- Cisco Community
- Technology and Support
- Networking
- Network Management
- Re: Restrict access to APIC-EM :443 ?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Restrict access to APIC-EM :443 ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-25-2019 01:52 PM
Using APIC-EM solely for PnP function to configure new devices, and I have been given a requirement to restrict access to the APIC-EM GUI to specific IPs. I really don't want to have to put it behind an internal firewall.
I can't see a way in the Web GUI to restrict access (understandable, this is likely uncommon - probably just me).
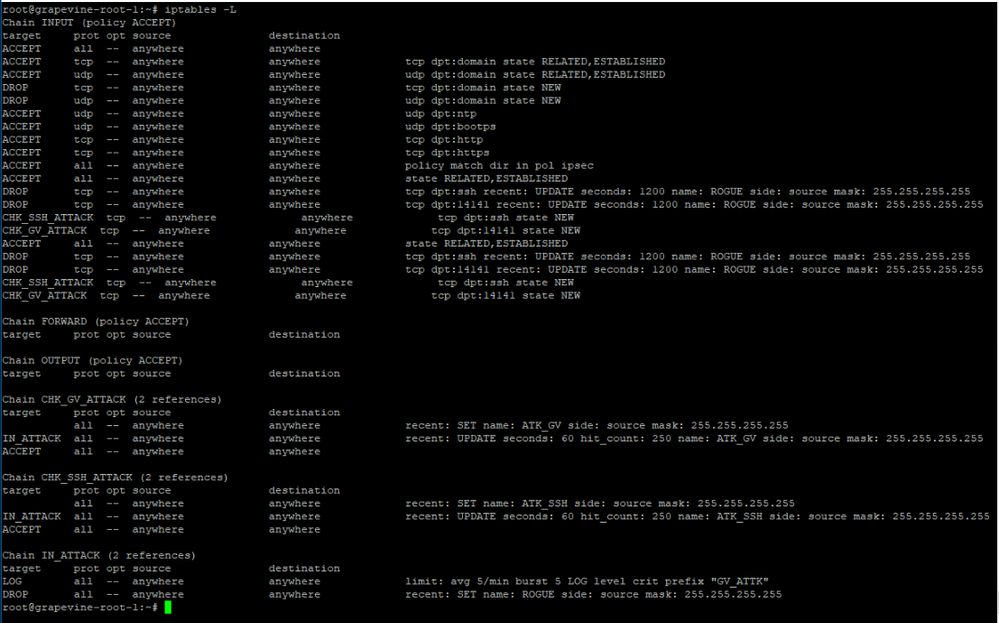
BUT, from the CLI I can see that the Linux VM implements iptables.... so I am wondering if I could safely add source restrictions on :443 to restrict access to the web GUI? I realize I need to permit the target PnP subnets also .. this is a rather contained implementation doing PnP configs in a staging area only, not network-wide, but the APIC-EM is in a datacenter elsewhere. I also understand that future APIC-EM upgrades may change/replace iptables and I'd need to revisit after upgrades, but is this something possible and worth pursuing? Thoughts?
Thanks folks, --David
- Labels:
-
Network Management
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-25-2019 03:27 PM
Hi there,
For the reason that you mention; having to redo the tweak after each update, I wouldn't go down the path of editing iptables on the VM. I did something similar with the hosts file on a Prime install which turned into a real pain after each update!
Why not just add an OUTbound ACL to the SVI which is connected to the subnet which APIC-EM resides on?
... permit tcp <pnp_subnets> <pnp_netmasks> host <apic-em_ip> eq 443 deny ip any host <apic-em_ip> ...
cheers,
Seb.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-26-2019 07:18 AM
Thank you for the reply and sharing your experience with similar situation under Prime.... was afraid of that; nice to have confirmation that it could indeed pose issues.
Unfortunately, adding an ACL in the environment I am working in may be nearly as difficult as a firewall solution !
Regards, --dmr
@Seb Rupik wrote:Hi there,
For the reason that you mention; having to redo the tweak after each update, I wouldn't go down the path of editing iptables on the VM. I did something similar with the hosts file on a Prime install which turned into a real pain after each update!
Why not just add an OUTbound ACL to the SVI which is connected to the subnet which APIC-EM resides on?
... permit tcp <pnp_subnets> <pnp_netmasks> host <apic-em_ip> eq 443 deny ip any host <apic-em_ip> ...cheers,
Seb.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide