- Cisco Community
- Technology and Support
- Security
- VPN
- Re: Cisco FTD 1120 using FDM- HA IPSEC VPN using two separate ISPs
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-11-2022 08:07 AM
Good day,
Running FTD code 6.7.0.2-24 on two FTD 1120s in HA (active/standby).
Potential design is to have a primary IPsec tunnel connect from the FTDs to multiple sites.
The secondary link is there as a backup connection in the event of failure of the primary.
If the primary ISP does go down, then VPNs come up on the secondary ISP connection.
When trying to configure the VPN using the secondary ISP, the FTD gives an error indicating that duplicate remote peer ip address is found, the remote peer has to be unique for the VPN configuration.
Is there a way to do the HA configuration or this a limitation of the FTD FDM setup?
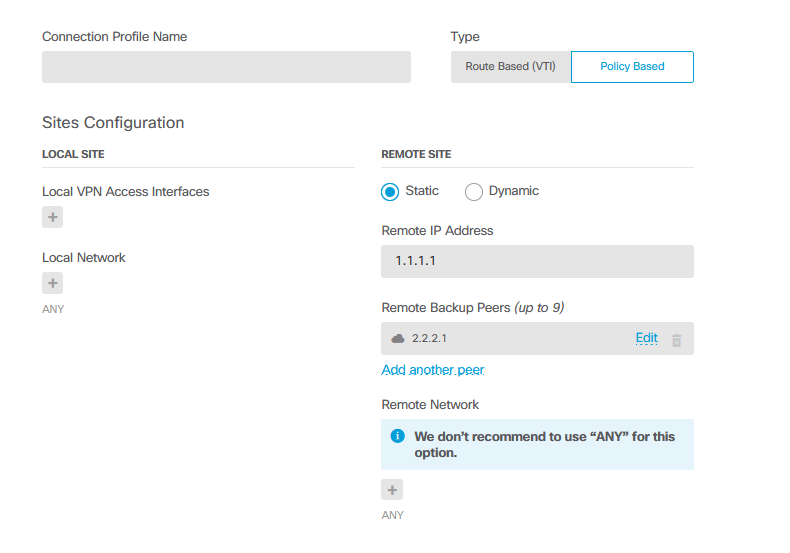
I also know that backup peers can be configured using the API explorer but this is only if the remote side has 2 remote IP addresses to connect, correct?
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-11-2022 10:56 AM
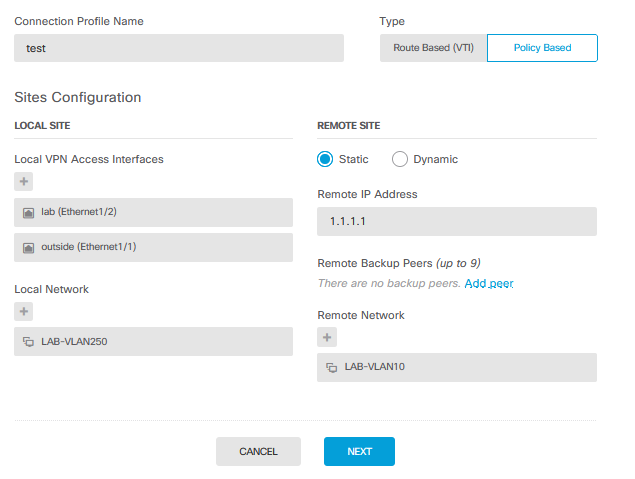
@Davion Stewart you can add multiple local VPN access interfaces (outside interfaces) without having to define a backup peer.
If you define multiple local VPN access interfaces and a backup peer, you'd should be able to establish a VPN from both your outside interfaces (assuming route failover is configured) to both the primary and backup peer IP addresses.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-11-2022 09:16 AM
@Davion Stewart when you create the connection profile, you can select multiple interfaces (you can on 7.1 anyway). This will enable crypto on both outside interfaces, you would need to use IP SLA and tracking to failover to the second ISP upon failure of the first.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-11-2022 10:44 AM
Thanks Rob, didn't recognize that version 7.1 allowed you to configure that.
Based on the Configuration guide, is it that when you add a remote backup peer, the configuration then allows you add another local VPN access interface in the event the backup peer is reachable through a different interface or can you add another local VPN access interface without adding a backup peer?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-11-2022 10:56 AM
@Davion Stewart you can add multiple local VPN access interfaces (outside interfaces) without having to define a backup peer.
If you define multiple local VPN access interfaces and a backup peer, you'd should be able to establish a VPN from both your outside interfaces (assuming route failover is configured) to both the primary and backup peer IP addresses.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-11-2022 11:13 AM
Ahh beautiful, @Rob Ingram exactly what I wanted to see. I was going to ask for a screenshot in my last reply but i said lemme wait.
Thanks for the confirmation of how it works.
One more thing concerning the last part of your statement. With two outside interfaces and two backup peers configured, VPNs can be formed over both in what ways? The scenarios assume that both sides have two outside interfaces.
There is:
local primary to remote primary
local primary to remote secondary (backup peer)
local secondary to remote primary
local secondary to remote secondary (backup peer)
Yes, I understand that route failover via IP SLA will need to be configured. Also, I suppose DPD will need to be configured properly on both sides so that the initial VPN can be torn down.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-11-2022 11:28 AM - edited 03-11-2022 11:35 AM
@Davion Stewart the scenario doesn't necessarily assume the remote peer has 2 outside interfaces, the backup peer could be another VPN device.
All traffic from the local FTD would be routed via ISP1 to remote primary until remote primary failure, then failover to remote backup peer. If local FTD ISP1 fails, SLA/tracking changes default routing via ISP2, VPN is established to remote peer, if remote peer failure failover to remote backup peer.
DPD is enabled by default on FDM, no way to change it for a L2L VPN.
tunnel-group 1.1.1.1 ipsec-attributes
no ikev1 pre-shared-key
peer-id-validate req
no chain
no ikev1 trust-point
isakmp keepalive threshold 10 retry 2
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-11-2022 12:54 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-18-2022 08:15 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-18-2022 09:05 AM - edited 08-18-2022 09:06 AM
@engineer467 a backup VPN peer is avaiable to be configured in the GUI from FDM 7.1. https://www.cisco.com/c/en/us/td/docs/security/firepower/710/relnotes/firepower-release-notes-710/features.html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-18-2022 09:17 AM
Wished there was a way to do it in 7.0.1.
Anyways, thanks always, Rob.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-11-2023 12:03 AM
Here is the link to the Cisco bug document that mentions to be able to create a backup tunnel leaving through a backup VPN interface on FDM (not managed by FMC), the minimum release that supports this feature is 7.1.0.
https://bst.cloudapps.cisco.com/bugsearch/bug/CSCvt06355
HTH!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide