- Cisco Community
- Technology and Support
- Security
- VPN
- Re: Configure WRVS4400N VPN Client Account to connect my computer via VPN to my home internal subnet
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Configure WRVS4400N VPN Client Account to connect my computer via VPN to my home internal subnet
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-29-2018 03:18 PM - edited 03-12-2019 05:25 AM
I know that this has been beat to death but none the posts I have found via Google have fixed my problem.
First let me explain what my goal here is. I want to connect my computer to my home network when I am on the road, I do not want a VPN that connects directly to a computer or other device. I want to have access to my home internal subnet so I can connect via IP to any of the devices.
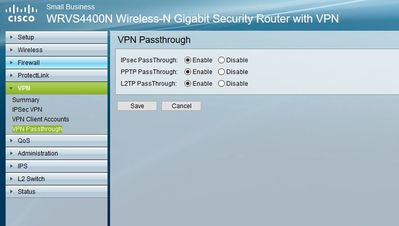
Here are the steps I went through to setup a VPN connection to my WRVS4400N VPN router.
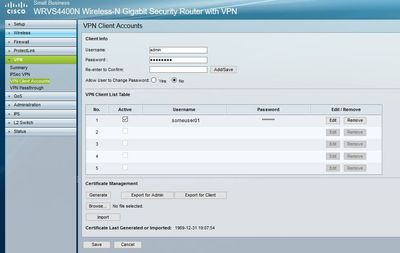
I built a VPN user under the VPN | VPN Client Account and saved the account.
Next I generated both the Admin and Client Certificates and downloaded both to my local computer.
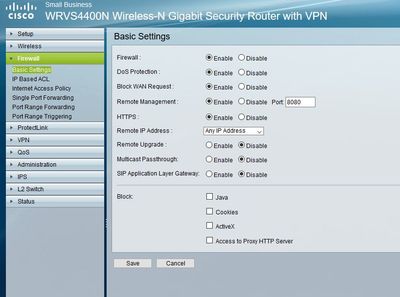
Next I enabled Firewall / Basic Settings / Remote Management. This enabled HTTPS and set Remote IP Address to Any IP address. I saved the settings.
Next I downloaded the QuickVPN Client and placed the client certificate I downloaded from the WRVS4400N into the QuickVPN install directory.
Next I setup the QuickVPN Client to connect to my public cable modem IP address.
Next I setup a connection to the internet using a NATted outside public IP address from another provider and tested the VPN connection. It failed!
Now when I try to connect to the VPN via the QuickVPN Client I get the following in my QuickVPN Client Log.txt file.
[WARNING]Failed to ping remote VPN Router!
Note: I have masked my public IP address with 7x.1xx.4x.5x.
--------------------------Begin Log.txt--------------------------
2018/06/29 10:35:45 [STATUS]OS Version: Unknown
2018/06/29 10:35:45 [STATUS]One network interface detected with IP address 172.20.10.6
2018/06/29 10:35:45 [STATUS]Connecting...
2018/06/29 10:35:45 [DEBUG]Input VPN Server Address = 7x.1xx.4x.5x
2018/06/29 10:35:45 [STATUS]Connecting to remote gateway with IP address: 7x.1xx.4x.5x
2018/06/29 10:35:48 [STATUS]Remote gateway was reached by https ...
2018/06/29 10:35:48 [STATUS]Provisioning...
2018/06/29 10:35:51 [STATUS]Success to connect.
2018/06/29 10:35:51 [STATUS]Tunnel is configured. Ping test is about to start.
2018/06/29 10:35:51 [STATUS]Verifying Network...
2018/06/29 10:35:57 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:36:00 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:36:03 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:36:06 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:36:09 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:36:13 [WARNING]Ping was blocked, which can be caused by an unexpected disconnect.
2018/06/29 10:36:15 [STATUS]Disconnecting...
2018/06/29 10:36:21 [STATUS]Success to disconnect.
2018/06/29 10:37:45 [STATUS]OS Version: Unknown
2018/06/29 10:37:45 [STATUS]One network interface detected with IP address 172.20.10.6
2018/06/29 10:37:45 [STATUS]Connecting...
2018/06/29 10:37:45 [DEBUG]Input VPN Server Address = 7x.1xx.4x.5x
2018/06/29 10:37:45 [STATUS]Connecting to remote gateway with IP address: 7x.1xx.4x.5x
2018/06/29 10:37:49 [STATUS]Remote gateway was reached by https ...
2018/06/29 10:37:49 [STATUS]Provisioning...
2018/06/29 10:37:52 [STATUS]Success to connect.
2018/06/29 10:37:52 [STATUS]Tunnel is configured. Ping test is about to start.
2018/06/29 10:37:52 [STATUS]Verifying Network...
2018/06/29 10:37:58 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:38:01 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:38:04 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:38:07 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:38:10 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:38:14 [WARNING]Ping was blocked, which can be caused by an unexpected disconnect.
2018/06/29 10:38:16 [STATUS]Disconnecting...
2018/06/29 10:38:22 [STATUS]Success to disconnect.
2018/06/29 10:49:59 [STATUS]OS Version: Unknown
2018/06/29 10:49:59 [STATUS]One network interface detected with IP address 172.20.10.6
2018/06/29 10:49:59 [STATUS]Connecting...
2018/06/29 10:49:59 [DEBUG]Input VPN Server Address = 7x.1xx.4x.5x
2018/06/29 10:49:59 [STATUS]Connecting to remote gateway with IP address: 7x.1xx.4x.5x
2018/06/29 10:50:03 [STATUS]Remote gateway was reached by https ...
2018/06/29 10:50:03 [STATUS]Provisioning...
2018/06/29 10:50:07 [STATUS]Success to connect.
2018/06/29 10:50:07 [STATUS]Tunnel is configured. Ping test is about to start.
2018/06/29 10:50:07 [STATUS]Verifying Network...
2018/06/29 10:50:12 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:50:15 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:50:18 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:50:21 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:50:24 [WARNING]Failed to ping remote VPN Router!
2018/06/29 10:50:28 [WARNING]Ping was blocked, which can be caused by an unexpected disconnect.
2018/06/29 10:50:29 [STATUS]Disconnecting...
2018/06/29 10:50:32 [WARNING]Failed to disconnect.
--------------------------End Log.txt--------------------------
Any and all help will be greatly appreciated.
Also I tried to open a support ticket and support said since it is End Of Support they can't help me. They suggested buying a new VPN router so I can open a warranty support ticket. This is too good of a router to just replace because I am having a difficult time setting up a VPN connection.
Thank you,
ChanceDawgMiner
- Labels:
-
Other VPN Topics
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-30-2018 02:51 PM
Hello,
is this your setup:
Local LAN --> WRVS4400N (in routed mode) - Cable Modem --> Internet
?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-30-2018 03:42 PM
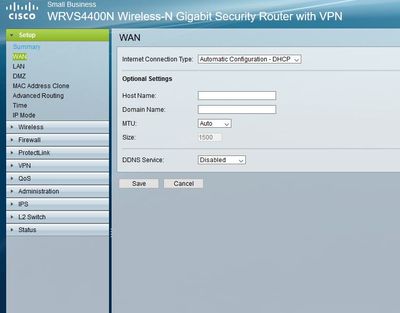
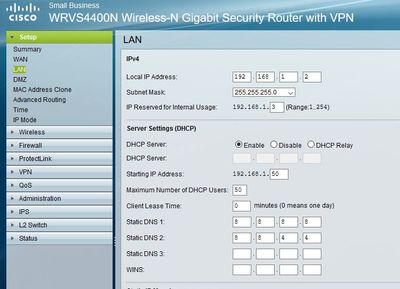
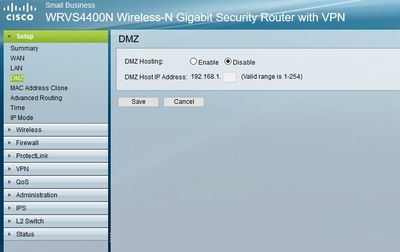
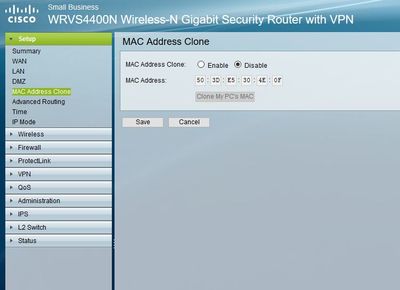
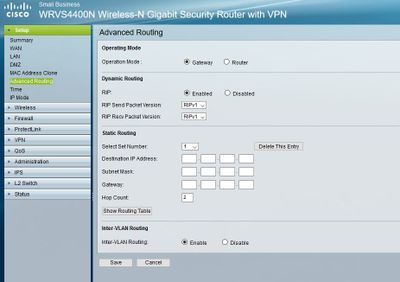
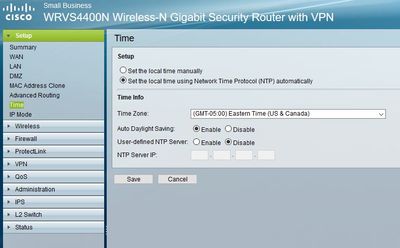
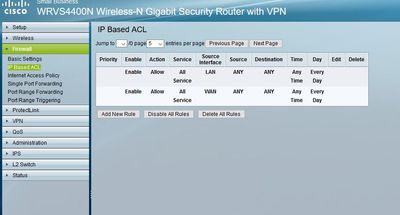
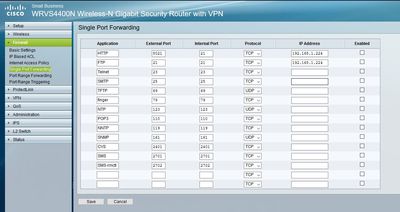
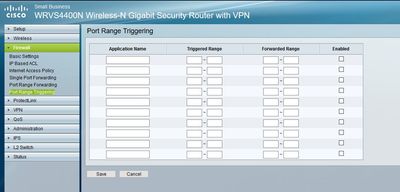
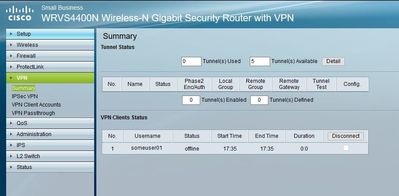
To make this a little easier I am going take screenshots of the router config pages and upload them later this evening when I am back home. I believe that will be the best way for you to see all of the settings.
I will redact/mask personal info such as public IP addresses and username other than default usernames.
Talk at you later this evening.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-30-2018 04:51 PM
I was able to get the screenshots done earlier than I expected.
I hope these help find out what I messed up.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-01-2018 12:52 AM
Hello,
sorry for the delay, I am on GMT +1...
What is the local LAN IP address of the machine you are connecting from ? Your WRVS4400N has 192.168.1.0/24 configured, make sure the remote PC you are trying to connect from doesn't have an IP address in that same range.
The screenshots showing your setup look fine, I can't see anything wrong.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-01-2018 11:25 AM - edited 07-01-2018 01:28 PM
It is 172.20.10.6
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-01-2018 02:00 PM
Hello,
have you tried to use another client, such as the Cisco VPN Client (link attached, scrool down to the '
CISCO VPN CLIENT 64BIT VERSION')...
http://www.firewall.cx/downloads/cisco-tools-a-applications.html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-01-2018 02:08 PM
Or use the Windows 10 built-in VPN client...
https://support.microsoft.com/en-us/help/20510/windows-10-connect-to-vpn
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-01-2018 03:51 PM
I tried the Window 10 built in VPN client and I also tried the "Cisco AnyConnect Secure Mobility Client" Version 4.3.01095 and both failed.
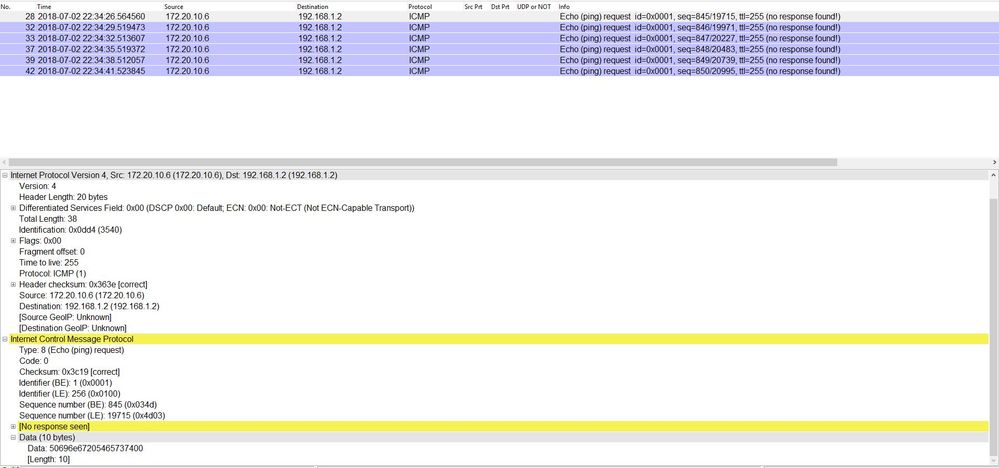
For a couple of tests I setup "L2 Switch | Port Mirroring" to mirror the Outside WAN port to another computer and did a packet capture via Wireshark while also doing a packet capture via Wireshark on my client computer while trying to connect via the QuickVPN Client.
From the packet captures I see the PING 192.168.1.2 being sent out from my client computer. And from the WAN port mirror packet capture I see everything from the remote client coming into the router except the PING 192.168.1.2.
Doesn't that lead to the conclusion that the PING is not reaching the router? Since the PING is sent from the client computer un-encrypted it makes sense that a plain ping packet from my client computer on the public internet could not reach the IP address 192.168.1.2 since it is a non-public route-able IP address. Shouldn't the PING packet be encrypted and sent through a tunnel to the router or should it be a public IP address like the router's public IP address?
ChanceDawgMiner
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-01-2018 11:00 PM
Hello,
you are right, the PING should go through the VPN tunnel...
I have read through the entire post again - can you check if Windows Defender actually allows IPSec through ?
How to Setup Windows 10 Firewall for L2TP/IPSec
https://www.magnumvpn.com/setup-windows-10-firewall-l2tp.html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-02-2018 10:28 AM - edited 07-02-2018 10:33 AM
Windows 10 Defender is disabled, Kaspersky is the firewall not Defender.
Is there a test or something else I can do to verify that IPSec is working?
As an FYI I have a VPN connection to my company's internal network that I use the "Cisco AnyConnect Secure Mobility Client" to connect to and it works 100%. Would this prove that IPSec is working?
I do not have the company VPN connection running while I am testing the QuickVPN Client connection to my WRVS4400N router.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-02-2018 10:35 AM
According to the QuickVPN guidelines the Windows Firewall has to be enabled, and any third party firewall/virus scanner software has to be disabled.
Try and create the IPSec rule in Defender and disable Kaspersky...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-02-2018 11:05 AM
Unfortunately I can't enable Windows Defender until I uninstall Kaspersky.
I'll uninstall Kaspersky long enough to test the QuickVPN with Windows Defender Firewall enabled after which I will have to reinstall Kaspersky.
Not sure when I will be able to do this, it may be tonight or a day or two. I have other work things to do that I have to complete before I can take the time to do the uninstall | test | reinstall.
I'll update as soon as I can get it done.
Thank you,
ChanceDawgMiner
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-02-2018 12:38 PM
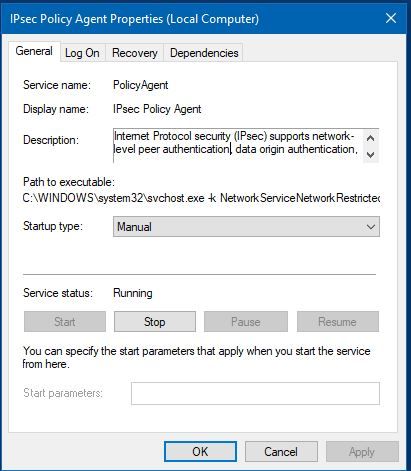
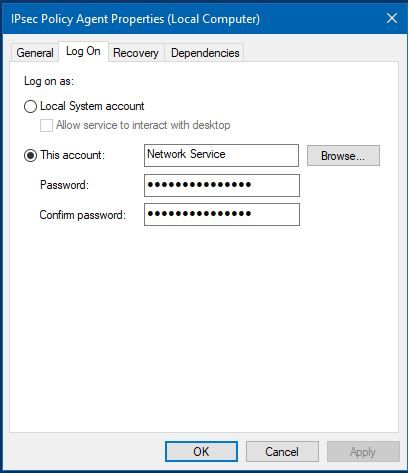
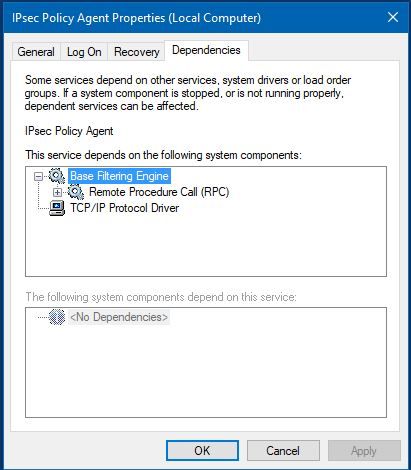
As an FYI I found that the "IPSec Policy Agent" is running screenshots below.
Does that prove IPSec is working?
Here is the description of the service.
-----------------
Internet Protocol security (IPsec) supports network-level peer authentication, data origin authentication, data integrity, data confidentiality (encryption), and replay protection. This service enforces IPsec policies created through the IP Security Policies snap-in or the command-line tool "netsh ipsec". If you stop this service, you may experience network connectivity issues if your policy requires that connections use IPsec. Also,remote management of Windows Defender Firewall is not available when this service is stopped.
-----------------
Am I wrong in thinking that IPSec is working with Kaspersky Firewall enabled and Windows Defender Firewall disabled?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-02-2018 07:46 PM - edited 07-02-2018 07:47 PM
Okay I uninstalled Kaspersky then rebooted. Made sure that Windows Defender Firewall was on and created the inbound rule for UDP ports 50, 500, and 4500. Ran another test of the QuickVPN Client connection and it failed with the exact error as before.
--------------------------------------
2018/07/02 22:34:41 [WARNING]Failed to ping remote VPN Router!
2018/07/02 22:35:03 [WARNING]Ping was blocked, which can be caused by an unexpected disconnect.
--------------------------------------
Ran the test again with port rule set for both inbound and outbound and it failed also.
I did a packet capture and the client is still trying to ping 192.168.1.2 as shown in the screen grab below.
There has to be a setting wrong that is causing the client to ping the 192.168.1.2 before the tunnel is up.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-03-2018 11:17 AM
I was able to make the ping work for testing purposes only.
I edited the vpnserver.conf file and changed "remotelanip=192.168.1.2" to "remotelanip=7x.1xx.4x.5x" then made vpnserver.conf file Read-Only then tested.
With 7x.1xx.4x.5x as the remotelanip the ping worked and the client connected to the router. This doesn't work for setting up the connection to my internal IP subnet but it proves that ping from the remote client to the router does work so the problem has got to be a client or router config issue.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide