- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Re: ISE (SNS-3695) Cluster on-boarding steps
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2022 05:29 AM
Can you please assist to provide high-level SNS-3695 appliance onboarding steps? I got ISE 3.0 shipped along with appliances.
I want to understand the sequential steps to be followed. I randomly put a few steps below, and I request your guidance and a few reference guides, and sequential order of approach to onboard these nodes.
1. ISE 3.0 Patch install
2. Migrate from 3.0 to 3.1( unable to see existing patch version running on new nodes)
3. License Migration from 2.X to 3.X- Can both ISE 2.x and 3.X nodes can consume ISE smart licenses?
4. ISE node registration cert, migrate from self-signed to Public PKI cert
5 Create EAP and other Portal PKI cert
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2022 08:58 AM
Start here: Cisco ISE & NAC Resources - Cisco Community
Specifically with the admin and installation guides. Step 1 should also be to re-image the 3695s with the 3.1 ISO as 3.1 is now the suggested release.
Yes multiple ISE deployments can consume from the same Smart Account / Virtual Account.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2022 08:58 AM
Start here: Cisco ISE & NAC Resources - Cisco Community
Specifically with the admin and installation guides. Step 1 should also be to re-image the 3695s with the 3.1 ISO as 3.1 is now the suggested release.
Yes multiple ISE deployments can consume from the same Smart Account / Virtual Account.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2022 09:55 AM
Definitely use the link provided by @ahollifield
3. License Migration from 2.X to 3.X- Can both ISE 2.x and 3.X nodes can consume ISE smart licenses?
-Yes. Note that the license model between 2.x and 3.x has changed. Any 2.x model type licenses will require TAC to migrate. Have a peek here: https://www.cisco.com/c/en/us/products/collateral/security/identity-services-engine/ise-licensing-migration-guide-og.html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2022 01:19 PM - edited 05-14-2022 01:30 PM
Hi @Anilvnair ,
I would like to add the following points:
. ISE 3.1 is the Suggested Release:
a. Patch 3 is the latest patch, but very new: May 2nd
b. Patch 2 is a Deferred Release
c. Patch 1 (Dec 7th), you also need to install the LOG4J2-FIX-3.1PATCH1
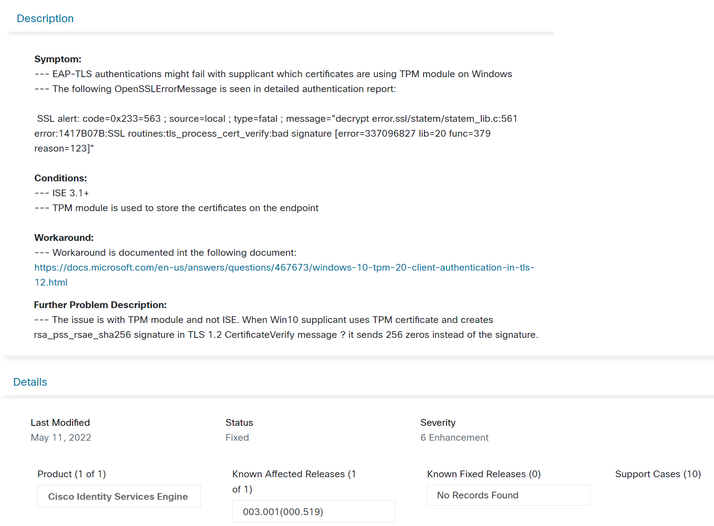
Note: in Cisco ISE Release 3.1, EAP-TLS Authentication might fail for certificates using TPM module on Windows 10. This is an issue with the TPM module and not with Cisco ISE.
. ISE 3.0
a. Patch 5 is the latest patch (Jan 31th), for this patch you don't need to install the LOG4J2-FIX-2.4-3.0
Hope this helps !!!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-15-2022 06:38 PM
@Marcelo Morais - regarding the comment "Note: in Cisco ISE Release 3.1, EAP-TLS Authentication might fail for certificates using TPM module on Windows 10. This is an issue with the TPM module and not with Cisco ISE." - how is this ISE 3.1 specific? Do you have a bug ID or some other links for this issue?
thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-15-2022 06:58 PM
Hi @Arne Bier ,
please take a look at ISE 3.1 Release Notes., search for EAP-TLS Authentication Might Fail for Certificates Using TPM Module., and CSCwb19635 ISE 3.1 EAP-TLS authentications might fail with certificates installed in TPM module.
Regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-15-2022 09:08 PM
thanks @Marcelo Morais - charming, isn't it? As if 802.1X wasn't tricky enough
I am not sure why this is listed under ISE 3.1 only - does that mean it was only found by a customer running ISE 3.1, and would not affect other ISE implementations? The way I read that Release Note, it sounds very much 3.1 specific. Or did I miss something?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-16-2022 04:03 AM
Hi @Arne Bier ,
I agree with you, not only it looks like a 3.1 specific in the ISE 3.1 Release Notes, but also at the CSCwb19635 Conditions description: "... ISE 3.1+ ...".
Please take a closer look to: Windows 10 TPM 2.0 Client Authentication in TLS 1.2 with RSA PSS making trouble.
" ... By disabling RSA PSS on the Client, the Client uses another cipher to sign the packet and then it works. ... "
" ...Keep in mind that this is only a workaround and should not be used as a final solution. We are actually still working with Microsoft on a solution. It's still not 100% clear if it's the TPM that is making the issue or if it is the OS. ... "
Maybe versions of ISE earlier than 3.1 handle RPA PSS differently than ISE 3.1.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-18-2022 06:12 AM
Hi @Arne Bier ,
take a look at the following post: TLS Handshake fail ISE 3.1.
" ... Opened a TAC Case and it seems that 3.1 using a different SSL library/version. In Patch 4 which should arrive in October you're able to choose the different Ciphers, ISE will use to negotiate with the Client so you can disable the RSA PSS which causes this problems... "
Regards
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide