Need help understand ASA with firepower vs FTD2100
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-13-2018 10:16 AM - edited 02-21-2020 07:45 AM
Hi !!
I have to configure ASA with firepower services in HA mode. (Active/standby). I am confused now as I see many documents.
My understanding of things. Kindly correct or add if I miss anything.
1. ASA with Firepower services needs to be updated first for firepower image. Not sure if I need this to be done through cli only or through FMC as I see sfr 6.2.0 to be present/
ciscoasa# show module
Mod Card Type Model Serial No.
---- -------------------------------------------- ------------------ -----------
1 ASA 5516-X with FirePOWER services, 8GE, AC, ASA5516 JAD21770NGZ
sfr FirePOWER Services Software Module ASA5516 JAD21770NGZ
Mod MAC Address Range Hw Version Fw Version Sw Version
---- --------------------------------- ------------ ------------ ---------------
1 4c77.6dd8.75ec to 4c77.6dd8.75f4 3.0 1.1.8 9.8(1)
sfr 4c77.6dd8.75eb to 4c77.6dd8.75eb N/A N/A 6.2.0-362
Mod SSM Application Name Status SSM Application Version
---- ------------------------------ ---------------- --------------------------
sfr ASA FirePOWER Up 6.2.0-362
Mod Status Data Plane Status Compatibility
---- ------------------ --------------------- -------------
1 Up Sys Not Applicable
sfr Up Up
2. I already have sfr 6.2.0 present but I see asa promt. How do I go to FTD prompt? Also do I need to configure any class-map or policy-map to redirect the traffic from asa to firepower??
3. If my asa in currently state directly configurable from FMC? Can i plug and start the configuration of ASA with firepower using FMC for IP addressing, HA , Access Control, NAT etc? or I am missing some steps?
Kindly share your views.
Note: I have experience in configuring the FTD2100 appliances and I was able to configure them just by adding the ip addressing and then adding them to FMC. But ASA with firepower is something new for me.
- Labels:
-
NGFW Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2018 12:50 AM - edited 05-14-2018 12:52 AM
Hello Nandan,
So you can do the update of the firepower module through ASDM: Update ASA FirePOWER Modules Managed with ASDM, or you can do it using the Firepower Management Center: Update 7000 and 8000 Series Devices, NGIPSv, and ASA FirePOWER Modules Using the Firepower Management Center
To go to FDM prompt, login to your ASA that has the Firepower Services on and type: session sfr console, on the ASA CLI, enter the username and password that you set for the Firepower Services and you are in.
I am not 100% what you want to do on your third point, but from the Firepower Management Console you can configure only Firepower related services and functions (every aspect of them) but you cannot make changes to the ASA itself. For that you will have to use the ASA CLI or the ASDM.
Hope that helps.
If this was helpful, please vote as helpful by clicking on the star icon below.
-------------------------------------
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2018 01:04 AM - edited 05-14-2018 01:22 AM
Hi!!
Can you confirm if we cannot configure the ASA with Firepower for any access control and NAT policies, HA configuration, Anyconnect configuration etc using FMC? Do we need to use CLI or ASDM for this part of the configuration?
I thought FMC would be enough to configure the ASA with firepower module for whole configuration.
As one of the document says "
ASA FirePOWER Management
The module has a basic command line interface (CLI) for initial configuration and troubleshooting only. You configure the security policy on the ASA FirePOWER module using one of the following methods:
- Firepower Management Center—Can be hosted on a separate Firepower Management Center appliance or as a virtual appliance. Previous to version 6.0, the management center was called FireSIGHT Management Center.
- Adaptive Security Device Manager (check for compatibility with your model/version)—You can manage both the ASA and the module using the on-box ASDM.
https://www.cisco.com/c/en/us/td/docs/security/asa/quick_start/sfr/firepower-qsg.html#pgfId-139815
"
Kindly confirm if my understanding is wrong.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2018 01:23 AM
Hello Nandan,
The point here is that ASA and Firepower they might run under the same hardware, but they are separate devices so what you configure on the ASA firewall does not affect the Firepower firewall and what you configure on Firepower does not affect the ASA. Firepower is basically a Virtual Machine that lives on the ASA.
So, if you want to configure NAT, AnyConnect and HA, for the ASA firewall then you do it via CLI or ASDM for the ASA, not the Firepower.
If you want to configure NAT, AnyConnect and HA, for the Firepower then you do it via the Firepower Management Console.
Hope that helps.
If this was helpful, please vote as helpful by clicking on the star icon below.
-------------------------------------
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2018 04:46 AM
@AlexPi has it correct.
@Nandan Mathure your FTD 2100 is running a very different image than an ASA with Firepower service module.
FTD is a unified image and all functions (after initial bootstrap) are managed from the GUI (FMC or, optionally, the local Firepower Device Manager).
A Firepower service module can be managed with either ASDM or FMC. Most people don't use ASDM unless it's a very very small or lab setup since FMC is much better with event retention, reporting, object and policy reuse etc. When you manage it with FMC it is ONLY managing the module, not the associated ASA configuration.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2018 05:20 AM - edited 05-14-2018 05:25 AM
Thanks @AlexPi and @Marvin Rhoads
Since this is a brand new install...by your comments it means I will have to configure Firepower services related part with FMC and also use ASDM (or CLI)for or overall configuration of ASA 5516-X with firepower in HA mode like NAT, Access Control, Anyconnect etc. I cannot just use FMC to configure everything like I did with FTD2110.
Also do I have to add following on CLI?
access-list ACL-FirePOWER extended permit ip any any class-map CM-SFR match access-list ACL-FirePOWER exit policy-map global_policy class CM-SFR sfr fail-open exit exit write mem
Correct me if wrong. Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2018 05:29 AM
Hi Nandan,
That's right. If you need to use the ASA like you do FTD2100, you would need to reimage the box with a FTD image.
Otherwise you can continue managing ASA with ASDM/CLI and firepower module with FMC.
Hope it helps,
Yogesh
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2018 05:58 AM - edited 05-14-2018 06:09 AM
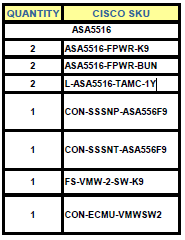
Thanks @yogdhanu and @Marvin Rhoads, I might go with the Upgrade. Do I need any additional licenses that you may think of?
I currently have this...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2018 08:17 AM
By upgrade do you mean change from ASA with Firepower service module to ASA running FTD image? If that's what you want to do then your current TAMC license is incorrect.
FTD uses a Base plus URL Filtering and Malware licenses that are priced slightly differently than the Firepower module (although they end up doing mostly the same thing). Also they are Smart licenses not PAK-based like Firepower service module licenses.
The FMC license you listed is for two devices. Is that a separate FMC than is managing your FTD devices? I ask because FMC licenses are not additive (i.e., you cannot buy 2 each 2-device FMC licenses and then be authorized to manage 4 devices.)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2018 11:33 PM - edited 05-14-2018 11:53 PM
FS-VMW-2-SW-K9 is for managing 2 ASAs with Firepower services in HA. We just have these 2 devices which will be in active/standby. Kindly correct if I am understanding it in a wrong way.
I read your comments about licensing now but till then I had already upgraded to unified image. Today I will reimage them back to ASA with firepower services so I don,t have to change any licenses.
So that
2 ASAs with firepower services in HA will be managed by FMC (for IPS, Apps, AMP, URL) and ASDM/CLI for HA, Access Policies, NAT, Anyconnect, etc.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-15-2018 01:39 AM
Yes that will work.
When you add the Firepower modules to FMC, just put them in a device group so that you will be sure to apply policy once to both units
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2018 05:30 AM
@Nandan Mathure that's correct.
The ACL you have assumes you want to inspect everything with Firepower. It is the most common way it's setup although other more selective ACLs are sometimes used. For instance, when we have trusted flows to a remote data center or perhaps an IPsec flow through the ASA that cannot effectively be inspected or is otherwise trusted we can tune that ACL to not pass that particular traffic to the module for inspection.
The equivalent in FTD is a prefilter policy rule with action "trust".