ipv4 lab-video
end-class-map
!
class-map match-any 3play-voip
match access-group ipv4 telnet
end-class-map
!These are the class-maps used later in the control policy. You can
!match on various aspects of the interface/session. Like username,
!domain. In this case we have simple class-maps that match on the
!protocol so we are doing to differentiate between PPP and IPsubs
!
class-map type control subscriber match-any PPP
match protocol ppp
end-class-map
!
class-map type control subscriber match-any DHCP
match protocol dhcpv4
end-class-map
!
!In this sample class-map we are taking the username and apply a
!separator switch on it as defined in the “format DOMAIN” attribute
!definition and see if that domain name matches “vrf_vpn”
class-map type control subscriber match-any matchdomain
match domain vrf_vpn format DOMAIN
end-class-map
!
!This is the most important part, the XR control Policy.
policy-map type control subscriber sub
event session-start match-first
!
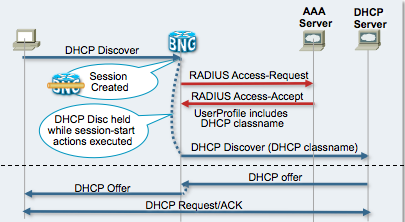
!Events: during the session life time, various events are triggered. !In this case a session-start event we provide a handler for. This is
!the reception of a PADI for pppoe sessions or a dhcp discover for IP
!sessions.
!The match-first describes that we are only handling one class of the !event, and the class that we match first.
!This as opposed to match-all, which means that we will traverse all
!classes to see if they match and execute the actions defined
!underneath the class.
!
Event | What does it do or when is it triggered? |
session-start | when we get the first sign of life (for pppoe that is at PADR) |
session-activate | This is done at the authentication phase – i.e. when we’ve got the username/password (or challenge/response) (PPPoE ONLY) |
authentication-failure* | when we receive an access-reject from radius |
authentication-no-response | when the method list for authentication request does not return any response (success/reject) |
authorize-failure* | when we receive an access-reject from radius |
authorize-no-response | when the method list for authen or author does not return any response (success/reject) |
service-stop | when a service that is applied to the session is removed or stopped |
class type control subscriber CLASS do-until-failure
!
!CLASS: Underneath that event, we define the classes. In this example
!I created 2 classes to match specifically on DHCP and PPP sessions.
!I can have 1 control policy with 1 event, and then the class
!differentiator to determine what I want to do specifically/separately
!for both session types.
!
Do until? | What does it do? |
do-until-failure | Until we receive a failure (eg access reject or no radius response or feature application failure) We stop the execution. |
do-until-success | When we successfully executed the task we stop. |
do-all | Regardless of the success or failure all actions are executed |
!
10 activate dynamic-template TPL
!
!Activation of the dynamic template configuration. PPP will take the !LCP parameters and auth protocol from there.
!
!Class-actions:
!
event session-activate match-first
class type control subscriber CLASS do-until-failure
10 activate dynamic-template TPL
20 authenticate aaa list default
- Authenticate: Use the username and password from the line and send it to the servers defined in the list
- Authorize: More flexible then authenticate, still the SAME radius request (access-request) but flexibly formatted with a username composed of different information such as domain, circuit-id, nas-port etc
Note: Because authenticate uses the line username, it is generally useless on the session-start event, the authorize with which you compose the username based on mac/circuit id etc is very useful in both session start and activate
!
!
end-policy-map
!
policy-map type control subscriber ipsub
event session-start match-first
class type control subscriber DHCP do-until-failure
10 authorize aaa list default identifier source-address-mac password cisco
! Use the authorize here to compose the username to be sent to
! radius. In this case we use pw cisco as the password.
!
end-policy-map
! Define the bundle-ether master and configure for destination ip
! based loadbalancing, this so each subscriber hashes all its traffic ! onto one member only for accurate QOS
interface Bundle-Ether100
bundle load-balancing hash dst-ip
! The IP session interface must have an ip address. This in order to
! accept ip packets, the dhcpdiscover.
! If the unicast flag is set, like in MAC OSX or WXP (IOS dhcp client
! leaves the broadcast flag), then this address MUST be the same as
! the subnet for the ip sessions. If it is not the same we can’t
! unicast the offer.
interface Bundle-Ether100.2
ipv4 address 87.78.77.1 255.255.255.0
service-policy type control subscriber ipsub_fancy_auth
encapsulation dot1q 2
ipsubscriber ipv4 l2-connected
initiator dhcp
initiator unclassified-source
!
! Define the bundle sub interface for the right vlan, enable for PPPoE
! via the bba-group and attach the control policy
interface Bundle-Ether100.20
service-policy type control subscriber sub
pppoe enable bba-group X
encapsulation dot1q 20
! Loopback interface for ppp sessions
interface Loopback1000
ipv4 address 101.101.1.1 255.255.255.255
!
interface GigabitEthernet0/0/0/19
! Enable LACP on the bundle member and set it to bundle-e100
bundle id 100 mode active
load-interval 30
!
interface GigabitEthernet0/1/0/19
! Enable LACP on the bundle member and set it to bundle-e100
bundle id 100 mode active
load-interval 30
Show command verification
RP/0/RSP0/CPU0:A9K-BNG#show subscr ses all det
Mon Nov 7 17:20:27.701 EDT
Interface: Bundle-Ether100.2.ip5
Circuit ID:
Remote ID: testme
Type: IP: DHCP-trigger
IP Address: 172.28.15.1, VRF: default
Mac Address: 0019.2f43.9a38
Account-Session Id: 00000044
Nas-Port: 67108896
Username: unknown
Subscriber Label: 0x00000044
Created: Thu Nov 3 16:26:33 2011
State: Activated
Authentication: unauthenticated
Access-interface: Bundle-Ether100.2
Policy Executed:
policy-map type control subscriber ipsub_fancy_auth
event Session-Start match-first [at Thu Nov 3 16:26:33 2011]
class type control subscriber DHCP do-until-failure [Succeeded]
5 activate dynamic-template IPSUB [Succeeded]
10 authorize aaa list default [Failed]
Session Accounting: disabled
Last COA request received: never
User Profile Attribute List: None
Interface: Bundle-Ether100.100.pppoe2
Circuit ID: Unknown
Remote ID: Unknown
Type: PPPoE:PTA
IP Address: 199.1.1.2, VRF: default
Mac Address: 0019.2f43.9a38
Account-Session Id: 00000145
Nas-Port: 67110466
Username: test
Subscriber Label: 0x00000145
Created: Thu Nov 3 16:28:10 2011
State: Activated
Authentication: authenticated
Access-interface: Bundle-Ether100.100
Policy Executed:
policy-map type control subscriber sub
event Session-Start match-first [at Thu Nov 3 16:28:10 2011]
class type control subscriber CLASS do-until-failure [Succeeded]
10 activate dynamic-template TPL [Succeeded]
event Session-Activate match-first [at Thu Nov 3 16:28:31 2011]
class type control subscriber CLASS do-until-failure [Succeeded]
10 activate dynamic-template TPL [Succeeded]
20 authenticate aaa list default [Succeeded]
Session Accounting: disabled
Last COA request received: never
User Profile Attribute List: 0x500c0d24
1: service-type len= 4 value= Framed
2: sub-qos-policy-out len= 5 value= shape
Related Information
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Xander,
I already configure this for option-82 :
!
dhcp ipv4
profile DHCP-PROXY-DATA proxy
helper-address vrf default 10.211.x.y giaddr 10.10.a.b
helper-address vrf default 10.211.x.z giaddr 10.10.a.b
relay information option
relay information policy keep
relay information option allow-untrusted
!
interface Bundle-Ether2.10 proxy profile DHCP-PROXY-DATA
but I cant see any option82 value whether from debug dhcp ipv4 proxy event / debug dhcp ipv4 packet ("not inserted option82") and show dhcp ipv4 proxy binding details (insertedCurcuitID & InsertedRemoteID = -)
I also set a username to forard to AAA using remot-id but because option82 is not inserted, the aaa didn't find any value for the username.
looking forward for your feedback.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Option 82 is generally inserted by a etherlike dslam or switch. If you connect your computer directly to a port then there is likely no option 82 info available.
If the debugs don't print it, in this case for sure, it is not received.
xander
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Xander,
Thanks for the feedback. In addition, I'm not connecting the dummy client directly to ASR, but via L2 switch instead. since connectivity from dummy client to ASR resides on the same broadcast domain, this should be justified to get the option82 right ?
thanks in advance
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
If your switch is capable of intercepting the dhcp discover and insert the option 82 info (usually done via configuration on the connected interface) then the 9k would see it and can use it.
There are some cisco metro switches that can do that, but not every device.
xander
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Xander,
thanks again for the feedback. Does it means that i have to insert opt82 on L2 switch even if the client and9k relies on same segment ? I already tried both either using ip dhcp relay information option / ip dhcp snooping information option (but helper-address located on 9k) but still there's no opt82 on 9k. I'm using cat6506 as L2 switch..
looking forward for your response
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Lets assume the following topology:
CPE---DSLAM/Etherswitch----BNG----dhcp_server
The cpe sends the discover, without any o82. The dslam/etherswitch is now acting as a relay agent and when instructed, it can intercept the dhcp discover and add this o82 info in there when it forwards it on to the BNG.
The BNG, can then interpret this info, modify it and proxy the dhcp request over to the server.
The 9k CAN insert and modify the circuit ID and remote ID no problem, but normally you'd want the AN (access node) to do that so we get the specific line info from the AN to which the CPE is connected. As the BNG would only have an "aggregated" view of the lineID (i.e. it came in on my bundle-e100, but that potentially terminates thousands of subs).
Some example ofr the switch and option 82 is here.
There should be some more doc on the switch side also and I have seen some IOS images able to configure customized strings on a per access interface basis too.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello Xander,
great walkthrough. I am tying to configure IPoE on ASR9001 4.3.0. PPPoE is already tested and it works great.
Now it's time to do some testing for the IPoE/DHCP feature. I used your documents on support forum and this pdf
"Residential Broadband Subscriber Aggregation and BNG Deployment Models" from Cisco Live.
Config looks like this:
dhcp ipv4
profile IP_SUB proxy
helper-address vrf default 10.100.14.36 giaddr 10.100.30.1
!
interface Bundle-Ether992.3127 proxy profile IP_SUB
ipv4 access-list HTTPRDRT_ACL
10 permit tcp any any eq www
!
ipv4 access-list IPSUB_ACCLIST
10 permit tcp any host 10.100.14.108 eq www
15 permit icmp any any
!
class-map type traffic match-any IPSUB_ACL
match access-group ipv4 IPSUB_ACCLIST
end-class-map
!
class-map type traffic match-any HTTPRDRT_CM
match access-group ipv4 HTTPRDRT_ACL
end-class-map
policy-map type pbr HTTP_REDIRECT_PBR
class type traffic IPSUB_ACL
transmit
!
class type traffic HTTPRDRT_CM
http-redirect 10.100.14.108
!
class type traffic class-default
drop
!
end-policy-map
nterface Bundle-Ether992.3127
description # IPSUB #
ipv4 point-to-point
ipv4 unnumbered Loopback30
service-policy type control subscriber IP_SUB_PMAP
encapsulation dot1q 3127
ipsubscriber ipv4 l2-connected
initiator dhcp
initiator unclassified-source
interface Loopback30
ipv4 address 10.100.30.1 255.255.255.0
dynamic-template
type service HTTP_FORCE_REDIRECT
service-policy type pbr HTTP_REDIRECT_PBR
!
type ipsubscriber IPSUB_TEMPLATE
accounting aaa list default type session
!
class-map type control subscriber match-any IP_SUB
match protocol dhcpv4
end-class-map
!
!
class-map type control subscriber match-all AUTH_TIMER_CM
match timer AUTH_TIMER
match authen-status unauthenticated
end-class-map
!
policy-map type control subscriber IP_SUB_PMAP
event session-start match-first
class type control subscriber IP_SUB do-until-failure
10 activate dynamic-template IPSUB_TEMPLATE
20 activate dynamic-template HTTP_FORCE_REDIRECT
30 set-timer AUTH_TIMER 10
!
!
event account-logon match-first
class type control subscriber IP_SUB do-until-failure
10 authenticate aaa list default
20 deactivate dynamic-template HTTP_FORCE_REDIRECT
!
!
event timer-expiry match-first
class type control subscriber AUTH_TIMER_CM do-until-failure
10 disconnect
!
!
end-policy-map
I am using a DHCP server on Windows Server and I see that the BNG gets the IP address from the DHCP server
(DHCP server on Linux was not working for some reason)
Problem is that I don't get the IP address on my test PC that is sending the DHCP DISCOVER.
On BNG I can see the subscriber:
show subscriber session all
Wed Jul 17 15:17:27.594 UTC
Codes: IN - Initialize, CN - Connecting, CD - Connected, AC - Activated,
ID - Idle, DN - Disconnecting, ED - End
Type Interface State Subscriber IP Addr / Prefix
LNS Address (Vrf)
--------------------------------------------------------------------------------
IP:DHCP No CD 10.100.30.2 (default)
show subscriber session all detail
Wed Jul 17 15:53:06.363 UTC
RP/0/RSP0/CPU0:BNGDEMO#show subscriber session all detail
Wed Jul 17 15:53:28.965 UTC
Interface: None
Circuit ID: Unknown
Remote ID: Unknown
Type: IP: DHCP-trigger
IPv4 State: Up Pending, Wed Jul 17 15:53:16 2013
IPv4 Address: 10.100.30.2, VRF: default
Mac Address: 000a.e43c.a077
Account-Session Id: 0000007b
Nas-Port: Unknown
User name: unknown
Outer VLAN ID: 3127
Subscriber Label: 0x0000007b
Created: Wed Jul 17 15:53:16 2013
State: Connected
Authentication: unauthenticated
Access-interface: Bundle-Ether992.3127
Policy Executed:
policy-map type control subscriber IP_SUB_PMAP
event Session-Start match-first [at Wed Jul 17 15:53:16 2013]
class type control subscriber IP_SUB do-until-failure [Succeeded]
10 activate dynamic-template IPSUB_TEMPLATE [Succeeded]
20 activate dynamic-template HTTP_FORCE_REDIRECT [Succeeded]
30 set-timer AUTH_TIMER 10 [Succeeded]
Session Accounting: disabled
Last COA request received: unavailable
Do you have an idea why I don't get the IP address on my test PC?
And is this config good for force web logon? We want to use it for our WiFi customers.
I hope that you can help me out with this.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Is this because of this?
The IP address is held by the BNG until the client is not authenticated?
https://supportforums.cisco.com/docs/DOC-23170#How_IP_sessions_DHCP_interact_with_AAA
But how can I access the Captive portal without an IP address on my test PC?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
since you dont have authentication in your session start event, this scenario doesnt apply, but yes you can run into it.
the discover is held until the radius ack is seen.
the problem is likely that the subscriber cant be reeiving the ack on the sub if because it has no unnumbered, that is there is no ip enabled on the template for the subscriber.
so you want to make the IPSUB_TEMPLATE unnumbered to the loopback 30.
that will make the routing go fine and the subscriber having the ability to ACK its lease to the dhcp server.
the discover is handled by the terminating access interface, the ack is handled by the subscriber interface.
also you may need to twiddle with the boradcast policy some OS's dont like broadcasted offers, but at this point there is this config thing that might be affecting you.
preventing broadcast offers btw helps in security too so that other stations dont learn the mac/ip combo...
regards
xander
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Awesome!
I added unnumbered under dynamic template and its working fine.
Yesterday, when I was pasting my config I have prepared in notepad I got an error regarding this and I thought that I can not have unnumbered under bundle interface and dynamic template at the same time, and thus I removed it.
Good that I have asked you
How should the force redirect to web logon portal work? I configured a service pmap, applied it to control pmap with seq 20 and thats it. After I do a ipconfig -release and -renwe I get an IP address, open a browser and type an URL but it's not redirecting me to my web portal 10.100.14.108.
The same config is on in the guide I found on Cisco Live.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
awesome, glad to hear it works!
For the HTTPR problem, also check http://www.youtube.com/watch?v=Z_Hw9i_TcGY
I think your class need to be:
class type traffic HTTPRDRT_CM
http-redirect http://10.100.14.108
I think by saying not redirecting meaning it doesn't do anything not even go to the orignal site right?
that is likely caused by the fact that DNS is not permitted in your open garden, so add
ipv4 access-list IPSUB_ACCLIST
20 permit udp any any eq domain
or in your test browser do an http://1.1.1.1 or so, so it does not require a domain lookup.
Also check within the subscriber details that the PBR/HTTPR service is indeed applied successfully to the session.
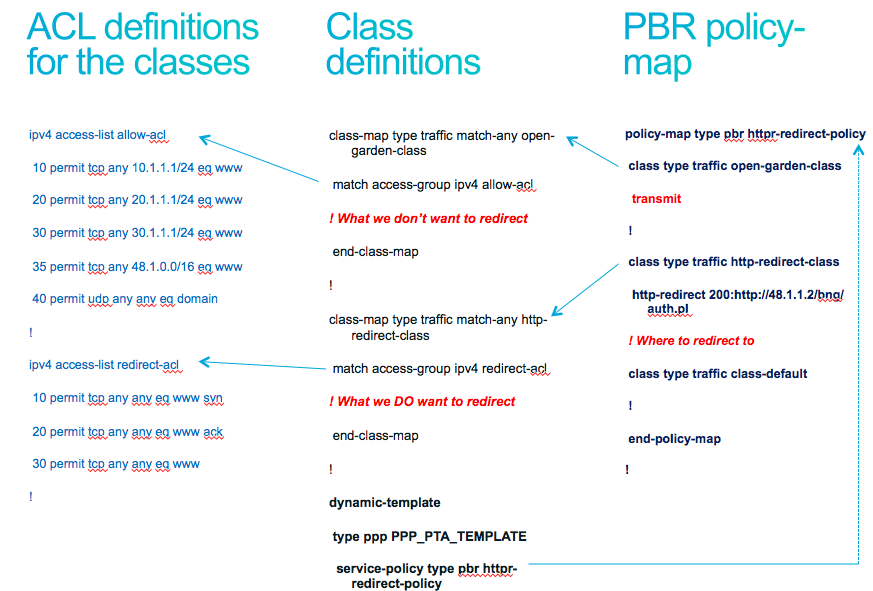
(ps the 200: in front of the http example was a test at teh time of development, use http://x.x.x.x only)
xander
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
You helped me again, http:// was missing, but this was not in the guide I found on Cisco Live.
Thank you very much.
Another question please, I hope that it's not too much.
I have this ACL for the type pbr pmap:
ipv4 access-list IPSUB_ACCLIST
10 permit tcp any host 10.100.14.108 eq www
15 permit icmp any any
30 permit udp any any eq domain
class-map type traffic match-any IPSUB_ACL
match access-group ipv4 IPSUB_ACCLIST
policy-map type pbr HTTP_REDIRECT_PBR
class type traffic IPSUB_ACL
transmit
!
class type traffic HTTPRDRT_CM
http-redirect http://www.bngportal.com
!
class type traffic class-default
drop
!
end-policy-map
Is this enough security? I removed ICMP from the ACL and ICMP was not working anymore.
ACL under dynamic template is not needed, like this example?
dynamic-template
type ipsubscriber IPSUB_TEMPLATE
ipv4 access-group IPSUB_ACCLIST ingress
ipv4 access-group IPSUB_ACCLIST egress
I will now apply additional steps in my subscriber pmap where I will deactivate "HTTP_FORCE_REDIRECT" where the
IPSUB_ACCLIST is used.
It's this one:
policy-map type control subscriber IP_SUB_PMAP
event session-start match-first
class type control subscriber IP_SUB do-until-failure
10 activate dynamic-template IPSUB_TEMPLATE
20 activate dynamic-template HTTP_FORCE_REDIRECT
30 set-timer AUTH_TIMER 10
event account-logon match-first
class type control subscriber IP_SUB do-until-failure
10 authenticate aaa list default
20 deactivate dynamic-template HTTP_FORCE_REDIRECT
event timer-expiry match-first
class type control subscriber AUTH_TIMER_CM do-until-failure
10 disconnect
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
very nice, this is a good day I'll tell the guy who did the preso to update that config example, although I am afraid that the pdf's wont be updated with that info anymore now that CL is over.
when a user has PBR/HTTPR enabled, it is a sort of implicit ACL already. all traffic is trapped by that PBR policy as per configuration. So you dont need the acl at that time, but after the http-r is removed, then it is open garden.
so in that case you may want to hvae a "base" acl or apply a service with an acl if there is something you want to restrict.
whether to allow icmp or not, I am either way about it. it might be good to at least allow icmp to the redirect server and the domain server in case people try to do some troubleshooting on their own.
regards
xander
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Yes, it's a good day
Well, after I have removed the HTTP_FORCE_REDIRECT because in seq 10 the user has been authenticated.
event account-logon match-first
class type control subscriber IP_SUB do-until-failure
10 authenticate aaa list default
20 deactivate dynamic-template HTTP_FORCE_REDIRECT
Because the user is authenticated, he should not have any restrictions.
This scenario is for our WiFi users where we want to use a Captive portal.
How can I authenticate residential users that have moved from PPPoE to DHCP, because there is no way to type an user/pass like its with the PPPoE client (Windows, home router...)?
I know that we can authorize them and compose an username with the MAC address and additionaly circuit-id and remote-id, but I think we will have status "unauthenticated" under "show subscribers session all det".
In summary: New users should have DHCP only and it should be plug&play because we have the MAC address of the CPE and circuit/remote id (option 82). So the username should be MAC+CIRCUITID+REMOTEID in our RADIUS database, and password for all users in the same (e.g. 12345).
This is how I understood the guides I have found. Sorry for my ignorance, still new with BGN stuff
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
correct yeah, when you use the authorize statement, you can compose the username and predefine a password, if that succeeds based on that mac, vlan etc whatever you compose the username with, the "state" is still unauthenticated. This is just a state flag that we move when the user is actually authenticated with his own username and password, either from the line from ppp or as part of an account logon coa event.
you could construct your class for the event to separate the user type (ppp, dhcp) and for instance not check on the auth state for dhcp sessions.
Now the thing is also, I have requested the functionality to "SET" the auth state as part of a control policy action, but that has not yet been honored.
To me that makes the auth flag a bit less useful in a mixed session enviroment exactly as you have.
In other words, in tyour design, I think I would not check the auth state as part of your policy.
Because if the account logon succeeds we know the auth state already anyway.
xander
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: