- Cisco Community
- Technology and Support
- Service Providers
- Service Providers Knowledge Base
- ASR9000/XR: Migrating from IOS to IOS-XR a starting guide
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 02-21-2012 06:29 AM
Introduction
This document tries to assist in an easy and smooth migration from IOS to IOS-XR. Because of the fundamental different nature of the IOS XR operating system and the way things have been implemented specifically by the ASR9000 platform, this article tries to collect a couple of key items to think about and providing some pointers that prevent issues down the road and prepare for proper planning to the great ASR9000.
In this article various topics are separated out per main topic.
- Operating System
- Monolithic for MicroKernel
Understanding the IOS-XR prompt and privilege levels/taskgroups
Memory architecture
- NETIO and "slow switching"
- Using show commands and the location keyword
- RIB, FIB and adjacencies
- Committing configurations and rollback points
- Commit options
- Rollback options
- OSPF
Processes and Using OSPF as a PE-CE protocol
- BGP
- Capability advertisement
- Using neighbor, peer and session groups
- RPL
- RPL and changes to the policy
- InterAS
- L2VPN
- Matching configuration from 7600 to ASR9K for L2 Services:
- Spanning Tree
- SVI and BVI
- EFP
- Converting IOS trunks into XR
- SNMP
This is a "living document", we'll add more and more items as we see questions coming in that have not been covered before, so watch the revision of the document to see if new items have been added. I realize that this document is not complete, but more to be added as we go.
Operating System
Monolithic vs Microkernel
One of the key differences between IOS and IOS-XR is the base operating system. Legacy IOS is known to be a "monolithic" operating system. Effectively it is a run to completion whereby some timesharing is done between processes. This model has proven to be working out very well for over 25 years given the success of Cisco IOS based routers and switches. Also IOS uses a complete shared memory space.
Of course there are also drawbacks which IOS-XR focusses on to address.
One of these enhancements is that XR is running on a microkernel (qnx based) and on top of that we are running the IOS XR processes.
These processes are running similar to a process on a linux based operating system. Effectively the QNX gives us a K-Shell from which we can do similar things as a unix based OS.
When seeing the IOS-XR prompt, if you type "run" it will give you access to the K-Shell. Although it is not supported officially, sometimes it is handy and useful to access the kshell to get hardware level counters or access the file system to copy things around etc.
The flexibility that IOS-XR gives with these processes are:
- ability to restart a process
- ability to patch a process (Via a SMU, the software maintenance update)
- complete control plane and data plane separation (if eg OSPF crashes it doesn't affect the forwarding)
- control plane distribution (some functionality can be offloaded to the linecards like netflow or BFD for scale increase)
Understanding the IOS-XR prompt and privilege levels/taskgroups
IOS has a very simple prompt with a host name followed by a sign that identifies the "mode" that you are in, whether that is privileged exec or regular exec etc.
For instance:
CPE#
or
CPE>
IOS-XR prompt looks like this:
RP/0/RSP0/CPU0:A9K-BNG#
The way to interpret it is as follows:
RP : We are looking at a route processor
0 : Currently we are attached to shelf 0. In the case of multichassis (CRS) or Clustering (ASR9000) we can link multiple chassis together functioning as a single entity, this number identifies which shelf from that same logical node we are looking at.
RSP0: Which RSP we are connecting to. In the case of dual RSP the lower slot ID is RSP0 and the higher slotID is RSP1. Generally you always logon to the active RSP via telnet which can then either be RSP1 or RSP0.
CPU0: today we only have a single (multicore) CPU on the RSP and linecards. This would identify the CPU we are working with in the case that we are adding CPU's on the system.
:hostname : this is the well known part, the hostname.
Note that the suffix of the complete prompt is always with a hash '#' sign. Which suggests that you are in privilige 15 mode.
IOS-XR does NOT have the concept of privilege levels but instead uses task group authorization.
To learn more about using task groups in IOS-XR check you can see in this picture.
Some key differences and highlights between 7600/IOS and ASR9000/XR
Matching configuration from 7600 to ASR9K for L2 Services
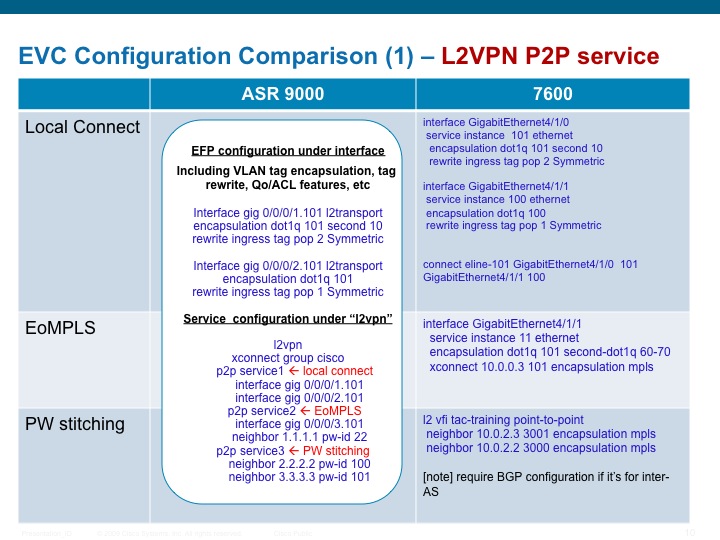
A very comprehensive overview of the EVC model is found on this link.
Spanning Tree
The ASR9000 only supports full MSTP and no other spanning tree protocol.
There is the possibility to use the PVST in PVST-AG mode or Access Gateway.
The "AG" version of the MST or PVST gives you the ability to run these protocols in an P2MP VPLS deployment without the need to run the full protocol set. It basically is designed around the 9K PE's being the root, advertising pre-canned BPDU's and receive the TCN's from the access switches to trigger MAC withdrawl.
More info on VPLS and ASR9000 is here.
Running Spanning Tree (not the AGG) version together with IOS requires you to be aware of the concept of VLAN pruning that IOS does and XR is not aware of.
Migrating spanning tree from 7600 to ASR9000 can be a complex task. IOS switches run STP by default, and you need to disable it explicitly if you don't want to run it. ASR9000 does not run any spanning tree protocol by default and you need to enable it explicitly.
Also the way that BPDU's are handled in XR/ASR9000 is dependant on your configuration.
The following scenarios cover a few of these design migrations you need to be aware of.
This section tries to cover both MSTP and PVST. The key difference for these 2 protocols is that MSTP sends BPDU's untagged and PVST sends tagged BPDU's on the vlans that are PVST enabled.
One of the first decisions you need to make is whether you want the A9K's to be part of the Spanning Tree design or be transparent to them.
There are pros and cons to each option.
In this first picture below shows a design whereby the ASR9000's are NOT part of the spanning tree topology.
If you have defined an untagged EFP like this:
int Gig0/0/0/P.1 l2trans
encap untagged
you will capture the MSTP BPDU's and put them subject to the service that is attached to this untagged EFP.
This can either be a Cross connect (p2p) or a Bridge domain (p2mp). The difference between XCON and BD is that XCON transparently takes whatever comes in on the Attachment Circuit (AC) and send it to the other side (whether that is a phyiscal interface again or a PseudoWire). An Xcon can only have 2 interfaces.
A bridge domain can have multiple EFP's and also employs mac-learning. If the Destination MAC is not know or part of a broadcast/multicast mac address it will get "Flooded" over to all EFP's in the Bridge Domain, except for the originating EFP (split horizon).
Ok so in this design, with that knowledge from above, the BPDU's from switch X are sent via interfaces X and Y to PE1 and PE2.
PE1 would take the BPDU from the untagged EFPand sends them transparently to PE2 over interface M to Switch B's interface U.
In other words Switch A and B see each other as directly connected neighbors. The A9k's are completely transparent and acting as a transparent L2 wire.
This STP design will block one of the 4 (X, Y, U or V) interfaces to break the loop.
Design 1
If you were to have a bridge domain on PE1 and a pseudowire between PE1 and PE4, the BPDU *also* gets sent to PE4 and arriving on interface V.
This model whereby the 9k's are transparent to STP cannot be used with a full mesh of PseudoWires.
This design that you see above is generally seen by "accident" when it is forgotten that the switches run STP by default and the 9k would transparently pass everything on.
"Solutions" are to break to loop manually and using an L2ACL to block the MSTP BPDU's from traversing your 9K's.
In the scenario that you do want the 9k's to participate in spanning tree you basically create to STP "islands" on the left and right side.
The 9k's now terminate the spanning tree coming from the switches. A full PW mesh is possible and this is also one of the designs where the AG version of the STP protocol becomes very useful.
Switch A sees PE1 and PE2 as neighbor.
Design it such that the PE1 and PE2 are root and back up root.
The configuration for this design is to put the interface P into the STP Configuration so that BPDU's are sent and received.
Design 2
The effects of the design scenarios and the relation to the spanning-tree protocol in use are pretty much the same for both MSTP and PVST.
What happens when you follow design 1 or 2 in relation to the EFP configuration associated with it, will be discussed below separated out between the two key STP's.
More detailed configurations and VPLS designs are discussed in this article.
Let us evaluate the various configuration options that you have when defining your EFP's with and without Spanning tree.
MSTP
Scenario 1 in this picture above is the model that you want to use in the design option "2". There is no untagged EFP necessary in this case, and BPDU's received are punted and locally generated BPDU's are injected directly into the port to the switch.
Scenario 2 describes a situation whereby sometimes people want to peel out their untagged traffic and transport it while still running MSTP on the 9k as in design "2". This is problematic today for a few reasons:
1) received BPDU's are subject to the untagged EFP service defintion and will get forwarded. The local MSTP configuration injects BPDU's.
2) this causes the locally connected switch to see BPDU's from the VPLS remote side (switch B) as well as PE1.
3) it will cause MSTi mismatches and unexpected blocked ports.
Scenario 3 can be used for "design option 1". We don't have any local configuration for STP, so we're not injecting anything, we are sending the BPDU's across as per the EFP service definition.
Note:
Scenario 2 is however a design that is recognized as a design we need to support. Starting XR421 scenario 2 will work as follows:
If there is an untagged EFP *and* local STP config on the PE, THEN we will NOT forward the BPDU, but punt them for local STP handling.
We will continue to inject local BPDU's towards the locally connected switch.
In other words if you have untagged traffic that you want to transport but not the BPDU's this will work in XR421. Today, you will get the behavior as described above in scenario 2.
If your intend is to use design option 1, and you want to forward untagged traffic (config scenario 3), but you don't want to forward the BPDU's then you must apply an L2 ACL onto the untagged EFP to block and deny the DMAC used for (MSTP) BPDU's.
The ACL definition is discussed in this article in the related information section.
PVST
The story above doesn't change that much when we are considering PVST.
However there are some minor tweaks caused by the fact that PVST BPDU's are vlan tagged.
Scenario 1 is used in design option "2" whereby you want your A9K's to participate in PVST. Note that we don't do full PVST, but PVST-AG or access gateway, which means that we are sending the bpdu's on the EFP's for the respective vlans and take the BPDU's from these vlans and react on them with mac widthdrawl. The configuration scenario looks like this:
!EFP's
interface g0/0/0/P.10 l2trans
encap dot1q 10
...etc
!service definitions
l2vpn
bridge group VLANS
bridge-domain vlan-10
interface g0/0/0/P.10
bridge-domain vlan-20
interface g0/0/0/P.20
...etc
!spanning-tree config
spanning-tree pvst-ag
interface g0/0/0/P.10
interface g0/0/0/P.20
interface g0/0/0/P.30
HOT HOT HOT HOT
Scenario 2 is a common issue we see happening causing a lot of trouble. This config scenario does NOT have any local PVST configuration, but if the adjacent switches have PVST enabled (and that can be the default!!) then we'd be transparently passing on the vlans as part of the EFP's service definition! The PVST BPDU's are arriving at the remote side and what can be worse is that if we are doing vlan manipulation in terms of tag rewriting with pop or push operations, then the remote side received BPDU's meant to describe vlan 10, but received as VLAN X after the rewrite!
This scenario can be the intended design as described in design option "1" above.
Scenario 3 is a remedy for scenario 2. Basically we are using an L2ACL blocking any bpdu's on the EFP's received so that we are not confusing switches on either end. Alternatively you can also disable STP on the switches connected to the 9k PE's. We are applying L2 ACL's that are blocking a particular DMAC that is used for the PVST bpdu's (see
This issue described here above is something you MUST be aware of.
The ACL definition is discussed in this article in the related information section.
SVI and BVI
The concept between a Switch Virtual Interface and a Bridge Virtual Interface is the same: and L3 endpoint in an L2 environment.
The SVI is a switch concept and the BVI is an L3 concept generally seen on routers.
The BVI interface in IOS-XR/ASR9000 has some restrictions well documented in the CCO documentation for BVI.
Use this reference to setup IRB (Integrated Route Bridging) using the BVI.
EFP
When you set up your Ethernet Flow Point (EFP), especially the untagged one, it can make you run into unexpected scenarios.
For instance, when you have an untagged EFP and you are running full MSTP, the 9K will be able to inject BPDU's to the peer, but the peer's BPDU's are subject to the service of the untagged EFP and may get forwarded. This results in MSTP conflicts on your peer device.
With XR 4.2.1 we'll have the auto ability to peel out the BPDU's from the untagged EFP when MSTP configuration is present.
Also the forwarding of vlan traffic out of an EFP and vlans has a few things that you need to be aware of documented in this article
Converting IOS trunks into XR
Because the IOS-XR EVC model is not aware of trunks like IOS devices are, the conversion from an IOS trunk to an XR EVC based config can be a bit confusing at first. This configuration example documents how to convert an IOS trunk to an XR EVC model:
IOS:
interface TenGigabitEthernet13/3
description my-trunk
switchport
switchport trunk encapsulation dot1q
switchport trunk allowed vlan 4,130,133
switchport mode trunk
no ip address
interface Vlan 4
ip add 10.11.2.1 255.255.255.0
XR:
The translation will be:
interface TenGigabitEthernet 0/0/0/0
description my-trunk-like-xr-interface
Define the EFP's with their respective vlan tags. Because a BVI is used we need to pop the tag so that "inside" the bridge-domain we see untagged packets. On egress, the vlan tag will be slapped on as per EFP definition. Effectively, we create a bridge-domain per vlan.
interface ten0/0/0/0.4 l2transport
encapsulation dot1q 4
rewrite ingress tag pop 1 symmetric
interface ten0/0/0/0.130 l2transport
encapsulation dot1q 130
rewrite ingress tag pop 1 symmetric
int ten0/0/0/0.133 l2transport
encapsulation dot1q 133
rewrite ingress tag pop 1 symmetric
The L2transport command makes these switchports for L2 services
For the switchport trunk allowed vlans, and the interface vlan X, you need to do the following:
First create the bvi interface:
interface BVI4
ipv4 address 10.4.1.10 255.255.0.0
interface BVI130
ipv4 address 10.130.1.1 255.255.0.0
interface BVI133
ipv4 address 10.130.1.1 255.255.0.0
Note that the BVI interface number doesn't necessarily need to be the same as the VLAN identifier, same goes for the subinterface number of the l2transport interface. Though for this example, the practice is followed to make the BVI number, the same as the dot1q TAG value and the same as the EFP subinterface number for clarity.
Then you need to create the bridge group to tide all together.
l2vpn
bridge group MyTrunks
bridge-domain VLAN4
interface ten0/0/0/0.4
routed-interface bvi4
bridge-domain VLAN130
interface ten0/0/0/0.130
routed-interface bvi130
bridge-domain VLAN133
interface ten0/0/0/0.133
interface bvi133
The Bridge group is just a non functional configuration hierarchy to tie several bridge-domains together in part of the same functional group. It functionaly is no different then creating multiple individual groups with their domains, as opposed to one group with multiple domains.
SNMP
Because as you've seen throughout this document XR is heavily distributed, SNMP being a component that requests data from every feature or functioanlity potentially is very heavily relient on IPC's to get its info. Sometimes it feels that show commands or SNMP performs slower in a next generation OS like XR, but this is because of these IPC's.
Also because IOS-XR employs the concept of "SDR" or Secure Domain Routers (CRS specific), some restrictions apply to the way that SNMP operates.
Significant performance options have been put in place. For instance, when you get the stats for an interface, rather then sending an IPC for one interface, we collect a "bulk" of info for the next X interfaces also as you might do a getnext for the next if inline.
Some "standard" data like the Entity info is subject to the load of the MGBL pie that gives access to these MIBS as well as special config is needed to expose this info to the SNMP agent. See here for more detail on that.
Related Information
Xander Thuijs, CCIE #6775
Sr Tech Lead ASR9000
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
PWs are built either statically from one device to the MPLS RID of another device and an assigned PW-ID. This id is unique between the 2 endpoints and must match between the two.
Theoretically we dont care what the AC is on the other side, bundle, subif, main if etc, but when we do protocol conversion like ATM or FR then it is important to understand that we have to IP interworking. The 9K wont support the xlate so that has to be done on the remote PE. FR doesnt have mac addresses, or PPP for that matter neither, so that is where a difficulty comes in when doing protocol conversion. I would try to prevent that as much as possible due to the complexities associated with that.
In terms of the VFI, check this reference:
https://supportforums.cisco.com/docs/DOC-15963
section SPLIT HORIZON
regards
xander
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Xander,
Thanks a lot. I would like to clarify one more thing. Can we apply "eth-cfm" in l2vpn ? Does asr9k support General Switch Management Protocol in vpls ?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Rakesh,
some protocols are dependent on whether they are locally configured, eg BPDU's and CFM.
IF we dont have the service locally configured, they are subject to the EFP defined service.
Some other protocols need to be explicitly configured via L2TP service definitions, eg in the case of LACP.
regards
xander
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Alexander,
Is Multicast Listener Discovery (MLD) used only by ipv6 ? Can I get a confirmation that asr 9k doesn't support mld snooping in vpls(l2vpn) becasue some one told me it doesn't support mld snooping or mld in case of vpls.
I am expecting your response.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Shiras,
MLD snooping is an XR4.3.0 feature.
And correct the MLD is something specific to the ip v6 stack.
MLD is used by IPv6 routers for discovering multicast listeners on a directly attached link, much like
IGMP is used in IPv4. The protocol is embedded in ICMPv6 instead of using a separate protocol.
xander
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Alexander,
But when I read XR 4.3 config document also, they mention IPv6 Multicast Listener Discovery (MLD) snooping is not supported. Will it support under VPLS ?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi,
Thanks for the reply.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Shiras, That is a misnomer in the documentation... MLD snooping is in XR4.3 and snooping applies to the L2VPN configuration.
xander
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Alexander,
Thanks for your information.May I know how to enable Periodic Transmission Timer of MRP(Multiple Registration Protocol) and how to control its periodic time ? is it enabled by default ?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Xander,
May I know how to create Pwseudo wire redundancy in case of vpls in asr 9k. Can I get any documents which includes the commnds of vpls Pws? I am expecting your precious response.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Rakesh:
the concept of a backup neighbor pertains more the vpws service (as it is not a multipoint service). in the case of vpls you just configure multiple neighbors and you want to have them active all and let spanning tree/mac learning figure out where to go.
The questions you ask dont have that much to do with the article at hand here, I would want to recommend raising new questions via the forum so more people are alerted to chime in and allow you to get more inputs in a more timely manner.
The main entry for ASR9000/XR related questions is here:
https://supportforums.cisco.com/community/netpro/service-providers/ios-xr
regards
xander
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Alexander,
May I know , can we configure Anti-Spoofing for VPLS DHCP in our ASR 9 k. Does the router supports anti spoof config or should I purachase any application s/w for achieving that?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
yeah its called dhcp snooping, there are some good guides on that also in the documentation.
regards
xander
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Alexander,
But I asked about anti-spoofing. Please accept my apologies if it is my ignorance.Can we say dhcp anti-spoofing = dhcp snooping ? Please give your confirmation.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
that is what dhcp snooping helps in preventing
you can also leverage features such as DAI (dynamic arp inspection) and IPSG (ip source guard).
In l2 designs these features together make sure that the traffic received on bridge ports conforms with our understanding of the L3 and L2 information from that source.
xander
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: