- Cisco Community
- Technology and Support
- Networking
- Routing
- Re: default route practice in ospf
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-11-2022
12:00 AM
- last edited on
12-14-2022
01:18 AM
by
Translator
![]()
Hello
Hope you are all right. I think I had readed most of below link.
I have some question about practice. Hope can have your advice and share experience.
In a typical environment. A head office with multi branch office.
Q1. How to design ospf area for head office and each? Head office with area 1 then edge router have area 0, all other branch similar this? or other way?
Q2. How office have ospf communicate with each other? I just put IPSEC vpn(limit by knowledge, I only know this) to confirm each office can touch each other, then ospf can work?
Q3. Should I put wan link ospf as demand-circuit to keep it on?
Q4. If I use
default-information originate
in router ospf sesction on edge router. It will originate default router to let other router use me as default gateway. This work in current area, but this type 5 lsa will lean by whole AS, include other branch office. This is not what I want, cause branch office have their wan and their self edge for gateway. Summary the question. How could I let each area know their default gateway properly and separately?
Thanks for you time.
Best Regards.
Scott
Solved! Go to Solution.
- Labels:
-
Other Routing
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-12-2022
05:31 AM
- last edited on
12-14-2022
01:30 AM
by
Translator
![]()
Hello Scott,
to generate a default route that is bounded / limited to a single area you should use a stub area. With a stub area the ABR(s) will implicitly generate an LSA type 3 O IA for 0.0.0.0/0 to be sent into the stub area. This was the solution of the old thread mentioned above. And it is also the meaning of
implicit injected routes based on area type
written by Joseph.
However, for the network scenario that you have described up to now in this thread:
a) Head Office and Branch offices each with an indipendent internet connection
b) The use of GRE/IPSec tunnels for interconnection like DMVPN with OSPF running over tunnels
Probably the best choice is to avoid to have the main office edge routers to inject a default route they should just advertise the internal networks of the main office.
The injection of a default route would be needed if you would like to have all branch offices to access the public internet via the main office. But if this is not the case your best option is likely to avoid to create a default route in OSPF.
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-11-2022 01:34 AM
Hello,
A1: Head office with area 0 as backbone. All other area must to connect with backbone area.
A2 and A3: GRE over IPsec. You can use internet and one of solutions from cisco for example DMVPN.
A4: Here you have similar topic:
https://community.cisco.com/t5/routing/redistribute-default-route-using-ospf-multiarea-only-in-one-area/td-p/1081484
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-11-2022
04:06 AM
- last edited on
12-14-2022
01:20 AM
by
Translator
![]()
Hello Chester
I didn't understand the answer. On that example, I would like have
default-information originate
on area 1 ABR. So how could I use
no default-information originate
on it again? And it said
no default-iinformation originate
and
no default-information originate
always". Acutally, which command I should use?
Thank you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-11-2022
01:56 AM
- last edited on
12-14-2022
01:21 AM
by
Translator
![]()
I think you need area0 in tunnel between Spoke and hub, this can make you config any area in Spoke.
for the
default route
the solution is Front-Door VRF.
the Front-Door VRF is for tunnel source/destination and global behind is for tunnel.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-11-2022
07:36 AM
- last edited on
12-14-2022
01:23 AM
by
Translator
![]()
When designing an OSPF network, there are a few key considerations to keep in mind:
-
The OSPF area design is an important factor in determining how routing information is exchanged within the network. In a typical environment, the head office might be assigned to OSPF area 1, while the branch offices are each assigned to their own OSPF areas (e.g. area 2, area 3, etc.). Edge routers, which connect the OSPF network to external networks, are typically assigned to area 0. This allows the head office and each branch office to have its own independent routing domain, while still allowing routing information to be exchanged between the different areas.
-
In order for the different offices in your network to communicate with each other using OSPF, they need to be connected via some type of network link. This can be achieved using an IPsec VPN, as you mentioned, which will allow the offices to securely exchange OSPF routing information. Alternatively, you could use a dedicated WAN link (e.g. a leased line) to connect the offices, or even a combination of both VPN and WAN links.
-
Whether or not you should enable OSPF on your WAN links (i.e. use demand-circuit) depends on a number of factors, such as the type of link you are using and the specific requirements of your network. In general, demand-circuit can be a useful way to conserve bandwidth on WAN links, but it may not always be the best choice depending on your network configuration. It is worth considering the potential trade-offs and deciding on the best approach for your specific environment.
-
The
default-information originate
command in OSPF is used to advertise a default route to other routers in the same OSPF area. This can be useful if you want to use a specific router as the default gateway for the area. However, as you mentioned, this default route will also be propagated to other OSPF areas within the same Autonomous System (AS), which may not be desirable in your network. To avoid this, you can use a feature calleddefault-information originate always
which will prevent the default route from being propagated to other areas. This will allow each OSPF area to have its own default gateway, without affecting the routing in other areas.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-11-2022
04:12 PM
- last edited on
12-14-2022
01:24 AM
by
Translator
![]()
"Edge routers, which connect the OSPF network to external networks, are typically assigned to area 0. This allows the head office and each branch office to have its own independent routing domain, while still allowing routing information to be exchanged between the different areas."
Yea, but what do all these edge routers, with area zero interfaces, logically connect to as adjacent area zero router(s)? Do you want some small branch, with a very small ISR, acting as an ABR in all cases? Possibly not. Just as the words "always" and "never" often have "exceptions", is there really a "typical environment". Maybe "typical" is all branches and all available circuit/connection options are not the same between sites.
#4 I recall the difference, in OSPF, between
default-information originate
and between
default-information originate always
, the former requires the router to have a default route already "known" to that router, while the latter does not.
For example, of the former, an OSPF router also running BGP, with an ISP, if receiving a BGP default route, from ISP, will generate a default route, to itself, in OSPF, but if BGP drops the default, OSPF will withdraw the OSPF default too. I.e. OSPF default will "mirror" BGP.
However, in the latter case, "always", that router will generate a default, directly to itself, regardless of whether it "knows" of a default path out of itself.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-11-2022 10:34 PM - edited 12-12-2022 04:34 AM
Hello MaxShantar
Thanks for reply.
I still get default route on R3.
My question is open. I just wonder how to propagate default route within area. If best practice is process by other way, please just let me know that and forget my question.
Thanks for you time.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-12-2022 05:49 AM - edited 12-12-2022 08:20 AM
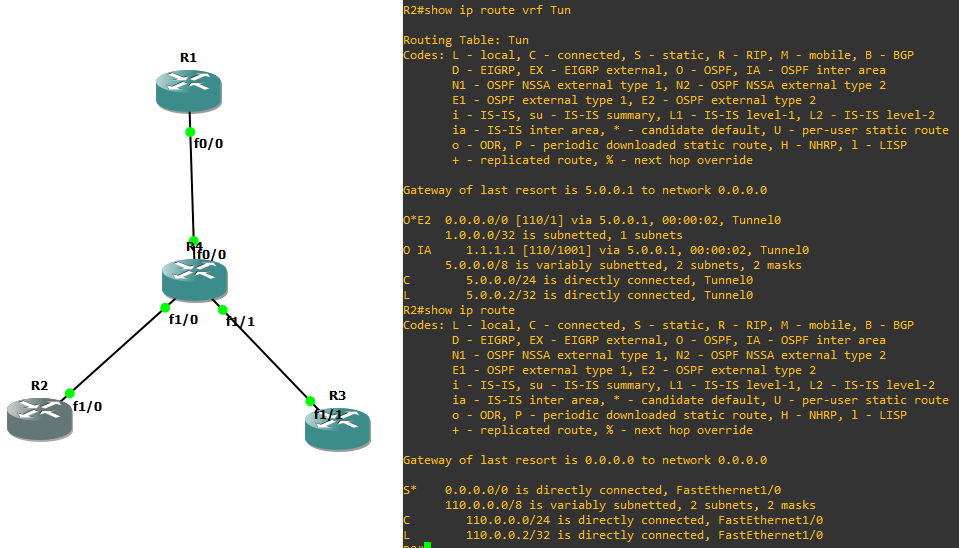
you can see there are two defualt route in Spoke R2,
why because as I mention before using FVRF or IVRF,
this give you the option to have two default route in Spoke.
one default route for all traffic not need to pass through tunnel, direct to internet.
other default route for all traffic need to pass through tunnel to Hub and then to internet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-12-2022 06:18 PM - edited 12-12-2022 06:19 PM
Dear MHM
I didn't understand FVRF and IVRF. I may need to review your answer after I learn.
Thanks for your help.
Best Regards.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-13-2022 01:53 AM
Tunnels and the Use of Front Door VRFs : Networking with FISH
this link can help you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-11-2022 03:55 PM
Q1 Much of an OSPF design depends on what you need to support. You mention "In a typical environment. A head office with multi branch office.", yea HO with branches is not uncommon, but how large a HO? How many branches? How large each branch? Etc.
Q2. Via some kind of network link. Yes, an IPSec VPN might be used, but there are many more network link kinds, although what's possible also, of course, depends on what service providers can actually provide for/at a location.
Q3. Normally, no. Demand circuits are "down" until you bring them "up" to transmit traffic. Such circuits usually charge for actual "up" time, so when using such, you only bring them up when needed. (BTW, most circuits are "up" all the time, although some charge for actual traffic sent on circuit. On these, you might reduce the usage charge if configured as a demand type circuit, because, OSPF constantly sends "hellos" between adjacent routers. [Modern network applications, often being so bandwidth demanding, reducing "hellos" often provides little cost savings. Ditto for real demand circuit, unless used as a backup circuit. And if active, for backup, again, suppressing just "hellos" often makes little difference in cost.])
Q4. Where and when to inject a default route, is part of an OSPF overall design. For example, are you using a dynamically injected default route just to avoid having all internal routes everywhere, or for the "world" (e.g. to/toward Internet) or for both purposes.
What about implicit injected routes based on area type.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-11-2022
10:44 PM
- last edited on
12-14-2022
01:28 AM
by
Translator
![]()
Hello Joseph
Thanks for reply.
I don't understand about
dynamically injected default route
and
implicit injected routes based on area type
Could you provide some command sample help for understanding?
My question is open. I just wonder how to propagate default route within area. If best practice is process by other way, please just let me know that and forget my question.
Thanks for you time.
Best Regards.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-12-2022
05:31 AM
- last edited on
12-14-2022
01:30 AM
by
Translator
![]()
Hello Scott,
to generate a default route that is bounded / limited to a single area you should use a stub area. With a stub area the ABR(s) will implicitly generate an LSA type 3 O IA for 0.0.0.0/0 to be sent into the stub area. This was the solution of the old thread mentioned above. And it is also the meaning of
implicit injected routes based on area type
written by Joseph.
However, for the network scenario that you have described up to now in this thread:
a) Head Office and Branch offices each with an indipendent internet connection
b) The use of GRE/IPSec tunnels for interconnection like DMVPN with OSPF running over tunnels
Probably the best choice is to avoid to have the main office edge routers to inject a default route they should just advertise the internal networks of the main office.
The injection of a default route would be needed if you would like to have all branch offices to access the public internet via the main office. But if this is not the case your best option is likely to avoid to create a default route in OSPF.
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-12-2022
06:15 PM
- last edited on
12-14-2022
01:33 AM
by
Translator
![]()
Dear Giuseppe
Thanks for reply. I understood default for stub or totally stub.
I can have below option to inject default within area.
| area stub | block type 4 and 5 | originate type 3 default route | only propagate with stub |
| area stub no-summary | block type 3,4, 5 | originate type 3 default route | only propagate with stub |
| area nssa default-information-originate | block type 4 and 5 | originate type 7 default route | ABR will translate to type 5 default route and propagate to other area. |
| area nssa default-information-originate nssa-only | block type 4 and 5 | originate type 7 default route | only propagate with NSSA |
| area nssa no-summary | block type 3,4, 5 | originate type 3 default route | only propagate with NSSA |
So
default-information originate
will not be use in most of case, only if I really want to route whole AS all traffic to one router. Am I right?
Also understood about inject default route on head office edge route. This call split tunnel in VPN. It will heavy load head office internet line and cause branch office internet access slow. I don't prefer this too.
Thank you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-13-2022
08:34 AM
- last edited on
12-14-2022
01:38 AM
by
Translator
![]()
"Also understood about inject default route on head office edge route. This call split tunnel in VPN. It will heavy load head office internet line and cause branch office internet access slow. I don't prefer this too."
Yes, generally within an IGP you use a default route to get traffic to come to the Internet edge. Also, yes, some use the same Internet connection for general Internet traffic and VPN using the Internet. The latter often causes all kinds of variable performance for the VPN traffic, i.e. your ". . . cause branch office internet access slow.", but that's not really due to using a default route used by a whole AS, the problem is mixing the two kinds of Internet traffic on a shared link.
"So
default-information originate
will not be use in most of case, only if I really want to route whole AS all traffic to one router. Am I right?"
In my experience, if you support internal traffic going to the Internet, using a default route is the way to do it. Of course, you can setup default routes in multiple ways, the
default-information originate
is often just a nice way to do it.
As to all of an AS's traffic going to one router, that's not always the case. Remember, the real goal of a default route is to provide a direction for traffic that does not have a match in the route table. Further, remember, a match in the route table overrides the default. I.e. You can use default routes in imaginative ways.
For example, your mention of having branch offices accessed via a Internet VPN. Sure, I might use a default to pull all internal unknown destination network traffic to some point of the network, using a default route, perhaps via
default-information originate
but as some point, I "presume" you know the branch networks. At the point, I can redirect that traffic to a different Internet link, for that purpose. I.e. no need to split tunnel (which I personally detest) because of the performance issues (as you also note) when you mix VPN traffic and general Internet traffic on the same link.
(BTW, using specific Internet connections only for VPN, with QoS, I've often achieved network performance, on par [laugh even, rarely, sometimes better], with any private cloud technology [often at much reduced cost].)
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide