Cisco is changing networking forever! 2017 was the start of a network revolution that will ushered in the dawn of The Network. Intuitive. beginning with Enterprise Switching.
Cisco’s customers and partners were introduced to new and exciting hardware and software innovations that laid the foundation for a network revolution.
Catalyst 9000 Series Switches
While the industry has been buzzing about intent based networking, Cisco did it. In 2017, we unveiled a breakthrough in Enterprise Switching by introducing the Catalyst 9000 series switches which are built for evolving trends of ever-growing connected devices. These switches deliver high performance and unmatched functionality with innovations in security, IoT convergence, cloud readiness and mobility. The boxes come ready to accept the software subscription updates that are so popular now.
Software-Defined Access (SD-Access)
SDA is the industry’s first intent-based networking solution for the Enterprise built on the principles of Cisco Digital Network Architecture. The solution advances Cisco’s intent-based networking by providing policy-based automation from the Edge to the Cloud. This means IT managers can identify network policy and that intent will become automatically embedded within the network. Manual network set up was a hundred-hour effort. SDA makes bringing up a network, including the ever important policy implementation, something that takes a few hours. SDA is a gift to the IT departments doing box by box connections and knowing there has to be an easier way….well there is.
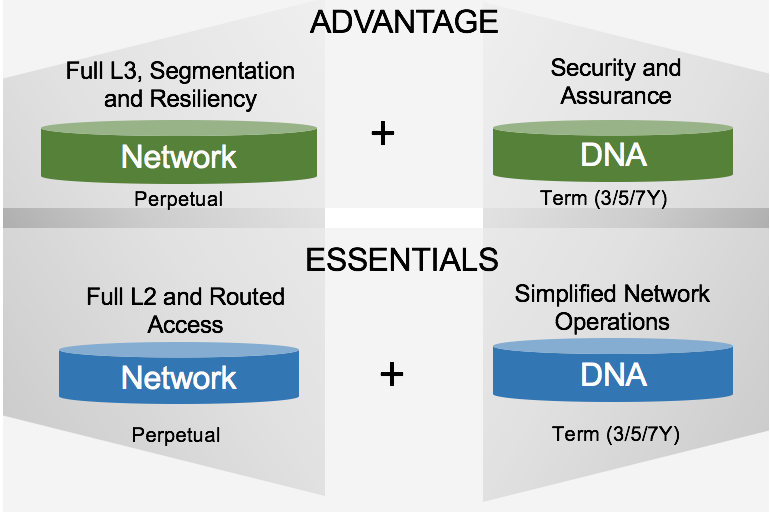
Software Subscription
Cisco transformed how network infrastructure software is bought and deployed by introducing subscription-based network software. The subscription-based software focuses on reducing cost of ownership over the software lifecycle. It also means software updates are available to customers immediately without requiring a hardware purchase.
Encrypted Traffic Analysis (ETA)
Given that the threat landscape is rapidly growing in the enterprises where data is being encrypted at a much faster rate, Cisco has solved the biggest cybersecurity challenge by finding a way to analyze threats without decrypting traffic. Cisco altered enterprise security via ETA to enable malware detection through behavioral analytics on encrypted traffic. This tremendous advancement gives users of Cisco networks greater security as the network can apply analysis on ETA data to isolate security issues and prevent similar issues in the future.
Additional Software Features and Releases
Cisco maintains its lead in simplification of cloud-scale networking by delivering model-driven telemetry and adding new yang data-models.
Cisco continues to show its commitment for increasing high-availability and reducing operational downtime for customer’s networks by providing new software features like Software Maintenance Updates (SMU), Graceful Insertion and Removal (GIR) and Stackwise Virtual.
In terms of the releases, Cisco promotes the long-term stability in customer deployments -- the recommended software releases for Catalyst 3850 and Catalyst 3650 was changed from IOS XE 3.6/3.7 to the new IOS XE 16.3.5b.
These features help automate the customer’s network, maintain the network’s stability, improve reliability, and thus reduce operational expenses for customers.
As Cisco Systems continues to drive disruptive innovation into the marketplace, our customers will see more features in support of The Network. Intuitive. In addition to the capabilities we introduced last year to help set up the physical network, the second wave is going to put more features on that network and ensure that network runs the way it is intended to.
Stay tuned for more exciting news as Cisco unveils new innovations in 2018!
