- Cisco Community
- Technology and Support
- Networking
- Switching
- 8.2 Destination NAT Configuration
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-17-2014 02:04 PM - edited 03-07-2019 06:15 PM
I cannot figure out how to NAT the destination field in the IP Packet. I have tried a few different things.
We have a server that needs to connect over a VPN to an IP that we currently have in-use. I have chosen the 192.168.13.x /24 network to use for NAT on the ASA. (I would advertise the remote server as 192.168.13.10)
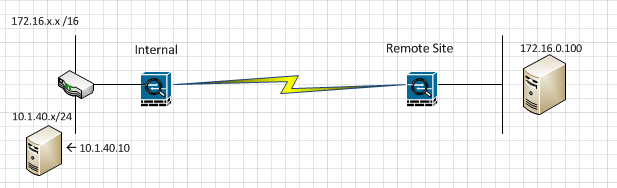
10.1.40.10 needs to connect to 172.16.0.100 over the VPN and retain the source IP but change the destination ip from 192.168.13.10 to 172.16.0.100 once it passes through the ASA.
I figure some kind of policy-NAT that could translate the destination?
This is my guess but I know it is not right... It seems like this would change the source
access-list PNAT ex permit ip host 10.1.40.10 host 192.168.13.10
static (inside,outside) 172.16.0.100 access-list PNAT
Thank You!!
Solved! Go to Solution.
- Labels:
-
Other Switching
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-17-2014 02:29 PM
Jeremy
Do you need policy NAT as the only time you go to that IP is down the VPN ?
Can you try this -
static (outside, inside) 192.168.13.10 172.16.0.100 netmask 255.255.255.255
if you need policy NAT just create an acl for the specific traffic and tie it to the NAT statement.
Jon
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-17-2014 02:29 PM
Jeremy
Do you need policy NAT as the only time you go to that IP is down the VPN ?
Can you try this -
static (outside, inside) 192.168.13.10 172.16.0.100 netmask 255.255.255.255
if you need policy NAT just create an acl for the specific traffic and tie it to the NAT statement.
Jon
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-17-2014 03:11 PM
Hi John,
I thought policy NAT becuse I only wanted to NAT that particulat flow. I didn't want to possibly break other VPN's that use this server, or break its other NAT configurations.
I just GNS3'd this up and I think it worked. I just am not sure how to write the ACL for the policy NAT.
I tried:
access-list PNAT extended permit ip host 172.16.0.100 host 10.1.40.10
static (OUT,IN) 192.168.13.10 access-list PNAT
This didn't work like I was hoping.
I'm not use to seing the outside come first: (outside,inside).
Thank You!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-17-2014 03:24 PM
Jeremy
To be honest i have only ever done this type of NAT from inside to outside so you may have to play around with the acl although i can't say for sure it will work as i have never tested it.
I only asked about whether you needed to use an acl because it is not the source IP you are translating but only the destination IP so the only time you ever go to that address from the inside is via the VPN.
Jon
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-21-2014 03:59 PM
This did seem to work. I couldn't figure out how to add an ACL to make it more of a policy-nat.
I ended up asking the admin on the remote side to configure policy-NAT on his ASA and after he did that I didn't have to worry about doing NAT on my end.
Thanks!!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide