

Yokohama, Japan was the host city for IETF 94. The IETF hackathon, sponsored by Cisco DevNet, got things started the weekend before, October 31 – November 1. The hackathon was the 3rd in a continuing series to advance the pace and relevance of IETF standards activities by bringing the speed and collaborative spirit of open source software into the IETF.

More than 70 developers came together to test experimental protocols, produce reference implementations, create useful utilities, etc. Many participants were long time IETF contributors, but there were several first time attendees and young developers with new ideas, including our youngest coder who was 16 years old.
More than 70 participants formed into roughly a dozen teams working across a wide range of technologies. These included many IETF working groups (e.g. dane, dhc, dnsop, dprive, homenet, i2rs, iptube, netconf, netvc, sfc) and corresponding open source projects (e.g. Dalla, getdns, Kea, OpenDaylight, OPNFV, RIOT, Thor). Each team produced significant results, including the DNS privacy and security team, which extended and demonstrated use of getdns APIs to eliminate metadata leakage, and the Homenet team, which prototyped and demonstrated provider aware selection of IPv6 prefixes from home routers, PCs, and mobile devices.


How does an IETF Hackathon work?
The hackathon started Saturday at 09:00. Technology “champions” introduced each technology and proposed projects. Next, champions and participants formed teams and started hacking. Several teams included members from more than one IETF working group and/or open source community. The ensuing collaboration, mixing of cultures and ideas, and new friendships all point to the long term benefits that extends beyond the hackathon itself.




Motivated, caffeinated, and energized, participants worked tirelessly, advancing the standards that provide the internet’s foundation and creating open source implementations that validate these standards and makes them easier for others to consume. Not everything worked according to design and there were frustrating moments, but course correction and eventual success ruled the day.




Sunday afternoon, each team shared accomplishments and lessons learned with peers and a panel of esteemed judges - Jari Arkko (IETF Chair), Ray Pelletier (IETF Administrative Director), and Adam Roach (NETVC chair). The judges recognized teams based on various criteria established for the hackathon:
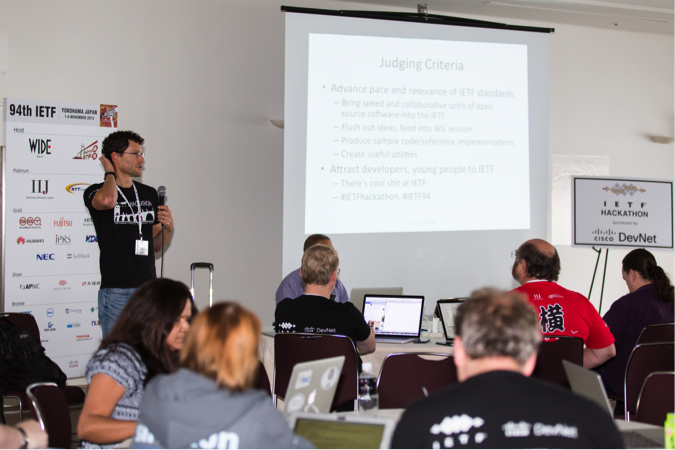
In case you are tired of squinting, the slide reads:
- Advance pace and relevance of IETF standards
- Bring speed and collaborative spirit of open source software into the IETF
- Flush out ideas, feed into WG session
- Produce sample code/reference implementations
- Create useful utilities
- Attract developers, young people to IETF
- There’s cool sh*t at IETF
There were techie prizes compliments of Cisco DevNet and tickets to the IETF social event donated by WIDE, but the real winners were the IETF community. The efforts of the hackers where shared in corresponding working group meetings the following week, and a number of teams demonstrated their work and fielded Q&A at Bits ’N Bites Thursday night.

The complete set of technologies and projects are available via the event Wiki. From the main hackathon page, its easy to navigate to this Wiki and those from previous hackathons as well. The IETF and open source communities are encouraged to bookmark and reference these sites to help with their ongoing work.
What comes next?
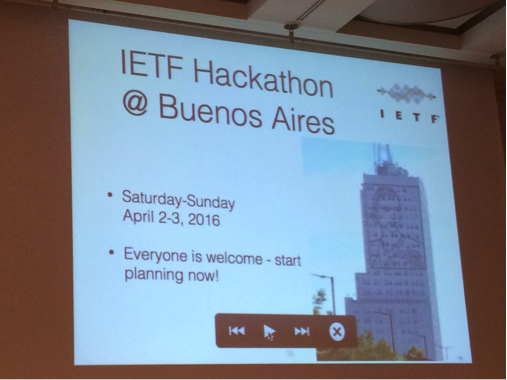
For the first time ever, the IETF goes to South America. IETF 95 is in Buenos Aires, with the Hackathon kicking things off the weekend before, April 2-3. So mark your calendar, plan to arrive early, and join us as we accelerate the pace and relevance of the IETF’s tireless work extending and improving the internet we all know, love, and use ever day.
Stay informed
The keep up to date with all things related to past and future hackathons, subscribe to hackathon@ietf.org.
