- Cisco Community
- Technology and Support
- Wireless - Mobility
- Wireless - Mobility Knowledge Base
- FlexConnect Split Tunneling
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
10-31-2012 01:25 AM - edited 11-18-2020 03:00 AM
- Split Tunneling - Introduction
- Supported Access Points:
- Configuration (CLI):
- More Information
- Introduction -Release 7.5
- The Packet Flow Process
- Useful Link
Split Tunneling - Introduction
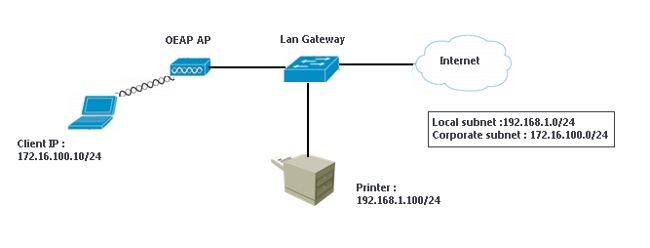
When a client is connected over a WAN link associated with a centrally switched WLAN wants to send some data to a device in local site, then the client has to send the traffic over CAPWAP to the controller and then get the same data back to the local site over CAPWAP. This consumes WAN link bandwidth as the same data is send and received. This can be avoided to utilize the WAN bandwidth efficiently.
FlexConnect Split tunneling feature helps avoid such scenario by classifying the data send by the client based on the packet contents using FlexConnect ACL. The matching packets are locally switched and the rest of the traffic is centrally switched. The traffic that is sent by the client that matches the IP address of the device present in the local site can be classified as locally switched traffic and the rest of the traffic as centrally switched.
FlexConnect ACL feature allows to create a filter that can be applied on FlexConnect AP for protection of locally switched data traffic from the AP.
FlexConnect ACLs are created on the WLC and then be configured with the VLAN present on the FlexConnect AP.
Supported Access Points:
Split Tunneling supported on the AP1040, AP1140, AP1260, AP2600, AP3500, and AP3600 access points.
Split tunneling is not supported on Cisco 1500 Series, Cisco 1130, and Cisco 1240 access points.
Configuration (CLI):
To configure split tunneling on a per-AP basis, enter this command:
config ap local-split enable wlan-id acl acl-name ap-name
To creates an ACL on a FlexConnect access point:
config flexconnect acl create name
To add an ACL rule:
config flexconnect acl rule add acl-name rule-index
To Apply the ACL to the FlexConnect AP:
config flexconnect acl apply acl-name
According to Release Notes of Cisco Wireless LAN Controllers and Lightweight Access Points for Release 7.5.102.0:
You can configure split tunneling for the Cisco OEAP to enable or disable local printer access. You can enable or disable split tunneling on a per WLAN or per remote LAN basis, or you can enable or disable split tunneling globally on the Cisco OEAP themselves.
More Information
Introduction - Release 7.5
The split tunnel access-points, with the controller code Release 7.5, allow clients (that connect to the corporate SSID) to connect to the corporate resources and access local resources simultaneously. It is available for clients that connect through the corporate SSID and the remote LAN. This feature presently supports the split tunneling for printers with the common printer ports such as PDL (port:9100), IPP (port:631), MFP (port: 9303), LPR (port:515), PSUS4 (port:34443), and Generic printer server (port:35).
The Packet Flow Process
1. AP inspects the traffic sent by the client to the corporate network for the well-known printers.
2. When the client is configured with a gateway, it sends all packets to the destination MAC address of the gateway. In this case, when the client is connected to the corporate SSID with the destination MAC address of the gateway, the SSID tries to connect to the printer 192.168.1.100.
3. The AP finds a match for the printer port and sends out an Address Resolution Protocol (ARP) request on the local network for the destination IP address of the printer.
4. When it receives a reply, it changes the destination of the MAC address. It changes from the gateway's MAC address to the printer's MAC address and forwards it to the local network.
5. The AP bridges back the reply traffic from the printer to the client.
Useful Link
Reference:
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks for this great document
Would you be able to do a config example of how to enable this feature on OEAP600 ? WLC 7.5.x code introduced this feature to that AP model. I am find it hard to go through all the steps required to get it working.
I posted it in support forum as well, but no responses so far
https://supportforums.cisco.com/thread/2238105
Rasika
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Great explaination thank you.
Do you know if this feature is supported on 3800 series APs?
regards
John
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Do you know if this feature is supported with AAA-override/radius return local-split acl and vlan-id/name?
Because of Flexconnect vlan based central switching does not support macfilter, I am looking for alternative approach.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Supported in Wave 2 APs (1800,2800,3800,4800) from version 8.8.100 🙂
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks for the heads up on version 8.8.100 - looks like I need to upgrade now to get my 3800's working!! 🙂
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community:



