- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Re: dACL in ISE
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-24-2016 10:25 AM
Hi team,
I'd like to know how dACL works in ISE and logon script.
I mean,for example user x needs to access file server (x.x.x.2 ) but in the first stage of cisco ise (machine authentication) X.X.X.2 isn’t permitted in the DACL so when the login script is applied this folder can't be access and it was hidden from shared folder in the my computer. So what is the solution to see those folders ? ( delay in the script or permit access in all stage of cisco ise )
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-24-2016 01:17 PM
There is an excellent session on 802.1X available from ciscolive.com which covers the details of machine and user authentication and sequence of events (BRKSEC-3005).
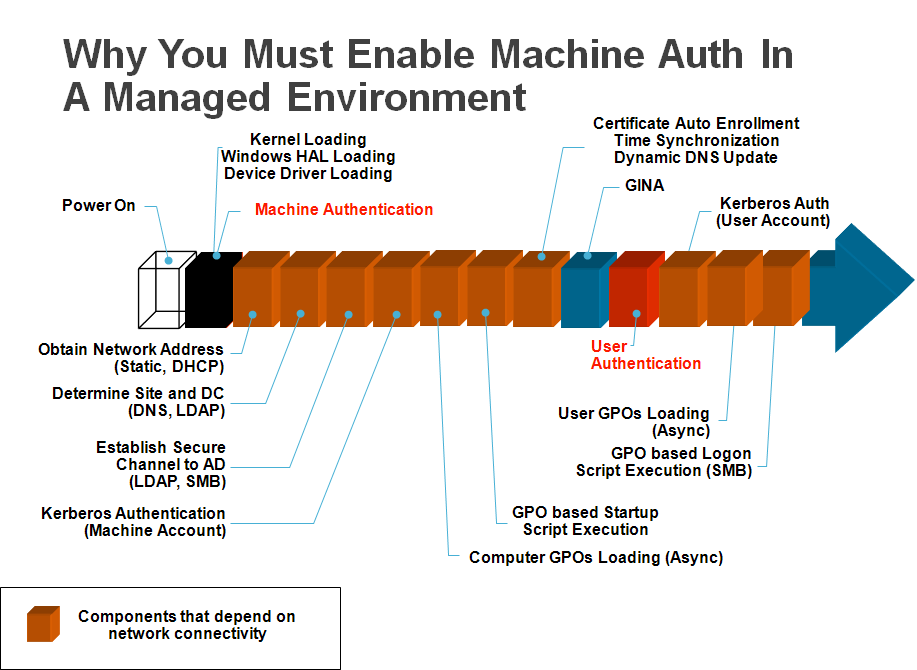
802.1X Machine auth will happen first at Layer 2 and using RADIUS to pass machine auth credentials to ISE and then validated to AD server. The Windows client does not require access to any file server or AD until after machine auth. It doesn't even have an IP yet! The network access device will authorize machine via RADIUS. At this point, ISE can return a dACL or other permission which allows DHCP, DNS, and access to the AD domain controller to the endpoint for user login. After user login, then full access can be given to client. If machine auth is not used, then it may be necessary to place port into Low Impact mode where DHCP, DNS, and AD access are granted prior to user auth.
/Craig
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-24-2016 01:17 PM
There is an excellent session on 802.1X available from ciscolive.com which covers the details of machine and user authentication and sequence of events (BRKSEC-3005).
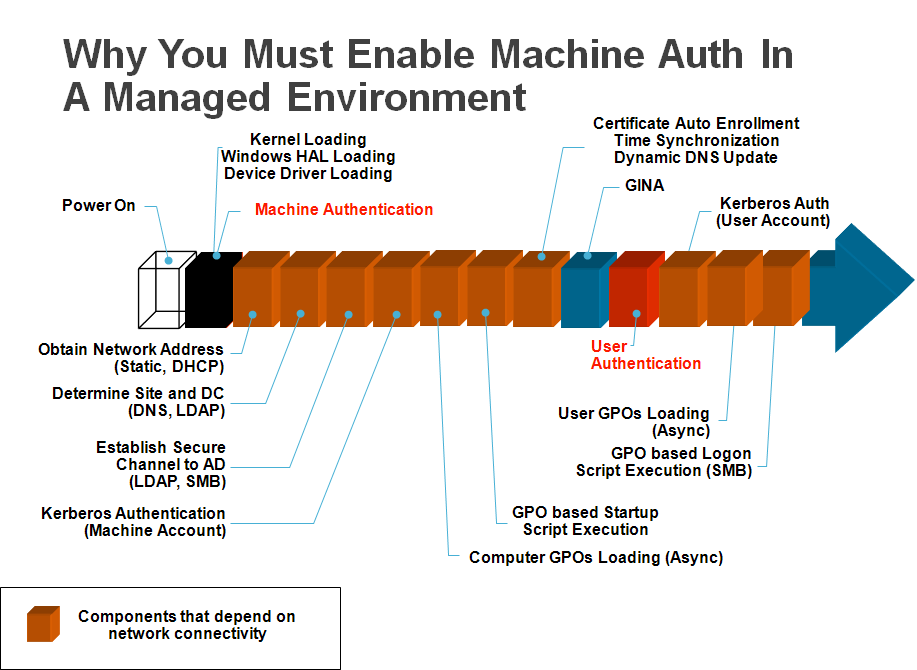
802.1X Machine auth will happen first at Layer 2 and using RADIUS to pass machine auth credentials to ISE and then validated to AD server. The Windows client does not require access to any file server or AD until after machine auth. It doesn't even have an IP yet! The network access device will authorize machine via RADIUS. At this point, ISE can return a dACL or other permission which allows DHCP, DNS, and access to the AD domain controller to the endpoint for user login. After user login, then full access can be given to client. If machine auth is not used, then it may be necessary to place port into Low Impact mode where DHCP, DNS, and AD access are granted prior to user auth.
/Craig
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-25-2016 06:02 AM
Thank you so much for this super explanation as always!
I'll listen the session! ![]()
- Jina
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-25-2016 10:04 AM
Jina,
We have conveniently linked all of our Cisco Live sessions for you on our ISE Training page!
-Thomas
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-28-2016 10:48 PM
Thanks Thomas, it will help me a lot ![]()
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide