- Cisco Community
- Technology and Support
- Security
- VPN
- Re: AnyConnect - split tunnel configuration not working - 5508-X
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
AnyConnect - split tunnel configuration not working - 5508-X
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-09-2020 07:00 AM
Hi,
I have been working on setting up VPN split tunnel with AnyConnect but cannot get it working. I want to allow users to print locally so wanted to exclude printing related traffic from the tunnel by creating an ACL and using "excludespecified" option.
access-list AnyConnect_Client_Local_Print extended deny ip any4 any4 access-list AnyConnect_Client_Local_Print extended permit tcp any4 any4 eq lpd access-list AnyConnect_Client_Local_Print remark IPP: Internet Printing Protocol access-list AnyConnect_Client_Local_Print extended permit tcp any4 any4 eq 631 access-list AnyConnect_Client_Local_Print remark Windows' printing port access-list AnyConnect_Client_Local_Print extended permit tcp any4 any4 eq 9100 access-list AnyConnect_Client_Local_Print remark mDNS: multicast DNS protocol access-list AnyConnect_Client_Local_Print extended permit udp any4 host 224.0.0.251 eq 5353 access-list AnyConnect_Client_Local_Print remark LLMNR: Link Local Multicast Name Resolution protocol access-list AnyConnect_Client_Local_Print extended permit udp any4 host 224.0.0.252 eq 5355 access-list AnyConnect_Client_Local_Print remark TCP/NetBIOS protocol access-list AnyConnect_Client_Local_Print extended permit tcp any4 any4 eq 137 access-list AnyConnect_Client_Local_Print extended permit udp any4 any4 eq netbios-ns group-policy SSLVPNAccess internal group-policy SSLVPNAccess attributes vpn-idle-timeout 86400 vpn-session-timeout 86400 vpn-tunnel-protocol ssl-client ssl-clientless split-tunnel-policy excludespecified split-tunnel-network-list value AnyConnect_Client_Local_Print webvpn anyconnect mtu 1300 anyconnect ssl keepalive 20 anyconnect profiles value default type user anyconnect ask enable default anyconnect tunnel-group SSLVPNAccess type remote-access tunnel-group SSLVPNAccess general-attributes address-pool SSLVPNAccess authentication-server-group RADIUS LOCAL default-group-policy SSLVPNAccess tunnel-group SSLVPNAccess webvpn-attributes group-alias SSLVPNAccess enable
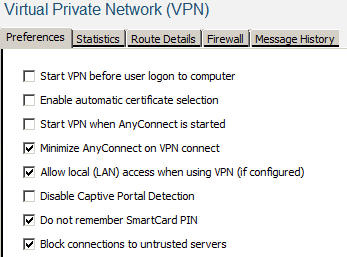
I also added AnyConnect profile that allows local LAN access and enabled it on the client side as well.
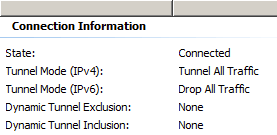
But despite that AnyConnect shows "tunnel all traffic" on the statistics tab and printing does not work obviously.
Any comments will be appreciated.
Thanks!
- Labels:
-
AnyConnect
-
VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-09-2020 09:17 AM
Hi,
Split-tunneling policy (ACL) needs to have IP statements, not TCP/UDP statements (because you can only have network routes, not TCP routes), and permit statements. If you want to allow users access to local lan, you would need your split-tunnelling ACL to have a single permit entry on "0.0.0.0/32". Find a configuration example here.
Regards,
Cristian Matei.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-09-2020 11:14 AM - edited 04-09-2020 11:14 AM
Hi Christian,
That is the guide I was following and before trying extended ACL I tried the standard one with "permit any4" as mentioned in the guide but the result was the same. Now I reverted the configuration back to the below but no luck.
access-list local_LAN standard permit any4 group-policy SSLVPNAccess attributes dns-server value 192.168.7.3 192.168.7.4 vpn-idle-timeout 86400 vpn-session-timeout 86400 vpn-tunnel-protocol ssl-client ssl-clientless split-tunnel-policy excludespecified split-tunnel-network-list value local_LAN
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide