- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Add New MAC Address for MAB on Identity Groups
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2018 08:03 PM
Hi Guys,
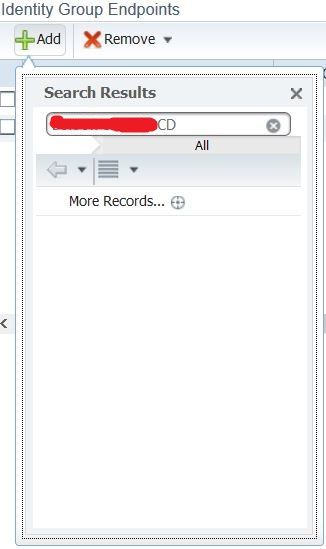
I want to add new MAC address to Endpoint Identity Groups to my ISE, so my IP phone can bypass dot1x authentication process via MAB. The thing is, I was unable to add the new MAC address since it is not on the available list, even though the IP phone is already connected to the network for more than 1 month. And I could not find a way to add that MAC address to the list. Below is the exhibit of what I found.
Is there any way I can add MAC address so it can be found on the list?
I found a workaround by connecting the IP phone to a port where dot1x is active. This way, the MAC can be found on the list because it was challenged for authentication. But I find it is not practical since I have hundreds of IP phone to be registered.
Thank you.
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2018 09:37 PM
Yes it is possible: go to context visibility -endpoints and paste the mac address . It must be there ,than edit and choose the group you want to add. Than in live logs you can see it is successful authenticated via mab
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2018 08:24 PM - edited 10-15-2018 08:29 PM
You can manually import device mac addresses in to the context visibility database and assign them to a static whitelist, but I think you might be going about this the hard way.
You mention that the device does not show up in ISE until you plug it in to a port with dot1x enabled. Your phones should be connected to switchports that have dot1x and mab enabled. This way when the phone is powered on, the switch attempts dot1x, it fails, you then authenticate the device via MAB. If you have the available licensing (plus), then IP phones are ideal candidates for profiling. ISE learns that the devices is an IP phone, it authenticates it via MAB, and then authorizes it in to the voice vlan against a policy set rule for phones.
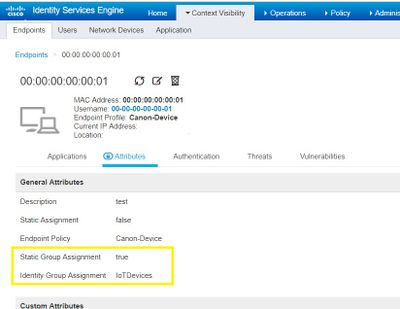
If you are plugging your phones in to ports without authentication enabled you don't need to authenticate them, I suspect you do want to authenticate them which has me questioning what's going on with your config. You do not add endpoint mac addresses within the window you linked, you create custom identify groups there, you modify an endpoint's membership from the context visibility endpoint database here.
https://yourise.server.com/admin/#context_dir/context_dir_devices
You map the identity groups within your mab authentication policy set rules. Add the device to the group either via profiling or statically like in the screenshot below.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2018 09:55 PM
Hi Damien,
I have a plan to deploy dot1x authentication on my wired connection, so only laptops with my company's certificate can connect to LAN. But, we have some IP phones and video conference devices that do not have such certificate, and a workaround is a must. My understanding was, if I add those MAC addresses to the endpoint identity groups, the MAB will "authenticate" them. And the extra port on the IP phone can authenticate end devices with my company's certificate.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2018 09:37 PM
Hi,again . What kind of IP phones you have in your deployment??If they are Cisco Phones you can authenticate them with Dot1x
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2018 09:37 PM
Yes it is possible: go to context visibility -endpoints and paste the mac address . It must be there ,than edit and choose the group you want to add. Than in live logs you can see it is successful authenticated via mab
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2018 09:47 PM
Hi Ognyan,
This is exactly what I've been looking for the past few days. Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-14-2019 09:10 PM
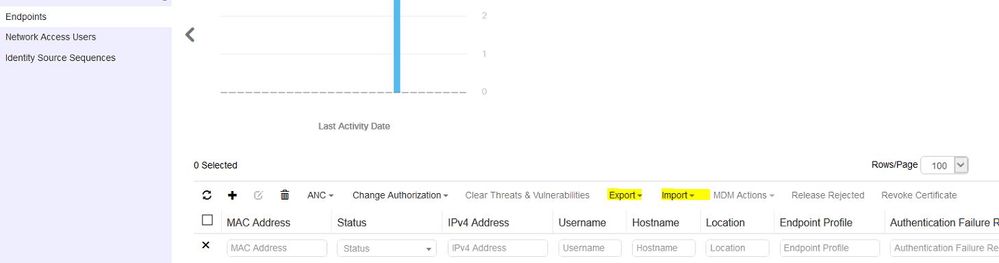
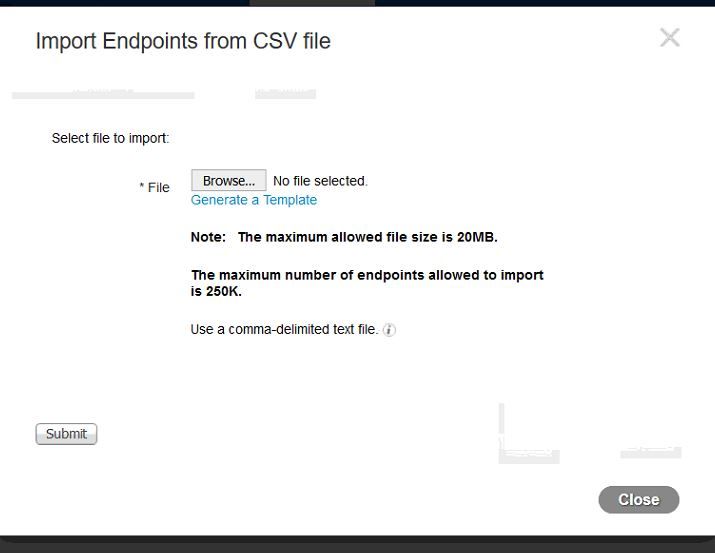
You can bulk import using the template:
WorkCentre > Network Access > Identities > Endpoints.
Add one mac address to the database and then export it to see the format or when you do import endpoints from CSV, you can generate the template and add MAC addresses and other details in 1 go.(Screenshots attached)
Hope that helps.
TA
Ab
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2019 01:54 AM
Hi,
I am trying to ADD new MAC address into Identity group
May i know if import using the template, wht are the fields that shld ONLY fill in? I am thinking of MACaddress and IdentityGroupAssignment only.
Will the ISE later change the device PolicyAssignment to Avaya-Device(this is the one detected by default if not added manually)? Does this really matter?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-03-2019 05:13 PM
Hi @getaway51
The fields that you require are as below:
| MACAddress | IdentityGroup | Description | User-Name | StaticAssignment | StaticGroupAssignment |
| xx:xx:xx:xx:xx:xx | Your_MAB_ID_Group | Optional | Mac-address | FALSE | TRUE |
Description is optional however as a good practice to fill it for user identification (like if static IP assignment, or location of connection, serial number etc).
In the MAC address/Username, you can enter the MAC address without the formatting as well.
Like: xxxxxxxxxx or xx-xx-xx-xx-xx-xx or xx:xx:xx:xx:xx:xx, but I always prefer to use the : as a delimiter.
Hope that helps.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide