The article is intended for anyone who is familiar with TCP/IP and explains the TCP three-way handshake process.
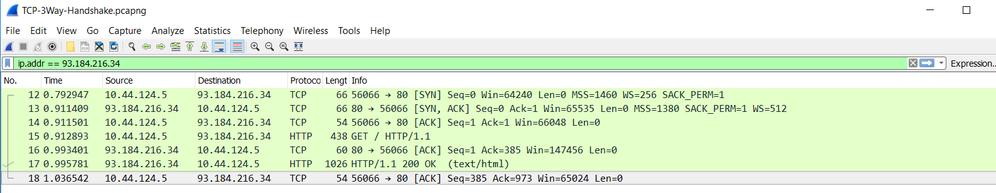
I have captured the traffic between the client PC and a web server (example.net) using Wireshark.
To establish a connection between client and server, TCP uses a process called three-way handshake. (SYN, SYN-ACK, ACK)
First thing first, why is three-way handshake called as a three-way handshake? The reason being is that three segments are exchanged between the client and the server for TCP connection to be established.
The following sequence shows the process of a TCP connection being established.
Step 1 Packet# 1
The client wants to initiate a connection to the server (93.184.216.34). So, the client sends a packet with SYN bit set. SYN flag announces an attempt to open a connection.
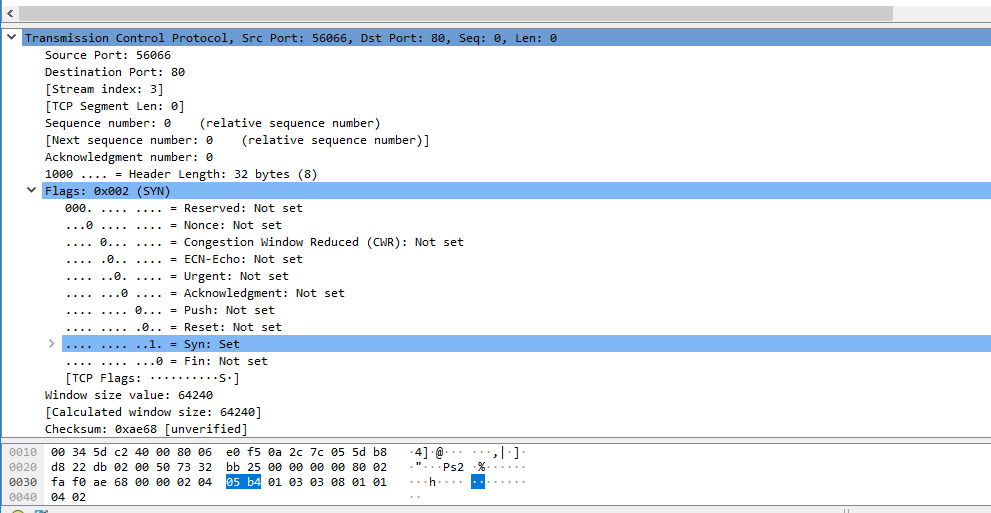
If you look at the TCP header, the source port is randomly selected by Windows and the destination is well-known port 80. Length of the data is zero because this is a SYN packet and no data is transmitted in this stage. If you look at the sequence number, the value is set to zero by Wireshark (Relative sequence number).
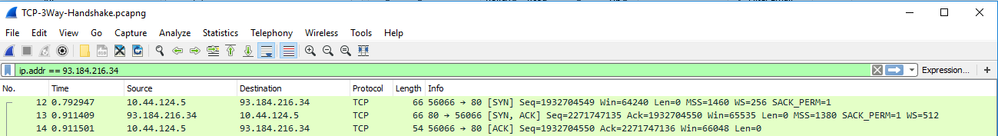
The actual value would be a 32 bit randomly selected number which we humans will find hard to keep up with. From the screenshot you can see the actual SEQ number from the client is 1932704549 (I have also attached the picture which shows the actual 32 bits sequence number below)
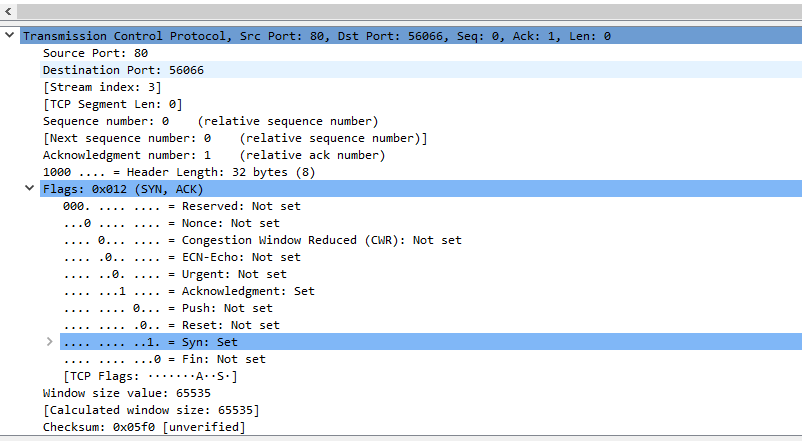
Step 2 Packet# 2
In step 2, the server will respond to the client with ACK and SYN bit set. Like step 1, Length of the data is zero, no data is transmitted in this stage. The sequence number is set to 0 (relative) and acknowledges the request of the client for synchronization. The server sends an acknowledgment of 1 to the client. The ACK is specific to the SYN the client sent. The acknowledge number is set to one more than the receive sequence number.
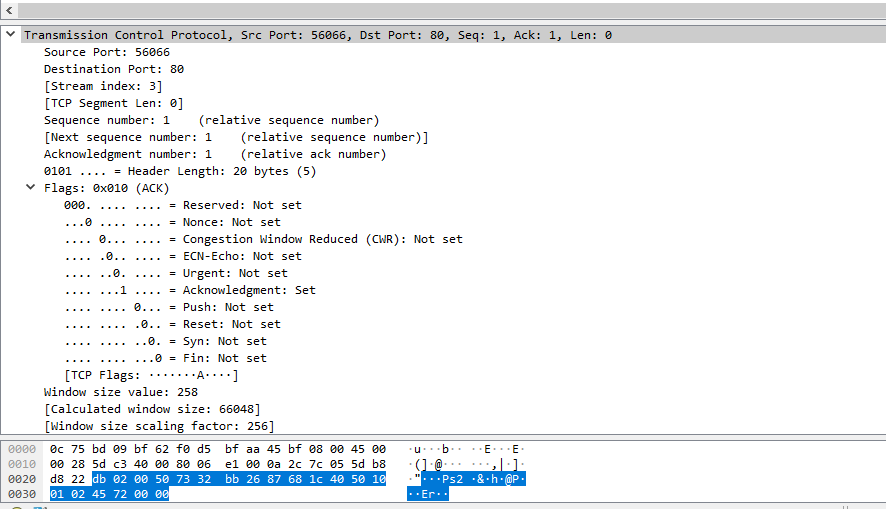
Step 3 Packet# 3
Finally, the client acknowledges the server’s request for synchronization with ACK 1. The ACK is specific to the SYN the server sent. The acknowledge number is set to one more than the receive sequence number.
The above process creates a reliable OSI Layer 4 connection between two hosts.
Thanks for the read
