- Cisco Community
- Technology and Support
- Security
- Network Access Control
- EAP-MD5 authentication Failing with 22056 Subject not found
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
EAP-MD5 authentication Failing with 22056 Subject not found
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-30-2018 02:42 AM
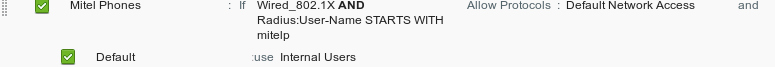
We have Mitel phones which we're trying to get to authenticate. We're using an internal user account and there is an authentication rule that points usernames beginning mitel to the internal users data store. When I plug the phone in I see only failed authentications with the above failure reason.
In the authentication report I can see that the selected identity stores only lists internal users.
I've double checked and the username in the request matches the username I created.
We're running v2.1
Thanks
- Labels:
-
Identity Services Engine (ISE)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-30-2018 06:15 AM
What condition are you using to match the username in your authentication rule? Post a screen shot of the details.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-30-2018 06:31 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-30-2018 06:28 AM
Check in the RADIUS logs and make sure that it is really failing authentication, and not the authorization step. You can use wildcards if you need to use static conditions. Make sure that your identity sequence has the applicable stores in it, and that the authentication policy is set to continue if authentication fails, and to continue to the next store if the user is not found.
HTH
Vince
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-30-2018 06:43 AM
| 11001 | Received RADIUS Access-Request | |
| 11017 | RADIUS created a new session | |
| 11117 | Generated a new session ID for a 3rd party NAD | |
| 15049 | Evaluating Policy Group | |
| 15008 | Evaluating Service Selection Policy | |
| 15048 | Queried PIP - Normalised Radius.RadiusFlowType | |
| 15048 | Queried PIP - Network Access.Device IP Address | |
| 15048 | Queried PIP - Radius.User-Name | |
| 15004 | Matched rule - Mitel Phones | |
| 11507 | Extracted EAP-Response/Identity | |
| 12300 | Prepared EAP-Request proposing PEAP with challenge | |
| 11006 | Returned RADIUS Access-Challenge | |
| 11001 | Received RADIUS Access-Request | |
| 11018 | RADIUS is re-using an existing session | |
| 12001 | Extracted EAP-Response/NAK requesting to use EAP-MD5 instead | |
| 12000 | Prepared EAP-Request proposing EAP-MD5 with challenge | |
| 11006 | Returned RADIUS Access-Challenge | |
| 11001 | Received RADIUS Access-Request | |
| 11018 | RADIUS is re-using an existing session | |
| 12002 | Extracted EAP-Response containing EAP-MD5 challenge-response and accepting EAP-MD5 as negotiated | |
| 15041 | Evaluating Identity Policy | |
| 15006 | Matched Default Rule | |
| 15013 | Selected Identity Source - Internal Users | |
| 24210 | Looking up User in Internal Users IDStore - mitelphone1 | |
| 24216 | The user is not found in the internal users identity store | |
| 22056 | Subject not found in the applicable identity store(s) | |
| 22058 | The advanced option that is configured for an unknown user is used | |
| 22061 | The 'Reject' advanced option is configured in case of a failed authentication request | |
| 12006 | EAP-MD5 authentication failed | |
| 11504 | Prepared EAP-Failure | |
| 11003 | Returned RADIUS Access-Reject |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-30-2018 07:32 AM
Also, remember that it is the device that is authenticating, not the username (the mitel username is for SIP with your voice system). You will need to make sure your identity sequence continues to the Internal Endpoint store, as this is where the device exits. Just test with the condition above, and it should work. I also break my Policies up to manage them better:
VPN policy
Wireless policy
Dot1x policy
MAB policy
Default policy
This way you can assign the authentication and authorization conditions with much more control
HTH-
Vince
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-30-2018 07:43 AM
It's been configured with a username and password to authenticate to the network. This is separate from any voice config.
Surely it's only hitting the default rule because ISE cannot find the identity in the identity store specified in the authentication rule hence the error message.
We break our policy sets down as well (though in a different way).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-31-2018 05:23 PM
Is the same set of the credentials working on other clients, perhaps using a different protocol?
If not already done, I would suggest to engage Cisco TAC to troubleshoot this further.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-30-2018 07:00 AM
you are matching the catch all "Default Rule" in the authentication profile for Dot1x. You will need to look carefully at the RADIUS log under attributes. Try creating a authentication rule that matches the Calling-Station-ID thet you see in your attributes, and place it above your default.
Vince
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-01-2018 01:40 PM
We have Avaya phones set up the same. Do you use 1 account for all phones?
Below is the flow I use.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide