- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- Network EAP vs Open Authentication with EAP in Autonomous AP's
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
03-26-2012 04:53 AM - edited 11-18-2020 02:58 AM
Introduction
In this document, we will discuss various aspects about Autonomous AP's and comparision between Network EAP vs Open Authentication with EAP and finding the right combination.
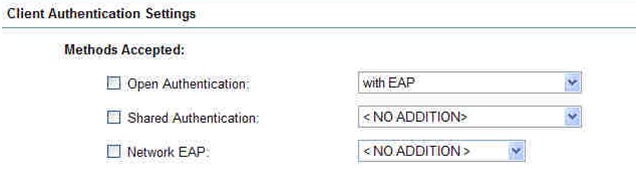
When configuring an SSID with EAP/802.1X on an autonomous AP, we are given the choice between Network EAP and Open Authentication with EAP (or both).
On the CLI, we would say
dot11 ssid whatever
authentication open eap eap_methods
authentication network-eap eap_methods
In configuration guide it is not completely clear, here is a quick summary of which one to choose and when.
Background information
All this started at the time when we had "nothing (Authentication set to 0 in the AP beacons)" or WEP PSK (Authentication set to 1 in the AP beacons). WEP was weak, so everybody needed a replacement for it. When LEAP implemented , which implies both authentication mechanism and some encryption. The Authentication value was set to 1 in the AP beacons using LEAP, not to indicate PSK but to indicate "authentication required" (and this is also why you cannot use LEAP with no encryption). But this does not really conform to the (future, when LEAP was created) 802.11i (and WPA) specifications, so this is specific.
Later on, when WPA and 802.11i appeared, the protocol detailed that, for compatibility with the 802.1X protocol, the authentication would occur at the association phase. In other words, with 802.1X you plug your PC to a switch, and it is only when you do that that authentication occurs. Similarly in the wireless space, you go through the 802.11 authentication phase (request/response) in an open manner, and it is only when you go to the association phase, which is the "hey, plug me to your cell" message, that the AP says "wait, I need to do 802.1X authentication first", and the EAP process starts. So, Authentication is set to 0 (for its 802.11 part), and EAP/802.1X starts at the association phase. When Cisco replaced LEAP with EAP-FAST Authentication is set to 0.
So it seems that Network EAP = LEAP and Open authentication with EAP = Any other EAP. This is something we see when checking Network EAP: the popup window clearly states that if we use EAP-FAST or any other EAP (than LEAP), we should check Open with EAP. We can of course check both when we want to allow LEAP and another EAP, but we will not be able to authenticate using EAP-FAST if we choose Network EAP only.
There is one exception though. for long, LEAP used to be the default "secure" authentication method. This makes that some old clients (for example access points!) need to be offered LEAP to get started (or turned on, name it the way you like). In other words, if we build a wireless link between 2 APs, for a repeater, bridge or Workgroup Bridge configuration, and if we use 802.1X on that link, we need to offer LEAP (i.e Network EAP) for the secure authentication to be used. So we can offer Network EAP, or Network EAP and Open with EAP, but we should not offer just Open with EAP.
Which one is going to be used if we offer both? Well, it all depends on how we configure our client side (non root Bridge, Workgroup Bridge, etc). If we use the "old" EAP Client (optional feature), in the SSID page:

Which is in the CLI:
dot11 ssid whatever
authentication client username Test password 7 104D000A0618
This is going to use LEAP only. If we want to use another EAP, for example EAP-FAST, we need to empty that EAP Client field (it cannot be used in combination with another method), then use the AP Authentication feature.
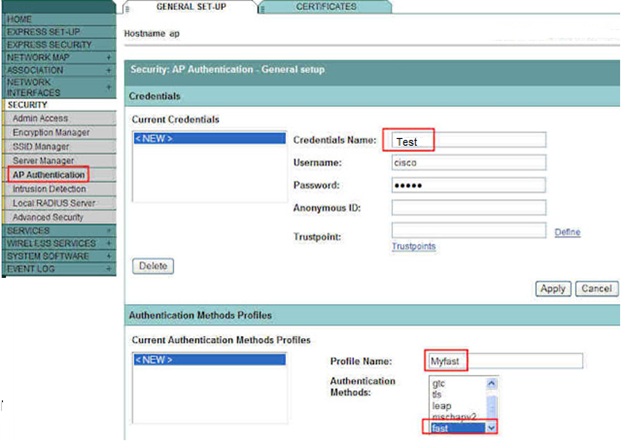
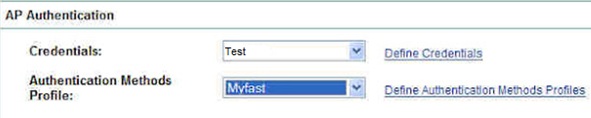
In this page, we define credentials and method. We can pick up several methods if we want. Then from the SSID page, we can call these methods:
In the CLI, this is:
dot11 ssid whatever
dot1x credentials Test
dot1x eap profile Myfast
exit
eap profile Myfast
method fast
dot1x credentials test
username cisco
password cisco
So we offer both LEAP and Open with EAP, and using the newer AP Authentication method allows us to use the credentials we defined, and use the most secure method selected. In this example, we use EAP FAST only, so that's the one we'll use. Of course, the RADIUS to which you main AP points (local RADIUS on the main APor external RADIUS) needs to allow that method.
Careful when testing, it is only from the non-root AP / WGB / repeater CLI that we will use, at authentication time, which method was used. The main AP CLI will just tell us "WPA", or "Open", etc., but not the details of the authentication method used.
If we offer just Open with EAP, as the AP expects LEAP (Network LEAP) among the possibilities, then the EAP part is discarded. Although our link may come up, if we look carefully at our non-root AP CLI, we will see that the authentication is going to be "Open" (NOT with EAP), so there is no real authentication there. As soon as we also offer Network EAP, the non-root AP is happy, being offered LEAP, btu also something stronger, and is going to use the stronger method (EAP-FAST in our example)
Reference
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: