- Cisco Community
- Technology and Support
- Wireless - Mobility
- Wireless
- Re: ISE - WLC - PEAP Authentication with Certificate
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-08-2019 08:27 AM - edited 07-05-2021 10:40 AM
Hello Folks,
I have a SSID with 802.1x PEAP as authentication metod, i want to know if there is some way or configuration on ISE to ask for the certificate on the client side. I want to configure that if you do not have the option to verify the certificate, you can not connect to the Wireless network. Is that possible on the WLC or ISE?
My Ise configurations:
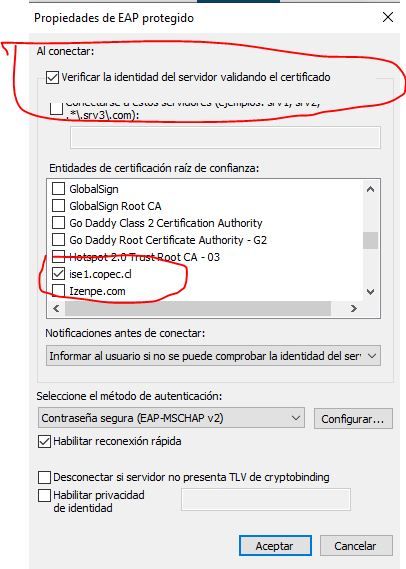
The option on Windows is:
Solved! Go to Solution.
- Labels:
-
Wireless LAN Controller
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-10-2019 02:37 PM
Hi
Oh right. If you have given users, who are external to the organisation, domain accounts, then there is the option of putting them in a separate AD Security Group that ISE can check on during Authorization. But anyway, there still is no client cert involved - the clients are the ones who should be concerned with checking the ISE cert. They can choose to ignore the checks and then potentially be fooled by a man in the middle. If you cannot control the client side (ensuring that they tick the right security check box to trust ISE) then you cannot guarantee that they will only ever talk to your ISE server.
If you want to restrict access to the network, then use AD Security Groups.
Some customers go one step further and create a separate BYOD SSID - but if this is also 802.1X then it doesn't achieve much. You can place a user into any VLAN you like and apply ACLs on per user basis, based on what ISE is configured to do.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-08-2019 08:36 PM
Hi @rponte ,
Please refer the link Configure 802.1x Authentication with PEAP, ISE 2.1 and WLC 8.3
HTH
Sathiyanarayanan Ravindran
Please rate the post and accept as solution, if my response satisfied your question:)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-09-2019 05:10 AM
Hello, thank you for you update. I configured it like it but if the client does not have the certificate he can connect to the network anyways.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-09-2019 06:05 AM
Hi @rponte ,
ISE or WLC will not ask for machine to send the certificate. This has to be done by the endpoint, Do you want to have a fall back like Password or Certificate based Authentication for your WiFi clients?
Sathiyanarayanan Ravindran
Please rate the post and accept as solution, if my response satisfied your question:)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-09-2019 07:08 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-09-2019 03:05 PM
Hi @rponte
I think there is some confusion here - or a confusion about what you expect to happen, and how EAP-PEAP works. PEAP (to use its short name) does not involve a certificate on the client side (the "supplicant"). That is EAP-TLS. With PEAP the supplicant establishes a TLS tunnel from itself to the RADIUS server to exchange a login credential. The login credential is typically a username/password. But getting back to the PEAP tunnel establishment ... there are many steps to this dance, and one of the important moves is for the RADIUS server to identify itself to the supplicant by sending over the RADIUS Server certificate to the supplicant. The supplicant analyses that cert to see whether it can be trusted (Android doesn't care, but iOS/Windows etc do the right thing by performing this check - yes, it can be disabled too, but that is stupidity - why bother then ...?). But the main point is that the client/supplicant NEVER sends a certificate to the RADIUS server.
When configuring the client side (the "supplicant") you can only perform one EAP method at the same time - you must choose EAP-PEAP, or EAP-TLS - you cannot do both at the same time.
The RADIUS server can support multiple EAP methods and it will keep offering alternatives as long as the supplicant is happy to proceed in that way (it will NAK until the RADIUS server offers him an EAP method that he likes - if not, then EAP will fail).
I hope that helps. Please click on the helpful button if this solved your question ;-)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-10-2019 05:29 AM
Hi @Arne Bier , thank you for you reply.
Now i understand the process better. The problem is that we have a wireless network where external suppliers without laptops on the domain connect with domain accounts, I need to restrict access to the network unless you have that option enabled to trust on the cert in order to avoid main on the middle attacks because we have not control on the external laptops.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-10-2019 02:37 PM
Hi
Oh right. If you have given users, who are external to the organisation, domain accounts, then there is the option of putting them in a separate AD Security Group that ISE can check on during Authorization. But anyway, there still is no client cert involved - the clients are the ones who should be concerned with checking the ISE cert. They can choose to ignore the checks and then potentially be fooled by a man in the middle. If you cannot control the client side (ensuring that they tick the right security check box to trust ISE) then you cannot guarantee that they will only ever talk to your ISE server.
If you want to restrict access to the network, then use AD Security Groups.
Some customers go one step further and create a separate BYOD SSID - but if this is also 802.1X then it doesn't achieve much. You can place a user into any VLAN you like and apply ACLs on per user basis, based on what ISE is configured to do.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-11-2019 05:16 AM
Totally right. Thank you for your help @Arne Bier .
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide