- Cisco Community
- Technology and Support
- Networking
- Routing
- Re: Can't get anyconnect "vpn-filter value VPN-FILTER-ACL" to work :-(
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-16-2019 06:24 AM - edited 05-16-2019 06:25 AM
AnyConnect is working fine for remote colleagues but I can't lock down the connections with vpn-filter. I've put in an ACL on outside-in but I can't do that when I replace the main firewall. The full ASA 5520 configuration is attached.
Here is the AnyConnect configuration that works great. How can I put in a vpn-filter? Can I put in a vpn-filter for each username? I've searched the internet and can't find a vpn-filter configuration that works.
webvpn
anyconnect image flash:anyconnect-win-4.6.03049-webdeploy-k9.pkg
enable outside
anyconnect enable
sysopt connection permit-vpn
ip local pool VPN_POOL 192.168.181.5-192.168.181.10 mask 255.255.255.0
access-list SPLIT_TUNNEL standard permit 192.168.168.0 255.255.255.0
group-policy ANYCONNECT_POLICY internal
group-policy ANYCONNECT_POLICY attributes
vpn-tunnel-protocol ssl-client ssl-clientless
split-tunnel-policy tunnelspecified
split-tunnel-network-list value SPLIT_TUNNEL
dns-server value 192.168.168.1
webvpn
anyconnect keep-installer installed
anyconnect ask none default anyconnect
anyconnect dpd-interval client 30
tunnel-group MY_TUNNEL type remote-access
tunnel-group MY_TUNNEL general-attributes
default-group-policy ANYCONNECT_POLICY
address-pool VPN_POOL
exit
tunnel-group MY_TUNNEL webvpn-attributes
group-alias SSL_USERS enable
webvpn
tunnel-group-list enable
username SSL_USER password NEW_PASSWORD
username SSL_USER attributes
service-type remote-access
end
Solved! Go to Solution.
- Labels:
-
Other Routing
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-16-2019 11:47 AM
Careful with that ACL, what other things uses internet on that firewall (and its subnets) DNS? NTP? What about VPN clients, will they use the internet the firewall has?
If all the boxed are checked, then yes the ACL you have should work, you just need to add it to the correct interface using the command
access-group OUTSIDE-IN in interface <name_of_the_interface>
Hope this helps.
Rolando A. Valenzuela.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-16-2019 07:45 AM
Hello!
I don't see the command in question. What are you trying to restrict? is this just for one user or for all of them?
Rolando A. Valenzuela.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-16-2019 08:16 AM - edited 05-16-2019 08:22 AM
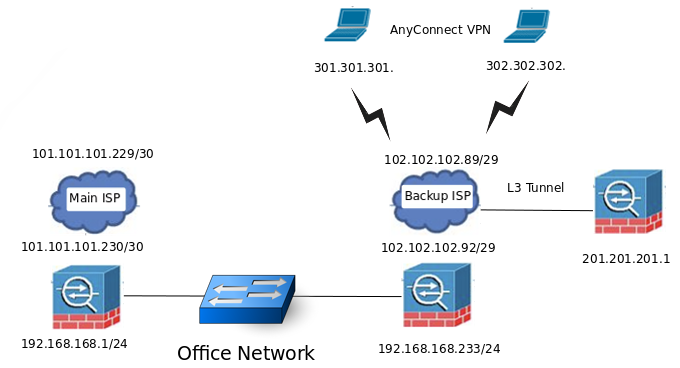
Hi Rolando, I'm trying to lockdown the anyconnect VPN to the remote AnyConnect customers:
remote VPN client 1 301.301.301.
remote VPN client 2 302.302.302.
From what I've been able to understand, the VPN_FILTER goes here?
webvpn
anyconnect keep-installer installed
anyconnect ask none default anyconnect
anyconnect dpd-interval client 30
tunnel-group MY_TUNNEL type remote-access
tunnel-group MY_TUNNEL general-attributes
------------> vpn-filter value VPN-FILTER
default-group-policy ANYCONNECT_POLICY
address-pool VPN_POOL
exit
Once that is done, and I put in the NAT OVERLOAD for access to the internet, it should be pretty secure. Only client IPs can get to AnyConnect, the standing L3 Tunnel is peer-to-peer, and only NAT can get out to 0.0.0.0 0.0.0.0.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-16-2019 08:27 AM - edited 05-16-2019 09:29 AM
Looks like I got it. Just goes to show that finding a good reference makes all the difference.
access-list VPN-TEST-ACL extended permit ip host 101.101.101.230 any log
username TEST password Yys0My.yB60Du9Q4 encrypted
username TEST attributes
vpn-filter value VPN-TEST-ACL
service-type remote-access
May 16 2019 16:20:11: %ASA-6-302013: Built inbound TCP connection 94188 for outside:101.101.101.230/49929 (101.101.101.230/49929) to identity:102.102.102.92/443 (102.102.102.92/443)
May 16 2019 16:20:11: %ASA-6-302013: Built inbound TCP connection 94190 for outside:101.101.101.230/49932 (101.101.101.230/49932) to identity:102.102.102.92/443 (102.102.102.92/443)
May 16 2019 16:20:11: %ASA-5-737003: IPAA: Session=0x0000a000, DHCP configured, no viable servers found for tunnel-group 'MY_TUNNEL'
May 16 2019 16:20:11: %ASA-5-737034: IPAA: Session=0x0000a000, IPv6 address: no IPv6 address available from local pools
May 16 2019 16:20:11: %ASA-5-737034: IPAA: Session=0x0000a000, IPv6 address: no IPv6 address returned
May 16 2019 16:20:11: %ASA-4-722041: TunnelGroup <MY_TUNNEL> GroupPolicy <ANYCONNECT_POLICY> User <TEST> IP <101.101.101.230> No IPv6 address available for SVC connection
May 16 2019 16:20:11: %ASA-5-722033: Group <ANYCONNECT_POLICY> User <TEST> IP <101.101.101.230> First TCP SVC connection established for SVC session.
May 16 2019 16:20:11: %ASA-7-746012: user-identity: Add IP-User mapping 192.168.181.5 - LOCAL\TEST Succeeded - VPN user
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-16-2019 08:59 AM
You can do it with vpn-filter value, but that it is usually to restrict the traffic inside the VPN. If you just want to restrict who can connect to the VPN, why don't you create a ACL on the outside interface? and not to what they can connect?
Rolando A. Valenzuela.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-16-2019 09:36 AM - edited 05-16-2019 10:56 AM
OH, ((( restrict the traffic inside the VPN ))) means that anyone can hit the https://102.102.102.92:443 and get an authentication prompt? I tested the VPN-FILTER and I can even login!!! But I can't access anything - just like you said.
Looks like the best that I can do is to put AnyConnect on a weird port and put in an OUTSIDE ACL for that port.
access-list OUTSIDE-IN extended permit ip 301.301.301.0 255.255.255.0 host 201.201.201.92 eq 8086
access-list OUTSIDE-IN extended deny ip any any
webvpn
no enable outside
port 8086
enable outside
anyconnect enable
tunnel-group-list enable
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-16-2019 11:47 AM
Careful with that ACL, what other things uses internet on that firewall (and its subnets) DNS? NTP? What about VPN clients, will they use the internet the firewall has?
If all the boxed are checked, then yes the ACL you have should work, you just need to add it to the correct interface using the command
access-group OUTSIDE-IN in interface <name_of_the_interface>
Hope this helps.
Rolando A. Valenzuela.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-17-2019 04:53 AM
Renanda, Got it, can't even connect to http anyconnect with this acl :-)
<<< access-group OUTSIDE-IN in interface outside control-plane >>>
control-plane is the key word that examines all traffic entering the ASA, not just traversing the ASA. So now I can put anyconnect on a weird port and lock down that port :-)
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide