- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Re: Generating CSR Error on ISE for System Certificate used for EAP Authentication
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-14-2020 08:17 PM
Hi All,
Quite new to the whole experience of ISE and Certificate based authentication on it.
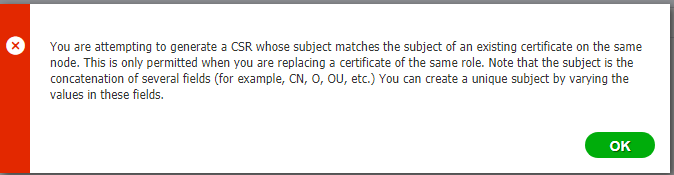
I am trying to generate a CSR for a System EAP authentication certificate that expires on 7th May for us. While trying to generate CSR however, I get below error message and the CSR does not get generated. How can I get beyond this? I am not sure if I should change any of the details from existing certificate.
Thank you.
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-05-2023 09:49 PM
You can do it that way, but it will cause a restart of the ISE services every time you move the Admin role to another certificate.
You can create a CSR with the same subject. ISE will throw a warning, but the old certificate won't be deleted until the new signed certificate is bound to the CSR.
My preference, however, is to make a minor change in the subject (like the OU) so you can install the new certificate without warning or replacement. You can then move the relevant role(s) to the new certificate. If there is any issue with the new certificate, you can easily move the role(s) back to the old certificate without having to re-import it with the private key (which would then delete the new certificate)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-14-2020 08:36 PM - edited 04-14-2020 08:45 PM
Hi
The csr your generating must'nt have same values in all fields as the on existing today already in use. Have you validated that you're filling in the same values on all fields?
Edit:typo error
Thanks
Francesco
PS: Please don't forget to rate and select as validated answer if this answered your question
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-14-2020 09:30 PM
Thank you for the inputs. So I can add to OU field and make it different and ensure it isn't use in any policy matching, and it should be fine.
Brings me to another important issue I am facing with CSR though - I am doing it for two nodes at the same time - how do I fill up the CN field under Subject in that case?
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-14-2020 09:38 PM
There are two typical approaches... wildcard certificates or Subject Alternative Name (SAN).
Some clients might not support wildcard certs for EAP authentication so, when I've had a similar customer wanting to use a single EAP cert for multiple PSNs, I've used the SAN option.
You would create the CSR (on PSN1) such that the CN = PSN1 FQDN and the SAN field has both the PSN1 and PSN2 FQDNs (in that order).
You would then bind the cert to the CSR on PSN1, export the certificate with the key, then import the cert into PSN2.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-14-2020 09:41 PM
By default, it's filled in with the keyword fqdn and ise will use the fqdn of each server automatically for each csr you generate (1 at a time).
If you want to have only 1 cert, you can do 1 csr, export it with its private key and import it on all other nodes.
Thanks
Francesco
PS: Please don't forget to rate and select as validated answer if this answered your question
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-14-2020 10:10 PM - edited 04-14-2020 10:10 PM
Thanks again.
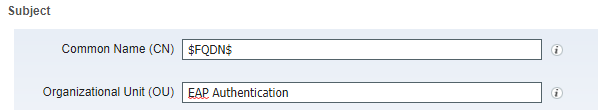
So sounds like there is two ways, although I find it much simpler if I let it use the FQDN under CN field, if it works. Currently CN field has by default $FQDN$ so that should work so long as I update one of the other fields, say OU to differentiate the certs from the existing ones and then it should all fall in place.
So I would generate CSR with those two fields as below for eg.:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-15-2020 03:45 PM
Thanks
Francesco
PS: Please don't forget to rate and select as validated answer if this answered your question
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-21-2020 06:54 PM
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-21-2020 07:42 PM
ISE requires that the EAP function (usage) is assigned to a certificate (and only one) so you cannot simply remove EAP from the existing certificate. You would have to install a new certificate with the EAP usage and ISE will move the EAP usage from the old to the new cert.
As long as the new certificate has a different Subject than the old cert, the old cert should remain on ISE until you delete it. In that case, if the new cert does not work, you should be able to move the EAP usage back to the old cert.
Best practice, however, is to export all identity certificates with their keys and copy them to a safe location that has strong security controls. That way, you can simply re-import them in the event of an unrecoverable node failure and not have to create new CSRs, trust chains, etc.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-14-2020 08:42 PM
ISE will not allow creating a CSR or binding a certificate that has the same Subject as another certificate. A common approach is to modify one of the certificate fields so that there is no matching Subject value.
I typically use the OU field in the certificate to indicate the Usage (Admin, EAP, etc) of the certificate to avoid duplicate Subject value issues. When renewing a certificate, I often just modify the same OU field slightly (like adding the Month/Year) to produce a unique Subject value.
I haven't seen anyone using the OU attribute as a matching condition in policies, so it is often easy to change.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-04-2023 09:34 PM
@Greg Gibbs
Hi Greg
How to renew certificate with the same CN,OU,O,....?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-05-2023 03:49 PM
If you install a certificate with the same Subject as an existing certificate, ISE will throw a warning and the existing certificate will be deleted and replaced with the new one. If you run into issues with the new certificate, you will need to re-import the old certificate with the private key, which will again replace the new one.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-05-2023 06:34 PM
@Greg Gibbs
You mean .
1. Delete the exsiting certificate and change role (Admin / EAP Authen / Portal) to new Cert
2. CSR with same attribute and sign then install to ISE change role to (Admin/EAP Authen/Portal)
Am I correct?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-05-2023 09:49 PM
You can do it that way, but it will cause a restart of the ISE services every time you move the Admin role to another certificate.
You can create a CSR with the same subject. ISE will throw a warning, but the old certificate won't be deleted until the new signed certificate is bound to the CSR.
My preference, however, is to make a minor change in the subject (like the OU) so you can install the new certificate without warning or replacement. You can then move the relevant role(s) to the new certificate. If there is any issue with the new certificate, you can easily move the role(s) back to the old certificate without having to re-import it with the private key (which would then delete the new certificate)
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide