- Cisco Community
- Technology and Support
- Security
- VPN
- IKEv2 on ASAv in Azure
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-01-2020 02:08 PM
I've deployed an ASAv (without a license yet) in my virtual network at Azure in order to test it to see if it will function how I expect it to when connecting IPsec VPNs (Azure tunnels don't support enough features).
I was able to bring up an IKEv1 tunnel just fine, and pass traffic from my virtual network at Azure to an ASA onsite.
However, when I try to do IKEv2 an NAT the traffic on the Azure side I can't even get the tunnel to negotiate phase 1. I see nothing in the debug for IKEv2 HA. I do see that the ASAv is NATing the traffic as it should.
Is this a limitation due to not having a license on the ASAv, or am I doing something else wrong?
Please see attached configuration for the ASAv
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2020 08:36 PM
I figured out my issue after looking at debugs on the onsite ASA. It was a configuration issue on that ASA. I needed to tell my tunnel-group on the ASA onsite to use ikev2 with a policy. I'm guessing this is required in software release 9.1 because the ASAv didn't need the policy and it is running 9.14
group-policy GroupPolicy_x.x.x.x internal
group-policy GroupPolicy_x.x.x.x attributes
vpn-tunnel-protocol ikev2
!
tunnel-group x.x.x.x type ipsec-l2l
tunnel-group x.x.x.x general-attributes
default-group-policy GroupPolicy_x.x.x.x
tunnel-group x.x.x.x ipsec-attributes
ikev2 remote-authentication pre-shared-key *****
ikev2 local-authentication pre-shared-key *****
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-01-2020 08:25 PM
Hi dcusher2006,
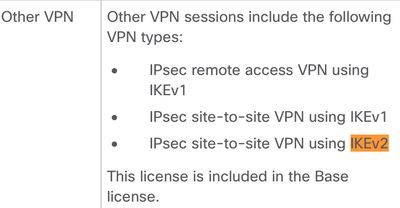
No other license should be required besides the base license.
What is the output of a packet tracer on the ASA?
Rate if it helps.
Regards,
Josue Brenes
TAC - VPN Engineer.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2020 07:47 AM - edited 09-02-2020 07:51 AM
Here are the packet captures from the outside interface of the ASAv. I can also provide packet captures for the outside interface of the remote ASA if needed.
Edit: I don't think the PCAP file is attaching, so if you can't see it here is the output of "show capture CAPOUT detail"
Saas-ASAv(config)# sh capture CAPOUT detail
16 packets captured
1: 14:39:02.773321 000d.3a9c.d349 1234.5678.9abc 0x0800 Length: 616
10.5.7.196.500 > 172.17.0.1.500: [udp sum ok] udp 574 (ttl 255, id 17187)
2: 14:39:03.175741 1234.5678.9abc 000d.3a9c.d349 0x0800 Length: 571
172.17.0.1.500 > 10.5.7.196.500: [udp sum ok] udp 529 (ttl 239, id 27329)
3: 14:39:03.176657 000d.3a9c.d349 1234.5678.9abc 0x0800 Length: 330
10.5.7.196.500 > 172.17.0.1.500: [udp sum ok] udp 288 (ttl 255, id 15667)
4: 14:39:03.197881 1234.5678.9abc 000d.3a9c.d349 0x0800 Length: 298
172.17.0.1.500 > 10.5.7.196.500: [udp sum ok] udp 256 (ttl 239, id 19145)
5: 14:39:03.200932 1234.5678.9abc 000d.3a9c.d349 0x0800 Length: 122
172.17.0.1.500 > 10.5.7.196.500: [udp sum ok] udp 80 (ttl 239, id 32192)
6: 14:39:03.201146 000d.3a9c.d349 1234.5678.9abc 0x0800 Length: 122
10.5.7.196.500 > 172.17.0.1.500: [udp sum ok] udp 80 (ttl 255, id 32048)
7: 14:39:03.219059 1234.5678.9abc 000d.3a9c.d349 0x0800 Length: 122
172.17.0.1.500 > 10.5.7.196.500: [udp sum ok] udp 80 (ttl 239, id 1746)
8: 14:39:03.219226 000d.3a9c.d349 1234.5678.9abc 0x0800 Length: 122
10.5.7.196.500 > 172.17.0.1.500: [udp sum ok] udp 80 (ttl 255, id 2970)
9: 14:39:11.775182 000d.3a9c.d349 1234.5678.9abc 0x0800 Length: 616
10.5.7.196.500 > 172.17.0.1.500: [udp sum ok] udp 574 (ttl 255, id 32170)
10: 14:39:12.180914 1234.5678.9abc 000d.3a9c.d349 0x0800 Length: 571
172.17.0.1.500 > 10.5.7.196.500: [udp sum ok] udp 529 (ttl 239, id 16809)
11: 14:39:12.181936 000d.3a9c.d349 1234.5678.9abc 0x0800 Length: 330
10.5.7.196.500 > 172.17.0.1.500: [udp sum ok] udp 288 (ttl 255, id 15938)
12: 14:39:12.203053 1234.5678.9abc 000d.3a9c.d349 0x0800 Length: 298
172.17.0.1.500 > 10.5.7.196.500: [udp sum ok] udp 256 (ttl 239, id 27569)
13: 14:39:12.206822 1234.5678.9abc 000d.3a9c.d349 0x0800 Length: 122
172.17.0.1.500 > 10.5.7.196.500: [udp sum ok] udp 80 (ttl 239, id 11571)
14: 14:39:12.207035 000d.3a9c.d349 1234.5678.9abc 0x0800 Length: 122
10.5.7.196.500 > 172.17.0.1.500: [udp sum ok] udp 80 (ttl 255, id 24308)
15: 14:39:12.224857 1234.5678.9abc 000d.3a9c.d349 0x0800 Length: 122
172.17.0.1.500 > 10.5.7.196.500: [udp sum ok] udp 80 (ttl 239, id 10019)
16: 14:39:12.225040 000d.3a9c.d349 1234.5678.9abc 0x0800 Length: 122
10.5.7.196.500 > 172.17.0.1.500: [udp sum ok] udp 80 (ttl 255, id 1153)
16 packets shown
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2020 07:43 PM - edited 09-02-2020 07:47 PM
I finally got the ikev2 debug to work. Please see the attached file.
EDIT: It appears I still can't attach files. Please see below.
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=000 0000000000000 (I) MsgID = 00000000 CurState: IDLE Event: EV_INIT_SA
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=00000000000000 00 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_GET_IKE_POLICY
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=00000000000000 00 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_SET_POLICY
IKEv2-PROTO-7: (423): Setting configured policies
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=00000000000000 00 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_CHK_AUTH4PKI
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=00000000000000 00 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_GEN_DH_KEY
IKEv2-PROTO-4: (423): [IKEv2 -> Crypto Engine] Computing DH public key, DH Group 14
IKEv2-PROTO-4: (423): Request queued for computation of DH key
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=00000000000000 00 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_NO_EVENT
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=00000000000000 00 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_OK_RECD_DH_PUBKEY_RESP
IKEv2-PROTO-7: (423): Action: Action_Null
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=00000000000000 00 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_GET_CONFIG_MODE
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=00000000000000 00 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_BLD_MSG
IKEv2-PROTO-4: (423): Generating IKE_SA_INIT message
IKEv2-PROTO-4: (423): IKE Proposal: 1, SPI size: 0 (initial negotiation),
Num. transforms: 4
(423): AES-CBC(423): SHA256(423): SHA256(423): DH_GROUP_2048_MODP/Gr oup 14IKEv2-PROTO-7: Construct Vendor Specific Payload: DELETE-REASONIKEv2-PROTO -7: Construct Vendor Specific Payload: (CUSTOM)IKEv2-PROTO-7: Construct Notify P ayload: NAT_DETECTION_SOURCE_IPIKEv2-PROTO-7: Construct Notify Payload: NAT_DETE CTION_DESTINATION_IPIKEv2-PROTO-7: Construct Notify Payload: IKEV2_FRAGMENTATION _SUPPORTEDIKEv2-PROTO-7: Construct Vendor Specific Payload: FRAGMENTATION(423):
IKEv2-PROTO-4: (423): Sending Packet [To 172.17.0.1:500/From 10.5.7.196:500/VR F i0:f0]
(423): Initiator SPI : 0B09989D5CADF4B4 - Responder SPI : 0000000000000000 Messa ge id: 0
(423): IKEv2 IKE_SA_INIT Exchange REQUESTIKEv2-PROTO-5: (423): Next payload: SA, version: 2.0 (423): Exchange type: IKE_SA_INIT, flags: INITIATOR (423): Message id: 0, length: 574(423):
Payload contents:
(423): SA(423): Next payload: KE, reserved: 0x0, length: 48
(423): last proposal: 0x0, reserved: 0x0, length: 44
Proposal: 1, Protocol id: IKE, SPI size: 0, #trans: 4(423): last transform : 0x3, reserved: 0x0: length: 12
type: 1, reserved: 0x0, id: AES-CBC
(423): last transform: 0x3, reserved: 0x0: length: 8
type: 2, reserved: 0x0, id: SHA256
(423): last transform: 0x3, reserved: 0x0: length: 8
type: 3, reserved: 0x0, id: SHA256
(423): last transform: 0x0, reserved: 0x0: length: 8
type: 4, reserved: 0x0, id: DH_GROUP_2048_MODP/Group 14
(423): KE(423): Next payload: N, reserved: 0x0, length: 264
(423): DH group: 14, Reserved: 0x0
(423):
(423): 42 03 3c 46 2e b3 02 04 68 41 18 9a da da c3 bc
(423): 25 a6 88 ad 4d 35 21 a5 19 c3 77 28 0c fe 90 49
(423): 54 72 f0 3f bc b2 7a 0c 41 8f 69 7f d9 6f 42 df
(423): a1 84 cd 43 3f a2 ee 2d 7a aa 0e 32 bd 87 cb 50
(423): e0 d3 a1 ba db 7f 5a 8a 0a c1 a6 56 7f 45 86 05
(423): a7 55 f3 a6 01 88 ff 92 7a 37 30 ad 7b cf ed 14
(423): f6 9f e2 4e f1 30 22 91 b3 59 7d 40 07 fa 72 ca
(423): 81 ec f8 a8 8e 16 da b0 83 61 27 7e a2 69 31 c6
(423): 16 d1 1e 36 7e 06 d7 d1 11 0d 28 14 07 1f 7e 6c
(423): 16 55 b4 3f 74 75 4e 5b b2 44 72 f5 da 06 45 f0
(423): 7a 48 b9 78 74 c3 5e d7 4d 00 93 f4 15 b7 fb 2f
(423): 68 db f8 af 37 6b b8 5e 37 8b c9 da 5e 52 79 7b
(423): 3f 25 15 a2 e1 8d 52 b3 a9 ec 8a 69 53 ba 60 22
(423): 32 29 ef 5c 19 16 18 c5 32 16 a3 c2 1d d7 a9 7f
(423): b8 b2 bd 35 04 10 00 c5 ff bb c2 46 62 a4 44 9f
(423): 97 85 17 72 50 d2 1a a2 4d 54 9f 99 93 7c b1 ba
(423): N(423): Next payload: VID, reserved: 0x0, length: 68
(423):
(423): 32 2a 33 11 a5 71 7c 2b ef b1 15 60 7e df c1 10
(423): e7 b8 4d bb 0b 3b a5 fc d6 0e 9f e4 91 ad 73 f6
(423): 87 ed 60 fc a3 7e 40 b7 4e 9c 15 02 f4 53 63 67
(423): 9e ce 11 e8 ec e8 c0 02 6b b4 db 36 3a 4c 64 a4
(423): VID(423): Next payload: VID, reserved: 0x0, length: 23
(423):
(423): 43 49 53 43 4f 2d 44 45 4c 45 54 45 2d 52 45 41
(423): 53 4f 4e
(423): VID(423): Next payload: NOTIFY, reserved: 0x0, length: 59
(423):
(423): 43 49 53 43 4f 28 43 4f 50 59 52 49 47 48 54 29
(423): 26 43 6f 70 79 72 69 67 68 74 20 28 63 29 20 32
(423): 30 30 39 20 43 69 73 63 6f 20 53 79 73 74 65 6d
(423): 73 2c 20 49 6e 63 2e
(423): NOTIFY(NAT_DETECTION_SOURCE_IP)(423): Next payload: NOTIFY, reserved: 0x0, length: 28
(423): Security protocol id: IKE, spi size: 0, type: NAT_DETECTION_SOURCE_IP
(423):
(423): 6c 43 3a 02 a2 76 35 1e fc ab 59 92 ff f1 c0 49
(423): 4c 20 8f 6e
(423): NOTIFY(NAT_DETECTION_DESTINATION_IP)(423): Next payload: NOTIFY, reser ved: 0x0, length: 28
(423): Security protocol id: IKE, spi size: 0, type: NAT_DETECTION_DESTINATI ON_IP
(423):
(423): a7 8e 5e 10 28 f6 89 c1 01 49 2f db 18 e8 94 78
(423): 10 69 b6 7b
(423): NOTIFY(IKEV2_FRAGMENTATION_SUPPORTED)(423): Next payload: VID, reserve d: 0x0, length: 8
(423): Security protocol id: Unknown - 0, spi size: 0, type: IKEV2_FRAGMENTA TION_SUPPORTED
(423): VID(423): Next payload: NONE, reserved: 0x0, length: 20
(423):
(423): 40 48 b7 d5 6e bc e8 85 25 e7 de 7f 00 d6 c2 d3
(423):
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=00000000000000 00 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_INSERT_SA
IKEv2-PROTO-4: (423): Insert SA
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=00000000000000 00 (I) MsgID = 00000000 CurState: I_WAIT_INIT Event: EV_NO_EVENT
(423):
IKEv2-PROTO-4: (423): Received Packet [From 172.17.0.1:500/To 10.5.7.196:500/V RF i0:f0]
(423): Initiator SPI : 0B09989D5CADF4B4 - Responder SPI : 76A03DE8E5FAA77B Messa ge id: 0
(423): IKEv2 IKE_SA_INIT Exchange RESPONSEIKEv2-PROTO-5: (423): Next payload: SA , version: 2.0 (423): Exchange type: IKE_SA_INIT, flags: RESPONDER MSG-RESPONSE (423): Message id: 0, length: 529(423):
Payload contents:
(423): SA(423): Next payload: KE, reserved: 0x0, length: 48
(423): last proposal: 0x0, reserved: 0x0, length: 44
Proposal: 1, Protocol id: IKE, SPI size: 0, #trans: 4(423): last transform : 0x3, reserved: 0x0: length: 12
type: 1, reserved: 0x0, id: AES-CBC
(423): last transform: 0x3, reserved: 0x0: length: 8
type: 2, reserved: 0x0, id: SHA256
(423): last transform: 0x3, reserved: 0x0: length: 8
type: 3, reserved: 0x0, id: SHA256
(423): last transform: 0x0, reserved: 0x0: length: 8
type: 4, reserved: 0x0, id: DH_GROUP_2048_MODP/Group 14
(423): KE(423): Next payload: N, reserved: 0x0, length: 264
(423): DH group: 14, Reserved: 0x0
(423):
(423): ab c3 d3 7a 98 37 66 3d f3 e7 aa 20 08 bd 2d fd
(423): 36 b1 04 6e 9b 26 cb ee 91 68 59 86 af 31 b9 a7
(423): ca 3c cc 8d db 9b 90 92 bf d5 7a 77 dc 2e 25 68
(423): 08 f7 1e ea c5 95 1a a2 20 34 fc 1e 17 fc 6c 07
(423): 93 c4 b5 43 e3 73 ed fc df 2e 17 28 e2 c2 be 69
(423): 43 c2 30 87 1b 92 67 81 85 8b ed 0b 4a 7d 6f ad
(423): 29 05 ad fa 4f ab 99 e0 e9 cf 24 2f 30 32 fa 02
(423): 52 d4 d9 af 43 b2 d0 3f a7 1d 62 86 d1 ee 06 dd
(423): 7f 78 3f 1f 12 fc 28 92 d1 28 fe 56 74 e7 df f7
(423): b2 0b a5 fc 99 3d cc 8a 10 15 00 52 c8 ed b7 95
(423): dd e8 d5 b5 9c 68 94 92 f8 bc d3 4c ae 24 98 07
(423): e5 02 29 6f cc 57 5d 0f 2f 72 36 b9 11 4c 73 57
(423): 11 6f 9e 6d 47 5b 0e 67 01 51 11 f4 8d 94 47 23
(423): 07 91 2e 4a 6c d4 dc ce 0a 86 7a 3d 18 27 6a 17
(423): 61 e0 a6 46 05 a2 4f b6 ed eb 6c 11 57 31 ef e9
(423): 67 62 98 e5 e8 b3 64 90 3c 4a a0 67 82 a0 cc 52
(423): N(423): Next payload: VID, reserved: 0x0, length: 68
(423):
(423): 37 7f a6 ba 90 d9 10 25 c2 45 4b 9c bc 87 4c 60
(423): 53 ae 31 29 6b df 3c 86 d8 5b 54 e0 9f ea ac 35
(423): 66 b5 44 fb d8 fb 71 1a 88 8e e1 5e 00 3f e0 e3
(423): 6b 87 63 a9 76 37 1e 49 47 59 67 f8 cb 2b ca aa
IKEv2-PROTO-7: Parse Vendor Specific Payload: CISCO-DELETE-REASON(423): VID(423 ): Next payload: VID, reserved: 0x0, length: 23
(423):
(423): 43 49 53 43 4f 2d 44 45 4c 45 54 45 2d 52 45 41
(423): 53 4f 4e
IKEv2-PROTO-7: Parse Vendor Specific Payload: (CUSTOM)(423): VID(423): Next p ayload: VID, reserved: 0x0, length: 59
(423):
(423): 43 49 53 43 4f 28 43 4f 50 59 52 49 47 48 54 29
(423): 26 43 6f 70 79 72 69 67 68 74 20 28 63 29 20 32
(423): 30 30 39 20 43 69 73 63 6f 20 53 79 73 74 65 6d
(423): 73 2c 20 49 6e 63 2e
IKEv2-PROTO-7: Parse Vendor Specific Payload: (CUSTOM)(423): VID(423): Next p ayload: VID, reserved: 0x0, length: 19
(423):
(423): 43 49 53 43 4f 2d 47 52 45 2d 4d 4f 44 45 02
IKEv2-PROTO-7: Parse Vendor Specific Payload: FRAGMENTATION(423): VID(423): N ext payload: NONE, reserved: 0x0, length: 20
(423):
(423): 40 48 b7 d5 6e bc e8 85 25 e7 de 7f 00 d6 c2 d3
(423):
(423): Decrypted packet:(423): Data: 529 bytes
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: I_WAIT_INIT Event: EV_RECV_INIT
IKEv2-PROTO-7: (423): Processing IKE_SA_INIT message
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: I_PROC_INIT Event: EV_CHK4_NOTIFY
IKEv2-PROTO-4: (423): Processing IKE_SA_INIT message
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: I_PROC_INIT Event: EV_VERIFY_MSG
IKEv2-PROTO-4: (423): Verify SA init message
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: I_PROC_INIT Event: EV_PROC_MSG
IKEv2-PROTO-4: (423): Processing IKE_SA_INIT message
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: I_PROC_INIT Event: EV_DETECT_NAT
IKEv2-PROTO-7: (423): Process NAT discovery notify
IKEv2-PROTO-7: (423): No NAT found
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: I_PROC_INIT Event: EV_CHK_NAT_T
IKEv2-PROTO-4: (423): Checking NAT discovery
IKEv2-PROTO-4: (423): NAT not found
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: I_PROC_INIT Event: EV_CHK_CONFIG_MODE
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: INIT_DONE Event: EV_GEN_DH_SECRET
IKEv2-PROTO-4: (423): [IKEv2 -> Crypto Engine] Computing DH secret key, DH Group 14
IKEv2-PROTO-4: (423): Request queued for computation of DH secret
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: INIT_DONE Event: EV_NO_EVENT
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: INIT_DONE Event: EV_OK_RECD_DH_SECRET_RESP
IKEv2-PROTO-7: (423): Action: Action_Null
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: INIT_DONE Event: EV_GEN_SKEYID
IKEv2-PROTO-7: (423): Generate skeyid
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: INIT_DONE Event: EV_DONE
IKEv2-PROTO-4: (423): Cisco Fragmentation is enabled
IKEv2-PROTO-7: (423): Cisco DeleteReason Notify is enabled
IKEv2-PROTO-4: (423): Completed SA init exchange
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: INIT_DONE Event: EV_CHK4_ROLE
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: I_BLD_AUTH Event: EV_GET_CONFIG_MODE
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: I_BLD_AUTH Event: EV_CHK_EAP
IKEv2-PROTO-4: (423): Check for EAP exchange
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: I_BLD_AUTH Event: EV_GEN_AUTH
IKEv2-PROTO-4: (423): Generate my authentication data
IKEv2-PROTO-4: (423): Use preshared key for id 10.5.7.196, key len 9
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: I_BLD_AUTH Event: EV_CHK_AUTH_TYPE
IKEv2-PROTO-4: (423): Get my authentication method
IKEv2-PROTO-4: (423): My authentication method is 'PSK'
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: I_BLD_AUTH Event: EV_OK_AUTH_GEN
IKEv2-PROTO-4: (423): Check for EAP exchange
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000000 CurState: I_BLD_AUTH Event: EV_SEND_AUTH
IKEv2-PROTO-4: (423): Generating IKE_AUTH message
IKEv2-PROTO-7: Construct Vendor Specific Payload: CISCO-GRANITEIKEv2-PROTO-4: (4 23): Constructing IDi payload: '10.5.7.196' of type 'IPv4 address'
IKEv2-PROTO-4: (423): ESP Proposal: 1, SPI size: 4 (IPSec negotiation),
Num. transforms: 3
(423): AES-CBC(423): SHA96(423): Don't use ESNIKEv2-PROTO-7: Construct Notify Payload: INITIAL_CONTACTIKEv2-PROTO-7: Construct Notify Payload: ESP_TFC_ NO_SUPPORTIKEv2-PROTO-7: Construct Notify Payload: NON_FIRST_FRAGSIKEv2-PROTO-4: (423): Building packet for encryption.
(423):
Payload contents:
(423): VID(423): Next payload: IDi, reserved: 0x0, length: 20
(423):
(423): 09 09 99 9d 4f 9a 07 f3 9f 7d 93 96 6b 9d 80 56
(423): IDi(423): Next payload: AUTH, reserved: 0x0, length: 12
(423): Id type: IPv4 address, Reserved: 0x0 0x0
(423):
(423): 0a 05 07 c4
(423): AUTH(423): Next payload: SA, reserved: 0x0, length: 40
(423): Auth method PSK, reserved: 0x0, reserved 0x0
(423): Auth data: 32 bytes
(423): SA(423): Next payload: TSi, reserved: 0x0, length: 44
(423): last proposal: 0x0, reserved: 0x0, length: 40
Proposal: 1, Protocol id: ESP, SPI size: 4, #trans: 3(423): last transform : 0x3, reserved: 0x0: length: 12
type: 1, reserved: 0x0, id: AES-CBC
(423): last transform: 0x3, reserved: 0x0: length: 8
type: 3, reserved: 0x0, id: SHA96
(423): last transform: 0x0, reserved: 0x0: length: 8
type: 5, reserved: 0x0, id: Don't use ESN
(423): TSi(423): Next payload: TSr, reserved: 0x0, length: 40
(423): Num of TSs: 2, reserved 0x0, reserved 0x0
(423): TS type: TS_IPV4_ADDR_RANGE, proto id: 0, length: 16
(423): start port: 0, end port: 65535
(423): start addr: 10.249.0.9, end addr: 10.249.0.9
(423): TS type: TS_IPV4_ADDR_RANGE, proto id: 0, length: 16
(423): start port: 0, end port: 65535
(423): start addr: 10.249.0.0, end addr: 10.249.1.255
(423): TSr(423): Next payload: NOTIFY, reserved: 0x0, length: 40
(423): Num of TSs: 2, reserved 0x0, reserved 0x0
(423): TS type: TS_IPV4_ADDR_RANGE, proto id: 0, length: 16
(423): start port: 0, end port: 65535
(423): start addr: 172.17.0.21, end addr: 172.17.0.21
(423): TS type: TS_IPV4_ADDR_RANGE, proto id: 0, length: 16
(423): start port: 0, end port: 65535
(423): start addr: 172.17.0.0, end addr: 172.17.0.255
(423): NOTIFY(INITIAL_CONTACT)(423): Next payload: NOTIFY, reserved: 0x0, len gth: 8
(423): Security protocol id: IKE, spi size: 0, type: INITIAL_CONTACT
(423): NOTIFY(ESP_TFC_NO_SUPPORT)(423): Next payload: NOTIFY, reserved: 0x0, length: 8
(423): Security protocol id: IKE, spi size: 0, type: ESP_TFC_NO_SUPPORT
(423): NOTIFY(NON_FIRST_FRAGS)(423): Next payload: NONE, reserved: 0x0, lengt h: 8
(423): Security protocol id: IKE, spi size: 0, type: NON_FIRST_FRAGS
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_BLD_AUTH Event: EV_ENCRYPT_MSG
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_BLD_AUTH Event: EV_NO_EVENT
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_BLD_AUTH Event: EV_OK_ENCRYPT_RESP
IKEv2-PROTO-7: (423): Action: Action_Null
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_BLD_AUTH Event: EV_TRYSEND
(423):
IKEv2-PROTO-4: (423): Sending Packet [To 172.17.0.1:500/From 10.5.7.196:500/VR F i0:f0]
(423): Initiator SPI : 0B09989D5CADF4B4 - Responder SPI : 76A03DE8E5FAA77B Messa ge id: 1
(423): IKEv2 IKE_AUTH Exchange REQUESTIKEv2-PROTO-5: (423): Next payload: ENCR, version: 2.0 (423): Exchange type: IKE_AUTH, flags: INITIATOR (423): Message id: 1, length: 288(423):
Payload contents:
(423): ENCR(423): Next payload: VID, reserved: 0x0, length: 260
(423): Encrypted data: 256 bytes
(423):
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_BLD_AUTH Event: EV_CHK_EAP_POST_ASYNC
IKEv2-PROTO-4: (423): Check for EAP exchange
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_WAIT_AUTH Event: EV_NO_EVENT
(423):
IKEv2-PROTO-4: (423): Received Packet [From 172.17.0.1:500/To 10.5.7.196:500/V RF i0:f0]
(423): Initiator SPI : 0B09989D5CADF4B4 - Responder SPI : 76A03DE8E5FAA77B Messa ge id: 1
(423): IKEv2 IKE_AUTH Exchange RESPONSEIKEv2-PROTO-5: (423): Next payload: ENCR, version: 2.0 (423): Exchange type: IKE_AUTH, flags: RESPONDER MSG-RESPONSE (423 ): Message id: 1, length: 256(423):
Payload contents:
IKEv2-PROTO-4: decrypt queued(423):
(423): Decrypted packet:(423): Data: 256 bytes
(423): REAL Decrypted packet:(423): Data: 180 bytes
IKEv2-PROTO-7: Parse Vendor Specific Payload: (CUSTOM) VID Next payload: IDr, r eserved: 0x0, length: 20
74 a0 3c e8 f6 cd 54 3c 9f 7d 93 96 6b 9d 80 56
IDr Next payload: AUTH, reserved: 0x0, length: 12
Id type: IPv4 address, Reserved: 0x0 0x0
42 ea 6a 02
AUTH Next payload: SA, reserved: 0x0, length: 40
Auth method PSK, reserved: 0x0, reserved 0x0
Auth data: 32 bytes
SA Next payload: TSi, reserved: 0x0, length: 44
last proposal: 0x0, reserved: 0x0, length: 40
Proposal: 1, Protocol id: ESP, SPI size: 4, #trans: 3 last transform: 0x3, reserved: 0x0: length: 12
type: 1, reserved: 0x0, id: AES-CBC
last transform: 0x3, reserved: 0x0: length: 8
type: 3, reserved: 0x0, id: SHA96
last transform: 0x0, reserved: 0x0: length: 8
type: 5, reserved: 0x0, id: Don't use ESN
TSi Next payload: TSr, reserved: 0x0, length: 24
Num of TSs: 1, reserved 0x0, reserved 0x0
TS type: TS_IPV4_ADDR_RANGE, proto id: 0, length: 16
start port: 0, end port: 65535
start addr: 10.249.0.0, end addr: 10.249.1.255
TSr Next payload: NOTIFY, reserved: 0x0, length: 24
Num of TSs: 1, reserved 0x0, reserved 0x0
TS type: TS_IPV4_ADDR_RANGE, proto id: 0, length: 16
start port: 0, end port: 65535
start addr: 172.17.0.0, end addr: 172.17.0.255
IKEv2-PROTO-7: Parse Notify Payload: ESP_TFC_NO_SUPPORT NOTIFY(ESP_TFC_NO_SUPPOR T) Next payload: NOTIFY, reserved: 0x0, length: 8
Security protocol id: IKE, spi size: 0, type: ESP_TFC_NO_SUPPORT
IKEv2-PROTO-7: Parse Notify Payload: NON_FIRST_FRAGS NOTIFY(NON_FIRST_FRAGS) Ne xt payload: NONE, reserved: 0x0, length: 8
Security protocol id: IKE, spi size: 0, type: NON_FIRST_FRAGS
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_WAIT_AUTH Event: EV_RECV_AUTH
IKEv2-PROTO-7: (423): Action: Action_Null
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK4_NOTIFY
IKEv2-PROTO-4: (423): Process auth response notify
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_PROC_MSG
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK_IF_PEER_CERT_NEEDS_T O_BE_FETCHED_FOR_PROF_SEL
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_GET_POLICY_BY_PEERID
IKEv2-PROTO-4: (423): Searching policy based on peer's identity '172.17.0.1' o f type 'IPv4 address'
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_VERIFY_POLICY_BY_PEERID
IKEv2-PROTO-4: (423): Verify peer's policy
IKEv2-PROTO-4: (423): Peer's policy verified
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK_AUTH_TYPE
IKEv2-PROTO-4: (423): Get peer's authentication method
IKEv2-PROTO-4: (423): Peer's authentication method is 'PSK'
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_GET_PRESHR_KEY
IKEv2-PROTO-4: (423): Get peer's preshared key for 172.17.0.1
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_VERIFY_AUTH
IKEv2-PROTO-4: (423): Verify peer's authentication data
IKEv2-PROTO-4: (423): Use preshared key for id 172.17.0.1, key len 9
IKEv2-PROTO-4: (423): Verification of peer's authenctication data PASSED
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK_EAP
IKEv2-PROTO-4: (423): Check for EAP exchange
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_NOTIFY_AUTH_DONE
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK_CONFIG_MODE
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK4_IC
IKEv2-PROTO-4: (423): Processing INITIAL_CONTACT
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK_IKE_ONLY
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_PROC_SA_TS
IKEv2-PROTO-4: (423): Processing IKE_AUTH message
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_OK
IKEv2-PROTO-7: (423): Action: Action_Null
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_UPDATE_CAC_STATS
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_INSERT_IKE
IKEv2-PROTO-4: (423): IKEV2 SA created; inserting SA into database. SA lifetime timer (28800 sec) started
IKEv2-PROTO-4: (423): Session with IKE ID PAIR (172.17.0.1, 10.5.7.196) is UP
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_REGISTER_SESSION
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_NO_EVENT
IKEv2-PROTO-4: (423): Initializing DPD, configured for 10 seconds
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_RECD_REGISTER_SESSION_RESP
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_GEN_LOAD_IPSEC
IKEv2-PROTO-4: (423): Load IPSEC key material
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_NO_EVENT
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_OK_RECD_LOAD_IPSEC
IKEv2-PROTO-7: (423): Action: Action_Null
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_START_ACCT
IKEv2-PROTO-4: (423): DPD timer started for 10 secs
IKEv2-PROTO-7: (423): Accounting not required
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_PARENT_NEG_COMPLETE
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_PKI_SESH_CLOSE
IKEv2-PROTO-7: (423): Closing the PKI session
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_CHECK_DUPE
IKEv2-PROTO-4: (423): Checking for duplicate IKEv2 SA
IKEv2-PROTO-4: (423): No duplicate IKEv2 SA found
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_CHK4_ROLE
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: READY Event: EV_CHK_IKE_ONLY
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: READY Event: EV_I_OK
IKEv2-PROTO-7: (423): Deleting negotiation context for my message ID: 0x1
IKEv2-PROTO-7: (423): Request has mess_id 0; expected 0 through 0
(423):
IKEv2-PROTO-4: (423): Received Packet [From 172.17.0.1:500/To 10.5.7.196:500/V RF i0:f0]
(423): Initiator SPI : 0B09989D5CADF4B4 - Responder SPI : 76A03DE8E5FAA77B Messa ge id: 0
(423): IKEv2 INFORMATIONAL Exchange REQUESTIKEv2-PROTO-5: (423): Next payload: E NCR, version: 2.0 (423): Exchange type: INFORMATIONAL, flags: RESPONDER (423): M essage id: 0, length: 80(423):
Payload contents:
IKEv2-PROTO-4: decrypt queued(423):
(423): Decrypted packet:(423): Data: 80 bytes
(423): REAL Decrypted packet:(423): Data: 12 bytes
DELETE Next payload: NONE, reserved: 0x0, length: 12
Security protocol id: ESP, spi size: 4, num of spi: 1
c0 3a 41 a5
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000000 CurState: READY Event: EV_RECV_INFO_REQ
IKEv2-PROTO-7: (423): Action: Action_Null
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000000 CurState: INFO_R Event: EV_RECV_INFO_REQ
IKEv2-PROTO-4: (423): Building packet for encryption.
(423):
Payload contents:
(423): DELETE(423): Next payload: NONE, reserved: 0x0, length: 12
(423): Security protocol id: ESP, spi size: 4, num of spi: 1
(423):
(423): 0f 58 1b d6
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000000 CurState: INFO_R Event: EV_ENCRYPT_MSG
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000000 CurState: INFO_R Event: EV_NO_EVENT
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000000 CurState: INFO_R Event: EV_OK_ENCRYPT_RESP
IKEv2-PROTO-7: (423): Action: Action_Null
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000000 CurState: INFO_R Event: EV_TRYSEND
(423):
IKEv2-PROTO-4: (423): Sending Packet [To 172.17.0.1:500/From 10.5.7.196:500/VR F i0:f0]
(423): Initiator SPI : 0B09989D5CADF4B4 - Responder SPI : 76A03DE8E5FAA77B Messa ge id: 0
(423): IKEv2 INFORMATIONAL Exchange RESPONSEIKEv2-PROTO-5: (423): Next payload: ENCR, version: 2.0 (423): Exchange type: INFORMATIONAL, flags: INITIATOR MSG-RES PONSE (423): Message id: 0, length: 80(423):
Payload contents:
(423): ENCR(423): Next payload: DELETE, reserved: 0x0, length: 52
(423): Encrypted data: 48 bytes
(423):
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000000 CurState: INFO_R Event: EV_CHK_INFO_TYPE
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000000 CurState: INFO_R Event: EV_RECV_DEL
IKEv2-PROTO-4: (423): Process delete request from peer
IKEv2-PROTO-4: (423): Processing DELETE INFO message for IPsec SA [SPI: 0xC03A41 A5]
IKEv2-PROTO-7: Removing child SA with spi A5413AC0
IKEv2-PROTO-7: Successfully removed child SAs
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000000 CurState: INFO_R Event: EV_CHK4_ACTIVE_SA
IKEv2-PROTO-4: (423): Check for existing active SA
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000000 CurState: INFO_R Event: EV_START_DEL_NEG_TMR
IKEv2-PROTO-7: (423): Action: Action_Null
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000000 CurState: EXIT Event: EV_CHK_PENDING
IKEv2-PROTO-7: (423): Sent response with message id 0, Requests can be accepted from range 1 to 1
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000000 CurState: EXIT Event: EV_NO_EVENT
IKEv2-PROTO-7: (423): Request has mess_id 1; expected 1 through 1
(423):
IKEv2-PROTO-4: (423): Received Packet [From 172.17.0.1:500/To 10.5.7.196:500/V RF i0:f0]
(423): Initiator SPI : 0B09989D5CADF4B4 - Responder SPI : 76A03DE8E5FAA77B Messa ge id: 1
(423): IKEv2 INFORMATIONAL Exchange REQUESTIKEv2-PROTO-5: (423): Next payload: E NCR, version: 2.0 (423): Exchange type: INFORMATIONAL, flags: RESPONDER (423): M essage id: 1, length: 80(423):
Payload contents:
IKEv2-PROTO-4: decrypt queued(423):
(423): Decrypted packet:(423): Data: 80 bytes
(423): REAL Decrypted packet:(423): Data: 8 bytes
DELETE Next payload: NONE, reserved: 0x0, length: 8
Security protocol id: IKE, spi size: 0, num of spi: 0
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: READY Event: EV_RECV_INFO_REQ
IKEv2-PROTO-7: (423): Action: Action_Null
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: INFO_R Event: EV_RECV_INFO_REQ
IKEv2-PROTO-4: (423): Building packet for encryption.
(423):
Payload contents:
(423): DELETE(423): Next payload: NONE, reserved: 0x0, length: 8
(423): Security protocol id: IKE, spi size: 0, num of spi: 0
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: INFO_R Event: EV_ENCRYPT_MSG
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: INFO_R Event: EV_NO_EVENT
IKEv2-PROTO-7: (423): Locked SA.Event EV_FREE_NEG queued in the state EXIT
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: INFO_R Event: EV_OK_ENCRYPT_RESP
IKEv2-PROTO-7: (423): Action: Action_Null
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: INFO_R Event: EV_TRYSEND
(423):
IKEv2-PROTO-4: (423): Sending Packet [To 172.17.0.1:500/From 10.5.7.196:500/VR F i0:f0]
(423): Initiator SPI : 0B09989D5CADF4B4 - Responder SPI : 76A03DE8E5FAA77B Messa ge id: 1
(423): IKEv2 INFORMATIONAL Exchange RESPONSEIKEv2-PROTO-5: (423): Next payload: ENCR, version: 2.0 (423): Exchange type: INFORMATIONAL, flags: INITIATOR MSG-RES PONSE (423): Message id: 1, length: 80(423):
Payload contents:
(423): ENCR(423): Next payload: DELETE, reserved: 0x0, length: 52
(423): Encrypted data: 48 bytes
(423):
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: INFO_R Event: EV_CHK_INFO_TYPE
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: INFO_R Event: EV_RECV_DEL
IKEv2-PROTO-4: (423): Process delete request from peer
IKEv2-PROTO-4: (423): Processing DELETE INFO message for IKEv2 SA [ISPI: 0x0B099 89D5CADF4B4 RSPI: 0x76A03DE8E5FAA77B]
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: INFO_R Event: EV_CHK4_ACTIVE_SA
IKEv2-PROTO-4: (423): Check for existing active SA
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: INFO_R Event: EV_STOP_ACCT
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: INFO_R Event: EV_IPSEC_DEL
IKEv2-PROTO-4: (423): Delete all IKE SAs
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: INFO_R Event: EV_START_DEL_NEG_TMR
IKEv2-PROTO-7: (423): Action: Action_Null
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: EXIT Event: EV_CHK_PENDING
IKEv2-PROTO-7: (423): Sent response with message id 1, Requests can be accepted from range 2 to 2
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000001 CurState: EXIT Event: EV_NO_EVENT
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (R) MsgID = 00000000 CurState: EXIT Event: EV_FREE_NEG
IKEv2-PROTO-7: (423): Deleting negotiation context for peer message ID: 0x0
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: READY Event: EV_RECV_DEL
IKEv2-PROTO-7: (423): SM Trace-> SA: I_SPI=0B09989D5CADF4B4 R_SPI=76A03DE8E5FAA7 7B (I) MsgID = 00000001 CurState: DELETE Event: EV_FREE_SA
IKEv2-PROTO-4: (423): Deleting SA
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=0000000000000000 (I) MsgID = 00000000 CurState: IDLE Event: EV_INIT_SA
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=0000000000000000 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_GET_IKE_POLICY
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=0000000000000000 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_SET_POLICY
IKEv2-PROTO-7: (845): Setting configured policies
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=0000000000000000 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_CHK_AUTH4PKI
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=0000000000000000 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_GEN_DH_KEY
IKEv2-PROTO-4: (845): [IKEv2 -> Crypto Engine] Computing DH public key, DH Group 14
IKEv2-PROTO-4: (845): Request queued for computation of DH key
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=0000000000000000 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_NO_EVENT
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=0000000000000000 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_OK_RECD_DH_PUBKEY_RESP
IKEv2-PROTO-7: (845): Action: Action_Null
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=0000000000000000 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_GET_CONFIG_MODE
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=0000000000000000 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_BLD_MSG
IKEv2-PROTO-4: (845): Generating IKE_SA_INIT message
IKEv2-PROTO-4: (845): IKE Proposal: 1, SPI size: 0 (initial negotiation),
Num. transforms: 4
(845): AES-CBC(845): SHA256(845): SHA256(845): DH_GROUP_2048_MODP/Group 14IKEv2-PROTO-7: Construct Vendor Specific Payload: DELETE-REASONIKEv2-PROTO-7: Construct Vendor Specific Payload: (CUSTOM)IKEv2-PROTO-7: Construct Notify Payload: NAT_DETECTION_SOURCE_IPIKEv2-PROTO-7: Construct Notify Payload: NAT_DETECTION_DESTINATION_IPIKEv2-PROTO-7: Construct Notify Payload: IKEV2_FRAGMENTATION_SUPPORTEDIKEv2-PROTO-7: Construct Vendor Specific Payload: FRAGMENTATION(845):
IKEv2-PROTO-4: (845): Sending Packet [To 172.17.0.1:500/From 10.5.7.196:500/VRF i0:f0]
(845): Initiator SPI : 24F73212A5F2FB99 - Responder SPI : 0000000000000000 Message id: 0
(845): IKEv2 IKE_SA_INIT Exchange REQUESTIKEv2-PROTO-5: (845): Next payload: SA, version: 2.0 (845): Exchange type: IKE_SA_INIT, flags: INITIATOR (845): Message id: 0, length: 574(845):
Payload contents:
(845): SA(845): Next payload: KE, reserved: 0x0, length: 48
(845): last proposal: 0x0, reserved: 0x0, length: 44
Proposal: 1, Protocol id: IKE, SPI size: 0, #trans: 4(845): last transform: 0x3, reserved: 0x0: length: 12
type: 1, reserved: 0x0, id: AES-CBC
(845): last transform: 0x3, reserved: 0x0: length: 8
type: 2, reserved: 0x0, id: SHA256
(845): last transform: 0x3, reserved: 0x0: length: 8
type: 3, reserved: 0x0, id: SHA256
(845): last transform: 0x0, reserved: 0x0: length: 8
type: 4, reserved: 0x0, id: DH_GROUP_2048_MODP/Group 14
(845): KE(845): Next payload: N, reserved: 0x0, length: 264
(845): DH group: 14, Reserved: 0x0
(845):
(845): d1 40 37 78 68 a7 f8 9e 42 75 1a cd 15 f1 32 2d
(845): 87 57 ff 92 35 b1 0a c7 db f4 11 03 9d 48 64 e8
(845): 30 11 b7 62 43 a6 42 2f 1a eb ba 6b a6 c1 3f c5
(845): 5b ad 44 65 e3 81 8f 57 d7 5d a4 ab 78 03 2a 5a
(845): d5 b8 88 f3 cd c3 4a fa f0 bf ee d5 8b 1e d8 bb
(845): 4f f0 06 21 e4 8b ed d3 36 74 44 b5 a4 99 b3 fe
(845): 4a f9 ca 3e 6b 5b ec 02 cd 31 73 e7 13 41 42 31
(845): 13 26 51 75 e3 cd 9b af 94 93 a9 11 d5 97 00 ea
(845): c4 c6 6a 50 67 01 23 07 e8 71 66 83 cc 10 4b 64
(845): 15 a6 6e 6d 9c 29 91 64 07 ef 20 e8 61 87 a5 e4
(845): 8e 72 62 68 c4 8e 87 72 22 f9 05 75 2d 09 2c 69
(845): 45 a1 1b 7e 07 08 7f c3 66 c0 ad 5d 01 a9 92 8f
(845): 47 d0 85 7d b5 f7 bf 45 ae ae df d4 e8 e5 8e 1d
(845): ac 1e e2 a2 0c 61 a6 fd 30 06 ee e7 8c d7 1b 93
(845): 3e 19 01 bf e0 f5 c8 15 71 64 92 11 d3 98 42 d0
(845): 55 db fd 61 a7 e7 a0 48 12 4e 5a 44 17 23 e8 a5
(845): N(845): Next payload: VID, reserved: 0x0, length: 68
(845):
(845): 3d 06 0d ba 40 6a 84 4e e4 1a fc ef 9b 63 9a 29
(845): 42 60 99 f4 54 0a 39 c2 2f ee bf 9f 0d d6 11 3f
(845): 82 40 ed 9a 61 13 3e 8c f4 e8 8e 40 04 7e 03 48
(845): fb a5 ca 3c 41 68 0c 9f 4f d6 cc 32 b3 6a 2e e9
(845): VID(845): Next payload: VID, reserved: 0x0, length: 23
(845):
(845): 43 49 53 43 4f 2d 44 45 4c 45 54 45 2d 52 45 41
(845): 53 4f 4e
(845): VID(845): Next payload: NOTIFY, reserved: 0x0, length: 59
(845):
(845): 43 49 53 43 4f 28 43 4f 50 59 52 49 47 48 54 29
(845): 26 43 6f 70 79 72 69 67 68 74 20 28 63 29 20 32
(845): 30 30 39 20 43 69 73 63 6f 20 53 79 73 74 65 6d
(845): 73 2c 20 49 6e 63 2e
(845): NOTIFY(NAT_DETECTION_SOURCE_IP)(845): Next payload: NOTIFY, reserved: 0x0, length: 28
(845): Security protocol id: IKE, spi size: 0, type: NAT_DETECTION_SOURCE_IP
(845):
(845): 9a c5 a7 13 a0 84 b2 02 4f b6 f2 a0 2e cc d1 a9
(845): 6d 1e d9 ed
(845): NOTIFY(NAT_DETECTION_DESTINATION_IP)(845): Next payload: NOTIFY, reserved: 0x0, length: 28
(845): Security protocol id: IKE, spi size: 0, type: NAT_DETECTION_DESTINATION_IP
(845):
(845): c8 b0 48 70 e3 f5 2e a8 43 ba 85 c1 51 54 19 95
(845): 70 72 64 69
(845): NOTIFY(IKEV2_FRAGMENTATION_SUPPORTED)(845): Next payload: VID, reserved: 0x0, length: 8
(845): Security protocol id: Unknown - 0, spi size: 0, type: IKEV2_FRAGMENTATION_SUPPORTED
(845): VID(845): Next payload: NONE, reserved: 0x0, length: 20
(845):
(845): 40 48 b7 d5 6e bc e8 85 25 e7 de 7f 00 d6 c2 d3
(845):
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=0000000000000000 (I) MsgID = 00000000 CurState: I_BLD_INIT Event: EV_INSERT_SA
IKEv2-PROTO-4: (845): Insert SA
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=0000000000000000 (I) MsgID = 00000000 CurState: I_WAIT_INIT Event: EV_NO_EVENT
(845):
IKEv2-PROTO-4: (845): Received Packet [From 172.17.0.1:500/To 10.5.7.196:500/VRF i0:f0]
(845): Initiator SPI : 24F73212A5F2FB99 - Responder SPI : EE68310E6E6B1C24 Message id: 0
(845): IKEv2 IKE_SA_INIT Exchange RESPONSEIKEv2-PROTO-5: (845): Next payload: SA, version: 2.0 (845): Exchange type: IKE_SA_INIT, flags: RESPONDER MSG-RESPONSE (845): Message id: 0, length: 529(845):
Payload contents:
(845): SA(845): Next payload: KE, reserved: 0x0, length: 48
(845): last proposal: 0x0, reserved: 0x0, length: 44
Proposal: 1, Protocol id: IKE, SPI size: 0, #trans: 4(845): last transform: 0x3, reserved: 0x0: length: 12
type: 1, reserved: 0x0, id: AES-CBC
(845): last transform: 0x3, reserved: 0x0: length: 8
type: 2, reserved: 0x0, id: SHA256
(845): last transform: 0x3, reserved: 0x0: length: 8
type: 3, reserved: 0x0, id: SHA256
(845): last transform: 0x0, reserved: 0x0: length: 8
type: 4, reserved: 0x0, id: DH_GROUP_2048_MODP/Group 14
(845): KE(845): Next payload: N, reserved: 0x0, length: 264
(845): DH group: 14, Reserved: 0x0
(845):
(845): 4f 66 c7 e3 56 2a 3c 30 68 8d 3d 56 2a 97 d3 86
(845): 3a d3 96 b5 2d 0f 6d 32 82 27 17 b2 51 3d 2b e6
(845): 43 4a c4 26 19 ea 3e 05 44 83 f6 c6 8a 7c 4b 1a
(845): 08 99 a9 62 70 42 37 0d 9f 68 e1 b5 40 c6 48 ce
(845): dc 5b a9 25 c1 dd 29 97 a1 b4 ee 1f 54 83 a8 f4
(845): 7b 54 d4 54 3b 24 9a 8d 7a 5d 78 a7 fe 85 da cf
(845): 35 0e d1 58 f8 dc 1f e1 01 71 43 9d e8 0f 0f e5
(845): f6 44 3c 23 3b 13 db f3 d0 14 d3 6f 7c ff 1b 3f
(845): 94 07 38 93 ea 29 94 e2 53 06 76 f8 ed 0b 39 59
(845): a1 dc 7e 5e 1b 9a 32 29 44 6f 3c f4 0c 37 c4 09
(845): 48 3a a3 c1 3c f7 39 0e 4b f7 a6 45 fa 60 16 e6
(845): 8d ec 81 b3 24 9d 37 d5 32 86 07 77 ea af 61 69
(845): 22 86 5f 45 9b e9 30 3f 72 75 14 c6 2c 89 43 eb
(845): 73 92 5d 94 ba 8c 2a cc 06 68 98 57 32 9d 6e ef
(845): 40 a0 8f 03 28 34 e6 04 01 ed 98 f3 4e 79 ae c5
(845): 3f 82 86 b8 6d ea c6 f8 46 cd 13 95 f9 94 23 df
(845): N(845): Next payload: VID, reserved: 0x0, length: 68
(845):
(845): fe 07 eb 5c ea 4e 01 8b 14 41 88 80 ae 0e c4 fe
(845): 6d b1 13 9e 24 29 06 9d e2 50 2c e4 fa 3b 9a 5b
(845): b7 02 6f ee bd 88 9c 9c ba 98 cf 12 9c f5 b9 77
(845): f0 c7 57 45 2c 85 c9 b3 6f dc 89 8b 0a d5 a0 49
IKEv2-PROTO-7: Parse Vendor Specific Payload: CISCO-DELETE-REASON(845): VID(845): Next payload: VID, reserved: 0x0, length: 23
(845):
(845): 43 49 53 43 4f 2d 44 45 4c 45 54 45 2d 52 45 41
(845): 53 4f 4e
IKEv2-PROTO-7: Parse Vendor Specific Payload: (CUSTOM)(845): VID(845): Next payload: VID, reserved: 0x0, length: 59
(845):
(845): 43 49 53 43 4f 28 43 4f 50 59 52 49 47 48 54 29
(845): 26 43 6f 70 79 72 69 67 68 74 20 28 63 29 20 32
(845): 30 30 39 20 43 69 73 63 6f 20 53 79 73 74 65 6d
(845): 73 2c 20 49 6e 63 2e
IKEv2-PROTO-7: Parse Vendor Specific Payload: (CUSTOM)(845): VID(845): Next payload: VID, reserved: 0x0, length: 19
(845):
(845): 43 49 53 43 4f 2d 47 52 45 2d 4d 4f 44 45 02
IKEv2-PROTO-7: Parse Vendor Specific Payload: FRAGMENTATION(845): VID(845): Next payload: NONE, reserved: 0x0, length: 20
(845):
(845): 40 48 b7 d5 6e bc e8 85 25 e7 de 7f 00 d6 c2 d3
(845):
(845): Decrypted packet:(845): Data: 529 bytes
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: I_WAIT_INIT Event: EV_RECV_INIT
IKEv2-PROTO-7: (845): Processing IKE_SA_INIT message
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: I_PROC_INIT Event: EV_CHK4_NOTIFY
IKEv2-PROTO-4: (845): Processing IKE_SA_INIT message
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: I_PROC_INIT Event: EV_VERIFY_MSG
IKEv2-PROTO-4: (845): Verify SA init message
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: I_PROC_INIT Event: EV_PROC_MSG
IKEv2-PROTO-4: (845): Processing IKE_SA_INIT message
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: I_PROC_INIT Event: EV_DETECT_NAT
IKEv2-PROTO-7: (845): Process NAT discovery notify
IKEv2-PROTO-7: (845): No NAT found
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: I_PROC_INIT Event: EV_CHK_NAT_T
IKEv2-PROTO-4: (845): Checking NAT discovery
IKEv2-PROTO-4: (845): NAT not found
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: I_PROC_INIT Event: EV_CHK_CONFIG_MODE
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: INIT_DONE Event: EV_GEN_DH_SECRET
IKEv2-PROTO-4: (845): [IKEv2 -> Crypto Engine] Computing DH secret key, DH Group 14
IKEv2-PROTO-4: (845): Request queued for computation of DH secret
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: INIT_DONE Event: EV_NO_EVENT
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: INIT_DONE Event: EV_OK_RECD_DH_SECRET_RESP
IKEv2-PROTO-7: (845): Action: Action_Null
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: INIT_DONE Event: EV_GEN_SKEYID
IKEv2-PROTO-7: (845): Generate skeyid
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: INIT_DONE Event: EV_DONE
IKEv2-PROTO-4: (845): Cisco Fragmentation is enabled
IKEv2-PROTO-7: (845): Cisco DeleteReason Notify is enabled
IKEv2-PROTO-4: (845): Completed SA init exchange
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: INIT_DONE Event: EV_CHK4_ROLE
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: I_BLD_AUTH Event: EV_GET_CONFIG_MODE
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: I_BLD_AUTH Event: EV_CHK_EAP
IKEv2-PROTO-4: (845): Check for EAP exchange
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: I_BLD_AUTH Event: EV_GEN_AUTH
IKEv2-PROTO-4: (845): Generate my authentication data
IKEv2-PROTO-4: (845): Use preshared key for id 10.5.7.196, key len 9
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: I_BLD_AUTH Event: EV_CHK_AUTH_TYPE
IKEv2-PROTO-4: (845): Get my authentication method
IKEv2-PROTO-4: (845): My authentication method is 'PSK'
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: I_BLD_AUTH Event: EV_OK_AUTH_GEN
IKEv2-PROTO-4: (845): Check for EAP exchange
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000000 CurState: I_BLD_AUTH Event: EV_SEND_AUTH
IKEv2-PROTO-4: (845): Generating IKE_AUTH message
IKEv2-PROTO-7: Construct Vendor Specific Payload: CISCO-GRANITEIKEv2-PROTO-4: (845): Constructing IDi payload: '10.5.7.196' of type 'IPv4 address'
IKEv2-PROTO-4: (845): ESP Proposal: 1, SPI size: 4 (IPSec negotiation),
Num. transforms: 3
(845): AES-CBC(845): SHA96(845): Don't use ESNIKEv2-PROTO-7: Construct Notify Payload: INITIAL_CONTACTIKEv2-PROTO-7: Construct Notify Payload: ESP_TFC_NO_SUPPORTIKEv2-PROTO-7: Construct Notify Payload: NON_FIRST_FRAGSIKEv2-PROTO-4: (845): Building packet for encryption.
(845):
Payload contents:
(845): VID(845): Next payload: IDi, reserved: 0x0, length: 20
(845):
(845): 26 f7 33 12 b6 c5 08 de 1e cb 2a 0c 65 96 bd 9a
(845): IDi(845): Next payload: AUTH, reserved: 0x0, length: 12
(845): Id type: IPv4 address, Reserved: 0x0 0x0
(845):
(845): 0a 05 07 c4
(845): AUTH(845): Next payload: SA, reserved: 0x0, length: 40
(845): Auth method PSK, reserved: 0x0, reserved 0x0
(845): Auth data: 32 bytes
(845): SA(845): Next payload: TSi, reserved: 0x0, length: 44
(845): last proposal: 0x0, reserved: 0x0, length: 40
Proposal: 1, Protocol id: ESP, SPI size: 4, #trans: 3(845): last transform: 0x3, reserved: 0x0: length: 12
type: 1, reserved: 0x0, id: AES-CBC
(845): last transform: 0x3, reserved: 0x0: length: 8
type: 3, reserved: 0x0, id: SHA96
(845): last transform: 0x0, reserved: 0x0: length: 8
type: 5, reserved: 0x0, id: Don't use ESN
(845): TSi(845): Next payload: TSr, reserved: 0x0, length: 40
(845): Num of TSs: 2, reserved 0x0, reserved 0x0
(845): TS type: TS_IPV4_ADDR_RANGE, proto id: 0, length: 16
(845): start port: 0, end port: 65535
(845): start addr: 10.249.0.9, end addr: 10.249.0.9
(845): TS type: TS_IPV4_ADDR_RANGE, proto id: 0, length: 16
(845): start port: 0, end port: 65535
(845): start addr: 10.249.0.0, end addr: 10.249.1.255
(845): TSr(845): Next payload: NOTIFY, reserved: 0x0, length: 40
(845): Num of TSs: 2, reserved 0x0, reserved 0x0
(845): TS type: TS_IPV4_ADDR_RANGE, proto id: 0, length: 16
(845): start port: 0, end port: 65535
(845): start addr: 172.17.0.21, end addr: 172.17.0.21
(845): TS type: TS_IPV4_ADDR_RANGE, proto id: 0, length: 16
(845): start port: 0, end port: 65535
(845): start addr: 172.17.0.0, end addr: 172.17.0.255
(845): NOTIFY(INITIAL_CONTACT)(845): Next payload: NOTIFY, reserved: 0x0, length: 8
(845): Security protocol id: IKE, spi size: 0, type: INITIAL_CONTACT
(845): NOTIFY(ESP_TFC_NO_SUPPORT)(845): Next payload: NOTIFY, reserved: 0x0, length: 8
(845): Security protocol id: IKE, spi size: 0, type: ESP_TFC_NO_SUPPORT
(845): NOTIFY(NON_FIRST_FRAGS)(845): Next payload: NONE, reserved: 0x0, length: 8
(845): Security protocol id: IKE, spi size: 0, type: NON_FIRST_FRAGS
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_BLD_AUTH Event: EV_ENCRYPT_MSG
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_BLD_AUTH Event: EV_NO_EVENT
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_BLD_AUTH Event: EV_OK_ENCRYPT_RESP
IKEv2-PROTO-7: (845): Action: Action_Null
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_BLD_AUTH Event: EV_TRYSEND
(845):
IKEv2-PROTO-4: (845): Sending Packet [To 172.17.0.1:500/From 10.5.7.196:500/VRF i0:f0]
(845): Initiator SPI : 24F73212A5F2FB99 - Responder SPI : EE68310E6E6B1C24 Message id: 1
(845): IKEv2 IKE_AUTH Exchange REQUESTIKEv2-PROTO-5: (845): Next payload: ENCR, version: 2.0 (845): Exchange type: IKE_AUTH, flags: INITIATOR (845): Message id: 1, length: 288(845):
Payload contents:
(845): ENCR(845): Next payload: VID, reserved: 0x0, length: 260
(845): Encrypted data: 256 bytes
(845):
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_BLD_AUTH Event: EV_CHK_EAP_POST_ASYNC
IKEv2-PROTO-4: (845): Check for EAP exchange
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_WAIT_AUTH Event: EV_NO_EVENT
(845):
IKEv2-PROTO-4: (845): Received Packet [From 172.17.0.1:500/To 10.5.7.196:500/VRF i0:f0]
(845): Initiator SPI : 24F73212A5F2FB99 - Responder SPI : EE68310E6E6B1C24 Message id: 1
(845): IKEv2 IKE_AUTH Exchange RESPONSEIKEv2-PROTO-5: (845): Next payload: ENCR, version: 2.0 (845): Exchange type: IKE_AUTH, flags: RESPONDER MSG-RESPONSE (845): Message id: 1, length: 256(845):
Payload contents:
IKEv2-PROTO-4: decrypt queued(845):
(845): Decrypted packet:(845): Data: 256 bytes
(845): REAL Decrypted packet:(845): Data: 180 bytes
IKEv2-PROTO-7: Parse Vendor Specific Payload: (CUSTOM) VID Next payload: IDr, reserved: 0x0, length: 20
ec 68 30 0e 7d 5c ef 63 1e cb 2a 0c 65 96 bd 9a
IDr Next payload: AUTH, reserved: 0x0, length: 12
Id type: IPv4 address, Reserved: 0x0 0x0
42 ea 6a 02
AUTH Next payload: SA, reserved: 0x0, length: 40
Auth method PSK, reserved: 0x0, reserved 0x0
Auth data: 32 bytes
SA Next payload: TSi, reserved: 0x0, length: 44
last proposal: 0x0, reserved: 0x0, length: 40
Proposal: 1, Protocol id: ESP, SPI size: 4, #trans: 3 last transform: 0x3, reserved: 0x0: length: 12
type: 1, reserved: 0x0, id: AES-CBC
last transform: 0x3, reserved: 0x0: length: 8
type: 3, reserved: 0x0, id: SHA96
last transform: 0x0, reserved: 0x0: length: 8
type: 5, reserved: 0x0, id: Don't use ESN
TSi Next payload: TSr, reserved: 0x0, length: 24
Num of TSs: 1, reserved 0x0, reserved 0x0
TS type: TS_IPV4_ADDR_RANGE, proto id: 0, length: 16
start port: 0, end port: 65535
start addr: 10.249.0.0, end addr: 10.249.1.255
TSr Next payload: NOTIFY, reserved: 0x0, length: 24
Num of TSs: 1, reserved 0x0, reserved 0x0
TS type: TS_IPV4_ADDR_RANGE, proto id: 0, length: 16
start port: 0, end port: 65535
start addr: 172.17.0.0, end addr: 172.17.0.255
IKEv2-PROTO-7: Parse Notify Payload: ESP_TFC_NO_SUPPORT NOTIFY(ESP_TFC_NO_SUPPORT) Next payload: NOTIFY, reserved: 0x0, length: 8
Security protocol id: IKE, spi size: 0, type: ESP_TFC_NO_SUPPORT
IKEv2-PROTO-7: Parse Notify Payload: NON_FIRST_FRAGS NOTIFY(NON_FIRST_FRAGS) Next payload: NONE, reserved: 0x0, length: 8
Security protocol id: IKE, spi size: 0, type: NON_FIRST_FRAGS
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_WAIT_AUTH Event: EV_RECV_AUTH
IKEv2-PROTO-7: (845): Action: Action_Null
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK4_NOTIFY
IKEv2-PROTO-4: (845): Process auth response notify
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_PROC_MSG
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK_IF_PEER_CERT_NEEDS_TO_BE_FETCHED_FOR_PROF_SEL
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_GET_POLICY_BY_PEERID
IKEv2-PROTO-4: (845): Searching policy based on peer's identity '172.17.0.1' of type 'IPv4 address'
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_VERIFY_POLICY_BY_PEERID
IKEv2-PROTO-4: (845): Verify peer's policy
IKEv2-PROTO-4: (845): Peer's policy verified
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK_AUTH_TYPE
IKEv2-PROTO-4: (845): Get peer's authentication method
IKEv2-PROTO-4: (845): Peer's authentication method is 'PSK'
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_GET_PRESHR_KEY
IKEv2-PROTO-4: (845): Get peer's preshared key for 172.17.0.1
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_VERIFY_AUTH
IKEv2-PROTO-4: (845): Verify peer's authentication data
IKEv2-PROTO-4: (845): Use preshared key for id 172.17.0.1, key len 9
IKEv2-PROTO-4: (845): Verification of peer's authenctication data PASSED
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK_EAP
IKEv2-PROTO-4: (845): Check for EAP exchange
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_NOTIFY_AUTH_DONE
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK_CONFIG_MODE
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK4_IC
IKEv2-PROTO-4: (845): Processing INITIAL_CONTACT
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_CHK_IKE_ONLY
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: I_PROC_AUTH Event: EV_PROC_SA_TS
IKEv2-PROTO-4: (845): Processing IKE_AUTH message
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_OK
IKEv2-PROTO-7: (845): Action: Action_Null
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_UPDATE_CAC_STATS
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_INSERT_IKE
IKEv2-PROTO-4: (845): IKEV2 SA created; inserting SA into database. SA lifetime timer (28800 sec) started
IKEv2-PROTO-4: (845): Session with IKE ID PAIR (172.17.0.1, 10.5.7.196) is UP
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_REGISTER_SESSION
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_NO_EVENT
IKEv2-PROTO-4: (845): Initializing DPD, configured for 10 seconds
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_RECD_REGISTER_SESSION_RESP
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_GEN_LOAD_IPSEC
IKEv2-PROTO-4: (845): Load IPSEC key material
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_NO_EVENT
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_OK_RECD_LOAD_IPSEC
IKEv2-PROTO-7: (845): Action: Action_Null
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_START_ACCT
IKEv2-PROTO-4: (845): DPD timer started for 10 secs
IKEv2-PROTO-7: (845): Accounting not required
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_PARENT_NEG_COMPLETE
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_PKI_SESH_CLOSE
IKEv2-PROTO-7: (845): Closing the PKI session
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_CHECK_DUPE
IKEv2-PROTO-4: (845): Checking for duplicate IKEv2 SA
IKEv2-PROTO-4: (845): No duplicate IKEv2 SA found
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: AUTH_DONE Event: EV_CHK4_ROLE
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: READY Event: EV_CHK_IKE_ONLY
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: READY Event: EV_I_OK
IKEv2-PROTO-7: (845): Deleting negotiation context for my message ID: 0x1
IKEv2-PROTO-7: (845): Request has mess_id 0; expected 0 through 0
(845):
IKEv2-PROTO-4: (845): Received Packet [From 172.17.0.1:500/To 10.5.7.196:500/VRF i0:f0]
(845): Initiator SPI : 24F73212A5F2FB99 - Responder SPI : EE68310E6E6B1C24 Message id: 0
(845): IKEv2 INFORMATIONAL Exchange REQUESTIKEv2-PROTO-5: (845): Next payload: ENCR, version: 2.0 (845): Exchange type: INFORMATIONAL, flags: RESPONDER (845): Message id: 0, length: 80(845):
Payload contents:
IKEv2-PROTO-4: decrypt queued(845):
(845): Decrypted packet:(845): Data: 80 bytes
(845): REAL Decrypted packet:(845): Data: 12 bytes
DELETE Next payload: NONE, reserved: 0x0, length: 12
Security protocol id: ESP, spi size: 4, num of spi: 1
f8 74 5a a1
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000000 CurState: READY Event: EV_RECV_INFO_REQ
IKEv2-PROTO-7: (845): Action: Action_Null
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000000 CurState: INFO_R Event: EV_RECV_INFO_REQ
IKEv2-PROTO-4: (845): Building packet for encryption.
(845):
Payload contents:
(845): DELETE(845): Next payload: NONE, reserved: 0x0, length: 12
(845): Security protocol id: ESP, spi size: 4, num of spi: 1
(845):
(845): 34 63 73 32
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000000 CurState: INFO_R Event: EV_ENCRYPT_MSG
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000000 CurState: INFO_R Event: EV_NO_EVENT
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000000 CurState: INFO_R Event: EV_OK_ENCRYPT_RESP
IKEv2-PROTO-7: (845): Action: Action_Null
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000000 CurState: INFO_R Event: EV_TRYSEND
(845):
IKEv2-PROTO-4: (845): Sending Packet [To 172.17.0.1:500/From 10.5.7.196:500/VRF i0:f0]
(845): Initiator SPI : 24F73212A5F2FB99 - Responder SPI : EE68310E6E6B1C24 Message id: 0
(845): IKEv2 INFORMATIONAL Exchange RESPONSEIKEv2-PROTO-5: (845): Next payload: ENCR, version: 2.0 (845): Exchange type: INFORMATIONAL, flags: INITIATOR MSG-RESPONSE (845): Message id: 0, length: 80(845):
Payload contents:
(845): ENCR(845): Next payload: DELETE, reserved: 0x0, length: 52
(845): Encrypted data: 48 bytes
(845):
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000000 CurState: INFO_R Event: EV_CHK_INFO_TYPE
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000000 CurState: INFO_R Event: EV_RECV_DEL
IKEv2-PROTO-4: (845): Process delete request from peer
IKEv2-PROTO-4: (845): Processing DELETE INFO message for IPsec SA [SPI: 0xF8745AA1]
IKEv2-PROTO-7: Removing child SA with spi A15A74F8
IKEv2-PROTO-7: Successfully removed child SAs
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000000 CurState: INFO_R Event: EV_CHK4_ACTIVE_SA
IKEv2-PROTO-4: (845): Check for existing active SA
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000000 CurState: INFO_R Event: EV_START_DEL_NEG_TMR
IKEv2-PROTO-7: (845): Action: Action_Null
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000000 CurState: EXIT Event: EV_CHK_PENDING
IKEv2-PROTO-7: (845): Sent response with message id 0, Requests can be accepted from range 1 to 1
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000000 CurState: EXIT Event: EV_NO_EVENT
IKEv2-PROTO-7: (845): Request has mess_id 1; expected 1 through 1
(845):
IKEv2-PROTO-4: (845): Received Packet [From 172.17.0.1:500/To 10.5.7.196:500/VRF i0:f0]
(845): Initiator SPI : 24F73212A5F2FB99 - Responder SPI : EE68310E6E6B1C24 Message id: 1
(845): IKEv2 INFORMATIONAL Exchange REQUESTIKEv2-PROTO-5: (845): Next payload: ENCR, version: 2.0 (845): Exchange type: INFORMATIONAL, flags: RESPONDER (845): Message id: 1, length: 80(845):
Payload contents:
IKEv2-PROTO-4: decrypt queued(845):
(845): Decrypted packet:(845): Data: 80 bytes
(845): REAL Decrypted packet:(845): Data: 8 bytes
DELETE Next payload: NONE, reserved: 0x0, length: 8
Security protocol id: IKE, spi size: 0, num of spi: 0
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: READY Event: EV_RECV_INFO_REQ
IKEv2-PROTO-7: (845): Action: Action_Null
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: INFO_R Event: EV_RECV_INFO_REQ
IKEv2-PROTO-4: (845): Building packet for encryption.
(845):
Payload contents:
(845): DELETE(845): Next payload: NONE, reserved: 0x0, length: 8
(845): Security protocol id: IKE, spi size: 0, num of spi: 0
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: INFO_R Event: EV_ENCRYPT_MSG
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: INFO_R Event: EV_NO_EVENT
IKEv2-PROTO-7: (845): Locked SA.Event EV_FREE_NEG queued in the state EXIT
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: INFO_R Event: EV_OK_ENCRYPT_RESP
IKEv2-PROTO-7: (845): Action: Action_Null
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: INFO_R Event: EV_TRYSEND
(845):
IKEv2-PROTO-4: (845): Sending Packet [To 172.17.0.1:500/From 10.5.7.196:500/VRF i0:f0]
(845): Initiator SPI : 24F73212A5F2FB99 - Responder SPI : EE68310E6E6B1C24 Message id: 1
(845): IKEv2 INFORMATIONAL Exchange RESPONSEIKEv2-PROTO-5: (845): Next payload: ENCR, version: 2.0 (845): Exchange type: INFORMATIONAL, flags: INITIATOR MSG-RESPONSE (845): Message id: 1, length: 80(845):
Payload contents:
(845): ENCR(845): Next payload: DELETE, reserved: 0x0, length: 52
(845): Encrypted data: 48 bytes
(845):
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: INFO_R Event: EV_CHK_INFO_TYPE
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: INFO_R Event: EV_RECV_DEL
IKEv2-PROTO-4: (845): Process delete request from peer
IKEv2-PROTO-4: (845): Processing DELETE INFO message for IKEv2 SA [ISPI: 0x24F73212A5F2FB99 RSPI: 0xEE68310E6E6B1C24]
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: INFO_R Event: EV_CHK4_ACTIVE_SA
IKEv2-PROTO-4: (845): Check for existing active SA
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: INFO_R Event: EV_STOP_ACCT
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: INFO_R Event: EV_IPSEC_DEL
IKEv2-PROTO-4: (845): Delete all IKE SAs
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: INFO_R Event: EV_START_DEL_NEG_TMR
IKEv2-PROTO-7: (845): Action: Action_Null
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: EXIT Event: EV_CHK_PENDING
IKEv2-PROTO-7: (845): Sent response with message id 1, Requests can be accepted from range 2 to 2
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000001 CurState: EXIT Event: EV_NO_EVENT
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (R) MsgID = 00000000 CurState: EXIT Event: EV_FREE_NEG
IKEv2-PROTO-7: (845): Deleting negotiation context for peer message ID: 0x0
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: READY Event: EV_RECV_DEL
IKEv2-PROTO-7: (845): SM Trace-> SA: I_SPI=24F73212A5F2FB99 R_SPI=EE68310E6E6B1C24 (I) MsgID = 00000001 CurState: DELETE Event: EV_FREE_SA
IKEv2-PROTO-4: (845): Deleting SA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2020 08:36 PM
I figured out my issue after looking at debugs on the onsite ASA. It was a configuration issue on that ASA. I needed to tell my tunnel-group on the ASA onsite to use ikev2 with a policy. I'm guessing this is required in software release 9.1 because the ASAv didn't need the policy and it is running 9.14
group-policy GroupPolicy_x.x.x.x internal
group-policy GroupPolicy_x.x.x.x attributes
vpn-tunnel-protocol ikev2
!
tunnel-group x.x.x.x type ipsec-l2l
tunnel-group x.x.x.x general-attributes
default-group-policy GroupPolicy_x.x.x.x
tunnel-group x.x.x.x ipsec-attributes
ikev2 remote-authentication pre-shared-key *****
ikev2 local-authentication pre-shared-key *****
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide