- Cisco Community
- Technology and Support
- Security
- VPN
- Routing between VRF and GRT to Core Layer. Dual-Hub Dual-ISP
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Routing between VRF and GRT to Core Layer. Dual-Hub Dual-ISP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-26-2010 02:11 AM
Hello All,
I'm having issues in routing from vrf to grt ( global routing table ) to the core router and vice versa.
Here's a quick overview of my setup:
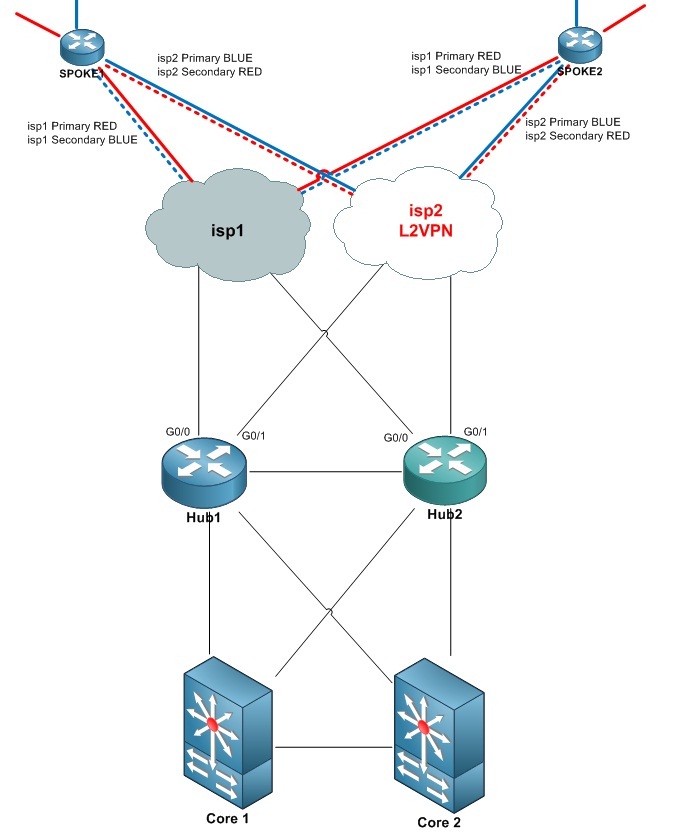
HUB1: Primary for RED
HUB2: Primary for BLUE
iVRF: RED and BLUE
fVRF: ISP1 and ISP2
RED: 10.100.x.x/24
BLUE: 10.105.x.x/24
ISP1: 100.0.0.x/24
ISP2: 200.0.0.x/24
Tunnels: 192.168.x.x/24
Hub to Core: 10.250.250.0/24
T0: 192.168.100.1 tunnel vrf isp1 - RED
T1: 192.168.101.1 tunnel vrf isp1 - BLUE
T2: 192.168.200.1 tunnel vrf isp2 - RED
T3: 192.168.201.1 tunnel vrf isp2 - BLUE
2 Tunnels always remain shutdown at the spokes, but whenever the connections fails at one of the ISP's, the spoke automatically shuts down the corresponding tunnel and brings up the Backup tunnel which registers through ISP2, but at the Hub1.
My setup is in the following order:
What I want to achieve is, I want to be able to access the VRF's from my core router, without involving anymore VRF's down the core layer.I want to terminate the VRF at the Hub's, and continue with normal routing below the Hub's without having too much routes on my Core routers , I want to advertise a summary route from the Hub's down to my Core routers ( Each Hub will advertise 2 Routers, for example Hub1 will advertise 10.100.x.x as its primary route, and possible 10.105.x.x as a secondary route , in the case if Hub2 fails ).
The only way to achieve this , it seems that the Spokes, Hub and the Core router need to know about each other in their GRT, otherwise it won't route.
I tried Route leaking from VRF to GRT, but it didn't go as expected.
I could easily redistribute static routes for my Tunnel interfaces to my core layer, and my core routers would always be able to access the Tunnel interfaces, because they all reside in a different Subnet, and they are static and never change their way, but as for RED and BLUE, if one ISP goes down at the spoke, the Spoke would switch to the other Tunnel, and the Hub would still be routing through the old tunnel because it doesn't know the spoke changed his way.That is for static route distributing to the core ,its too dynamic to go with static routes.
Here's a link to an example of what i'm doing, with a few changes:
http://eminent-ccie.blogspot.com/2010/06/vrf-aware-dmvpn-with-dual-isp.html
Attached you will find the configuration of Hub1 , which is primary for RED, and the configuration of Spoke1.
Thanks
- Labels:
-
VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-29-2010 04:58 AM
Does anyone have any suggestion as to what is best for this solution?
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide