Hi all,
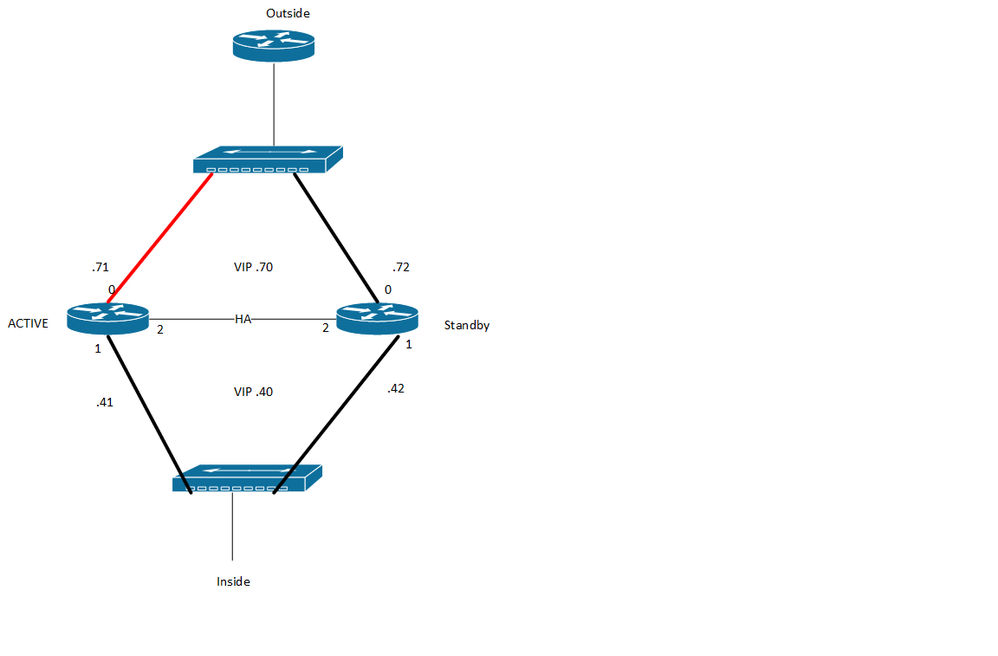
I have a pair of 4400s setup specifically for SIP voice services. In our config we have an 'outside' public IP connecting to the carrier voice cloud, and a 'inside' IP connecting to my private IP network.
Since i have two 4400s we wanted to use some sort of high availability service and found the 'redundancy' command and this PDF: https://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=2&cad=rja&uact=8&ved=2ahUKEwijqO_ZqPrgAhVm9IMKHbU3AxIQFjABegQICBAC&url=https%3A%2F%2Fwww.cisco.com%2Fc%2Fen%2Fus%2Ftd%2Fdocs%2Fios-xml%2Fios%2Fipaddr_nat%2Fconfiguration%2Fxe-3s%2Fnat-xe-3...
On both routers we setup:
redundancy
mode none
application redundancy
group 1
name voice-b2bha
priority 100 failover threshold 75
timers delay 30 reload 60
control GigabitEthernet0/0/2 protocol 1
data GigabitEthernet0/0/2
track 1 shutdown
track 2 shutdown
!
!
!
track 1 interface GigabitEthernet0/0/0 line-protocol
!
track 2 interface GigabitEthernet0/0/1 line-protocol
Then for each interface we set:
interface GigabitEthernet0/0/0
description PDC1-PDCL10-ASW1 G1/0/4
ip address 172.18.91.41 255.255.255.0
media-type rj45
negotiation auto
redundancy rii 1
redundancy group 1 ip 172.18.91.40 exclusive
ip virtual-reassembly
!
interface GigabitEthernet0/0/1
description pdc1-pdcp10-isw1 G1/0/25
ip address 12.100.35.71 255.255.255.224
media-type rj45
negotiation auto
redundancy rii 2
redundancy group 1 ip 12.100.35.70 exclusive
ip virtual-reassembly
!
On the standby router we set the same 'interface' commands but used the next IP (i.e. G0- 172.18.91.42 and G1- 12.100.35.72).
Gig 0/0/2 is simply a crossover cable between the two routers.
On to the problem:
For a test we disconnected the cable between Router 1 and G0/0/0 the interface went down/down as expected. Alll the redundancy rolled over to the Router 2 as it became 'active'.
However when Router1 lost interface G0/0/0 it reloaded with: System returned to ROM by RG-application reload on voice-b2bha RG at 16:08:47
We then reconnected the cable from Router1 G0/0/0. it rediscovered the HA and became Active. This then caused Router2 to reload with the same error.
In a call with TAC this behavior was 'normal' and suppose to be there to help prevent any split brain (loop, active interfaces, routes, etc) problems. It just seems very excessive to reload a router rather than employ some sort of standby process.
The sloppy drawing shows the interface we 'disconnected' for this test. Once that was done the Router 2 became Active and Router 1 reloaded.
Anybody else use this "Redundancy" service command? Can you point me to a better document or am i using this correctly?
This post is more of a discussion than troubleshooting BTW.