In less than a week, in Las Vegas, Cisco will showcase a revolutionary solution for defense and detection against encrypted malware.
In a recent global study, more than 40% of attackers used encryption to evade detection. Things will get much worse. By 2020, 80% of WW traffic will be encrypted according to multiple analysts. Simultaneously, weak, out-of-date, ciphers are proliferating, due to the rapid growth of users, devices and sessions. Enterprises often decrypt traffic for inspection on access networks. This approach will become prohibitively expensive due to sheer complexity, new privacy regulations and the adoption of perfect forward secrecy.
What is needed is to ubiquitously scan for threats in their encrypted state and continuously monitor your entire access infrastructure for the strong cryptography.
Cisco’s new Encrypted Traffic Analytics combines both these capabilities with new machine learning systems both in the cloud and on-premise. And it leverages your own network. Without decryption it detects hidden malware with high precision and it instantly identifies older cyphers and protocols so they can be updated.
At CiscoLive, Cisco will demonstrate the full power of machine learning enabled by Cisco Stealthwatch, Cognitive Analytics and new networking technologies.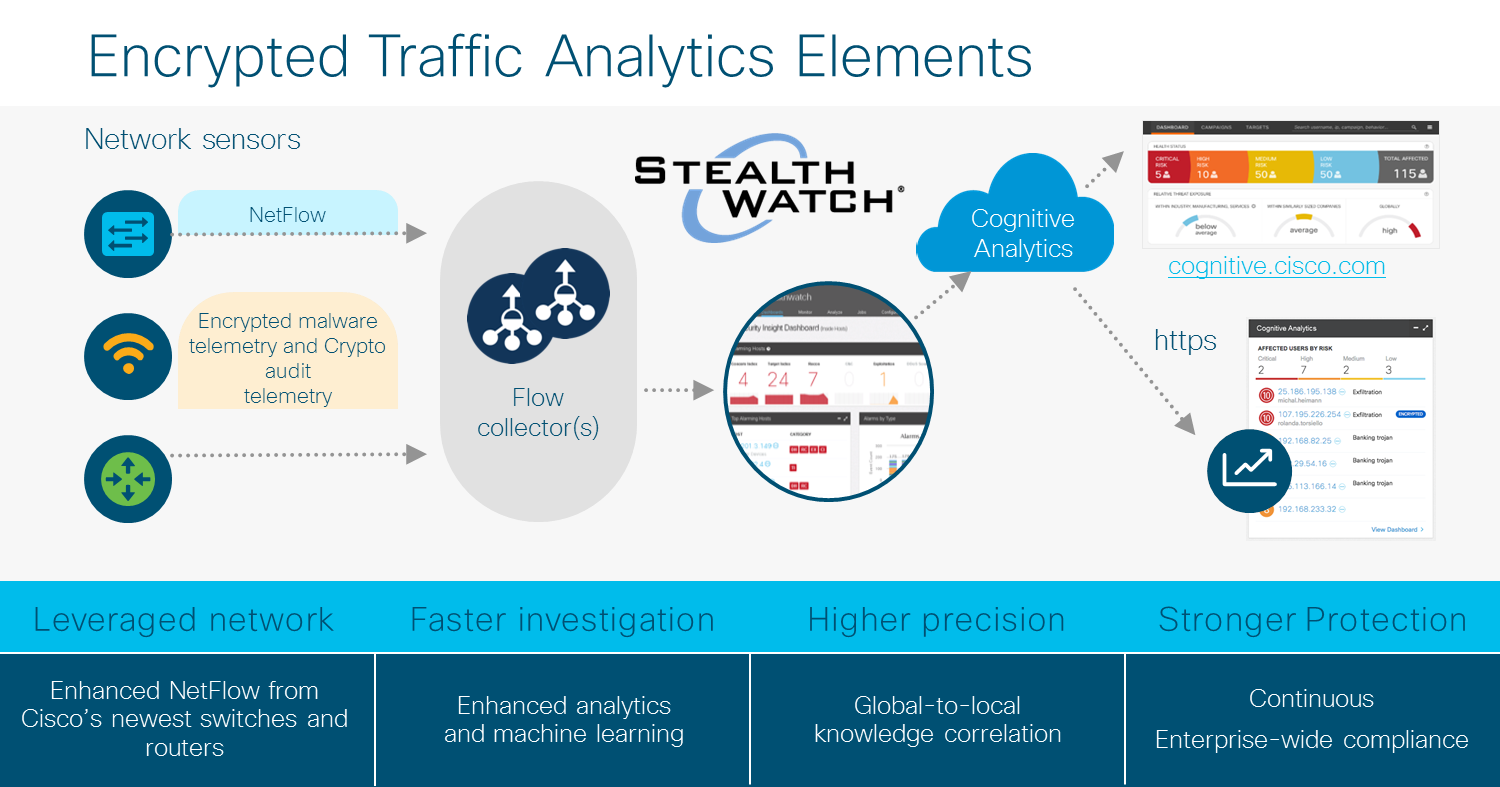
CiscoLive Events
World of Solutions Cisco Campus
| Demo | Zone |
|---|
| Stealthwatch Security Analytics | Security |
| Network Sensor and Enforcer | Enterprise Networks and Mobility |
| Network Security Analytics | IT Insights |
| Theater Presentations | Theater walk up |
Sessions and Tectorials
(Search for Session ID)
- Hidden Figures: Securing What You Cannot See - Session ID: INSSEC-1013
- Detect Threats in encrypted Traffic without decryption - Session ID: BRKCRS-1560
- Detecting Threats with Advanced Analytics Martin Rehak - Session ID: BRKSEC-3106
- Deciphering Malware's Use of TLS (without Decryption) - Session ID: BRKSEC-2809
- Understanding Encrypted Traffic Using "Joy" for Monitoring and Forensics - Session ID: DEVNET-1218
- DevNet Workshop - An Introduction to Monitoring Encrypted Network Traffic with "Joy" - Session ID: DEVNET-1215
- Security Monitoring with StealthWatch: The detailed walkthrough - Session ID: BRKSEC-3014
- Building Network Security Policy Through Data Intelligence - Session ID: BRKSEC-2026
|
After CiscoLive, join us on July 12, 2017 in the Cisco Customer Connection program. We'll have a special technical deep-dive breifing on Stealthwatch 6.9.2 and whole ETA solution. Simply join the Customer Connection program to register and navigate your way to the online briefings session registration. www.cisco.com/go/ccp
And later in July, look for another Cisco blog on the science of encrypted malware detection using machine learning.
Look forward to your attendance in person in Las Vegas and on-line for the webinar and follow-up blog.
|
