- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Yes, the ideal way to get
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-21-2016 09:50 AM - edited 03-11-2019 12:14 AM
Hi.
First of all the versions:
ACS: 5.8
WLC: 7.0.240.0
Now the problem:
I'm having problems making the following configuration work.
I want to restrict access to SSIDs based on AD group membership and the MAC address of the client device.
On the WLC, I created a WLAN with MAC Filtering and WPA2 with 802.1x+CCKM.
I joined the ACS to the domain and added the AD group.
I also created an Identity Store sequence and added both Internal Hosts and the AD to it.
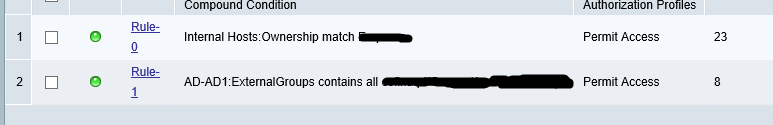
I created a rule on the Default Network Access:

The problem seems to be that ACS only checks one Identity Store.
If I edit the rule and remove the AD group condition, the host gets authenticated, but AD fails.
Is there a way for making this work?
Thanks in advance for any help.
Solved! Go to Solution.
- Labels:
-
AAA
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-22-2016 07:31 AM
Yes, the ideal way to get this done through 2 rules only.
However, my recommendation also to use WLAN with either MAC filtering or 802.1x.
Please rate as correct if it helps!!
Regards
Gagan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-22-2016 02:55 AM
Hi,
Generally we use either mac filtering or 802.1x authentication. If ACS authenticates with the first store in sequence, it will not move to other store.
Regards
Gagan
ps: rate if it helps!!!!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-22-2016 03:43 AM
Thank you for the answer.
I think I got it to work by using two rules. One for the Internal Host store (MAC address), and other for the AD group.
I don't know if this is the best way to do it, but it seems to be working.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-22-2016 07:31 AM
Yes, the ideal way to get this done through 2 rules only.
However, my recommendation also to use WLAN with either MAC filtering or 802.1x.
Please rate as correct if it helps!!
Regards
Gagan
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide

