- Cisco Community
- Technology and Support
- Security
- VPN
- Anyconnect is SSL VPN (tcp
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
AnyConnect cannot verify the VPN server
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-26-2015 04:22 PM - edited 02-21-2020 08:31 PM
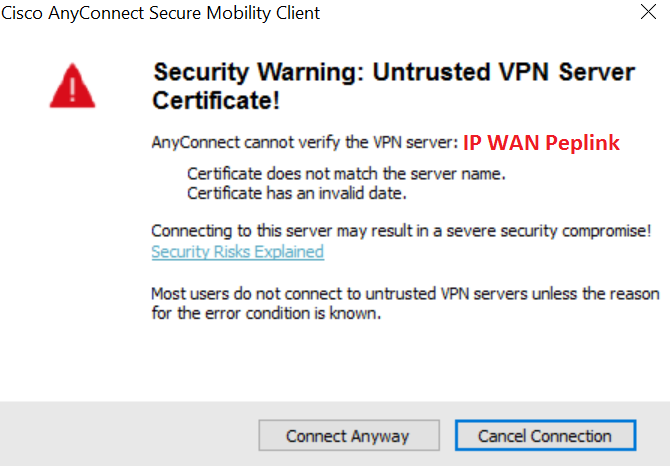
I'm failing when connecting via AnyConnect (error attached). This started happening after a code upgrade from 7.x to 8.2(5)55 on the ASA 5505. The output on the ASA is below:
Oct 26 2015 19:14:01: %ASA-6-725001: Starting SSL handshake with client comcast:1.1.1.156/58629 for TLSv1 session.
Oct 26 2015 19:14:01: %ASA-7-725010: Device supports the following 4 cipher(s).
Oct 26 2015 19:14:01: %ASA-7-725011: Cipher[1] : RC4-SHA
Oct 26 2015 19:14:01: %ASA-7-725011: Cipher[2] : AES128-SHA
Oct 26 2015 19:14:01: %ASA-7-725011: Cipher[3] : AES256-SHA
Oct 26 2015 19:14:01: %ASA-7-725011: Cipher[4] : DES-CBC3-SHA
Oct 26 2015 19:14:01: %ASA-7-725008: SSL client comcast:1.1.1.156/58629 proposes the following 6 cipher(s).
Oct 26 2015 19:14:01: %ASA-7-725011: Cipher[1] : AES256-SHA
Oct 26 2015 19:14:01: %ASA-7-725011: Cipher[2] : AES128-SHA
Oct 26 2015 19:14:01: %ASA-7-725011: Cipher[3] : DHE-DSS-AES256-SHA
Oct 26 2015 19:14:01: %ASA-7-725011: Cipher[4] : DHE-DSS-AES128-SHA
Oct 26 2015 19:14:01: %ASA-7-725011: Cipher[5] : DES-CBC3-SHA
Oct 26 2015 19:14:01: %ASA-7-725011: Cipher[6] : EDH-DSS-DES-CBC3-SHA
Oct 26 2015 19:14:01: %ASA-7-725012: Device chooses cipher : AES128-SHA for the SSL session with client comcast:1.1.1.156/58629
Oct 26 2015 19:14:01: %ASA-6-725002: Device completed SSL handshake with client comcast:1.1.1.156/58629
Oct 26 2015 19:14:01: %ASA-6-725007: SSL session with client comcast:1.1.1.156/58629 terminated.
Do I need to do something with the cert?
- Labels:
-
AnyConnect
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-26-2015 06:35 PM
As you were upgrading the version of code that runs on the ASA did you also upgrade the version of AnyConnect that you are using? This would seem to be more a behavior of the AnyConnect client than of the ASA itself.
We do not have enough information about the situation to be sure. But the logical guess is that the ASA has a self signed certificate. And with a self signed certificate if AnyConnect is configured to use strict verification of the server (which is the default) then you get an error like this one.
One option (and it would be the optimum choice) would be to install a public cert on the ASA. The other option would be to go into the AnyConnect options and to disable strict checking of the server.
HTH
Rick
Rick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-29-2015 12:42 PM
I have a certificate from Godaddy. I had to import the certificate on my iphone on the cisco anyconnect app and the error no longer shows
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-29-2015 12:58 PM
Thanks for posting back to the forum to let us know that you were able to solve the problem by importing the public cert on your iphone. That is good to know.
HTH
Rick
Rick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-29-2015 11:49 AM
Where you able to get this resolved?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-29-2015 12:40 PM
As I explained the most common cause of this issue is that the ASA is using a self signed cert. The default behavior in AnyConnect (in recent versions) is to do strict server checking and to not connect if the server is using a self signed cert. The original poster did not clarify whether he is using a self signed cert or not, but the best guess is that he was. Are you experiencing this symptom? And if so, are you using a self signed cert?
There are at least two options which should provide a solution here. The optimum solution is to obtain and install a public cert in place of the self signed cert. The other alternative is to use the option given in the error message to change the behavior of AnyConnect to not do strict server checking. This should allow connection to a server using a self signed cert.
Interestingly I recently encountered a situation where the option to change the setting does not work. This is for a customer whose ASA is running 9.5 and AnyConnect 4.2. The option to change the setting does not work. I have opened a case with Cisco TAC and that case is active at this point. It seems that the issue may relate to something in the interaction with IE as the browser. When we used Firefox as the browser to access the ASA and request AnyConnect we were able to change the option.
HTH
Rick
Rick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-07-2017 02:15 AM
Hi Rick,
Can you help me? Recently, my system include 1 ASA5516x which is connected to Peplink through outside interface. PepLink has responsibility for WAN, NAT, load-sharing. I have a task to configure Anyconnect IPsec VPN. I configure NAT port UDP 4500, UDP 500 on Peplink to IP outside of ASA, generate self-cert on ASA. But, VPN connection has failed, you can see log as followed:
[07-Jun-17 3:41:58 PM] Connection attempt has failed.
[07-Jun-17 3:41:59 PM] No valid certificates available for authentication.
[07-Jun-17 3:41:59 PM] Connection attempt has failed
Thanks Rick,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-07-2017 03:18 AM
Anyconnect is SSL VPN (tcp/443 by default), not IPsec (udp/4500 and udp/500).
It can be seup as IKEv2 IPsec but that is very uncommon.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide

