The cat's out of the bag! In October 2020, Cisco announced the Next Generation of Enterprising Routing Platforms: the Catalyst 8000 Edge Platforms Family including the Catalyst 8200, Catalyst 8300, Catalyst 8500, and Catalyst 8000V. The new family of Cats delivers a flexible platform and a secure experience from the branch to the cloud edge.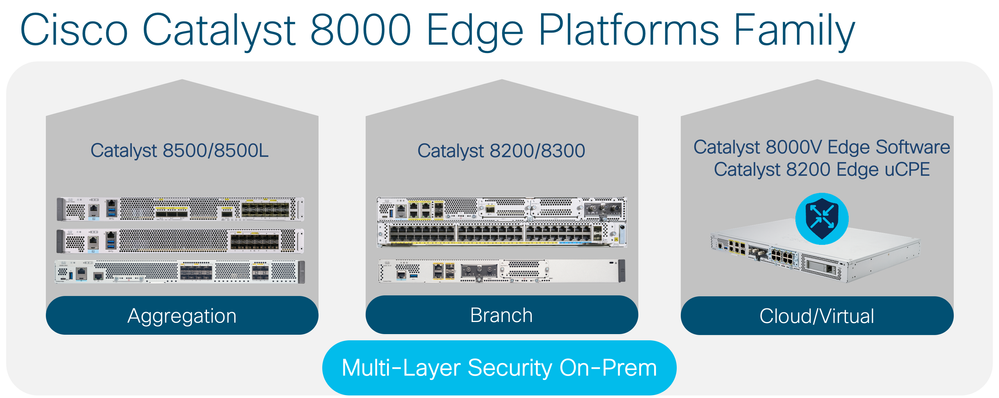
The Catalyst 8000 Edge Platforms are purpose-built for Aggregation, Branch, and Cloud/Virtual WAN edge deployments. Designed for each edge’s needs, the portfolio boasts a range of architectures:
- Aggregation Edge – Catalyst 8500 Series Edge Platforms are powered by Cisco’s Third Generation QuantumFlow Process ASIC (QFP 3.0).
- Branch Edge – Catalyst 8200 and Catalyst 8300 Series Edge Platforms are powered by x86 multicore System on Chip (SoC) architecture.
- Virtual/Cloud Edge - Catalyst 8000V Edge Software runs on any x86/VNF-based host either on-prem or cloud-based.
Buckle up for an exciting ride as we explore the power of SoC architecture and what it’s like to safely live on the Branch Edge with the Cats!
Dynamic Core Allocation
First stop – let’s get you a new car. Would you like to buy a sleek sports car designed for speed? Or a minivan equipped with the latest features and extra room? The choice is going to depend on your needs. You have 4 kids so you decide to go with the minivan. The minivan has enough seats for everyone, extra room for comfort and storage, and even a tv to keep the kids entertained – great. The minivan is just what you need for everyday life with the family, but when the weekend rolls around and your kids are with friends, you feel the need for speed and want to go fast. You think to yourself, maybe you made the wrong choice… but don’t fret! Take out the extra seats, unload your kids’ junk, and swap out the engine for one with more cylinders. Now your minivan is a weekend warrior and you are able to cruise around! Come Monday, put the seats back in, load up your kids’ belongings, and swap out the engine and you are ready to safely drop your kids off at school. Life is good – your minivan can serve all of your needs.
Thanks to the Intel x86 System on Chip (SoC) architecture, the Catalyst 8200/8300 Series offers the same system flexibility. One of the key innovations of the SoC architecture is dynamic core allocation which offers flexibility in which the multi-core planes can be utilized. Starting in the IOS XE 17.4 release, dynamic core allocation between the service plane and data plane is supported. Customers are able to modify the core allocation using CLI based on their deployment model and its needs (i.e., services heavy or data plane heavy). With IOS XE 17.4, a device reboot is required after re-allocation of the cores, however with the new IOS XE 17.5 release, a reboot is not necessary.
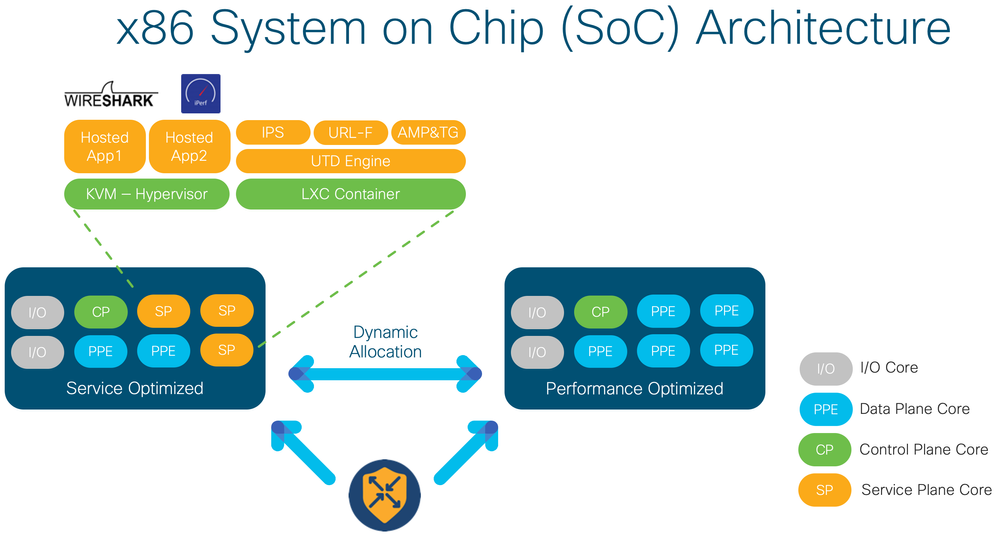
With dynamic core allocation, the Catalyst 8200 and Catalyst 8300 Series platforms provide the customer with a flexible system that can meet throughput and services demand based on their deployment requirements.
Multi-Layered Security
Next stop – multi-layered security! The Catalyst 8200 and Catalyst 8300 Series brings customers a flexible yet secure platform. They provide centralized, multi-layered security on-prem to protect traffic from enterprise office to cloud and back. With software-defined WAN security, the platforms benefit from a full security stack for protection against internal and external threats.
Simplified & Centralized Management
The service plane cores of the x86 SoC architecture can host security applications on-box using a Linux Kernel Container (LXC). With the LXC, a Unified Threat Defense (UTD) Engine can then run a variety of security application services. The LXC uses many of the kernel resources of the device unlike Kernel Virtual Machine (KVM) containers that have their own independent kernel giving a LXC a slight performance edge over a KVM.
On-Box Security Features
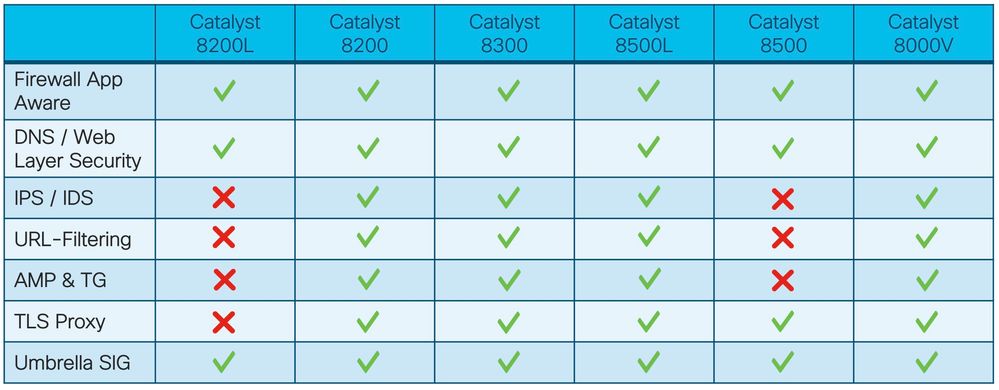
To protect the network from every angle, UTD can run a number of on-box security services:
- Firewall App Aware: Provides application visibility and granular policy and control of thousands of applications. Policies can be implemented to allow or block traffic by application category or specific application.
- Intrusion Prevention System (IPS): A built-in intrusion prevention system within an on-premises enterprise firewall based on Snort and powered by global Talos threat intelligence to detect and prevent vulnerabilities.
- URL-Filtering: Enforces acceptable use controls to block or allow based on 80+ web categories covering millions of domains and billions of web pages.
- Advanced Malware Protection & ThreatGrid (AMP & TG): Detects and prevents malicious files with sandboxing.
- TLS Proxy: Decrypts incoming and outgoing TLS traffic to enable its inspection by UTD and identify risks that are hidden by end-to-end encryption over TLS channels.
Cloud-Based Security Features
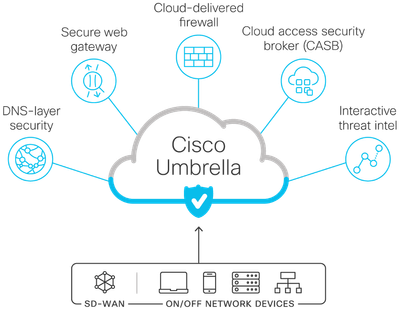
In addition to the on-box features, the Catalyst 8000 family also supports a variety of cloud-based security features:
- DNS/Web-Layer Security: Monitors and blocks DNS requests over any port or protocol, preventing both infiltration and exfiltration attempts. Malicious and unwanted domains, IP addresses, and applications are blocked before a connection is ever established, stopping threats at the earliest point.
- Secure Access Service Edge (SASE) Umbrella Secure Internet Gateway (SIG): A platform that offers cloud-delivered firewall (CDFW), secure web gateway (SWG), cloud access security broker (CASB), and threat intel.
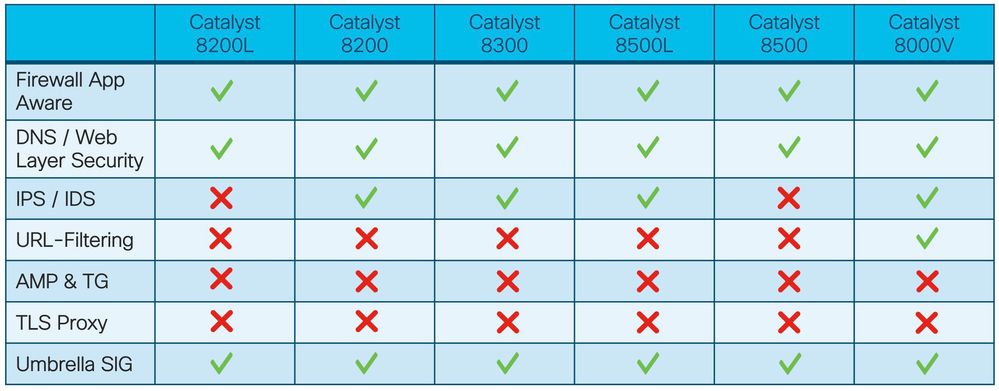
Together these security solutions offer constant protection against internal and external threats from a range of sources while meeting compliance demands. Check out which are supported on the Catalyst 8000 platforms in the table below:
SD-WAN Controller Mode:
Non-SD-WAN Autonomous Mode:
You can have all that and much, much more with the Catalyst 8000 Edge Platforms family.
What do you say – are you ready to live on the Edge with the secure Cats? Learn more now:
