- Cisco Community
- Technology and Support
- Networking
- Routing
- Failover question
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-07-2013 02:05 PM - edited 03-04-2019 07:13 PM
Hi everyone,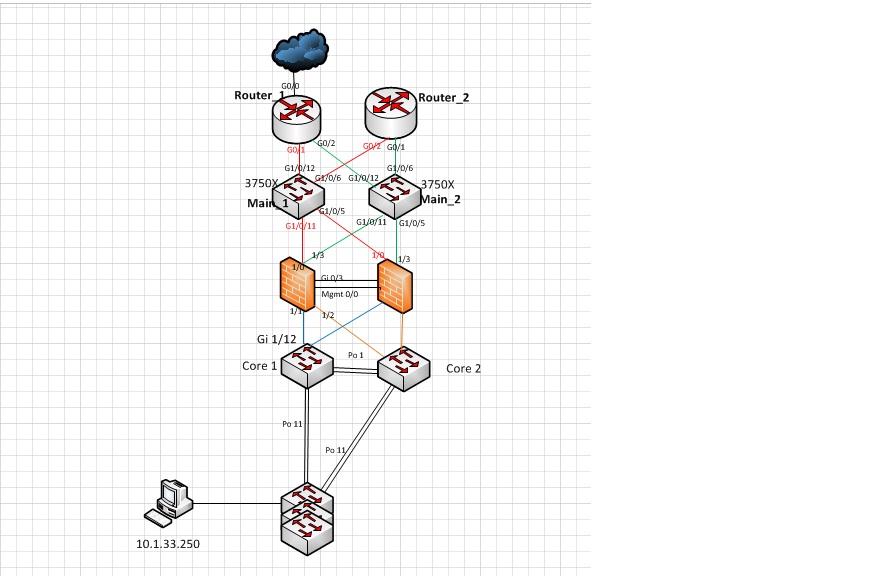
I’d like to ask some failover question. Please help me with it.
Thanks in advance.
In my network, the network is working well. It can ping 4.2.2.2. In order to test failover,
I shut down the interface Gi 1/12 of Core1 switch. After this,
From Host, it can ping the router 1 outside interface IP, X.X.X.X
And router 1 outside interface can ping 4.2.2.2
But the host is NOT able to ping 4.2.2.2.
And I found that the ASA outside interface can ping 4.2.2.2, but ping 4.2.2.2 with ASA inside interface does NOT work.
I have no idea how to troubleshoot it.
So please help me
Thank you very very much
router config :
……….
no aaa new-model
ip cef
!
ip domain round-robin
ip domain name aaaaa
ip name-server 4.2.2.2
multilink bundle-name authenticated
!
archive
log config
hidekeys
!
interface Loopback100
description mgmt interface
ip address 10.0.100.13 255.255.255.255
!
interface FastEthernet0/0
no ip address
shutdown
duplex auto
speed auto
!
interface GigabitEthernet0/0
description ISP circuit order 1-111111111111
ip address X.X.X.X 255.255.255.248
ip accounting output-packets
ip nat outside
ip nat enable
no ip virtual-reassembly
duplex full
speed 1000
media-type sfp
no negotiation auto
!
interface GigabitEthernet0/1
description uplink to main-1 interface g 1/0/12
ip address 192.168.2.253 255.255.255.0
ip accounting output-packets
ip nat inside
ip nat enable
no ip virtual-reassembly
duplex full
speed 1000
media-type sfp
no negotiation auto
standby 2 ip 192.168.2.254
standby 2 priority 110
standby 2 preempt
!
interface GigabitEthernet0/2
ip address 192.168.3.253 255.255.255.0
no ip redirects
duplex full
speed 1000
negotiation auto
standby 3 ip 192.168.3.254
standby 3 priority 110
standby 3 preempt
!
interface GigabitEthernet0/3
no ip address
duplex full
speed 1000
no negotiation auto
!
ip forward-protocol nd
ip route 0.0.0.0 0.0.0.0 X.X.X.X
ip route 10.1.0.0 255.255.0.0 192.168.2.1
ip route 10.1.20.0 255.255.255.0 192.168.2.13
no ip http server
!
ip dns server view-group aaaaaaa
ip dns server
ip nat pool mypool X.X.X.X X.X.X.X netmask 255.255.255.252
ip nat inside source list 1 pool mypool overload
!
logging alarm informational
access-list 1 permit 192.168.2.0 0.0.0.255
access-list 1 permit 192.168.3.0 0.0.0.255
!
control-plane
!
gatekeeper
shutdown
!
………..
switch config :
…..
ip domain-name xxxxxxxxxxxxxxxxxxxxxxxxx
ip name-server 4.2.2.2
interface Loopback100
ip address 10.0.100.15 255.255.255.255
!
interface FastEthernet0
no ip address
shutdown
!
interface GigabitEthernet1/0/1
!
interface GigabitEthernet1/0/2
switchport access vlan 2
switchport mode access
!
interface GigabitEthernet1/0/3
switchport access vlan 2
switchport mode access
!
interface GigabitEthernet1/0/4
switchport access vlan 2
switchport mode access
!
interface GigabitEthernet1/0/5
description uplink to asa12 port 0/0
switchport access vlan 2
switchport mode access
!
interface GigabitEthernet1/0/6
description uplink to router02 port g 0/1
switchport access vlan 2
switchport mode access
!
…
interface GigabitEthernet1/0/10
switchport access vlan 2
switchport mode access
!
interface GigabitEthernet1/0/11
description uplink to asa11 port 0/0
switchport access vlan 2
switchport mode access
!
interface GigabitEthernet1/0/12
description uplink to router01 port g 0/1
switchport access vlan 2
switchport mode access
!
interface Vlan1
no ip address
shutdown
!
interface Vlan2
ip address 192.168.2.4 255.255.255.0
!
ip default-gateway 192.168.2.254
!
ip http server
ip http secure-server
!
…..
monitor session 1 source interface Gi1/0/12
monitor session 1 destination interface Gi1/0/2
end
ASA config:
.....
interface GigabitEthernet0/3
description STATE Failover Interface
!
interface Management0/0
description LAN Failover Interface
management-only
!
interface GigabitEthernet1/0
media-type sfp
nameif outside
security-level 0
ip address 192.168.2.1 255.255.255.0
!
interface GigabitEthernet1/1
media-type sfp
nameif inside
security-level 100
ip address 192.168.4.1 255.255.255.0
!
interface GigabitEthernet1/2
media-type sfp
nameif inside-backup
security-level 100
ip address 192.168.5.1 255.255.255.0
!
interface GigabitEthernet1/3
media-type sfp
nameif outside-backup
security-level 0
ip address 192.168.3.1 255.255.255.0
!
ftp mode passive
same-security-traffic permit inter-interface
same-security-traffic permit intra-interface
object-group icmp-type AllowedICMP
icmp-object echo
icmp-object echo-reply
icmp-object traceroute
icmp-object unreachable
icmp-object time-exceeded
access-list EXEMPT extended permit ip 192.168.4.0 255.255.255.0 any
access-list EXEMPT extended permit ip 10.1.0.0 255.255.0.0 any
access-list EXEMPT extended permit ip 192.168.5.0 255.255.255.0 any
access-list no-nat extended permit ip 10.1.0.0 255.255.0.0 host 0.0.0.0
access-list outside_access_in extended permit icmp any any object-group AllowedICMP
access-list outside_access_in extended permit ip host 192.168.2.253 any
access-list outside_access_in extended permit ip 192.168.2.0 255.255.255.0 any
…
failover
failover lan unit secondary
failover lan interface fobasic Management0/0
failover key *****
failover link fostate GigabitEthernet0/3
failover interface ip fobasic 192.168.200.1 255.255.255.0 standby 192.168.200.2
failover interface ip fostate 192.168.201.1 255.255.255.0 standby 192.168.201.2
icmp unreachable rate-limit 1 burst-size 1
icmp permit any echo-reply outside
icmp permit any unreachable outside
no asdm history enable
arp timeout 14400
global (outside) 1 interface
global (outside-backup) 1 interface
nat (inside) 0 access-list no-nat
nat (inside) 1 0.0.0.0 0.0.0.0
access-group outside_access_in in interface outside
access-group outside_access_in out interface outside
access-group EXEMPT in interface inside
access-group EXEMPT out interface inside
!
router eigrp 10
no auto-summary
network 192.168.2.0 255.255.255.0
network 192.168.3.0 255.255.255.0
network 192.168.4.0 255.255.255.0
network 192.168.5.0 255.255.255.0
redistribute static
!
route outside 0.0.0.0 0.0.0.0 192.168.2.254 1
……
http 10.1.0.0 255.255.0.0 inside
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart
crypto ipsec security-association lifetime seconds 28800
crypto ipsec security-association lifetime kilobytes 4608000
!
track 1 rtr 123 reachability
……..
management-access inside
dhcpd dns x.x.x.x
!
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
webvpn
!
class-map inspection_default
match default-inspection-traffic
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect rtsp
inspect esmtp
inspect sqlnet
inspect skinny
inspect sunrpc
inspect xdmcp
inspect sip
inspect netbios
inspect tftp
inspect ip-options
inspect icmp
inspect icmp error
!
service-policy global_policy global
…..
Solved! Go to Solution.
- Labels:
-
Other Routing
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-07-2013 09:15 PM
Hi Sam,
You need to add subnets to NAT ACL on the router where hosts are located. I guess they are:
access-list 1 permit 192.168.4.0 0.0.0.255
access-list 1 permit 192.168.5.0 0.0.0.255
And other subnets if you have them. Then remove on the router's interface:
int g0/0
no nat enable
int g0/1
no nat enable
Then try to test again failover it should work.
Hope it will help.
Best regards,
Abzal
Abzal
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-09-2013 09:09 PM
Hi,
On the left ASA you're doing NAT so inside LAN subnet 192.168.4.0/24 gets translated into 192.168.2.1. I believe that's why you didn't need to add subnet into ACL. About ASA on the right side I cannot tell for sure. I think there might be NAT haven't been configured. So subnet are not getting translated instead just being forwarded to the router. For sure I can tell only after I see the config. of ASA and switches that is connected to.
Hope it will help.
Best regards,
Abzal
Abzal
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-07-2013 09:15 PM
Hi Sam,
You need to add subnets to NAT ACL on the router where hosts are located. I guess they are:
access-list 1 permit 192.168.4.0 0.0.0.255
access-list 1 permit 192.168.5.0 0.0.0.255
And other subnets if you have them. Then remove on the router's interface:
int g0/0
no nat enable
int g0/1
no nat enable
Then try to test again failover it should work.
Hope it will help.
Best regards,
Abzal
Abzal
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-08-2013 06:11 AM
hi Abzal,
Thank you so much for your reply.
and,
I've got another NAT exempt question.
when I debug NAT on the router,
the NAT transformation is like
s=192.168.2.1 -> X.X.X.X d=4.2.2.2
but my host inside the Firewall is, let's say 10.1.33.40.
so I think the NAT should be,
s=10.1.33.40 -> X.X.X.X d=4.2.2.2 since the IP doesn't transform by the firewall.
so what is wrong with my concept ?
Thanks again,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-08-2013 06:35 AM
Hi,
Nothing is wrong in you concept. Because you are using NAT it means that IP of source host inside your private LAN will be changed when packet goes outisde of your private to access public Internet. Because private addresses are non routable on the Internet. So NAT changes IP address of source with external IP address.
And on routers you need to show in ACL which IP addresses or subnets are allowed to go outside. When packets come to the router and packet is destined to the Internet, first it compares source IP address against NAT ACL then if it finds a match router does a paclet translation and packet goes out from outisde interface.
Here are great links that'll help you
http://book.soundonair.ru/cisco/ch24lev1sec1.html
http://www.cisco.com/en/US/tech/tk648/tk361/technologies_tech_note09186a0080094831.shtml
Hope it will help.
Best regards,
Abzal
Abzal
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-09-2013 05:27 PM
hi Abzal,
I've got another question.
in the first place, I didn't configure "access-list 1 permit 192.168.4.0 0.0.0.255"
It can ping very well.
But when the left firewall became standby and the right firewall became active,
then I need to confgire that command on router.
otherwise it was NOT able to failover.
so my question is that when the left firewall is Active, then I do NOT need to configure that command.
while when the right firewall is Active, then I DO need to configure that command.
Is there any link which can answer this question ?
Thanks again,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-09-2013 09:09 PM
Hi,
On the left ASA you're doing NAT so inside LAN subnet 192.168.4.0/24 gets translated into 192.168.2.1. I believe that's why you didn't need to add subnet into ACL. About ASA on the right side I cannot tell for sure. I think there might be NAT haven't been configured. So subnet are not getting translated instead just being forwarded to the router. For sure I can tell only after I see the config. of ASA and switches that is connected to.
Hope it will help.
Best regards,
Abzal
Abzal
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-12-2013 08:53 AM
about firewalls, they are sync.
the Active(left side) one has the same configuration with the Standby(right) one.
That was why I ask you this question.
I think I need to research about firewalls more then ask.
Thanks again ~
BTW, when I shut down the Gi 1/12 interface of Core 1 switch,
then the left firewall became standby and right one became active.
but,
when I shut down the 1/1(or 1/0 )interface of left ASA, the left ASA keeps Active and the right ASA
keeps Standby.
This is also one point which I don't understand now.
Thanks again and I am going to reserach more.
Thanks,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-18-2013 11:23 AM
hi Abzal,
sorry I've got another question.
Please help me when you get a chance ?
when I turn off the Gi 1/12 interface of Core 1 switch,
the firewall failover automatically.
but ...
when I turn off 1/0 or 1/1 interface of left firewall,
it did NOT failover automatically.
Do you know why ?
according to the cisco book "Cisco ASA 5500 series Configuration guide using the CLI"
Failover Behavior,
Failure Event Policy Active Action Standby Action Notes
Interface failure on active unit Failover Mark active as failed Become active
above threshold
In my case I shut down the 1/1 interface of left(Active) firewall, so it should go to Standby firewall.
but it remained Active.
This is my question.
Thanks a million,
thanks,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-18-2013 12:07 PM
hi
I just found this article,
https://supportforums.cisco.com/thread/228489
I am going to test it first.
So you could ignore the previous question,
thanks,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2013 08:58 AM
hi Abzal,
I've followed this link,
https://supportforums.cisco.com/thread/228489
but when I shut down the inside interface of left ASA,
it failed to failover.
Is it related to vlan 4 interface ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-08-2013 07:33 AM
Hi Abzal,
It is working now. It can failover well.
I truly truly appreciate your help.
Thanks a million
Best,
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide

