- Cisco Community
- Technology and Support
- Security
- VPN
- ASA DHCP Relay Problem [Configs Posted]
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
ASA DHCP Relay Problem [Configs Posted]
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-27-2011 12:03 PM
Hello,
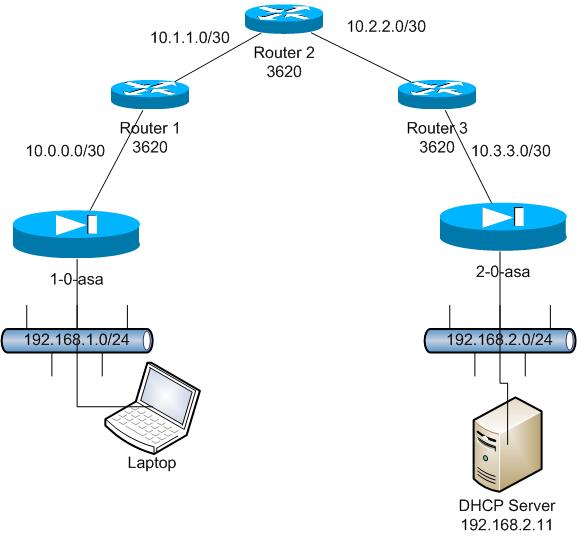
I've setup a lab environment to test a setup we are looking to deploy in the next week or so but am unable to get DHCP relay working. I've referenced the article here: https://supportforums.cisco.com/thread/2104771 but have been unsuccessful in getting this to work. I've attached a diagram outlining the current setup and the configs for each device.
1-0-asa Config:
: Saved
: Written by enable_15 at 21:57:03.799 UTC Mon Sep 26 2011
!
ASA Version 8.3(2)
!
hostname 1-0-asa
domain-name scwr.org
enable password 2KFQnbNIdI.2KYOU encrypted
passwd 2KFQnbNIdI.2KYOU encrypted
names
!
interface Vlan1
nameif inside
security-level 100
ip address 192.168.1.1 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
ip address 10.0.0.2 255.255.255.252
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
ftp mode passive
dns server-group DefaultDNS
domain-name scwr.org
object network NETWORK_OBJ_192.168.1.0_24
subnet 192.168.1.0 255.255.255.0
object network NETWORK_OBJ_192.168.2.0_24
subnet 192.168.2.0 255.255.255.0
object network obj-10.0.0.2
host 10.0.0.2
object network obj-192.168.1.0
subnet 192.168.1.0 255.255.255.0
access-list outside_1_cryptomap extended permit ip 192.168.1.0 255.255.255.0 192.168.2.0 255.255.255.0
access-list outside_1_cryptomap extended permit ip host 10.0.0.2 host 10.3.3.2
access-list outside_1_cryptomap extended permit ip host 192.168.1.1 host 192.168.2.11
pager lines 24
mtu inside 1500
mtu outside 1500
no failover
icmp unreachable rate-limit 1 burst-size 1
asdm image disk0:/asdm-635.bin
no asdm history enable
arp timeout 14400
nat (inside,outside) source static NETWORK_OBJ_192.168.1.0_24 NETWORK_OBJ_192.168.1.0_24 destination static NETWORK_OBJ_192.168.2.0_24 NETWORK_OBJ_192.168.2.0_24
!
object network obj-10.0.0.2
nat (outside,inside) static 192.168.1.6
object network obj-192.168.1.0
nat (outside,inside) static 192.168.1.0
route outside 0.0.0.0 0.0.0.0 10.0.0.1 1
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
dynamic-access-policy-record DfltAccessPolicy
http server enable
http 192.168.1.0 255.255.255.0 inside
http redirect inside 80
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart
crypto ipsec transform-set ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
crypto ipsec security-association lifetime seconds 28800
crypto ipsec security-association lifetime kilobytes 4608000
crypto map outside_map 1 match address outside_1_cryptomap
crypto map outside_map 1 set pfs group5
crypto map outside_map 1 set peer 10.3.3.2
crypto map outside_map 1 set transform-set ESP-AES-256-SHA
crypto map outside_map interface outside
crypto isakmp enable outside
crypto isakmp policy 10
authentication pre-share
encryption aes-256
hash sha
group 5
lifetime 86400
telnet timeout 5
ssh timeout 5
console timeout 0
dhcprelay server 192.168.2.11 outside
dhcprelay enable inside
dhcprelay setroute inside
dhcprelay timeout 60
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
webvpn
tunnel-group 10.3.3.2 type ipsec-l2l
tunnel-group 10.3.3.2 ipsec-attributes
pre-shared-key cisco123
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect ip-options
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect xdmcp
!
service-policy global_policy global
prompt hostname context
call-home
profile CiscoTAC-1
no active
destination address http https://tools.cisco.com/its/service/oddce/services/DDCEService
destination address email callhome@cisco.com
destination transport-method http
subscribe-to-alert-group diagnostic
subscribe-to-alert-group environment
subscribe-to-alert-group inventory periodic monthly
subscribe-to-alert-group configuration periodic monthly
subscribe-to-alert-group telemetry periodic daily
Cryptochecksum:304261141a85c2d11d5b7bd338381cc4
: end
2-0-asa Config:
: Saved
: Written by enable_15 at 22:22:33.209 UTC Mon Sep 26 2011
!
ASA Version 8.3(2)
!
hostname 2-0-asa
domain-name scwr.org
enable password 2KFQnbNIdI.2KYOU encrypted
passwd 2KFQnbNIdI.2KYOU encrypted
names
!
interface Vlan1
nameif inside
security-level 100
ip address 192.168.2.1 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
ip address 10.3.3.2 255.255.255.252
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
ftp mode passive
dns server-group DefaultDNS
domain-name scwr.org
object network NETWORK_OBJ_192.168.1.0_24
subnet 192.168.1.0 255.255.255.0
object network NETWORK_OBJ_192.168.2.0_24
subnet 192.168.2.0 255.255.255.0
object network obj-10.0.0.2
host 10.0.0.2
object network obj-192.168.1.0
subnet 192.168.1.0 255.255.255.0
access-list outside_1_cryptomap extended permit ip 192.168.2.0 255.255.255.0 192.168.1.0 255.255.255.0
access-list outside_1_cryptomap extended permit ip host 192.168.2.11 host 10.0.0.2
access-list outside_1_cryptomap extended permit ip host 192.168.2.11 host 192.168.1.1
pager lines 24
mtu inside 1500
mtu outside 1500
no failover
icmp unreachable rate-limit 1 burst-size 1
asdm image disk0:/asdm-635.bin
no asdm history enable
arp timeout 14400
nat (inside,outside) source static NETWORK_OBJ_192.168.2.0_24 NETWORK_OBJ_192.168.2.0_24 destination static NETWORK_OBJ_192.168.1.0_24 NETWORK_OBJ_192.168.1.0_24
route outside 0.0.0.0 0.0.0.0 10.3.3.1 1
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
dynamic-access-policy-record DfltAccessPolicy
http server enable
http 192.168.2.0 255.255.255.0 inside
http authentication-certificate inside
http redirect inside 80
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart
crypto ipsec transform-set ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
crypto ipsec security-association lifetime seconds 28800
crypto ipsec security-association lifetime kilobytes 4608000
crypto map outside_map 1 match address outside_1_cryptomap
crypto map outside_map 1 set pfs group5
crypto map outside_map 1 set peer 10.0.0.2
crypto map outside_map 1 set transform-set ESP-AES-256-SHA
crypto map outside_map interface outside
crypto isakmp enable outside
crypto isakmp policy 10
authentication pre-share
encryption aes-256
hash sha
group 5
lifetime 86400
telnet timeout 5
ssh timeout 5
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
webvpn
tunnel-group 10.0.0.2 type ipsec-l2l
tunnel-group 10.0.0.2 ipsec-attributes
pre-shared-key cisco123
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect ip-options
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect xdmcp
!
service-policy global_policy global
prompt hostname context
call-home
profile CiscoTAC-1
no active
destination address http https://tools.cisco.com/its/service/oddce/services/DDCEService
destination address email callhome@cisco.com
destination transport-method http
subscribe-to-alert-group diagnostic
subscribe-to-alert-group environment
subscribe-to-alert-group inventory periodic monthly
subscribe-to-alert-group configuration periodic monthly
subscribe-to-alert-group telemetry periodic daily
Cryptochecksum:ecda5162ededc8b3ee469fa0328f5e53
: end
Any help is greatly appreciated.
- Labels:
-
VPN
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide